HIPAA Compliance Checklist for 2025

Your legal team just forwarded an email. OCR opened an investigation. They want your current risk analysis, your access review records, and your breach notification timeline by next Friday.
You're the head of security. You start pulling the documents. Then you realize:
- Your last "official" risk analysis is from 2022, and it doesn't cover half the apps in your stack
- Three of your business associates have BAAs, but you can't remember the last time anyone reviewed their controls
- Two former employees still show up in your finance system's audit log, six months after they left
- Your incident response plan has a 60-day breach notification clock, but no one has tested how long it actually takes to escalate
This is the moment that ends most HIPAA investigations badly. Not the breach itself, but everything OCR finds when they look at how the breach was prevented, detected, and responded to.
In 2025 alone, OCR has collected over $8.2 million in civil monetary penalties across more than 20 HIPAA violation cases. The settlements that drove that number aren't unusual or sophisticated. They're ordinary security failures, the kind that exist quietly in most SaaS stacks until something forces them into the open.
This article walks through five HIPAA violation cases from 2025 and 2026 that your security team should know, what OCR penalized in each one, and what to fix before the same gaps end up in your investigation.
TL;DR
- OCR resolved 20+ HIPAA violation cases in 2025, with penalties ranging from $5,000 to $3 million
- Solara Medical Supplies ($3M) and Warby Parker ($1.5M) were the largest publicly announced HIPAA violation cases of the year
- The same three failures show up in nearly every settlement: missing or stale risk analyses, weak access controls, late breach notifications
- Business associates are now penalized at the same standard as covered entities, which puts every SaaS vendor handling PHI inside the enforcement perimeter
- Continuous compliance monitoring closes the gap between what your policies say and what your stack actually does
1. 5 HIPAA violation cases that defined 2025-2026
These five HIPAA violation cases cover the patterns OCR is enforcing right now. Phishing, credential stuffing, business associate ransomware, social media disclosure, and right of access. Each one ends with the SaaS security control that would have prevented it.
1. Solara Medical Supplies: $3 million for one phishing attack
Solara distributes diabetes care products direct-to-patient. Between April and June 2019, an attacker compromised eight employee email accounts through phishing, exposing the ePHI of 114,007 individuals.
Then it got worse. When Solara sent breach notification letters to affected patients, 1,531 of those letters went to wrong addresses, creating a second reportable breach inside the response to the first one.
OCR cited three failures: no compliant risk analysis, inadequate security measures, and late breach notifications. Solara settled for $3 million plus a two-year corrective action plan.

The lesson for SaaS security teams is simple: Email is your most exposed PHI surface, and most risk analyses don't cover it properly. If your assessment doesn't explicitly include identity, MFA, and email security across every PHI-handling user, you're carrying the same gap that drove one of the costliest HIPAA violation cases of the year.
2. Warby Parker: $1.5 million for a credential stuffing attack
This one surprises most people. Warby Parker, an eyewear company, was hit with a $1.5 million civil monetary penalty in February 2025 over a 2018 credential stuffing attack. They were a covered entity because they process vision insurance, which most teams reading this won't have considered.
OCR found the company hadn't conducted an accurate risk analysis, hadn't implemented security measures sufficient to reduce security risks, and hadn't reviewed system activity records.

If your platform touches insurance, pharmacy benefits, telehealth, wellness data, or any consumer health workflow, you may be a covered entity without realizing it. Plenty of HIPAA violation cases start with companies that didn't know they were inside HIPAA's scope until OCR told them they were.
3. BST & Co. CPAs: $175,000 for a business associate ransomware breach
The next case is one of the most important HIPAA violation cases for SaaS teams to study, because it confirms what most vendor risk programs still don't take seriously.
In December 2019, ransomware hit BST & Co., a New York accounting firm acting as a business associate to a covered entity client. The breach affected the PHI of roughly 170,000 individuals.
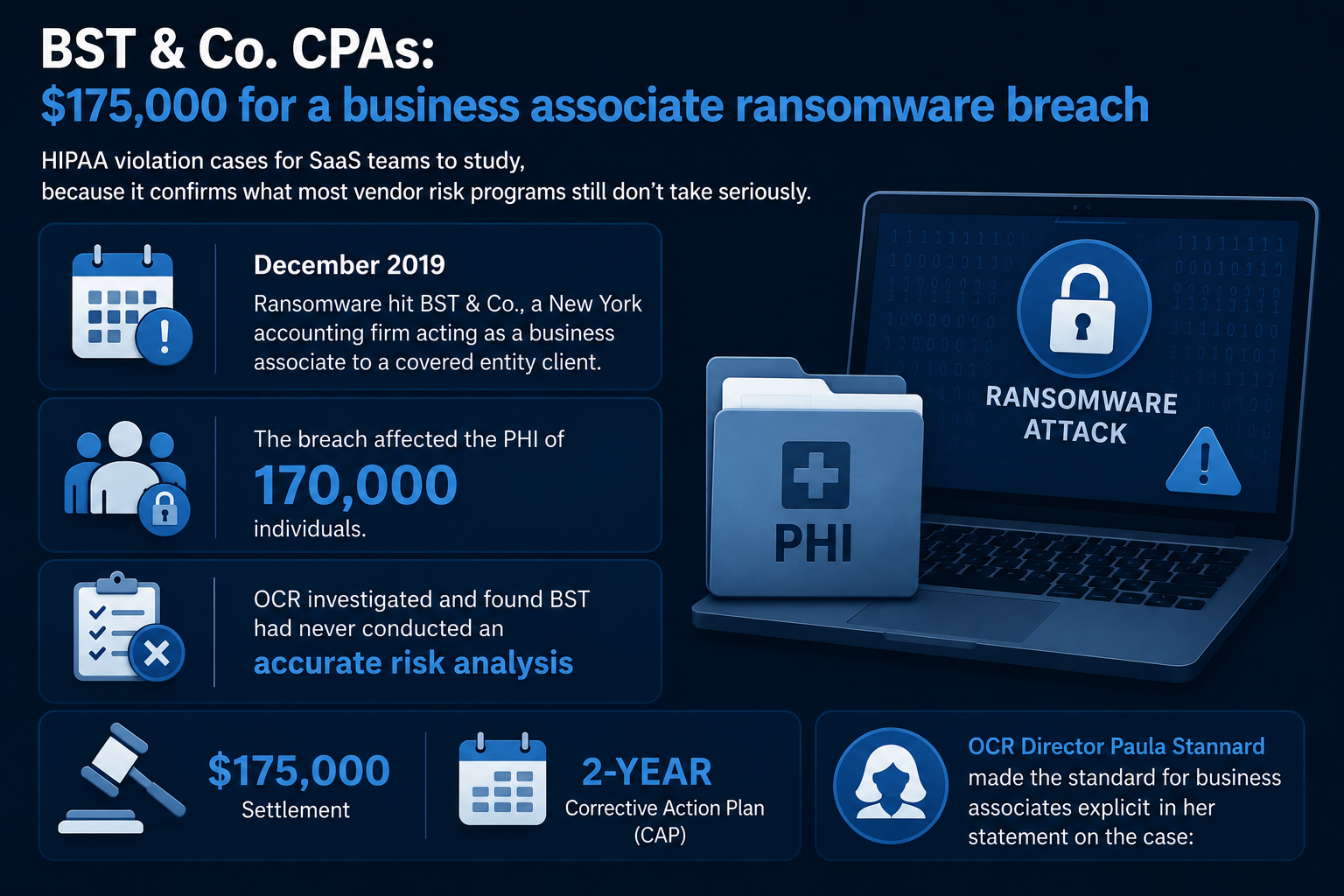
OCR investigated and found BST had never conducted an accurate risk analysis.
Settlement: $175,000 plus a two-year CAP. OCR Director Paula Stannard made the standard for business associates explicit in her statement on the case:
"A HIPAA risk analysis is essential for identifying where ePHI is stored and what security measures are needed to protect it. Completing an accurate and thorough risk analysis that informs a risk management plan is a foundational step to mitigate or prevent cyberattacks and breaches."
Paula Stannard, Director, HHS Office for Civil Rights
Translation: business associates are held to the same standard as covered entities. BST wasn't a hospital. It was a vendor sitting inside a healthcare client's data flow, and that was enough.
Most BAAs in your stack are signed once and forgotten. Vendor risk scoring, BAA tracking, and continuous control monitoring need to extend to every third party that touches PHI, including the ones nobody on your team has thought about in months.
4. Cadia Healthcare: $182,000 for posting patient stories on social media
Not every HIPAA violation case starts with a hacker. Five Delaware nursing homes operated by Cadia Healthcare ran a "Success Stories" marketing campaign between 2022 and 2024.
The marketing team pulled patient names, photos, diagnoses, and therapy details from medical records and posted them on Cadia's website and social media. None of those patients had given HIPAA-compliant authorization.

PHI of 150 patients was disclosed. Cadia hadn't sent breach notifications either. The settlement was $182,000 plus a two-year CAP requiring policy revisions, mandatory training for marketing personnel, and breach notifications to every affected patient.
The lesson here is about access governance: Marketing tools, CRMs, and content platforms inside your SaaS stack can leak PHI just as easily as a hacker can, and the people using them often don't know the data is regulated.
If your access governance stops at the IT and security teams, you have the same exposure Cadia did.
5. Concentra, Inc.: $112,500 for a 13-month delay in records access
The last of these HIPAA violation cases shifts from security to privacy. In December 2025, OCR announced its 54th Right of Access enforcement action. A patient made six requests for his medical records starting in February 2018 and didn't receive access until March 2019, more than a year later. Concentra paid $112,500.
This matters for SaaS security teams because right of access is a workflow problem before it's a legal one. If your platform can't surface and deliver PHI inside the 30-day window, you're exposed regardless of how strong your perimeter is.
Privacy violations get penalized just like security ones, and the operational fix sits inside your access controls and audit logs.

Real-Life HIPAA Violation Examples That Could Happen to You breaks down older patterns alongside these so you can see how the playbook has evolved.
2. What this means for SaaS security teams
Read those five HIPAA violation cases together and the same gaps surface every time. No current risk analysis. Access controls that exist in policy but not in practice. Business associate relationships that nobody's tracking. Detection and notification timelines that miss the 60-day clock.
Most security teams find out about these gaps during the audit. By then, the conversation with OCR has already started, and the goal shifts from compliance to damage control.
The fix is continuous, not annual. Why Continuous Compliance Beats Annual Audits explains why point-in-time controls fail under modern enforcement, but the operational shift comes down to four things your stack needs to do quietly, in the background, every day:
- Continuous risk analysis that tracks every app touching PHI as your stack changes, not just at audit time
- Access reviews that run quarterly without manual coordination, with orphaned and over-privileged accounts surfaced automatically
- Vendor risk monitoring that scores every business associate against HIPAA controls, including BAAs you signed years ago
- Real-time detection and escalation paths that start the 60-day notification clock the moment a breach is discovered, not when the investigation completes
This is what CloudEagle.ai gives security and IT teams in healthcare-adjacent companies. ICEYE, a CloudEagle.ai customer, used these capabilities to cut manual access reviews by 90% and reclaim 1,500+ hours annually. That's the bandwidth your team needs to actually answer auditor questions instead of reconstructing evidence after the fact.
“We went from spreadsheet-driven access reviews that took months to a fully automated, structured process. CloudEagle gave us complete visibility into users, roles, and permissions, while eliminating delays and reducing risk.” ~ Michal Lipinski, Director of IT & Security, ICEYE
For teams ready to formalize this further, How to Prove HIPAA Compliance Readiness to Auditors walks through what auditors expect to see and how to show it.
3. What to Fix Before OCR Knocks
Every settlement from 2025 and 2026 traces to a control gap that continuous compliance would have closed. The penalties differ in size. The corrective action plans differ in scope. The root causes don't. That's the through-line connecting every one of the HIPAA violation cases above.
OCR isn't asking new questions, but asking the same questions every time, and penalizing the teams that can't answer quickly with evidence.
The best time to fix your risk analysis was three years ago. The second-best time is before OCR asks for it. If you want to see how CloudEagle.ai helps SaaS security teams stay ahead of OCR enforcement, book a demo and we'll walk through the controls auditors are actually looking for in 2026.
4. Frequently asked questions
What is an example of a HIPAA violation case?
Solara Medical Supplies is a textbook example. A phishing attack compromised eight employee email accounts, exposing PHI of 114,007 individuals. OCR found Solara hadn't conducted a risk analysis, hadn't implemented adequate security measures, and hadn't issued timely breach notifications. The result was a $3 million settlement and a two-year corrective action plan.
What was the largest HIPAA violation?
Among publicly announced 2025 HIPAA violation cases, Solara Medical Supplies at $3 million was the largest. Warby Parker's $1.5 million civil monetary penalty came second. Historically, the largest HIPAA settlement remains Anthem at $16 million, paid in 2018 for a data breach that affected nearly 79 million people.
What is the maximum yearly fine for HIPAA violations?
The maximum annual penalty depends on the violation tier. After a 2019 OCR enforcement discretion notice, annual caps are $25,000 (Tier 1), $100,000 (Tier 2), $250,000 (Tier 3), and $1,500,000 (Tier 4), with annual inflation adjustments. Tier 4 applies to willful neglect that isn't corrected.
What are the top HIPAA violations in 2025?
The most common patterns across 2025 HIPAA violation cases were: failure to conduct an accurate risk analysis, inadequate security measures, late breach notifications, impermissible disclosures on social media, ransomware-related security gaps, lack of access controls and audit logs, and right-of-access delays.
Are business associates penalized differently than covered entities?
No. The BST & Co. settlement in August 2025 confirmed that business associates are held to the same Security Rule standards as covered entities. SaaS vendors, accounting firms, and any third party handling PHI carry full liability under HIPAA.
.avif)
%201.svg)









.avif)




.avif)
.avif)




.png)





