HIPAA Compliance Checklist for 2025

Most teams rely on Okta and SSO logs as their source of truth for SaaS activity. The real picture, however, is far messier. Industry reports show that 60% of organizations don’t include Shadow IT in their threat assessments, even though a significant share of cyber incidents in the last two years traced back to unsanctioned app usage.
If you’ve ever wondered what your SSO isn’t catching and why those blind spots keep growing, you’re in the right place. This article breaks down how SaaS is identified today, where SSO misses critical activity, and how CloudEagle detects Shadow IT far beyond identity systems.
TL;DR
- Okta and SSO only show the apps routed through them, leaving hundreds of direct logins, free tools, trials, and card-based purchases completely invisible.
- Shadow IT grows in those blind spots, creating unmanaged spend, duplicate tools, compliance gaps, and high-risk access you can’t review or offboard.
- CloudEagle rebuilds the entire SaaS map by combining finance data, contracts, direct usage APIs, HRIS context, browser signals, and identity logs into one accurate view.
- This multi-source visibility identifies every approved or unapproved app while surfacing risks, duplicate vendors, usage gaps, and spending trends in real time.
- With workflows, alerts, and automated nudges, CloudEagle helps teams act immediately, reduce risk, and stop Shadow IT before it becomes a security or cost problem.
1. How SaaS Discovery Works Today?
Think about the last time a new app surfaced inside the company.
It didn’t register through Okta. It didn’t appear in an onboarding checklist. It showed up later quietly in a credit card charge, an expense report, or a casual mention from a team already depending on it. That’s how most SaaS enters organizations today: individually, informally, and outside any predictable workflow.
For years, discovery relied on the assumption that central systems such as SSO logs, finance data, and spreadsheets would reveal everything. But SaaS adoption shifted. Employees now sign up for tools directly, use personal accounts, test free versions, and authenticate through paths that never touch the identity provider.
As a result, discovery has become reactive.
IT teams piece together whatever signals they can. They review Okta or Google SSO logs to see which apps are formally connected. They scrape credit card statements to identify unfamiliar vendors, often guessing which transactions are software. They check GSuite logs for login activity. They deploy browser extensions that only work when users install them. And even in mature teams, dashboards stitch these sources together, but the underlying data still leaves major gaps.
The reality of this process?
- Credit card reviews happen monthly or quarterly.
- SSO logs capture only the slice of apps tied into Okta.
- Manual lists and spreadsheets fall out of sync almost immediately.
- Browser plugins offer inconsistent coverage.
“Many non-IT people have no idea they are running a shadow IT activity, much less consider all of the safeguards they should have in place.” ~ Steve McGregory, Director of Application and Threat Intelligence at Ixia
The result is a partial map assembled from incomplete signals where every team ends up seeing a different version of the SaaS landscape.
2. Where Okta and SSO Miss Shadow IT Activity?
Identity tools like Okta centralize authentication, but they were never designed to reveal the full SaaS footprint. They show what’s formally connected, not what employees actually adopt, purchase, or use. This creates blind spots across usage, spend, and governance, exactly where Shadow IT takes hold.
What Okta and SSO doesn’t show you:
- Apps never integrated with Okta or any SSO provider
- Direct logins through vendor websites, personal accounts, or unapproved paths
- Mobile or desktop client logins that bypass the SSO flow
- Purchases made via corporate cards, reimbursements, or trial sign-ups
- Duplicate applications are adopted across different teams
- Unused or underutilized licenses contribute to silent budget waste
- Who is inactive, oversized, or using redundant tools
- Usage depth, feature adoption, and whether the app adds real business value
- Contract details, invoices, SKUs, or renewal timelines
- Any unified picture combining spend, access, and usage in one place
“By its very nature, shadow IT exists to circumvent IT governance and security controls by employees believing they’re doing something beneficial for the company. The painful truth is that shadow IT is one of the leading causes of insider data threats across any organization." ~ Rick Orloff, Vice President and Chief Security Officer at Code42.
SSO only tracks the authentication path and not the tool itself, the spend behind it, or the risk it introduces.
And they don’t support
- Detection of SaaS apps authenticated outside Okta or SSO
- Governance or offboarding workflows for non-SSO apps
- Access reviews with full visibility across all apps
- Risk scoring for unsanctioned or unknown tools
- Identification of duplicates across teams or departments
- Continuous monitoring of unmanaged or high-risk vendors
These limitations create a fragmented discovery model where identity tools see only what is routed through them and nothing else.
As a result, teams believe they’re looking at a complete SaaS inventory, but huge portions operate outside of Okta and SSO. Finance sees one number. IT sees another. Security can’t assess what it can’t see. And Shadow IT grows precisely in the gaps, such as direct logins, unmanaged purchases, personal accounts, free tools, and redundant apps that never surface in identity workflows.
This is where spend leakage builds, visibility breaks down, and operational risk begins.
3. How CloudEagle Detects Shadow IT Beyond Okta and SSO?
Traditional SSO-based discovery shows only the apps routed through Okta or Google Workspace. CloudEagle rebuilds discovery using a broader, multi-layered approach by correlating spend, usage, identity, traffic, contracts, and vendor signals to surface every sanctioned and unsanctioned app in your environment.
This method catches what Okta inherently misses: direct logins, personal-account usage, shadow vendors, free tools, trial conversions, and tools purchased outside procurement. CloudEagle.ai applies six layers of intelligence to detect Shadow IT accurately and continuously.
A. Multi-System Visibility Across Spend, Usage, Identity & Access
Before anything else, CloudEagle connects to the systems where Shadow IT leaves a trail: corporate cards, ERP, AP, expense tools, HRIS, direct app APIs, email domains, browser telemetry, and identity providers.
This foundation surfaces:
- App users log in via Google SSO
- Apps authenticated directly (bypassing Okta)
- Apps purchased with personal or corporate cards
- Free trials that quietly convert into paid usage
- Mobile/desktop logins that never leave identity footprints
- Vendors hidden behind abbreviations, parent companies, or misspellings
- Activity patterns from browser and network signals
CloudEagle rebuilds the SaaS map from multiple systems, not from a single authentication log.

CloudEagle’s multi-source visibility has already proven its impact in real environments. When Bold connected their finance systems, contract data, and usage logs into CloudEagle, hidden apps and unused licenses surfaced instantly.
That clarity helped them renegotiate smarter, eliminate waste, and save $100K in one renewal cycle, just by seeing the full footprint for the first time.

B. Detecting New Apps Through Spend, Usage & Contract Signals
CloudEagle triangulates three independent indicators to detect Shadow IT that Okta and SSO cannot identify:
This approach exposes both paid and unpaid Shadow IT, including tools that have no SSO integration at all.
C. Correlating Spend, Access, HR & Vendor Signals for True Discovery
Discovery alone is not enough. CloudEagle enriches each detected app using:
- HRIS data: department, role, employment status, manager
- Identity data: who authenticated through SSO vs bypass paths
- Vendor normalization: parent company mapping, spelling corrections, domain matching
- Direct connector data: license type, feature usage, admin vs non-admin users
- Contract & invoice documents: visibility into the real vendor relationship

This correlation reveals:
- Which teams adopted the tool
- Whether it's redundant with an approved app
- Who actually uses it vs who simply has access
- Whether access came from sanctioned or unsanctioned paths
This turns detection into complete situational awareness.
D. Risk Assessment & Risk Scoring for Discovered Apps
CloudEagle assigns a risk score to every discovered tool using:
- Data sensitivity indicators
- Permissions granted (admin, data export, integrations)
- Authentication method (SSO vs personal account)
- Known vendor vulnerabilities
- Usage anomalies (inactive users, privilege escalation, unusual access times)

This immediately surfaces:
- High-risk tools adopted without IT approval
- Apps exposing sensitive data
- Non-compliant tools used in regulated environments
Risk scoring is a core part of the HOW, not a separate outcome.
E. Automated Policy Enforcement with RBAC & Workflow Actions
CloudEagle doesn’t wait for quarterly access reviews. When a new or risky app is detected, the platform can automatically:
- Apply role-based access control (RBAC) rules
- Restrict access based on role, department, or context
- Trigger workflows to approve, restrict, or remove the tool
- Block specific login patterns
- Align access levels with internal policies
- Auto-notify users through Slack/email to verify or discontinue the tool
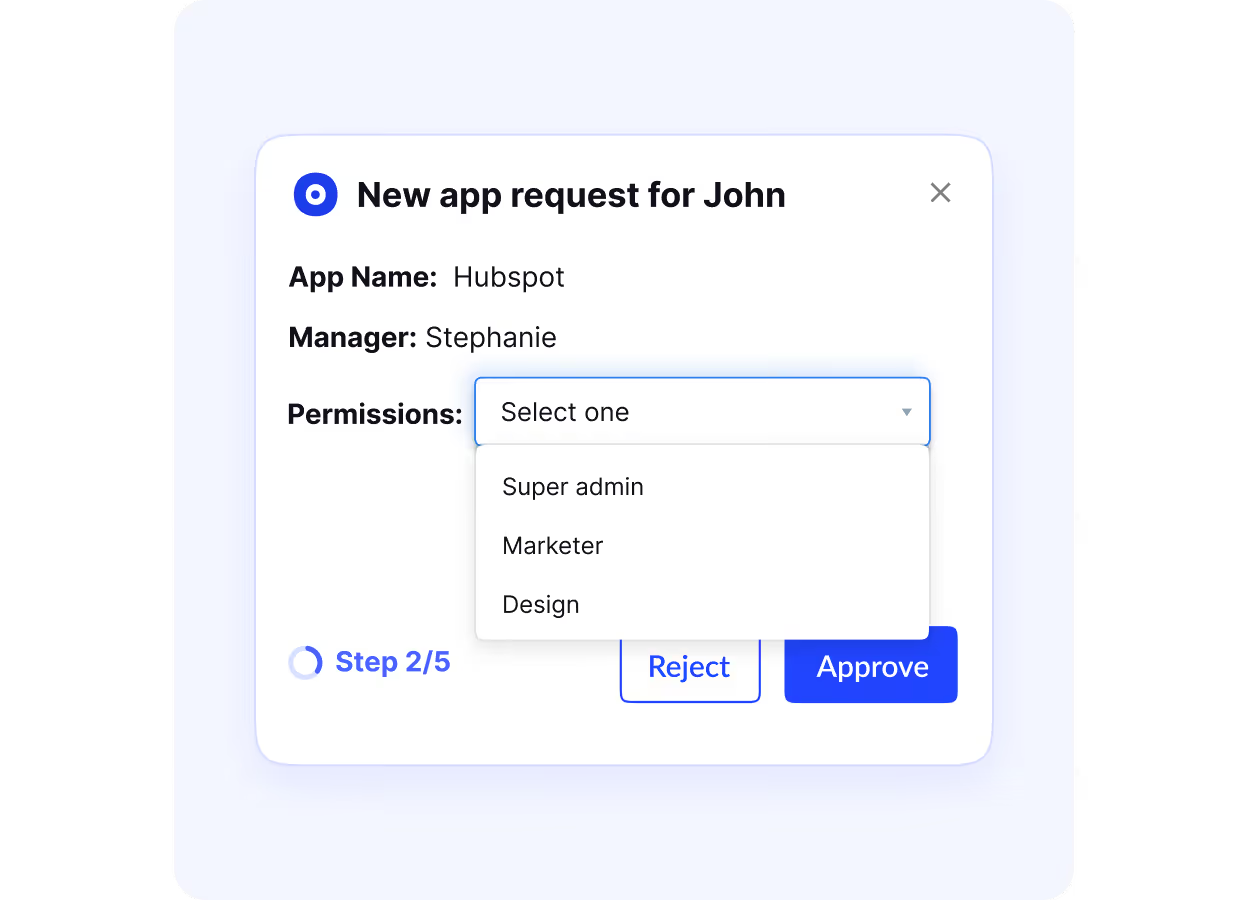
This enforces policy exactly at the moment of discovery, not after the risk has spread.
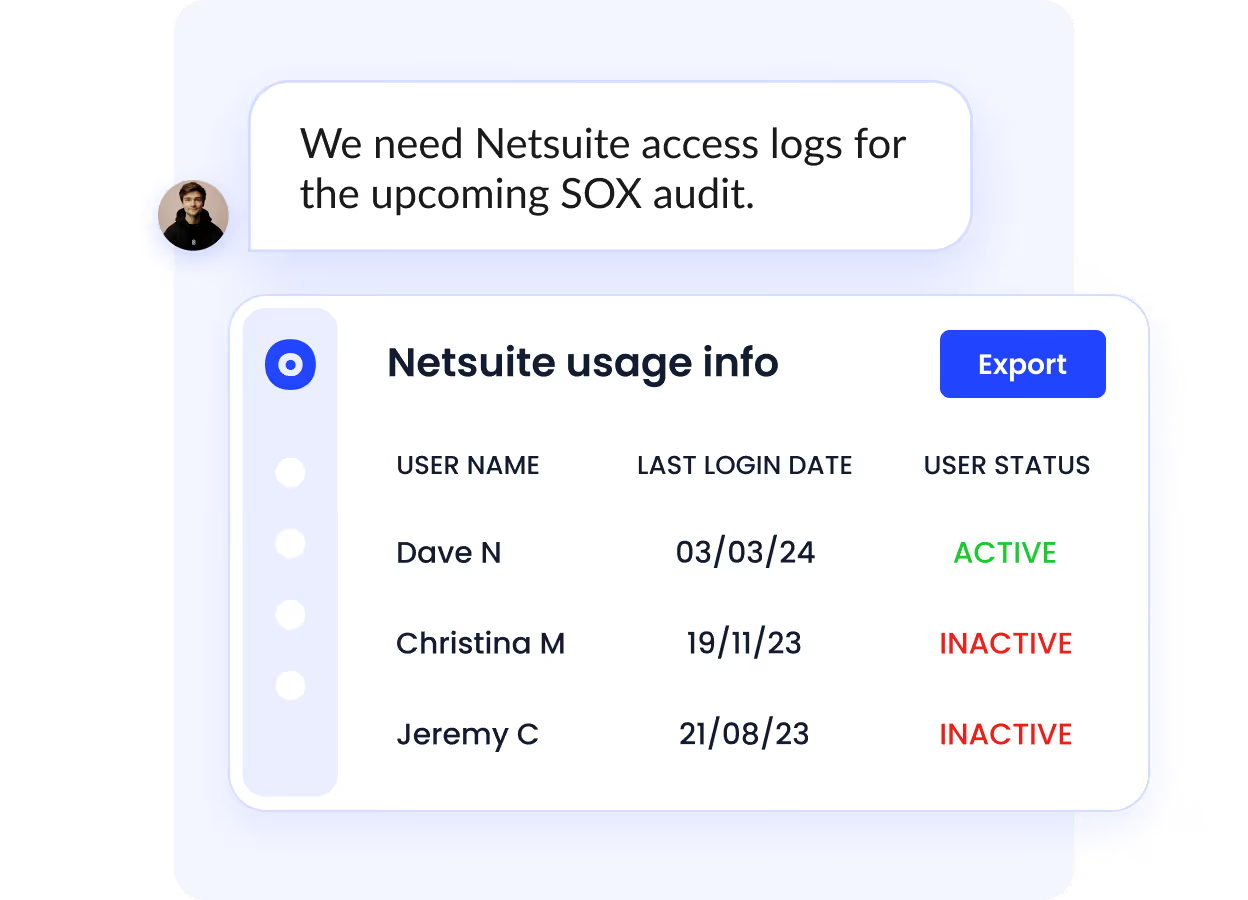
F. Real-Time Alerts, Reporting & User Education
Once Shadow IT surfaces, CloudEagle.ai immediately sends alerts when:
- A new unsanctioned app appears
- An existing app exhibits risky behavior
- A free tool turns into a paid subscription
- A user authenticates outside approved methods

Beyond alerts, CloudEagle.ai provides:
- Shadow IT dashboards
- Department-level usage and spend reports
- Contract-spend-usage reconciliation reports
- User education prompts that guide employees toward approved alternatives
- Compliance nudges to discourage risky or unauthorized tools
This closes the loop: employees understand the approved path, while IT sees everything happening outside it.
4. Why Full Visibility With CloudEagle Changes Everything?
Identity systems like Okta were built to authenticate users, not to reveal the full SaaS footprint hiding across spend reports, trials, personal accounts, or unapproved tools.
As SaaS adoption accelerated, these blind spots widened, creating duplicate apps, unmanaged vendors, risky tools, and spend teams couldn’t track. Login-based visibility simply couldn’t keep up.
CloudEagle changes that by shifting visibility from “who logged in?” to “what do we actually use and pay for?” It merges spend, usage, and access data into one view, revealing apps that SSO can’t detect and giving every team the context they’ve been missing.
Here’s how CloudEagle steps up to this strategic role:
- Visibility beyond SSO authentication: CloudEagle ties together finance data, direct usage integrations, contracts, and identity signals to surface every app, be it paid, free, trial, reimbursed, or accessed outside Okta. This unifies the SaaS inventory that SSO tools only partially show.
- Continuous, multi-source governance: Instead of relying on login logs, CloudEagle continuously analyzes spend patterns, feature usage, invoices, and access context. This reduces the gaps where Shadow IT typically grows and replaces ad-hoc discovery with ongoing intelligence.
- Bridging IT, security, procurement & finance: All teams operate from a shared view: who bought what, who’s using it, what it costs, and what risk it carries. This alignment stops duplicate purchases, unmanaged vendors, and non-compliant tools from slipping through.
- Reducing risk from high-risk or unmanaged apps: By identifying tools outside sanctioned flows of free apps, unapproved AI tools, and personal-account logins, CloudEagle flags risk early and maps apps to security categories so teams can take proactive action.
- Accelerating audit and renewal readiness: Every app, license, owner, invoice, and user is tracked automatically. This creates a complete audit trail and eliminates the scramble of chasing access, spend, or contract details during renewals or compliance cycles.
- Scaling with SaaS complexity: Whether it’s a global team, hybrid workforce, or rapid tool adoption, CloudEagle scales discovery across 500+ direct integrations, finance systems, and HRIS, giving teams the full context SSO alone cannot provide.
Shadow IT Ends Where CloudEagle Begins
Shadow IT isn’t hiding inside Okta; it’s living in the gaps between spend, usage, and access. Now you know how those blind spots form and why identity tools alone can’t close them.
CloudEagle brings the missing visibility layer: real usage, real spend, real access, all in one place so you can control the apps you actually have, not just the ones routed through SSO.
If you're ready to eliminate surprises, stop duplicate spend, and stay ahead of risky tools, CloudEagle is the natural next step.
.avif)
%201.svg)






.avif)




.avif)
.avif)




.png)





