HIPAA Compliance Checklist for 2025

Healthcare enterprises are under constant pressure to safeguard patient data, yet HIPAA violations remain surprisingly common, even among leading providers, with HIPAA violation cases continuing to surface across the industry.
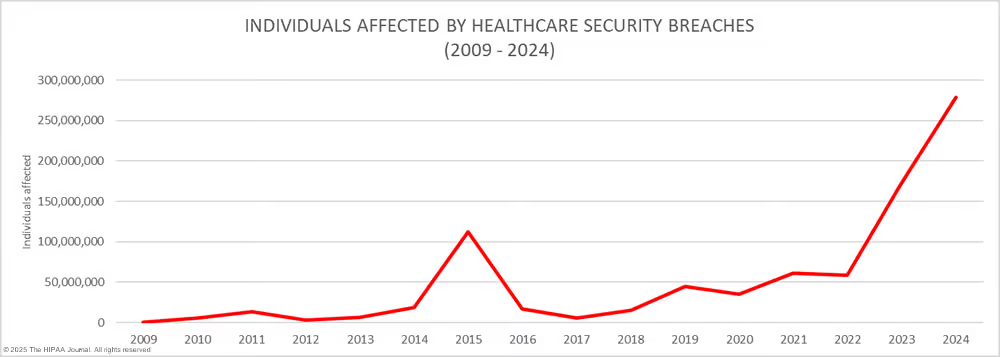
Since April 2003, the Office for Civil Rights (OCR) has received over 369,000 complaints related to HIPAA violations.
The consequences of a HIPAA violation can be serious, ranging from multi-million-dollar fines and legal action to reputational damage and loss of patient trust.
Let’s look at 10 real-life HIPAA violation examples, covering both everyday errors and high-profile cases, so you know what to watch out for and how to avoid them.
TL;DR
- HIPAA violations are more common than expected, and even small mistakes, like emailing patient data to the wrong person or not revoking access after offboarding, can lead to serious penalties. HIPAA violation cases have shown how easily data breaches occur, often without malicious intent.
- Real-life cases show the consequences including a 16 million dollar settlement at Anthem and celebrity snooping incidents at UCLA Health that damaged trust and triggered legal action.
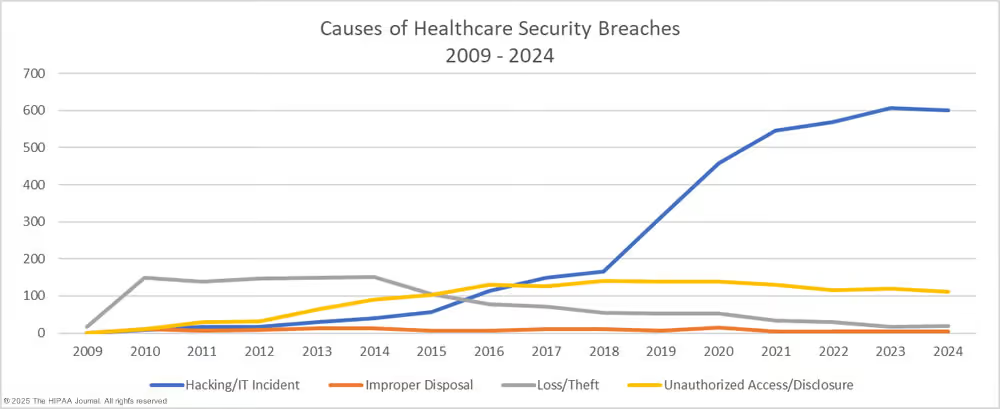
- Most violations happen due to human error such as weak access controls, improper data disposal, or lack of employee training.
- Staying compliant requires proactive safeguards like encryption, timely offboarding, role-based access control, and regular HIPAA training.
- CloudEagle.ai helps prevent HIPAA violations by centralizing access, automating user provisioning, enforcing least privilege, and detecting shadow IT in real-time. By using this platform, you can mitigate the risks that lead to HIPAA violation cases.
1. What Is HIPAA, and What Counts as a HIPAA Violation?
HIPAA (Health Insurance Portability and Accountability Act) is a US federal law that protects Protected Health Information (PHI) and sets rules for how healthcare providers, insurers, and business associates handle patient data.
A HIPAA violation happens when a covered entity or business associate fails to safeguard PHI, whether it’s accidental (human error) or intentional (unauthorized access).
HIPAA enforcement largely revolves around three core rules:
- Privacy Rule: limits who can access and disclose PHI
- Security Rule: requires safeguards for electronic PHI (ePHI) like encryption, access controls, and audit logs
- Breach Notification Rule: requires notification to affected individuals (often within 60 days) after discovery of a breach
Common HIPAA violation categories include:
- Unauthorized access (employee snooping)
- Improper disclosure (unsecured email, public conversations)
- Weak security controls (unencrypted devices, misconfigured storage)
- Vendor risk (missing BAAs)
- Delayed breach reporting
A. How are HIPAA violations discovered?
Most HIPAA violations are discovered through audits, complaints, whistleblowers, or OCR investigations and increasingly through automated detection and access logs.
- Access Monitoring: Maintain comprehensive activity logging and conduct quarterly access reviews to identify unauthorized permissions.
- Security Automation: Deploy Data Loss Prevention (DLP) and SIEM systems to track PHI movement and receive real-time threat alerts.
- Reporting Channels: Establish confidential incident hotlines to encourage staff to report potential HIPAA violation examples anonymously.
- Audits and Investigations: Use routine compliance reviews and vendor notifications to uncover security gaps before they escalate into large-scale breaches.
B. What are the most common HIPAA violations to avoid?
- Unauthorized Access to Patient Records: Employees accessing medical records without legitimate work reasons, such as celebrity snooping or curiosity about colleagues.
Prevention: Implement role-based access controls and continuous access monitoring to flag unusual activity.
- Unsecured PHI on Lost or Stolen Devices: Laptops, smartphones, or USB drives containing unencrypted patient data are lost or stolen.
Prevention: Mandate full-disk encryption on all devices storing PHI and enforce remote wipe capabilities.
- Missing Business Associate Agreements (BAAs): Sharing PHI with vendors or third parties without signed BAAs in place.
Prevention: Establish a vendor management process requiring BAAs before any PHI access.
- Inadequate Employee Training: Staff unaware of HIPAA requirements, leading to accidental violations like improper disclosures.
Prevention: Conduct annual HIPAA training with real-life scenario testing for all personnel.
- Improper Disposal of PHI: Throwing patient records, prescription labels, or medical documents in unsecured trash without shredding.
Prevention: Use certified shredding services and secure disposal bins for all PHI.
- Failure to Revoke Access After Offboarding: Former employees retaining system access to patient data after departure.
Prevention: Automate offboarding workflows to immediately deprovision access upon termination. - Sharing PHI via Unsecured Channels: Emailing or texting patient information without encryption or sending to wrong recipients.
Prevention: Use HIPAA-compliant secure messaging platforms and verify recipients before sending. - Delayed Breach Notification: Failing to notify affected individuals and HHS within the required 60-day window after discovering a breach.
Prevention: Establish an incident response plan with clear timelines and designated breach coordinators.
2. 10 Common HIPAA Violation Examples (Real Scenarios + Prevention Tips)
Most HIPAA violations fall into the same repeat patterns: unauthorized access, improper disclosure, weak security controls, missing vendor agreements, and delayed breach response.
Here are 10 real scenarios showing exactly how they happen and how to stop them.
1. Lost or Stolen Devices with Unencrypted Data
Laptops, phones, and USB drives go missing all the time. When they contain unencrypted patient data, that's an immediate HIPAA problem.
Lifespan Health System learned this the hard way, paying $1.04 million after an unencrypted laptop was stolen from an employee's car.
- Encrypt every device that touches PHI, no exceptions
- Enable remote wipe so stolen devices can be neutralized instantly
2. Unauthorized Access by Employees
Curiosity isn't a valid reason to open a patient's file. Checking records of a colleague, a neighbor, or a celebrity, even briefly, is a clear HIPAA violation and one of the most common ones at that.
Role-based access controls and access monitoring are the two things that catch and prevent this consistently.
3. Sending PHI to the Wrong Recipient
One wrong email address, one misdirected fax. That's all it takes to expose sensitive patient data to someone who was never supposed to see it.
Always verify recipients before sending anything PHI-related, and use encrypted, HIPAA-compliant channels for transmission.
4. Discussing Patient Info in Public Areas
Hallways, elevators, and cafeterias are not private spaces. Talking about a patient's condition or test results where others can overhear is a violation, even if it's accidental.
Train staff to handle patient conversations only in secure, private settings and to stay aware of their surroundings at all times.
5. Sharing PHI on Social Media
Photos, videos, or even vague stories about patient care can identify someone without ever using their name. That makes it a potential HIPAA violation regardless of intent.
The rule is simple: nothing about patient care goes on social media without explicit written consent from the patient.
6. Lack of Business Associate Agreements (BAAs)
Sharing PHI with a third-party vendor without a signed BAA in place is a textbook HIPAA violation. The BAA legally binds the vendor to protecting that data, without it, you're exposed if something goes wrong.
One of the most notable examples of violating HIPAA occurred in 2015, when the Center for Children’s Digestive Health (Illinois) paid $31,000 for sharing PHI with a vendor without a signed Business Associate Agreement, violating HIPAA’s legal safeguards.
7. Improper Disposal of PHI
Tossing patient records in the trash or discarding old devices without wiping them is a serious violation. PHI has to be properly destroyed, not just thrown away.
One of the best examples of breaking HIPAA occurred when New England Dermatology P.C. (Massachusetts) was fined $300,640 after improperly discarding specimen containers labeled with PHI in unsecured dumpsters.
Use certified shredding services and ensure all electronic devices are fully wiped before disposal.
8. Ransomware Attack Due to Weak Security
When hackers lock or steal patient records, it's not just a cybersecurity incident, it's a HIPAA violation if the right protections weren't in place.
Healthcare organizations need active risk assessments, strong endpoint security, and regular vulnerability checks. Waiting for an attack to happen is not a compliance strategy..
9. Delayed Breach Notification
HIPAA gives you 60 days from discovering a breach to notify affected individuals, HHS, and in some cases, the media. Miss that window, and you're looking at additional fines on top of the original violation.
Have an incident response plan ready before you need it, with clear owners and timelines built in.
10. Overheard Voicemail or Phone Conversations
Leaving a detailed voicemail with PHI or taking a patient call in a shared space can lead to unauthorized disclosure without anyone realizing it happened.
Keep patient calls to private areas and keep voicemails minimal, name and callback number, not a full medical update.
3. How CloudEagle.ai Helps Prevent Access-Driven HIPAA Violations?
HIPAA compliance starts with controlling who has access to what. If employees have the wrong access, or if former staff still have access, it puts your organization at risk.
CloudEagle.ai makes access management easy. It gives IT and compliance teams full visibility and automates access across all your apps and systems.
With 500+ integrations, it connects to your HR, identity, and IT tools to update access in real time based on role or employment changes.
Here’s how CloudEagle.ai helps prevent HIPAA violations:
A. Centralized Access Management
CloudEagle.ai brings all user access data into one place, offering a single, unified dashboard to manage access rights.
No more relying on outdated spreadsheets or manual tracking, which often lead to errors and oversights.
This comprehensive view enables IT and compliance teams to quickly identify unauthorized access, revoke permissions where necessary, and ensure only the right people have access to protected health information (PHI), helping you proactively prevent access-related HIPAA violations.
B. Enforce Least Privilege Access
CloudEagle.ai helps enforce least privilege policies by automatically reviewing user permissions, flagging over-provisioned accounts, and removing unnecessary access credentials.
This ensures that sensitive health information remains protected and that organizations reduce the window of opportunity for unauthorized exposure.
Consistent access reviews and automated controls are key to preventing these kinds of security incidents.
C. Automated Onboarding and Offboarding
HIPAA violations often occur when access isn’t removed after employees leave, as seen in the Memorial Healthcare System case. CloudEagle.ai automates both onboarding and offboarding processes.
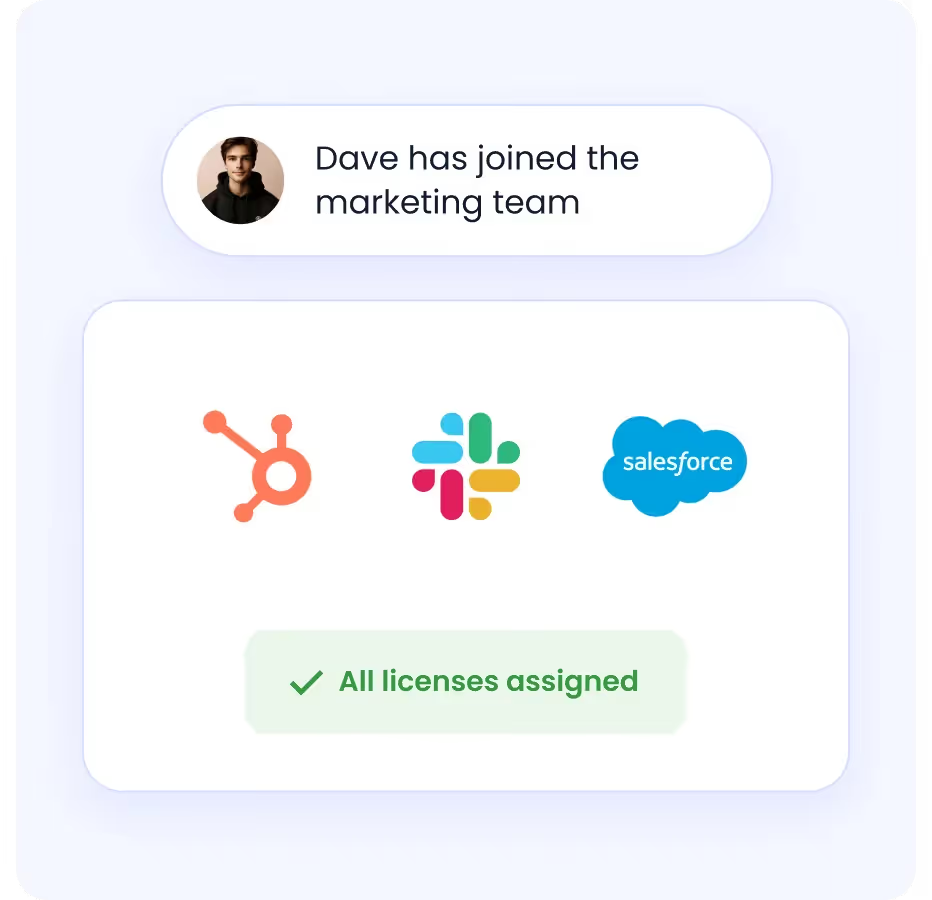
As soon as an employee joins or exits, access to protected health information (PHI) and sensitive systems is automatically granted or revoked based on their job role and employment status.
This ensures there are no unnecessary delays or manual steps, significantly reducing the risk of unauthorized access and potential HIPAA violations related to improper handling of PHI.
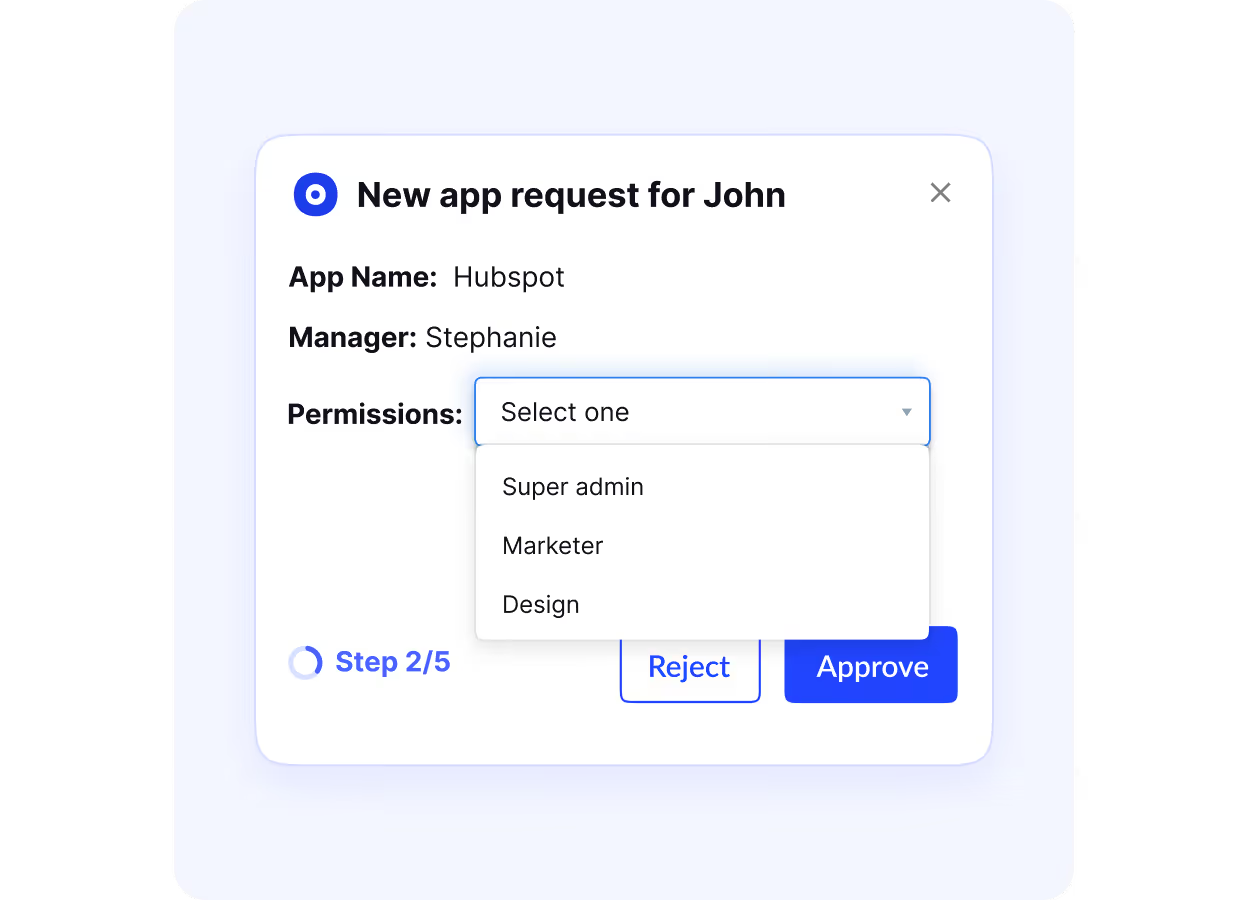
D. Role-Based Access Controls (RBAC)
Implementing robust RBAC access control policies is essential for preventing common HIPAA violations related to unauthorized data access.
CloudEagle.ai streamlines this process by allowing organizations to assign access privileges precisely according to each employee’s job responsibilities, helping ensure sensitive health information remains protected.
- With RBAC, employees are granted permissions that closely match their job functions, making it less likely for individuals to access confidential patient data they do not need.
- This structured approach to access control minimizes the chances of inappropriate data exposure, especially during events like staff promotions, team transfers, or changes in project assignments.
- Properly configured RBAC supports HIPAA compliance by ensuring only authorized personnel can view or modify protected health information, reducing the risk of accidental or intentional HIPAA violations.

E. Just-In-Time (JIT) Access
Sometimes, employees or contractors need temporary access to specific tools, sensitive applications, or patient data to perform their job duties or complete one-off projects.
Instead of granting permanent access, which increases risk and can lead to potential HIPAA violations, CloudEagle.ai supports Just-In-Time (JIT) access.
With JIT access, users can submit a request for access for a defined, limited period, ensuring they only have the minimum access necessary and only when it’s actually needed.
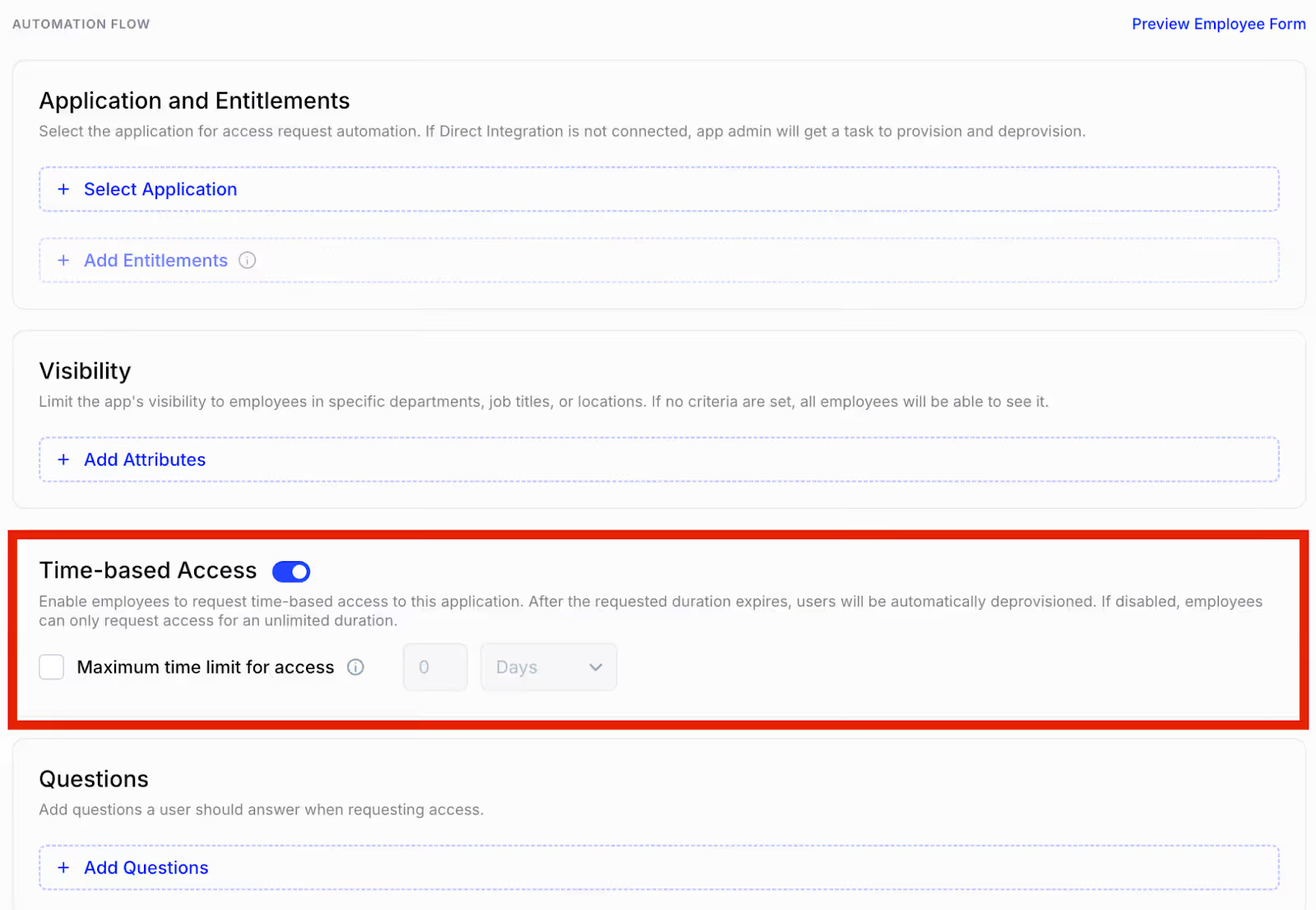
Once the task is done, access is automatically revoked. This approach minimizes standing access and reduces the chances of misuse or policy violations.
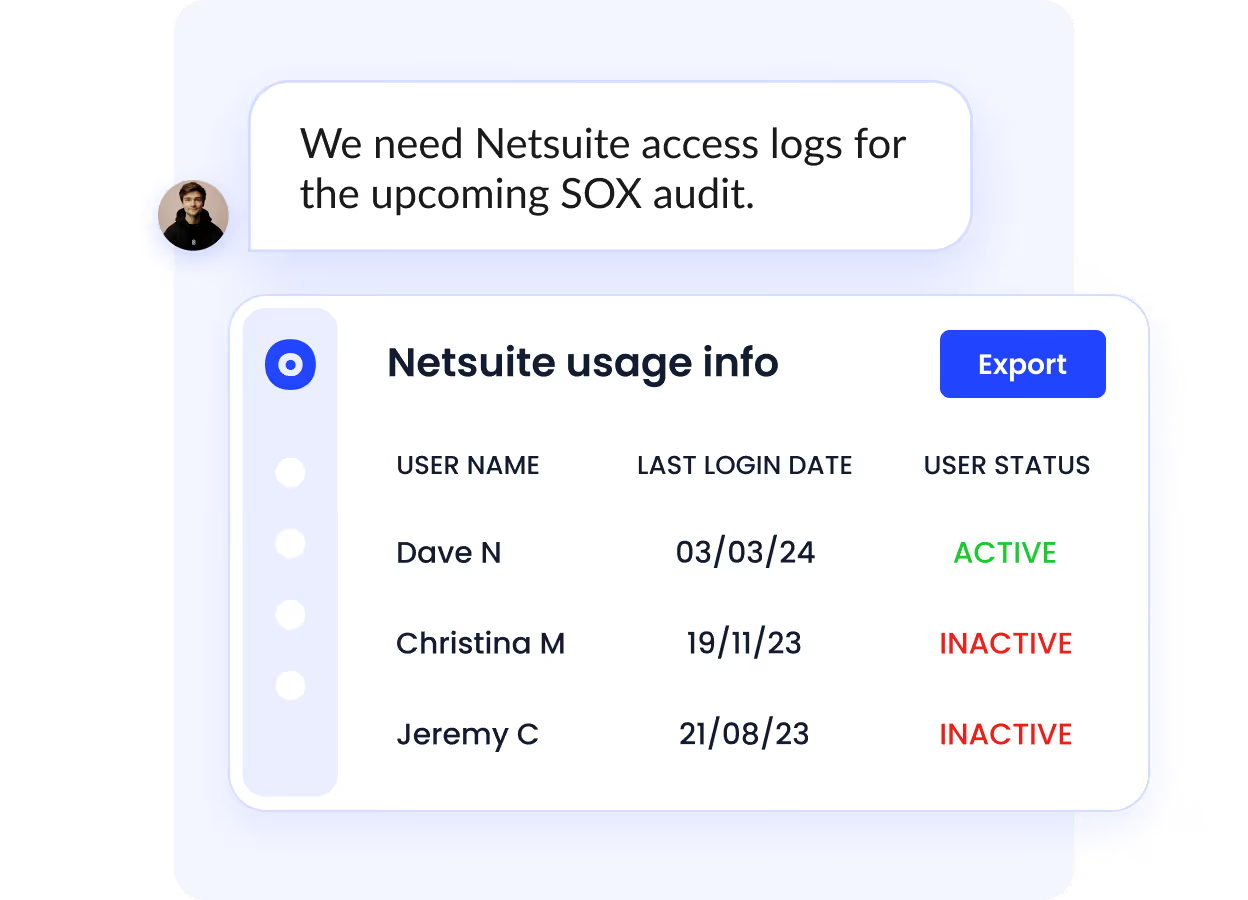
F. Audit-Ready Activity Logs and Reports
CloudEagle.ai tracks all access activity in real time and automatically generates comprehensive logs and detailed reports that are ready for compliance audits.
These audit-ready records allow you to present regulators with clear documentation showing exactly when and how access decisions were made.
This includes who accessed which systems, what changes were performed, and by whom, making it much easier to demonstrate full compliance with HIPAA requirements and avoid costly penalties for violations.
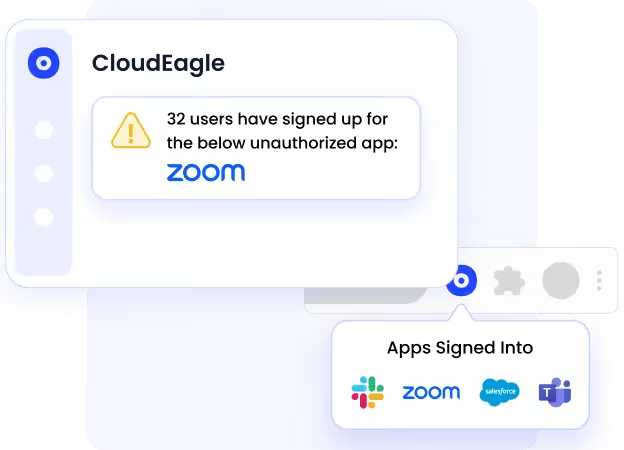
G. Continuous Access Monitoring
HIPAA compliance isn’t a one-time task. CloudEagle.ai continuously monitors user activity across your SaaS stack.
If someone accesses a system they shouldn’t, or if unauthorized third-party tools are connected, you’ll receive real-time alerts. This helps you respond quickly, before minor compliance issues turn into major violations.
H. Shadow IT Detection
Sometimes, employees use unapproved tools to store or share protected health information (PHI), which creates compliance risks.
CloudEagle.ai automatically detects shadow IT usage, so you can block risky apps and ensure all tools meet security and compliance standards.
I. Policy Enforcement and Access Reviews
With CloudEagle.ai, you can create and enforce custom access policies tailored to your organization’s unique HIPAA compliance obligations and internal security protocols, giving you granular control over sensitive data access.
CloudEagle.ai helps organizations minimize the risk of HIPAA violations by automating and optimizing user access review workflows, ensuring that permissions stay accurate as roles change, and reducing the incidence of unauthorized access to protected health information (PHI).
- Healthcare providers: Ensure only authorized staff have access to patient data, minimizing risks of PHI exposure.
- IT and compliance teams: Automate periodic access reviews, eliminating manual errors and reducing the administrative burden.
- Organizations experiencing frequent role changes: Continuously monitor and update access rights when employees transition roles, preventing access creep and outdated permissions.
- Businesses managing sensitive health information: Proactively prevent unauthorized access, maintain a strong compliance posture, and avoid common HIPAA violation scenarios.
By automating access reviews and removing obsolete permissions, CloudEagle.ai supports your efforts to stay compliant and safeguards against one of the leading causes of HIPAA violations.
Learn more about regular access reviews.
4. How Serious Is a HIPAA Violation? (Penalties, Consequences, and Real Risk)
A HIPAA violation occurs when protected health information (PHI), including patient names, medical records, and Social Security numbers, is mishandled or exposed.
The severity of the breach and the speed of reporting determine the resulting penalties.
Common HIPAA violation examples and their consequences include:
- Financial Penalties: Fines ranging from a few thousand to several million dollars.
- Legal Consequences: Civil lawsuits from patients and criminal charges for willful negligence or jail time.
- Reputational Damage: Significant loss of patient trust and public credibility.
- Security Failures: Accidental errors like using unencrypted devices, sending data to the wrong recipient, or failing to secure shared systems.
To mitigate these risks, healthcare organizations must prioritize comprehensive staff training, strict data policies, and robust encryption protocols.
A. What are the consequences of violating HIPAA?
- Financial Penalties: Fines vary by severity, ranging from $100 per incident to $1.9 million annually across four violation tiers.
- Operational Impact: Organizations face mandatory corrective action plans, increased OCR audits, and high remediation costs.
- Individual Consequences: Responsible employees may be terminated or face civil and criminal legal prosecution.
- Reputational Damage: Data breaches lead to a loss of patient trust, increased patient churn, and negative media exposure.
B. What are the penalties for HIPAA violations?
HIPAA penalties depend on the severity of the violation. Civil fines range from $100 to $50,000 per violation, escalating with willful neglect or repeated failure to resolve issues, with annual maximums up to $1.9 million.
Lower penalties apply to unintentional violations, while deliberate or uncorrected violations face the highest fines.
Criminal charges can bring up to $250,000 in fines and 10 years in prison, especially if PHI is misused for personal gain or harm.
6. What Is The Largest HIPAA Violation in History?
One of the most famous HIPAA violation cases occurred when Anthem Inc., a major health insurance company, suffered a cyberattack that exposed the electronic PHI of nearly 79 million individuals. This breach is considered one of the largest HIPAA violations in history.
Details:
- Hackers gained unauthorized access through phishing emails sent to employees.
- The attackers obtained names, birthdates, medical IDs, Social Security numbers, addresses, and employment information.
- The breach went undetected for several months, increasing its impact.
Violation:
- Failure to implement appropriate security measures.
- Inadequate risk analysis and failure to monitor information system activity.
Outcome:
- $16 million settlement with the U.S. Department of Health and Human Services (HHS).
- Multiple class-action lawsuits, costing millions more.
- Anthem also agreed to take corrective actions, including enhanced cybersecurity measures.
7. Conclusion
HIPAA violations aren't just distant headlines or cautionary tales; they’re immediate, costly threats to any healthcare provider, pharmacy, or contractor.
Compliance is never optional; if you handle patient data, you’re legally accountable for its security at every touchpoint. You can effectively mitigate these risks by focusing on:
- Enforcing granular access controls to ensure data is only seen by those who need it.
- Securing your SaaS stack to prevent accidental leaks through third-party apps.
- Building a rigorous culture of accountability and regular staff training.
Stop reacting to security gaps and start closing them before they lead to a breach.
Explore how CloudEagle helps healthcare teams reduce access risk and stay audit-ready.
Frequently Asked Questions
1. What is the full form of HIPAA?
HIPAA stands for Health Insurance Portability and Accountability Act of 1996.
2. What are HIPAA rules for?
HIPAA rules are designed to protect the privacy, security, and confidentiality of individuals’ health information and to standardize electronic healthcare transactions.
3. What are the three key points of HIPAA?
- Privacy Rule – Controls how PHI is used and disclosed.
- Security Rule – Requires safeguards for electronic PHI (ePHI).
- Breach Notification Rule – Mandates disclosure of data breaches.
4. Is saying a patient's first name a HIPAA violation?
Not necessarily. Using a patient’s first name alone is generally not a violation unless it is combined with other identifiable information or used in a way that discloses PHI inappropriately.
5. What is a Tier 4 HIPAA violation?
A Tier 4 violation involves willful neglect with no effort to correct the issue. It carries the highest penalties, up to $1.9 million per violation (based on recent penalty tiers).
6. What patient right is most often violated?
The right to privacy of their health information is the most commonly violated, especially when PHI is accessed or shared without consent.
7. What is the best example of a HIPAA breach?
One of the biggest HIPAA breaches was the 2015 Anthem Inc. cyberattack, where hackers accessed the PHI of nearly 79 million people, leading to a $16 million settlement.

%201.svg)









.avif)




.avif)
.avif)




.png)





