HIPAA Compliance Checklist for 2025

SaaS-related breaches cost organizations an average of $4.88 million per incident. The entry point is rarely a sophisticated exploit. It's a misconfigured app, a stale credential, or a shadow tool IT never approved. 28% of organizations reported a SaaS-related breach in the past year alone.
If you're evaluating SaaS security tools in 2026, you need more than a list. You need to know which tool closes which gap, where each one fits in your stack, and what to prioritize given your threat surface.
This article breaks down 12 of the best SaaS security tools for CISOs, what each does well, and how to build a stack that actually holds.
TL;DR
- 12 SaaS security tools cover the full SaaS security stack: discovery, access governance, SSPM, threat detection, and network control. No single tool does all of it.
- Tool selection depends on your biggest gap: shadow IT and AI sprawl need discovery-first tools; over-privileged access needs governance automation; misconfigurations need continuous SSPM.
- CloudEagle.ai is the broadest platform: it covers discovery, identity governance, zero-touch offboarding, AI usage tracking, and SSPM in one place, built for IT, security, and finance teams together.
- Some tools complement, some anchor: AppOmni, Obsidian, and Reco.ai work best alongside a core platform; Zscaler and CrowdStrike extend existing infrastructure investments.
- Start with what you can't see: any SaaS security tool is only as effective as the inventory it runs against. Discovery has to come before detection or governance.
1. What Makes a SaaS Security Tool Worth Buying
CISOs evaluating SaaS security tools in 2026 are dealing with a stack that changes daily: new apps adopted without IT review, AI tools processing sensitive data outside any governance framework, contractors with access that was never revoked, and configurations that drift the moment a vendor pushes an update.
The tools worth buying solve one or more of these gaps with automation, not manual workflows. Here's what's actually breaking security programs right now, and what to look for when evaluating a fix:
- Shadow IT and shadow AI: Multiple SaaS applications run without IT approval. AI tools have made this significantly worse. Look for tools that discover apps across spend signals, SSO gaps, browser activity, and OAuth grants, not just what's in your IdP.
- Misconfiguration: 70% of SaaS breaches start with a misconfigured setting. Look for continuous posture monitoring that flags drift between audits, not just point-in-time assessments.
- Over-privileged access: 85% of accounts are over-privileged. 48% of organizations have former employees with active access. Look for automated access reviews and zero-touch offboarding that covers apps outside your SSO.
- Fragmented governance: IT, finance, and security each manage a different piece of the SaaS stack. Look for tools that give all three teams a shared source of truth, not separate dashboards.
The Salesloft Drift incident hit 700 organizations in 2025, including Cloudflare, Palo Alto Networks, and CyberArk. If dedicated security companies with mature stacks couldn't see it coming, the gap isn't about expertise. It's about a tooling category that most organizations haven't fully addressed yet.
The 12 SaaS security tools below cover that layer across discovery, access governance, posture management, and threat detection, so you can evaluate what belongs in your stack and where to start.
2. 12 Best SaaS Security Tools for CISOs in 2026
1. CloudEagle.ai
Best for: Unified SaaS and AI governance across discovery, access, posture, and compliance
CloudEagle.ai is built for security, procurement, finance, and IT teams that need full control over a SaaS and AI stack that has grown beyond what spreadsheets, IdPs, or point tools can govern. It covers the full lifecycle from discovery to deprovisioning, with compliance evidence generated as a byproduct of day-to-day operations.
Key features:
a) SaaS and AI app discovery: Security teams can't govern what they can't see. CloudEagle.ai surfaces every app in the environment, including shadow tools, free-tier sign-ups, and OAuth-connected apps, by correlating spend signals, login data, and usage patterns across sources.

b) Identity governance and access reviews: Over-privileged accounts and stale permissions are the most reliable path into a SaaS environment. CloudEagle automates access certification across all connected apps, flags excessive permissions, and enforces least-privilege without manual review cycles.

c) Zero-touch offboarding: Every day a former employee retains access is an open attack surface. CloudEagle triggers instant deprovisioning across 500+ apps the moment an HRIS exit is detected, including apps outside SSO coverage, and generates audit-ready logs automatically.

Rec Room was manually logging into 30+ admin consoles per offboarding, leaving former employees with lingering access and burning $200K a year in unused licenses. After deploying CloudEagle.ai, they cut offboarding time by 96%, reduced lingering access by 75%, and reclaimed the full $200K annually.
d) Consumption-based AI usage tracking: AI tools are the fastest-growing shadow IT category. CloudEagle monitors Claude, Cursor, Gemini, and other AI tool usage so security teams can enforce data governance before sensitive information leaves the org.

For teams building AI security awareness across SaaS tools, CloudEagle provides the usage visibility and policy enforcement to make that program operational rather than theoretical.
e) SSPM and compliance automation: Over 45% of SOC 2 and ISO audit findings relate to access governance gaps. CloudEagle continuously monitors configurations against security baselines and generates audit evidence as a byproduct of normal operations.
For organizations that need SaaS tools with ISO-certified security controls built into the workflow, CloudEagle replaces the pre-audit scramble with continuous, automated compliance.
2. AppOmni
Best for: Deep SaaS posture management and behavioral threat detection

AppOmni is the right choice for security teams that need continuous visibility into how SaaS apps are configured and how users are behaving inside them. Its threat detection catches the attacks that perimeter tools miss: valid credentials operating inside trusted apps, misconfigured sharing settings, and OAuth abuse at scale.
Key features:
- Continuous posture scoring across high-risk apps like Salesforce, Microsoft 365, and ServiceNow
- Behavioral baselining to catch anomalous access patterns within SaaS environments
- Detection logic built around SaaS-specific attack patterns: credential stuffing, OAuth abuse, lateral movement
- Integration with existing SIEM and SOAR workflows for faster response
3. Valence Security
Best for: SaaS-to-SaaS integration risk and non-human identity governance

Most SaaS security tools focus on human users. Valence focuses on the connections between apps: OAuth grants, API keys, and service account tokens that accumulate invisibly and are rarely covered by standard IAM reviews. For any API security tools evaluation in SaaS environments, Valence belongs on the shortlist, as it governs the non-human identity layer that most platforms ignore entirely.
Key features:
- Maps every SaaS-to-SaaS integration and flags over-permissioned connections
- Governs non-human identities: service accounts, API tokens, and OAuth grants at scale
- Enforces remediation without disrupting business workflows
- Especially relevant as agentic AI tools create new integration surfaces automatically
4. Obsidian Security
Best for: Insider risk and SaaS threat detection

If your biggest concern is catching a compromised account or a malicious insider before damage is done, Obsidian is purpose-built for it. It builds behavioral baselines for every user and app, then alerts on deviations using logic designed for SaaS attack patterns, not generic SIEM rules that drown SOC teams in noise.
Key features:
- Behavioral baselining tailored to SaaS activity patterns
- Detection for account compromise, insider threats, and privilege escalation
- Low-noise alerting built around SaaS attack patterns, not generic SIEM rules
- Clean integration with existing SOAR and incident response workflows
5. Nudge Security
Best for: Shadow IT discovery and behavioral governance at scale

Nudge Security is built for organizations where top-down enforcement doesn't scale. Rather than blocking unapproved apps, which drives employees to workarounds, it discovers every app through browser-based signals and engages employees directly with contextual security nudges. Security teams set the policies; Nudge automates the outreach.
Key features:
- Agentless SaaS and AI discovery via browser extension, no network proxy required
- Automated employee-facing nudges for risky app behavior without IT bottlenecks
- Strong supply chain risk visibility across vendor integrations and OAuth grants
- Particularly effective for distributed teams where top-down enforcement creates friction
6. Grip Security
Best for: SaaS identity risk and IdP coverage gap analysis
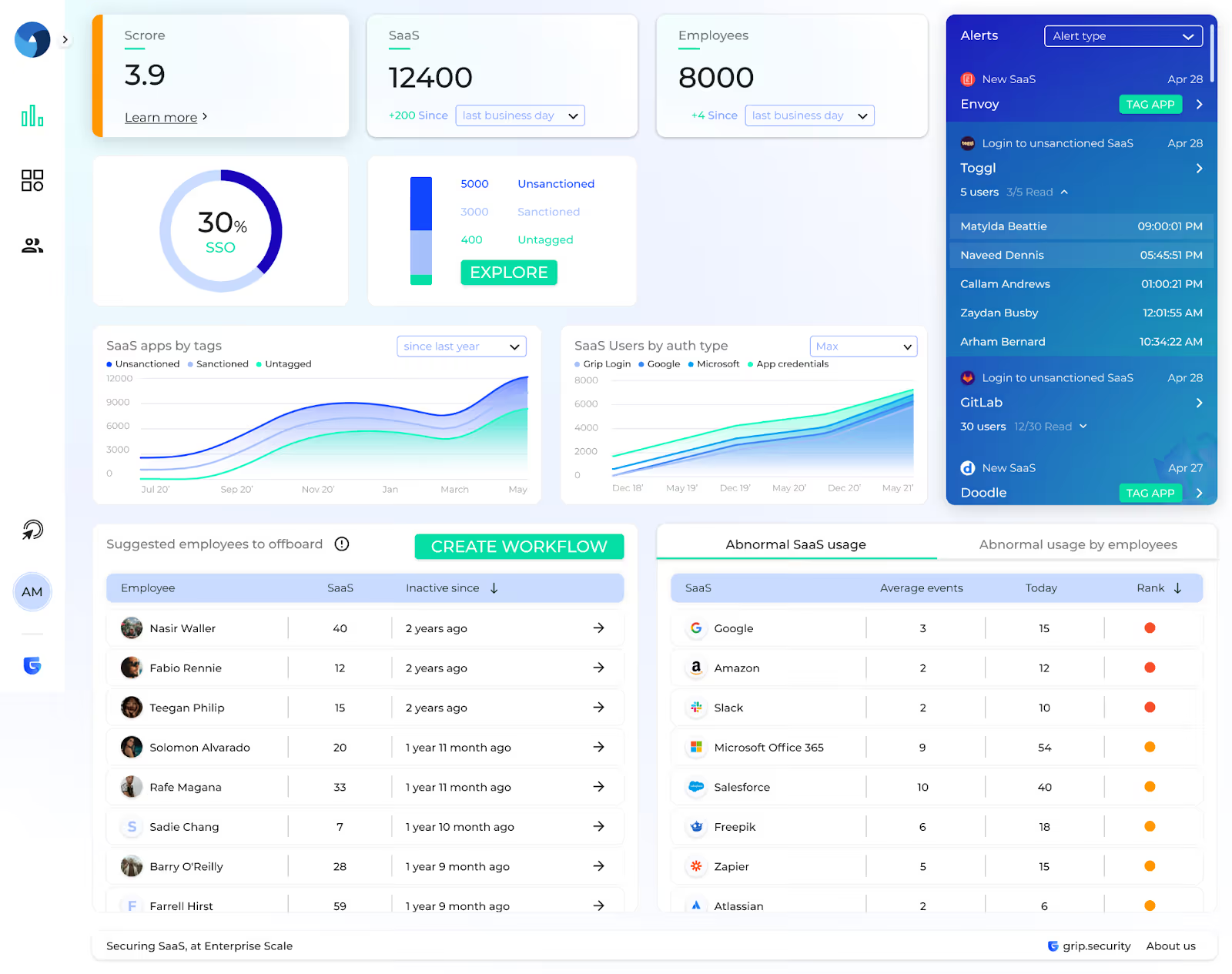
Most organizations assume their IdP covers their SaaS access risk. Grip shows them how much sits outside it. It maps every user-app relationship across the environment, including apps signed up with personal emails or predating the SSO rollout, giving security teams a clear picture of where identity governance has no reach.
Key features:
- Discovers all user-app relationships, including apps entirely outside IdP coverage
- Surfaces shadow SaaS exposure tied to personal email sign-ups
- Prioritizes enforcement actions by coverage gap and risk impact
- Helps security teams understand where the SSO extension would have the highest ROI
7. Reco.ai
Best for: AI-native SaaS security and data exposure management

Reco is built for security teams that need context, not just alerts. It uses AI to analyze SaaS activity and score risk based on user role, app sensitivity, and the data involved, so security teams spend time on genuine threats rather than false positives.
Key features:
- Context-aware risk scoring across SaaS activity and data exposure events
- Posture management and threat detection in a single platform
- Specific capabilities for governing AI-enabled SaaS apps and generative AI integrations
- Covers both configuration risk and behavioral anomalies within applications
8. Adaptive Shield (Check Point)
Best for: Enterprise SSPM with broad configuration coverage

For security teams that need continuous misconfiguration monitoring across a large, complex SaaS portfolio, Adaptive Shield provides the broadest app coverage in the SSPM category. It's consistently ranked among the best security compliance tools for SaaS companies running SOC 2, ISO 27001, or NIST programs, checking configurations automatically against established benchmarks and surfacing drift before it becomes a breach.
Key features:
- Configuration monitoring across 150+ SaaS applications out of the box
- Automated checks against CIS benchmarks, SOC 2, ISO 27001, and NIST frameworks
- Integrated with Check Point CloudGuard for unified cloud and SaaS posture
- Strong compliance reporting for audit readiness across multiple frameworks
- Preferred by organizations seeking SaaS tools with ISO-certified security monitoring, coverage spans ISO 27001, SOC 2, NIST, and CIS benchmarks out of the box.
9. Zscaler (CASB + SaaS Security)
Best for: Network-level SaaS control and data loss prevention

Zscaler is the right call when you need to control SaaS access and enforce DLP policies at the network layer, particularly across a large workforce where endpoint management is inconsistent. Its inline inspection catches data moving through SaaS apps before it leaves the organization.
Key features:
- Inline traffic inspection and DLP enforcement across all SaaS usage
- App discovery and risk scoring through network telemetry
- Granular access controls tied to user identity and device posture
- Best paired with an API-based SSPM for configuration governance inside apps
10. Microsoft Defender for Cloud Apps
Best for: Microsoft-first environments

For organizations running primarily on Microsoft 365, Defender for Cloud Apps is the most integrated option available. It pulls from existing Azure AD, Entra ID, and endpoint telemetry to provide CASB and SaaS security without additional connectors or data pipelines.
Key features:
- Native integration with Azure AD, Entra ID, and the broader Microsoft Defender XDR platform
- App discovery, shadow IT detection, and access governance within the Microsoft ecosystem
- Correlated signals across cloud, SaaS, and endpoint in a single investigation view
- Coverage outside Microsoft's own apps is more limited. Best as a primary tool for M365-centric stacks.
11. CrowdStrike Falcon for SaaS
Best for: Connecting SaaS risk to endpoint and identity telemetry
For security teams already running CrowdStrike, adding SaaS coverage through Falcon gives them correlated attack chain visibility without a separate vendor. When a compromised endpoint leads to SaaS credential exposure, Falcon connects those events in one timeline rather than requiring analysts to pivot between tools.
Key features:
- Connects SaaS compromise events to endpoint activity for unified attack chain visibility
- Particularly effective when a compromised device leads to SaaS credential exposure
- Leverages existing Falcon telemetry; no separate agent or data pipeline required
- Natural fit for organizations already running Falcon as their primary EDR
12. BetterCloud
Best for: SaaS lifecycle automation and operations

BetterCloud is the right pick when the biggest security risk is operational, stale accounts, delayed offboarding, and inconsistent provisioning. It automates the SaaS lifecycle workflows that create access gaps when done manually, reducing the risk that comes from IT teams operating at human speed across a fast-moving app portfolio.
Key features:
- Automated provisioning and deprovisioning workflows across a large SaaS portfolio
- File and data security policies are enforced at the SaaS layer
- Change management and alert workflows tied to SaaS activity
- Best for organizations where the primary security gap is operational: stale accounts, delayed offboarding, and inconsistent access setup
3. How to Choose the Right SaaS Security Tools for Your Stack
When running an API security tools evaluation for SaaS, also ask whether the tool covers app-to-app connections and OAuth grants, not just user-level access. Most visibility gaps live in the integration layer, not the identity layer.
Three questions that should drive your shortlist:
- What can't you see? Discovery comes first. Any investment in detection or governance is only as effective as the inventory it runs against.
- Where does access linger? Stale accounts and over-permissioned roles are the most exploited gaps in SaaS environments. Prioritize tools that automate the full access lifecycle.
- What does your next audit require? SOC 2, ISO 27001, and HIPAA all require continuous evidence of access governance and configuration control. Tools that generate that evidence automatically are worth more than tools that require manual evidence collection.
Also Read: SaaS security best practices: the governance controls your SaaS security tools need to enforce.
4. SaaS Security Best Practices for 2026
The tools above only work if your program is built to use them. These are the operational controls that separate organizations that close SaaS gaps from those that discover them after a breach.
- Run discovery continuously: A quarterly scan is already three months behind. Shadow IT and shadow AI grow daily. Effective programs treat discovery as a background process, not a periodic project.
- Automate access reviews: Manual certification cycles create governance theater. Workflows that trigger on role changes, contractor end dates, and offboarding events are the baseline standard in 2026.
- Deprovision at HR speed: Automated offboarding that fires the moment an HRIS system logs an exit, and covers every app, including those outside SSO, is a security control, not an IT convenience.
- Monitor configuration drift daily: A clean posture report from last quarter tells you nothing about today. Continuous SSPM closes the gap between audits, where most misconfigurations accumulate.
- Govern AI tool adoption before it governs you: Govern AI tool adoption before it governs you. Shadow AI is the fastest-growing unmanaged risk category.
Building AI security awareness into your SaaS tools evaluation process: vetting every AI app for data handling, permissions, and integration scope before approval is the control that closes the gap most programs are currently missing.
5. The Right SaaS Security Tools Won't Find Themselves
Every CISO on this list has a budget conversation, a board that wants fewer incidents, and an IT team stretched across a SaaS stack that grows faster than any one person can govern.
The organizations that got breached through SaaS in 2024 and 2025 mostly had security tooling in place. What they were missing was coverage of the SaaS layer specifically: the apps outside the IdP, the former employees with active credentials, the AI tools processing data nobody had reviewed.
If you're evaluating the best security compliance tools for SaaS companies right now, start with what you can't see. Book a demo with CloudEagle.ai to get a full inventory of your SaaS and AI environment in under 30 minutes.
6. Frequently Asked Questions
What is SaaS security?
SaaS security covers the tools and controls used to protect cloud applications and the data they contain, including app discovery, access governance, configuration monitoring, and threat detection across every app in use, sanctioned or not.
What are SaaS tools examples?
Common SaaS tools include Salesforce (CRM), Slack (communication), Workday (HR), GitHub (engineering), and AI tools like Claude and Gemini. The security challenge is the hundreds of additional apps employees adopt independently, often storing sensitive data outside IT's visibility.
What are the 4 types of security?
In a SaaS context: network security (data in transit), endpoint security (devices), identity security (access control), and application security (configurations, integrations, and data). SaaS security tools operate primarily in the identity and application layers, the ones traditional tooling leaves exposed.
Is Netflix a SaaS or PaaS?
Netflix is a consumer SaaS product. For enterprise security purposes, the distinction that matters is whether an app stores organizational data and requires formal access governance, which consumer services like Netflix do not.
.avif)
%201.svg)









.avif)




.avif)
.avif)




.png)





