HIPAA Compliance Checklist for 2025

You probably already have shadow IT.
Not because your team is reckless. Just because work moves fast, someone signs up for a tool to hit a deadline. Someone connects an AI assistant to speed up meetings. It feels productive. It feels harmless.
Until you realize half those apps never went through review. Some are duplicating tools you already pay for. Some are touching sensitive data. And now shadow AI is accelerating all of it.
If you’re trying to manage shadow AI and shadow IT, the real challenge isn’t stopping innovation. It’s getting visibility before experimentation turns into unmanaged risk.
Let’s break down how to do that without slowing the business down.
TL;DR
- 60% of AI and SaaS apps operate outside IT visibility, increasing risk and spend.
- Shadow AI management requires more than blocking tools; it needs continuous monitoring.
- Traditional IAM tools miss apps outside SSO and browser-based AI usage.
- A unified shadow IT management platform connects discovery, governance, and cost optimization.
- CloudEagle.ai helps enterprises reduce risk, eliminate waste, and regain full control over shadow AI and shadow IT.
1. Shadow AI vs. Shadow IT. They're Not the Same Problem, But They Need the Same Fix
Let’s clarify something first.
Shadow IT is not new. Shadow AI is.
Shadow IT refers to applications, SaaS tools, or software adopted without IT approval. Think employees signing up for Dropbox, Notion, or project management tools using company emails.
Shadow AI, however, deals specifically with generative AI tools like ChatGPT, Claude, Midjourney, or AI plugins embedded inside tools like Google Docs.
Here is the difference:
- Shadow IT = unapproved software adoption
- Shadow AI = unapproved AI usage that may process sensitive data
- Both create governance blind spots
- Both expand outside official procurement processes
Microsoft’s Work Trend Index found that 75 percent of knowledge workers use AI at work, and 78 percent bring their own AI tools.
So yes, they are different risks. But they require the same solution: unified shadow IT visibility tools with AI detection built in.
If you want to manage shadow AI and shadow IT effectively, you cannot treat them as separate programs.
2. What Happens When Shadow AI and Shadow IT Go Unmanaged for Too Long?
See, both shadow AI and shadow IT do not explode overnight.
It takes its sweet time.
First, it looks like experimentation. Then, productivity optimization. Then it becomes embedded into workflows.
Here is what happens when you fail to implement shadow AI management and proper shadow IT visibility tools:
A. Data Exposure Increases
- Employees paste customer data into AI tools.
- Developers connect AI APIs to internal systems.
- Marketing teams upload proprietary documents for summarization.
IBM reports that the average data breach cost reached 4.45 million dollars in 2023.
Shadow AI increases that risk surface dramatically.
B. Compliance Gaps Multiply
Unapproved tools often lack:
- SOC 2 certification
- GDPR compliance
- Proper data retention policies
- Role-based access control
Without a shadow IT management platform, you cannot audit or govern these tools.
C. SaaS Spend Becomes Invisible
Shadow IT makes this worse. Finance does not see it. Procurement does not control it. IT cannot optimize it.
To eliminate shadow IT, enterprises must first detect it. And most teams do not even know what exists.
D. AI Usage Bypasses Policy
You may have AI policies. But are they enforced?
If your security team does not know who is using which AI model, policies are just documentation.
That is why managing shadow AI and shadow IT requires continuous monitoring, not annual audits.
3. Why Managing Shadow AI and Shadow IT Is Harder Than Most Enterprises Expect?
On paper, it sounds simple.
- Create policies.
- Block risky domains.
- Educate employees.
In reality, managing shadow AI and shadow IT is messy because the problem is not visibility alone. It is scale, speed, and behavior.
Let’s break down why this gets complicated fast.
A. You Can't Manage What You Haven't Found Yet
Most enterprises underestimate how many apps are already connected to their ecosystem.
Employees sign up using corporate emails, personal emails, shared team logins, and API keys. Some tools never even show up in expense reports.
The visibility gap exists because:
- Apps connect through OAuth without procurement involvement
- AI browser extensions operate outside traditional SaaS tracking
- Department budgets bypass central IT
- Free tiers never trigger financial alerts
Turns out, what you don’t see really can hurt you. One CloudEagle.ai customer plugged into Workday and discovered far more apps than expected.
With real-time SaaS discovery and automated governance, CloudEagle.ai gave them complete visibility and control almost immediately.
B. Every Unapproved App Is a Compliance Gap Waiting to Be Discovered
Shadow AI management becomes critical the moment sensitive data enters the equation.
Many AI tools:
- Store prompts and conversation logs
- Use third-party subprocessors
- Lacks enterprise-grade compliance certifications
- Retain metadata longer than expected
Now layer that over frameworks like SOC 2, ISO 27001, HIPAA, or GDPR.
Each unmanaged tool becomes:
- An audit blind spot
- A data residency risk
- A vendor risk assessment waiting to fail
C. The Budget Leak No One Put in the Report
Shadow AI and shadow IT are not just security issues. They are financial ones.

When tools are adopted informally:
- Licenses overlap across teams
- Enterprise agreements are bypassed
- Inactive users remain assigned
- Redundant AI tools stack up quietly
IT believes spending is controlled. Finance believes procurement is centralized. In reality, subscriptions grow in parallel.
Without a shadow IT management platform, optimization is impossible.
D. Policies That Exist But Aren't Actually Enforced
Most enterprises already have AI and SaaS policies.
The problem is enforcement.
Policies fail when:
- Discovery is manual
- Access reviews happen annually
- Approvals rely on email threads
- No system links identity, spend, and usage
Shadow AI management requires automation, not documentation.
Because governance that depends on memory, spreadsheets, or one security analyst is not governance. It is hope.
4. How CloudEagle.ai Helps Enterprises Manage Shadow AI and Shadow IT?
CloudEagle’s 2025 IGA report found that 60 percent of AI and SaaS applications operate outside IT visibility. That means more than half your environment could be unmanaged.
If you’re trying to manage shadow AI and shadow IT, reactive cleanups won’t work anymore. You need continuous discovery, governance, and enforcement working together.
Here’s how CloudEagle.ai makes that practical.
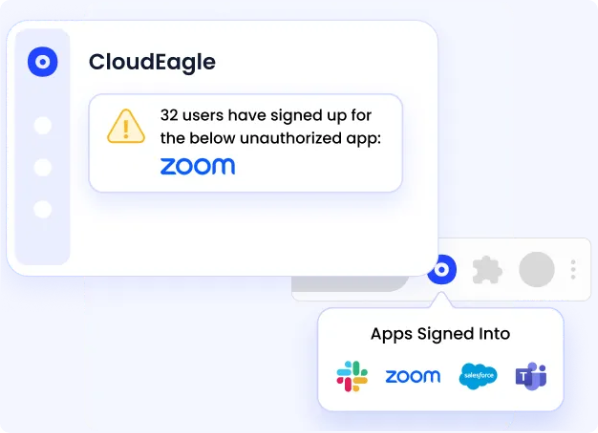
A. Discover Every App, Approved or Not
Before you can control anything, you need to see it.
CloudEagle.ai acts as a true shadow IT management platform by automatically detecting:
- Unsanctioned SaaS tools
- Browser-based AI apps like ChatGPT
- Free-tier tools that later convert to paid
- Credit card-based SaaS purchases

Unlike traditional IAM tools that only see apps behind SSO, CloudEagle.ai correlates:
- Login activity
- Browser and SSO data
- Finance and card spend
- Contract metadata
Outcome: A single dashboard showing every application in use, including shadow AI.
B. Govern Access with Automation
Discovery without action is just reporting.
CloudEagle.ai enables active shadow AI management and SaaS governance across all applications, whether or not they sit behind your identity provider.
Key capabilities include:
- Centralized employee app catalog
- Zero-touch onboarding and offboarding
- Automated access reviews with audit-ready logs
- Time-bound access controls for contractors
- Risk-based governance for AI tools
This directly prevents:
- Ex-employees retaining access
- Privilege creep
- Excessive admin rights
- Compliance failures
C. Detect and Remediate Shadow IT in Real Time
Seeing risk is good. Acting on it is better.
CloudEagle.ai closes the gap between detection and remediation by allowing teams to:
- Notify users automatically via Slack or email
- Trigger approval workflows
- Create ITSM tickets
- Auto-deprovision risky access
- Generate shadow IT risk reports
Instead of switching between tools, everything happens inside one shadow IT management platform.
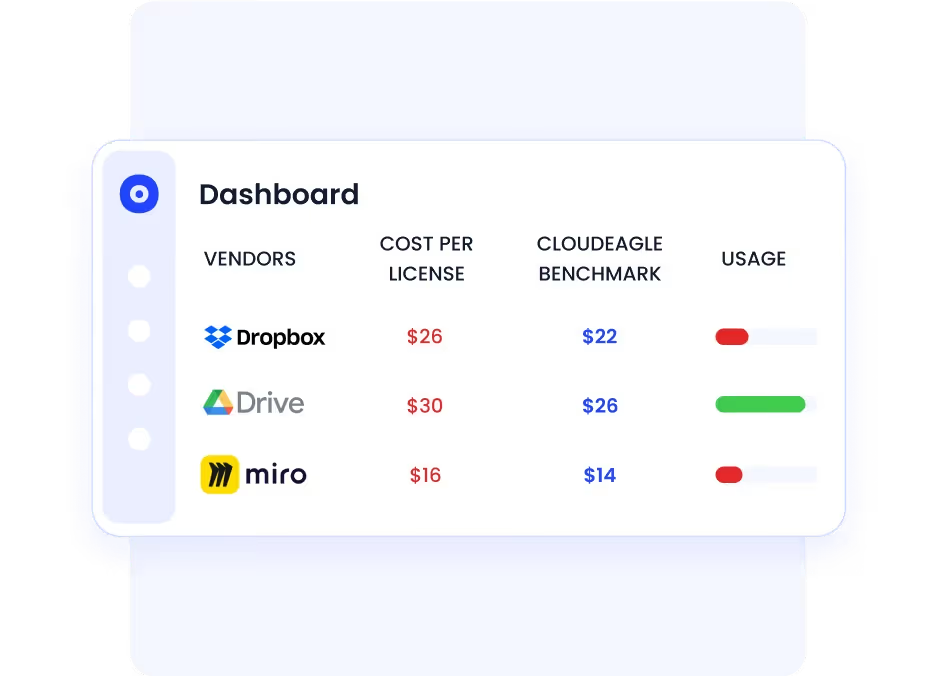
D. Eliminate Waste from Duplicate and Unused Apps
Shadow IT is not just a security issue. It is a budget problem.
CloudEagle.ai uses:
- AI-powered app categorization
- Duplicate app detection
- License usage tracking
- Automated license harvesting
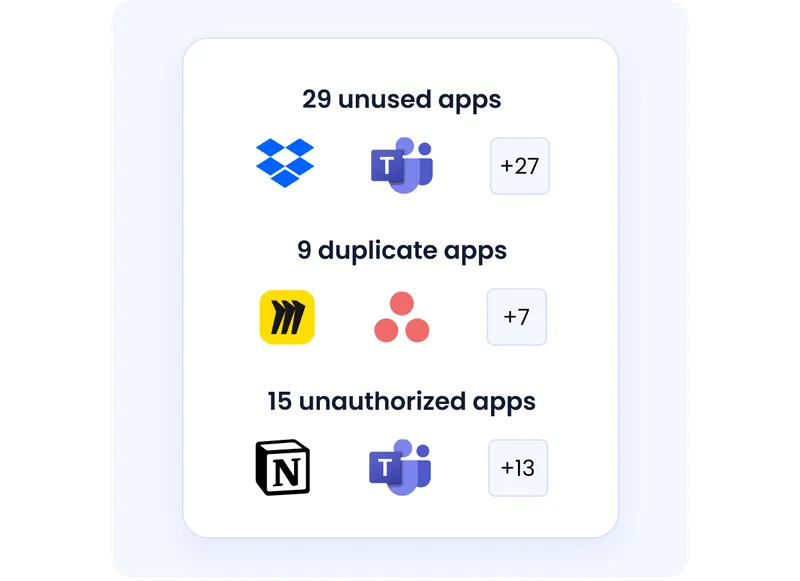
Enterprises typically save 10 to 30 percent on SaaS spend by eliminating waste and right-sizing licenses.
E. Prepare for Audits with Continuous Reviews
Most organizations still rely on quarterly or annual reviews. CloudEagle’s research shows that 95 percent of enterprises do not use AI-driven continuous reviews.
That creates gaps.
CloudEagle.ai automates:
- Periodic and continuous access reviews
- Risk-based user scoring
- SOC 2-ready audit logs
- Centralized reporting

Shadow AI management becomes sustainable when reviews are continuous, not reactive.
5. Why CloudEagle.ai Is the Practical Choice for Shadow AI and Shadow IT Management?
Many tools solve fragments of the problem.
CloudEagle.ai addresses the full lifecycle:
Discover → Govern → Optimize → Renew
That matters when you’re trying to manage shadow AI and shadow IT without creating more tool sprawl.
Here’s why it stands out.
A. Governance Beyond the IDP
Traditional IAM tools only govern apps behind SSO.
CloudEagle.ai governs:
- Free-tier tools
- Browser-based AI apps
- Department-purchased SaaS
- Apps outside identity systems
This makes it purpose-built for modern shadow AI management, not legacy IAM environments.
B. Unified Platform, Not Just Visibility
Some shadow IT visibility tools stop at dashboards.
CloudEagle.ai combines:
- Discovery
- Workflow automation
- Access governance
- License optimization
- Procurement and renewals

You don’t just see insights. You act on them.
That is what makes it a true shadow IT management platform
C. Built for IT, Security, and Procurement
Shadow AI and shadow IT sit across teams.
CloudEagle.ai bridges:
- IT: visibility and automated provisioning
- Security: continuous governance and AI risk controls
- Finance and procurement: license optimization and renewal intelligence
This cross-functional alignment is how enterprises eliminate shadow IT without creating friction.
D. Fast Time to Value
With 500+ integrations and rapid onboarding, enterprises get actionable insights quickly.
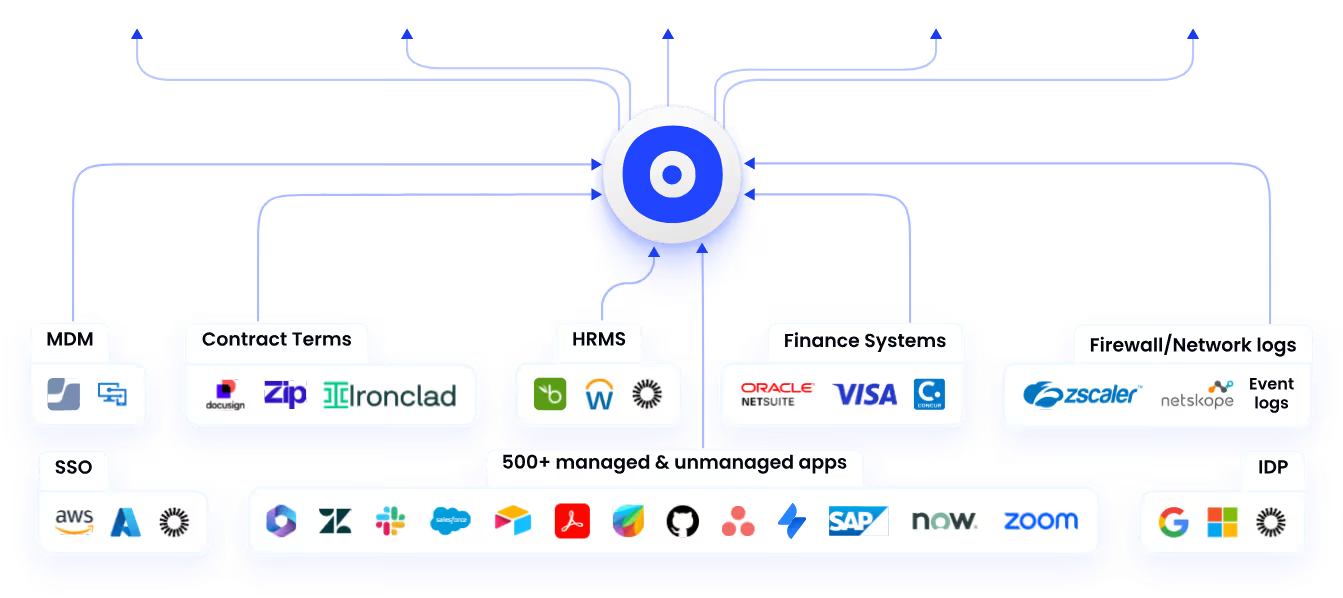
Instead of stitching together multiple tools, CloudEagle.ai delivers out-of-the-box governance for SaaS and AI sprawl.
And customers feel the difference.
CloudEagle's onboarding was fast and easy. The setup only took 30 minutes, thanks to all the integrations they provide. A game-changer in SaaS management. Thanks, CloudEagle!
- Devin Murphy, Senior Accounting Manager, Rec Room.
Final Words
Shadow AI and Shadow IT are not temporary disruptions. They are now embedded in how teams work, experiment, and move fast inside modern enterprises.
Trying to block everything will fail. The real solution is visibility, continuous governance, and automation that scales with how employees actually adopt tools.
To truly manage shadow AI and shadow IT, enterprises need more than detection. They need a shadow IT management platform that connects discovery, access control, spend optimization, and enforcement in one system.
CloudEagle.ai helps organizations move from reactive cleanups to proactive control, giving IT, security, and finance a unified way to eliminate shadow IT enterprise-wide without slowing innovation.
Book a free demo with CloudEagle.ai and take control of your shadow AI and shadow IT before it scales beyond visibility.
Frequently Asked Questions
- What is shadow IT management?
Shadow IT management is the process of discovering, governing, and controlling unapproved software and SaaS tools used within an organization to reduce security, compliance, and financial risks.
- What tools can help manage shadow IT?
Shadow IT visibility tools and a shadow IT management platform like CloudEagle.ai help detect unsanctioned apps, automate access governance, and optimize SaaS spend across departments.
- What are the risks of shadow AI?
Shadow AI increases the risk of data leakage, compliance violations, uncontrolled API integrations, and insider threats when AI tools process sensitive enterprise information without oversight.
- How to detect shadow AI?
Shadow AI can be detected using SaaS discovery tools that monitor OAuth connections, browser activity, finance data, SSO logs, and AI integrations across enterprise environments.
- What is the value of shadow IT discovery?
Shadow IT discovery provides real-time visibility into unapproved tools, helping enterprises reduce risk, prevent compliance gaps, eliminate duplicate spend, and strengthen governance.

%201.svg)









.avif)




.avif)
.avif)




.png)





