HIPAA Compliance Checklist for 2025

96% of organizations favor a zero-trust approach, and 81% plan to implement zero-trust strategies within the next 12 months.
So why are breaches still accelerating?
Here is the honest answer.
Most organizations are implementing zero-trust security at the network layer and calling it a day. They have ZTNA, they have MFA, they have SSO. And then one of their employees signs up for an AI tool using a personal email, connects it to a corporate data source via OAuth, and that entire zero-trust architecture has a blind spot nobody planned for.
This is not another vendor list. It is a buying framework that helps you understand which zero trust solutions solve which problems, and where most programs leave gaps they do not know about.
TL;DR
1. What Zero Trust Solutions Actually Need to Cover in 2026
Most buyers think of zero trust as a single product decision. It is not. It is a layered architecture, and different vendors solve different layers.
You are probably already working on Layers 1 and 2. The gap most organizations have is Layers 3 and 4, and that is exactly where breaches originate.
Here is the reality: most zero trust programs are built around Layers 1 and 2. Layers 3 and 4 are where attackers actually operate.
2. 8 Best Zero Trust Solutions for 2026
1. CloudEagle.ai
Most zero-trust platforms secure the network and identity layers. CloudEagle.ai secures the SaaS and AI layer underneath, where shadow AI, excessive privileges, and unreviewed access often operate outside traditional security controls.
CloudEagle.ai is an AI-powered SaaS Management, Security, and Identity Governance platform that gives enterprises a unified command center to discover, secure, govern, and optimize both human and non-human identities across their entire SaaS and AI ecosystem.
Shadow AI and Shadow IT Discovery
CloudEagle.ai automatically discovers SaaS and AI tools by correlating SSO data, browser signals, Zscaler logs, CrowdStrike signals, and finance integrations. This surfaces shadow AI, unauthorized SaaS apps, personal AI accounts, and OAuth-connected tools operating outside approved workflows.

- Complete SaaS and AI inventory, including tools outside SSO
- Detects shadow AI, duplicate copilots, and risky applications automatically
- Flags free trials, unauthorized purchases, and unmanaged app usage
- Visibility into adoption by user, team, and department
Excessive Privileged Users
CloudEagle continuously monitors privileged access across SaaS applications and flags users with unnecessary or elevated permissions before they become compliance or security risks.

- Detects over-privileged users, orphaned accounts, and permission mismatches
- Applies least-privilege governance across SaaS and AI applications
- Automates access reviews and privilege remediation workflows
- Just-in-time access ensures elevated permissions expire automatically
User Access Reviews
CloudEagle automates continuous user access reviews so enterprises can reduce reviewer fatigue, eliminate rubber-stamping, and stay audit-ready year-round.
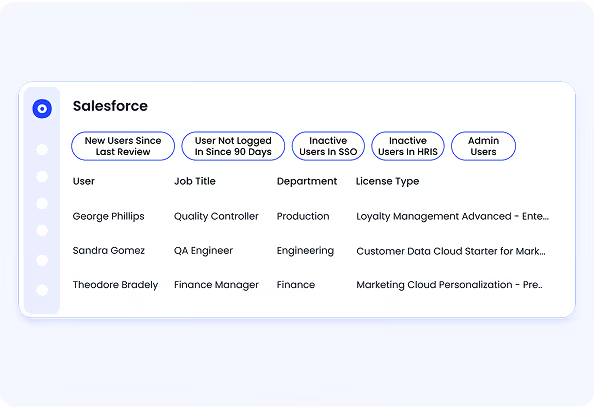
- Continuous access reviews replace slow quarterly certification cycles
- Flags high-risk users and ex-employees automatically
- Auto-attaches deprovisioning evidence for audit readiness
- Centralized dashboards give reviewers visibility into roles, permissions, and risk context
Trusted by enterprises like RingCentral, Rec Room, and ICEYE, CloudEagle supports 500+ direct integrations and helps enterprises operationalize governance across their SaaS and AI ecosystem.
Pricing: Enterprise pricing based on user count and integrations.
2. Okta
Okta is the default choice for identity-led zero trust access management. It handles SSO, MFA, lifecycle management, and conditional access policies across a broad ecosystem of applications.
- Key features: Adaptive MFA, SSO across 7,000+ app integrations, lifecycle management, Okta Verify device trust, identity threat protection
- Strengths: Deep integration ecosystem, strong developer tooling, mature conditional access policy engine
- Limitations: Primarily covers sanctioned apps behind SSO. Shadow apps and non-SSO access are outside its visibility.
- Pricing: Workforce Identity starts at $2/user/month for SSO. Advanced plans with lifecycle management from $4/user/month.
3. Microsoft Entra ID
Microsoft Entra ID (formerly Azure AD) delivers SSO, conditional access, identity protection, and Privileged Identity Management within the Microsoft stack. For organizations already on Microsoft 365, it is often the path of least resistance.
- Key features: Conditional access policies, Privileged Identity Management, identity protection risk scoring, SCIM provisioning, verifiable credentials
- Strengths: Deep Microsoft ecosystem integration, strong compliance reporting, broad enterprise scale
- Limitations: Coverage is strongest within Microsoft-connected apps. SaaS governance and shadow AI discovery require additional tooling.
- Pricing: Entra ID P1 at $6/user/month. P2 with identity protection and PIM at $9/user/month.
4. Zscaler Zero Trust Exchange
65% of organizations plan to replace VPN services within the year, a 23% jump from prior findings. Zscaler is where most of them are going. Its Zero Trust Exchange proxies all traffic through the cloud, connecting users directly to applications without exposing the network.
- Key features: ZTNA for private application access, SSL inspection, cloud firewall, data loss prevention, bandwidth optimization
- Strengths: Market-leading ZTNA capability, strong performance at scale, deep integration with Okta and CrowdStrike
- Limitations: Network and access layer only. Does not govern SaaS entitlements, shadow apps, or non-human identities.
- Pricing: Custom enterprise pricing. Typically starts at $60,000+ annually for mid-sized deployments.
5. Palo Alto Prisma Access
Prisma Access delivers ZTNA, secure web gateway, CASB, and firewall-as-a-service in a single cloud-delivered platform. It adds AI-powered threat prevention on top of the network access controls that Zscaler provides.
- Key features: AI-powered threat prevention, ZTNA, CASB, SWG, unified SASE platform, SD-WAN integration
- Strengths: Combines network security and access control, strong threat intelligence, good for complex hybrid environments
- Limitations: Complex to configure and maintain, expensive, limited SaaS governance depth beyond CASB capabilities
- Pricing: Custom enterprise pricing. Typically $100,000+ annually for full platform deployments.
6. Cloudflare One
Cloudflare One delivers ZTNA and SSE through Cloudflare's global edge network. It is faster to deploy than Zscaler or Palo Alto and tends to perform better for globally distributed teams because of Cloudflare's network footprint.
- Key features: ZTNA, secure web gateway, email security, cloud access security broker, Magic WAN
- Strengths: Fastest ZTNA deployment in this list, strong performance for distributed teams, and competitive pricing
- Limitations: CASB capabilities are less mature than Zscaler. Limited SaaS governance and entitlement management.
- Pricing: The Zero Trust plan starts free for up to 50 users. Business plans from $7/user/month.
7. CrowdStrike Falcon
CrowdStrike brings zero trust principles to the endpoint and identity layer through behavioral analysis, threat detection, and identity protection. It detects compromised credentials and privilege escalation in real time, which most identity providers do not.
- Key features: AI-driven behavioral endpoint detection, identity threat protection, privileged access monitoring, threat intelligence correlation
- Strengths: Best-in-class threat detection accuracy, strong identity risk signals, and integrates well with Okta and Zscaler
- Limitations: Primarily threat detection, not entitlement governance. Does not cover SaaS app visibility or shadow AI.
- Pricing: Falcon Go starts at approximately $15/endpoint/month. Enterprise bundles vary significantly.
8. Veza
Veza maps authorization relationships across your entire environment, answering "who has access to what and what can they do with it" at the entitlement level, not just the authentication level. It is the tool that operationalizes least privilege at scale.
- Key features: Authorization graph across cloud, SaaS, and data systems, access reviews, SoD violation detection, and non-human identity visibility
- Strengths: Deepest authorization visibility in this list, strong for data governance and compliance use cases, good non-human identity coverage
- Limitations: Focused on visibility and governance, not threat detection or network access. Requires pairing with Layer 1 and 2 tools.
- Pricing: Custom enterprise pricing. Typically starts at $50,000+ annually.
3. Why Most Zero Trust Programs Fail at the SaaS Layer
You have probably been told that MFA is the foundation of zero trust. That is partially true. But here is what nobody explains clearly enough.
MFA proves who you are. It says nothing about what you should be allowed to do, what SaaS apps you have quietly connected to, or what permissions accumulated on your account over the past two years of role changes. That is the authorization problem, and it is a completely separate layer.
Authentication Is Not Authorization
Think about someone who moved from engineering to product management last year.
Their Okta account still works. MFA is enabled. Nothing looks risky on the surface.
But behind the scenes, they may still have:
- Write access to production systems
- Admin rights in old SaaS tools
- API keys tied to workflows nobody reviews anymore
This is the part most zero-trust programs miss.
Authentication answers: Who is this user?
Authorization answers: Should they still have this level of access?
Those are not the same thing.
SaaS Sprawl Creates Access IT Cannot See
Your identity provider only sees the applications connected to it.
It does not see:
- The AI tool was purchased quietly on a company card
- The shadow SaaS app adopted by a department
- The OAuth integration connected to internal systems months ago
And that is where visibility starts breaking down.
SaaS adoption moves faster than governance. Access keeps accumulating while IT assumes control still exists.
In reality, large parts of the environment are operating outside the identity layer entirely.
Non-Human Identities Are the Growing Blind Spot
Most enterprises now have more non-human identities than human users, and most security teams do not realize how much access they actually hold.
API keys, service accounts, integrations, and AI agents often run with elevated permissions but rarely get reviewed properly. So even if employee access looks clean, machine access may still be operating quietly in the background.
4. How We Evaluated These Zero Trust Solutions
Every platform below was assessed against criteria that reflect all four layers, not just the ones vendors like to highlight:
- ZTNA capability for replacing legacy VPN infrastructure
- Identity governance and conditional access depth
- SaaS visibility, including shadow app and shadow AI discovery
- Authorization and entitlement controls, least privilege enforcement
- AI and non-human identity governance
- Compliance alignment and audit evidence generation
- Integration breadth and enterprise scalability
📖 Worth a Read: Shadow AI in Financial Services: How Finance Teams Are Introducing Unseen Risk
5. How to Build Your Zero Trust Architecture Without Buying Everything at Once
The mistake most teams make is trying to solve all four layers simultaneously.
You will buy too much, implement too little, and burn out your team. Here is the sequence that actually works:
Step 1: Start with identity: Enforce SSO and MFA across every sanctioned application before anything else. This is your foundation. Without it, the other layers do not hold.
Step 2: Replace VPN with ZTNA: Once identity is solid, move remote access from VPN to zero-trust network access. This closes the network perimeter exposure that legacy VPNs create.
Step 3: Enforce least privilege: Audit who actually has access to what. Run access reviews. Remove permissions that accumulate from role changes and project work. This is where CloudEagle's access governance capabilities fit.
Step 4: Discover shadow apps and AI tools: Find everything employees are using outside your provisioned stack. You cannot govern what you cannot see. This step usually surfaces more than teams expect.
Step 5: Govern non-human identities: Map every API key, service account, and AI agent. Review them with the same rigor you apply to human accounts. Most are over-privileged and under-monitored.
Step 6: Generate continuous compliance evidence: Move from point-in-time audits to continuous monitoring. Every access decision should be logged. Every policy change should be documented. Auditors should never surprise you
Conclusion
The best zero-trust solutions in 2026 are not the ones with the most features. They are the ones that close the gaps traditional identity and network controls still leave open.
Most organizations already have MFA, ZTNA, and identity controls in place. What they are missing is governance beyond the IdP: visibility into shadow AI, excessive privileges, SaaS access, and non-human identities operating outside approved workflows.
Zero trust in 2026 extends beyond networks and logins. It requires continuous governance across the SaaS and AI layer as well.
CloudEagle.ai helps enterprises extend zero trust into the SaaS and AI layer with continuous visibility, least-privilege governance, and real-time control over shadow AI and unmanaged access.
Book a demo to see which apps, identities, and AI tools your current zero-trust stack still cannot see.
Frequently Asked Questions
- What are zero-trust solutions?
Zero-trust solutions verify every user, device, and application before granting access. They typically cover network access, identity verification, authorization, and SaaS governance. - Which zero-trust platform is best for enterprises?
There is no single platform that covers every layer of zero trust. Enterprises usually combine tools like Zscaler for ZTNA, Okta for identity, and CloudEagle.ai for SaaS and AI governance. - How does zero trust apply to SaaS applications?
Zero trust for SaaS goes beyond SSO and MFA. It includes managing SaaS permissions, discovering shadow apps, governing OAuth integrations, and continuously reviewing access. - What is zero trust access management?
Zero trust access management continuously validates user access based on identity, context, and least privilege instead of assuming trust after login. - Why do most zero-trust programs fail in SaaS environments?
Most programs secure authentication but miss authorization. Shadow SaaS apps, stale permissions, API keys, and AI agents often operate outside traditional identity controls.

%201.svg)









.avif)




.avif)
.avif)




.png)





