HIPAA Compliance Checklist for 2025

Quick question: do you actually know every app your employees are accessing right now?
Not the ones behind SSO. Not the ones IT approved. Every app. Including the one a sales rep signed up for with a personal Gmail, the AI tool three engineers are using to summarize internal docs, and the contractor account that's been active for four months after the project ended.
If the answer is "probably not," you're not alone. And you're definitely not fine.
Identity is the top attack vector in 2026. 73% of security and IT leaders rank it as a top priority, yet most enterprises still rely on tools built for a simpler world.
The best identity security platforms in 2026 don't just handle SSO and MFA. They govern every identity, every app, and every access point, including the ones nobody officially approved. This list compares 10 of them. No fluff, no marketing speak.
TL;DR
1. What Is an Identity Security Platform and What Should It Actually Do?
A comprehensive identity security platform delivers end-to-end identity management, supporting Zero Trust by continuously verifying, governing, and protecting human and machine identities across environments.
Unlike fragmented tools focused only on authentication or governance, a unified platform provides full visibility and real-time protection against identity-based threats.
Here's what it actually needs to deliver:
- Identity discovery: every user, every app, every access point, including the unapproved ones
- Lifecycle management: automated provisioning on day one, updates on role change, immediate deprovisioning on exit
- Access governance: continuous reviews with automated flagging of risky or excessive permissions
- Privileged access management: extra controls and session monitoring for admin and high-privilege accounts
- Threat detection: spotting anomalous behavior, unusual login patterns, and identity-based attacks in real time
- Compliance evidence: audit-ready access logs and certification records generated automatically, not manually
If a platform only does two or three of these, it's a point solution. Not an identity security platform.
Worth a Read: The Identity Drift Crisis: Why Your Access Controls Age Faster Than Your Teams
2. Why the Platform You Pick in 2026 Will Be Hard to Walk Back From?
Identity infrastructure gets deeply embedded into your HR systems, your SaaS stack, your SSO layer, and your audit workflows. This isn't a decision you revisit in six months.
A few things make 2026 a particularly high-stakes moment:
- Consolidation is happening fast:36% of organizations are actively consolidating identity platforms, and another 46% are evaluating vendor unification. The window to make the right call is now.
- Machine identities are exploding: service accounts, bots, API keys, AI agents. Everyone needs governance. Most platforms weren't built for this scale.
- Shadow AI created a new identity surface: employees using unsanctioned AI tools are creating access and data exposure risks that traditional IAM tools simply can't see.
- Regulatory pressure keeps intensifying: GDPR, HIPAA, SOC 2, ISO 27001. Auditors want continuous governance evidence, not quarterly snapshots.
The top identity security investment priorities in 2026 are governance gaps (49%), compliance pressure (48%), and emerging identity complexities (46%). The same pain points are driving identity fatigue today. (Source: ManageEngine, 2026)
And if you're wondering how real the shadow AI and hidden access problem actually is:
CloudEagle's own research surfaced something striking. In our webinar "60% Invisible: Shadow AI and Hidden Access Crisis in SaaS & AI Environments," the team revealed that 60% of SaaS and AI apps in enterprise environments operate completely off IT's radar
Watch the full webinar here: 60% Invisible: Shadow AI and Hidden Access Crisis
3. The 10 Best Identity Security Platforms for 2026
1. CloudEagle.ai
CloudEagle.ai is an AI-powered platform that centralizes SaaS Management, Identity Governance, and Security for modern enterprises. Hundreds of apps, incomplete visibility, and identity risks that live outside your IDP. It doesn't just govern the apps behind SSO. It governs everything.
Best for: Enterprises managing SaaS-heavy environments where access governance, shadow IT, and license compliance are the core identity challenges
Shadow IT and AI Visibility
Most identity platforms only manage applications connected to SSO. The real risk sits outside it.
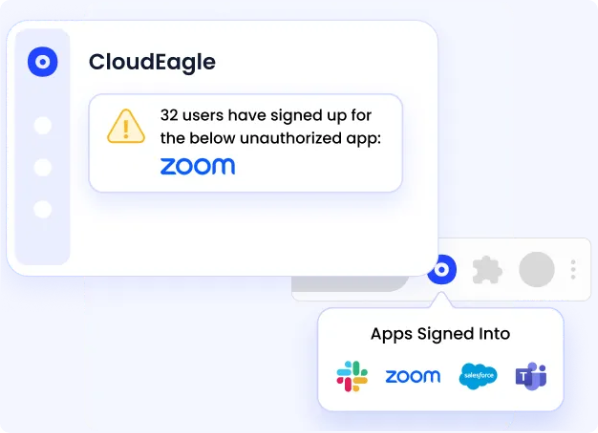
CloudEagle discovers every SaaS and AI tool employees access, including unsanctioned apps and shadow AI. Security teams get a unified inventory of apps, users, and access paths across both SSO and non-SSO environments.
User Access Reviews
Manual quarterly reviews often leave months of excessive access unnoticed.
CloudEagle automates access reviews with AI-driven risk detection. It flags stale permissions, excessive access, and risky privileges so reviewers can remediate them quickly from a single dashboard.
Compliance Automation
Preparing for audits usually means weeks of collecting screenshots and evidence.
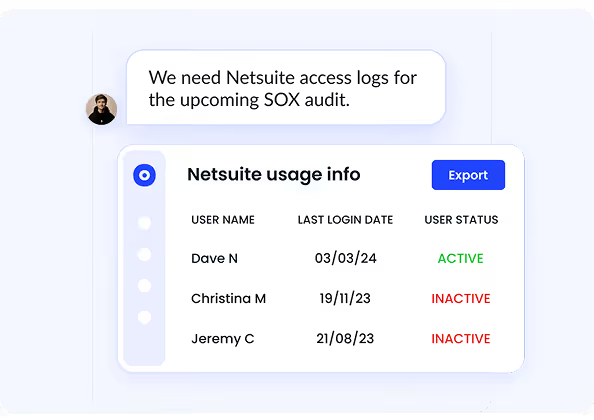
CloudEagle automatically tracks access changes and generates audit-ready reports mapped to frameworks like SOC 2 and ISO 27001. Evidence is continuously collected, so teams stay audit-ready at all times.
Excessive Privileged Users
Overprivileged users are one of the most common causes of identity-based breaches.
CloudEagle continuously monitors privileged roles and flags accounts with unnecessary admin access. Security teams can quickly remove excessive privileges before they become an attack path.
Self-Service App Catalog
Employees often bypass IT because requesting access takes too long.
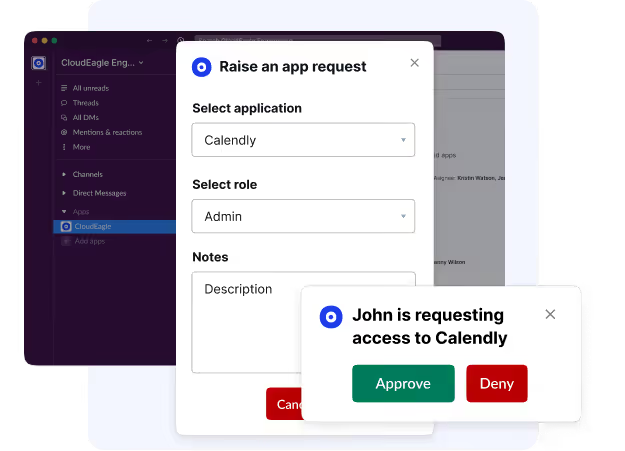
CloudEagle provides a self-service app catalog where employees can request applications with built-in approval workflows. IT and security teams maintain governance while reducing ticket backlogs.
User Onboarding and Offboarding
Manual onboarding and delayed offboarding create major identity risks.
CloudEagle automates provisioning and deprovisioning across all applications. Access is granted instantly during onboarding and revoked automatically when employees leave or change roles.
Pros:
- The only platform that governs apps completely outside your IDP
- Combines identity governance, SaaS spend management, and license compliance in one place
- Automated everything: no manual chasing, no ticket backlogs
- Reduces tracking errors during provisioning and role transitions by up to 70%
- SOC 2 access reviews are completed up to 80% faster
- Recognized in the 2025 Gartner Magic Quadrant for SaaS Management Platforms
Best for: Enterprises managing SaaS-heavy environments where access governance, shadow IT, and license compliance are the core identity challenges
Pricing: Available on request.
Still not sure how big the governance gap really is in 2026? Karl Haviland, CIO and CTO advisor, tackled it head-on on the SaaS Masterminds Podcast:
"The governance frameworks that worked for on-prem don't scale to a world where every employee is spinning up AI tools on a Tuesday afternoon."
If you're evaluating identity security platforms right now, this episode is worth 20 minutes.
Listen here: How AI-Driven Innovation Meets Real-World Governance
2. CrowdStrike Falcon Identity Protection
CrowdStrike brings its threat intelligence muscle into the identity space. Built for organizations where stopping active attacks, not just managing access, is the primary identity security concern.
Features:
- Detects identity-based attacks like credential stuffing, pass-the-hash, and lateral movement in real time
- Monitors Active Directory and Azure AD for misconfigurations and anomalous behavior
- Enforces risk-based MFA and conditional access policies
- Integrates natively with CrowdStrike's broader Falcon platform for unified threat response
- Behavioral analytics to detect insider threats and compromised accounts
Best for: Enterprises that need real-time identity threat detection tightly integrated with endpoint security.
Pricing: Part of the CrowdStrike Falcon platform. Pricing on request based on endpoints and modules.
3. SailPoint
One of the most established names in identity security software: purpose-built for governance at enterprise scale with deep compliance and audit capabilities.
Features:
- AI-driven identity governance across cloud, on-premise, and hybrid environments
- Automated access request, approval, and certification workflows
- Role management and separation of duties enforcement
- Privileged access governance integrated with PAM tools
- Compliance reporting for SOX, HIPAA, GDPR, and other frameworks
Best for: Large enterprises with complex identity governance and compliance requirements.
Pricing: Enterprise pricing on request. Typically starts at $100,000+/year for large deployments.
4. Okta
The go-to identity platform for cloud-first enterprises. Its massive integration library and developer-friendly approach make it one of the most widely deployed identity security platforms globally.
Features:
- Single sign-on and MFA across thousands of app integrations
- Lifecycle management with automated provisioning and deprovisioning
- Adaptive access policies based on user risk, device, and location
- Customer identity (CIAM) capabilities for external-facing applications
- Okta Identity Governance for access reviews and entitlement management
Best for: Cloud-first enterprises needing a flexible, integration-rich identity foundation.
Pricing: Workforce Identity starts at around $2/user/month for basic SSO. Governance and advanced features are priced separately.
5. CyberArk
The market leader in privileged access management. The go-to choice when your biggest identity risk is admin accounts, service accounts, and high-privilege users being compromised.
Features:
- Privileged access management with credential vaulting and session isolation
- Secrets management for DevOps pipelines and machine identities
- Endpoint privilege management to remove unnecessary local admin rights
- Identity threat detection and response for privileged account abuse
- Cloud entitlement management across AWS, Azure, and GCP
Best for: Enterprises where privileged access management and securing high-value accounts are the top priority.
Pricing: Enterprise pricing on request. Typically $50,000+/year depending on modules and user count.
6. Microsoft Entra ID
The identity backbone for millions of organizations worldwide. If your environment is Microsoft-heavy, it's often the default starting point for identity security tools for enterprises.
Features:
- SSO and MFA across Microsoft and third-party apps
- Conditional access policies based on user, device, and location risk
- Privileged Identity Management for just-in-time admin access
- Identity Protection with risk-based sign-in and user risk policies
- Entra ID Governance for access reviews and entitlement management
Best for: Enterprises already standardized on Microsoft 365 and Azure.
Pricing: Included in Microsoft 365 plans. Entra ID P1 at $6/user/month. P2 at $9/user/month.
7. Saviynt
Brings identity governance and PAM together in a unified, cloud-native platform: addressing the fragmentation that plagues organizations running separate IGA and PAM tools.
Features:
- Identity governance with automated access reviews and certifications
- Privileged access management with session recording and credential vaulting
- Application access governance for SAP, Salesforce, and other enterprise apps
- Cloud security and entitlement management across multi-cloud environments
- AI-powered risk scoring and anomaly detection
Best for: Enterprises needing converged identity governance and privileged access in a single cloud-native platform.
Pricing: Enterprise pricing on request. Typically starts around $150,000/year for large deployments.
8. Ping Identity
Built for organizations with complex, heterogeneous environments: legacy systems, multiple clouds, and a need for deep customization in how identity is managed and enforced.
Features:
- SSO and MFA with support for legacy and modern authentication standards
- Adaptive authentication with risk-based access policies
- API security and developer identity management
- Customer identity management at enterprise scale
- Zero Trust enforcement integrated with device posture and browser context
Best for: Enterprises needing flexible, standards-based identity across hybrid and multi-cloud environments.
Pricing: Modular pricing. Starts around $20,000/year. Enterprise contracts are negotiated directly.
9. Reco
A newer entrant focused specifically on identity risks inside SaaS applications: filling the gap that traditional IAM tools leave around what users are actually doing inside apps like Google Workspace, Salesforce, and GitHub.
Features:
- Discovers all SaaS apps and maps user identities and access across them
- Detects identity threats and anomalous behavior inside SaaS applications
- Identifies over-privileged users, misconfigured sharing, and sensitive data exposure
- SaaS security posture management (SSPM) with remediation workflows
- Integrates with SIEM and SOAR tools for automated response
Best for: Security teams that need SaaS-specific identity threat detection and access risk visibility.
Pricing: Pricing on request. Scales based on the number of SaaS apps and users monitored.
10. Proofpoint Identity Threat Defense
Built around one core idea: attackers exploit identity misconfigurations to move laterally and escalate privileges. This platform finds and fixes those misconfigurations before they're exploited.
Features:
- Discovers identity risks across Active Directory and Azure AD: misconfigurations, shadow admins, stale credentials
- Detects active identity attacks, including credential theft and lateral movement
- Attack path analysis showing how attackers could escalate from any user
- Remediates identity risks with automated or guided workflows
- Integrates with endpoint and email security for full attack chain visibility
Best for: Enterprises focused on stopping identity-based attacks before they become breaches.
Pricing: Enterprise pricing on request.
4. What to Check Before You Shortlist Any Identity Security Platform?
Before you book a single demo, run every candidate through these questions:
- Does it cover non-SSO apps? Most tools only govern what's behind your IDP. That leaves shadow IT and unmanaged SaaS completely blind.
- How does it handle offboarding? Instant, automated deprovisioning across all apps, or a ticket that someone has to manually action?
- Can it detect shadow AI tools? In 2026, this is a real attack surface. If the platform can't see unsanctioned AI usage, it has a dangerous blind spot.
- What does "continuous" actually mean? Weekly reports aren't continuous. Real-time flagging is. Ask for specifics.
- How long does implementation take? Some enterprise platforms take 6–12 months to fully deploy. That matters.
- Does it generate audit-ready evidence automatically? Or does someone have to manually export and format before every audit?
- What's the total cost of ownership? License fees are just the start. Factor in implementation, professional services, and integrations.
5. Why CloudEagle.ai Belongs on Your Identity Security Platform Shortlist?
Most identity security platforms were built for the world of managed, SSO-connected apps. CloudEagle.ai was built for the world you actually live in, where employees are using 50, 100, or 200+ apps, most of which IT didn't approve and can't see.
Here's what makes it different:
- Full app discovery: not just what's behind your IDP, but everything, including shadow IT and AI tools
- Non-SSO app governance: governs apps completely outside your identity provider's reach
- License compliance built in: identity governance and SaaS spend management in the same platform
- Automated everything: provisioning, deprovisioning, access reviews, evidence generation, license reclamation
- 500+ native integrations: connects to your HRIS, ITSM, identity providers, and SaaS stack
- Recognized in the 2025 Gartner Magic Quadrant for SaaS Management Platforms
And it's not just the features. Here's what a real customer had to say after switching:
Michal Lipinski, Director of IT & Security at ICEYE, put it this way: "We lacked confidence in our access certifications. CloudEagle brought structure and accountability to user access reviews without reviewer fatigue."
Final Verdict
Identity security in 2026 isn't about picking a tool. It's about picking an architecture.
CrowdStrike leads in threat detection. CyberArk leads on privileged access. SailPoint and Saviynt lead on governance at scale. Okta and Microsoft Entra ID lead on breadth and integration. Reco and Proofpoint go deep on SaaS-specific identity risks.
And CloudEagle.ai leads on the problem most of them don't fully solve: governing every app, every user, and every access point across the modern SaaS-heavy enterprise, including the ones you don't know about yet.
The right platform depends on where your biggest identity risk actually lives. Start there.
FAQs
- What are the best identity security platforms for enterprises in 2026?
The top platforms include CloudEagle.ai, CrowdStrike Falcon Identity Protection, SailPoint, Okta, CyberArk, Microsoft Entra ID, Saviynt, Ping Identity, Reco, and Proofpoint Identity Threat Defense, each built for different aspects of enterprise identity security.
- What is identity threat detection and response?
It's the practice of continuously monitoring identity systems for signs of attack, detecting credential theft, lateral movement, and privilege escalation in real time before they become breaches.
- How is an identity security platform different from a standard IAM tool?
Traditional IAM tools manage authentication and provisioning. Modern identity security platforms go further, adding continuous governance, threat detection, access reviews, compliance automation, and coverage for apps and identities outside the traditional IAM perimeter.
- What should enterprises prioritize when choosing an identity security platform in 2026?
Continuous governance over periodic reviews, coverage of non-SSO and shadow IT apps, automated offboarding, real-time threat detection, and audit-ready compliance evidence without manual effort.
- How much do identity security platforms cost?
Pricing varies significantly. Okta starts around $2/user/month. Mid-market platforms range from $20,000 to $100,000/year. Enterprise platforms like SailPoint and Saviynt typically start at $100,000+. CloudEagle.ai pricing is available on request.

%201.svg)









.avif)




.avif)
.avif)




.png)





