HIPAA Compliance Checklist for 2025

If an attacker can log in as a legitimate user, your entire security stack becomes secondary.
That is the reality of identity security in 2026. Compromised credentials and excessive access remain the fastest path into enterprise systems.
Yet most organizations still treat identity security like an IAM checklist. SSO, MFA, and quarterly reviews are done. Meanwhile, SaaS sprawl, shadow IT, and AI tools quietly expand the identity attack surface.
In this blog, we’ll break down what identity security really means, the identity security challenges enterprises still face, and the identity security best practices that actually work.
TL;DR
- Identity is now the most targeted layer in enterprise security.
- SaaS sprawl and non-human identities are expanding identity security challenges.
- Traditional IAM tools cannot fully govern apps outside SSO.
- Continuous access reviews and least-privilege enforcement are critical identity security best practices.
- CloudEagle.ai helps enterprises extend identity security beyond IAM with full SaaS visibility and automated governance.
1. What Is Identity Security? (And Why Your Firewall Can't Save You)
Identity security is the discipline of protecting digital identities and controlling access to systems, applications, and data across an organization.
It goes beyond identity access management security. IAM focuses on authentication and provisioning. Identity security ensures the right people, machines, and services have the right access at the right time, and nothing more.
In 2026, identity security includes:
- Human users
- Contractors and partners
- Privileged admins
- APIs and service accounts
- AI agents and non-human identities
If identity is the new perimeter, identity security is the gatekeeper.
2. Why Identity Is Now the Most Targeted Layer in Enterprise Security?
Attackers have evolved.
According to Verizon’s Data Breach Investigations Report, stolen credentials remain one of the top initial access vectors in breaches year after year. Phishing and credential abuse continue to dominate.
Why?
Because identities are easier to exploit than hardened infrastructure.
Instead of bypassing firewalls, attackers:
- Phish credentials
- Exploit weak MFA
- Abuse excessive privileges
- Hijack service accounts
As enterprises adopt SaaS, remote work, APIs, and AI tools, identity security challenges multiply.
Every new app creates new access. Every new integration creates new tokens. Every new employee creates a new risk. And most enterprises are still trying to manage all of it reactively.
CIOs and CTOs are navigating a tough balance, driving AI innovation while keeping governance tight. In this podcast episode, Karl Haviland, Founder of Haviland Software, explains how enterprises can move fast without creating identity and access blind spots.
Listen To The Podcast: How AI-Driven Innovation Meets Real-World Governance: A Blueprint for CIOs and CTOs
3. The Core Components of an Identity Security Program That Actually Works
A modern identity security program goes beyond checkbox compliance. It takes an identity-first approach, securing every human and machine identity across hybrid and multi-cloud environments.
A. Identity Governance: Knowing Who Has Access to What and Why
Identity governance ensures access is intentional, justified, and reviewed regularly.
Without it:
- Ex-employees retain access
- Users accumulate privileges over time
- Audit reviews become manual nightmares
Strong identity security best practices require:
- Automated provisioning and deprovisioning
- Periodic access reviews
- Role-based access control
- Clear ownership of applications
If you cannot answer “Who has access to what and why?” In minutes, your identity security program has gaps.
“We didn’t have a clear system to manage employee access. App requests came through different channels, access stayed active longer than needed, and ownership was unclear. CloudEagle helped us centralize access requests, apply time-bound controls, and bring structure to identity governance.”
~ Pushkala Pattabhiraman, Head of Security and Productivity, Datastax
Read the Case Study: How CloudEagle Streamlined App Access Requests with Policy-Based Automation →
B. Privileged Access Management: Because Some Accounts Need Extra Watching
Not all identities are equal.
Admin accounts, database owners, and cloud super-users can cause massive damage if compromised.
Identity security for enterprises must include:
- Just-in-time privileged access
- Session monitoring
- Approval workflows
- Time-bound admin rights
Without privileged access management, one compromised admin account can impact the entire organization.
C. MFA That’s Strong Enough to Matter
Multi-factor authentication is no longer enough if it is weak.
SMS-based MFA is being bypassed. Push fatigue attacks are rising. Phishing kits now capture session tokens.
Modern identity access management security requires:
- Phishing-resistant MFA
- Hardware keys or passkeys
- Conditional access policies
If MFA can be socially engineered, it is not strong enough.
D. Zero Trust Access: Verify First, Trust Later
Zero Trust assumes no identity or device is inherently trusted.
Every request is verified based on:
- User identity
- Device posture
- Location
- Risk signals
Identity security challenges increase when Zero Trust is implemented partially.
It must extend across SaaS, cloud, on-prem, and APIs.
E. Non-Human Identities: The Access Risk Most Teams Overlook
One of the fastest-growing identity security challenges in 2026 is non-human identities.
These include:
- Service accounts
- API tokens
- CI/CD pipelines
- AI agents
Many organizations manage human identities well, but ignore machine identities.
Yet service accounts often have excessive, never-expiring privileges.
Identity security best practices now require lifecycle management for both human and non-human identities.
4. What Identity Security Challenges Are Enterprises Still Struggling With in 2026?
Even with modern tools, identity security challenges persist.
Here’s what enterprises still get wrong.
A. Machine and Service Account Identities Are Multiplying Fast
Cloud-native environments create thousands of service accounts.
Many are:
- Hard-coded into applications
- Never rotated
- Poorly documented
These non-human identities expand the attack surface silently.
B. Shadow IT Is Widening the Identity Attack Surface Without Anyone Noticing
Every unapproved SaaS app creates new login credentials and OAuth permissions.
Shadow IT increases identity security challenges because:
- IT does not see new app connections
- Access is not governed centrally
- MFA policies may not apply
Identity security for enterprises must include SaaS discovery and governance, not just directory controls.
C. Access That Piles Up Over Time and Never Gets Cleaned Up
Privilege creep is real.
Employees change roles but keep old permissions. Contractors stay active longer than expected.
Without automated reviews, identity access management security becomes bloated.
And bloated access is dangerous access.
D. Phishing That’s Getting Harder to Spot Every Quarter
AI-powered phishing campaigns now mimic writing styles and internal communication patterns.
Even strong security awareness training cannot eliminate human error.
This makes phishing-resistant MFA and risk-based access essential identity security best practices.
E. SaaS Sprawl Making Full Identity Visibility Nearly Impossible
The average enterprise uses hundreds of SaaS applications.
Many exist outside core IAM systems.
This fragmentation creates identity security challenges because:
- Access is distributed
- Provisioning is inconsistent
- Deprovisioning is manual
Also Read: The Ultimate Shadow IT Checklist (Risk Assessment + Controls)
5. Which Identity Security Best Practices Are Actually Worth Implementing?
With so much noise in the market, here are identity security best practices that consistently deliver impact.
- Automate provisioning and deprovisioning across all apps
- Implement phishing-resistant MFA and passkeys
- Run continuous access reviews, not annual audits
- Govern non-human identities with lifecycle policies
- Integrate SaaS discovery into your identity security platform
Identity security for enterprises is effective only when visibility and enforcement are continuous.
6. How CloudEagle.ai Helps Close the Gaps in Your Identity Security Program?
Identity security programs are breaking under SaaS sprawl, shadow IT, and AI adoption. Traditional IAM tools were not built for an environment where 60 percent of SaaS and AI applications operate outside IT visibility.
That is the identity blind spot.
CloudEagle.ai moves organizations from reactive identity access management security to proactive, AI-powered identity governance built for SaaS-native enterprises.
Here’s how.
A. Eliminates Shadow IT Blind Spots
Many AI tools and SaaS apps never pass through your identity provider.
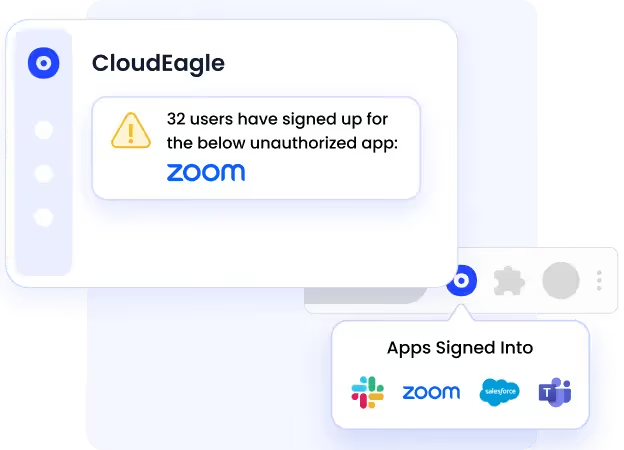
CloudEagle.ai:
- Detects apps using SSO logs, browser activity, and finance systems
- Correlates login data with spend signals
- Flags unapproved or duplicate applications
- Generates shadow IT reports with remediation workflows
IT gets visibility into every app employees use, not just SSO-governed apps.
B. Automates Provisioning and Deprovisioning Across All Apps
Manual onboarding and fragmented offboarding create serious identity security challenges.
The 2025 IGA report shows 48 percent of ex-employees retain access post-termination.

CloudEagle.ai:
- Enables zero-touch onboarding by role, department, and location
- Automates offboarding across all SaaS apps
- Enforces time-bound contractor access
- Maintains complete audit trails
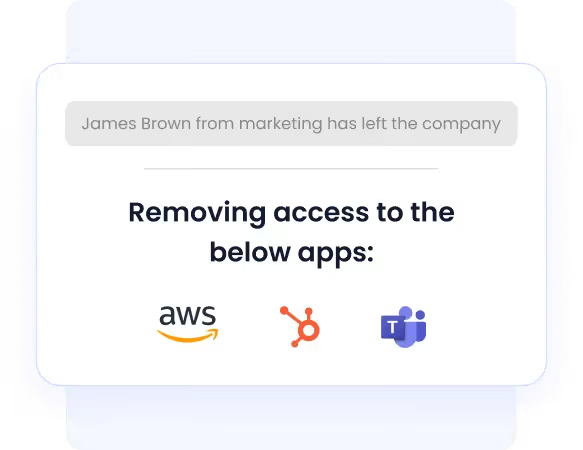
This eliminates orphaned accounts and reduces insider risk.
C. Replaces Manual Reviews with Continuous Governance
Most enterprises still rely on periodic access reviews.
CloudEagle.ai replaces that with:

- Continuous, automated access reviews
- Risk-based user flagging
- Just-in-time access controls
- SOC2-ready audit logs
Instead of reactive cleanup, identity security becomes continuous and adaptive.
D. Controls Excessive and Privileged Access
Privilege creep remains one of the biggest identity security challenges in 2026.
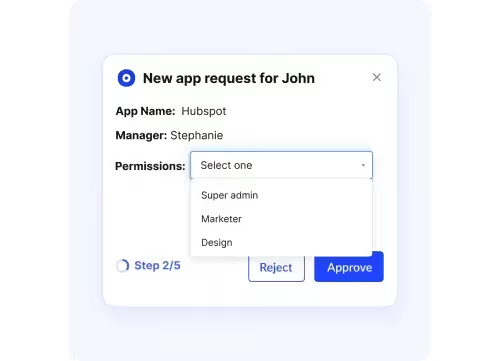
CloudEagle.ai:
- Enforces least-privilege access
- Automates role reassignment
- Detects high-risk users and unusual AI usage
- Centralizes app access through a role-based catalog
This reduces audit findings and limits lateral movement during breaches.
E. Connects Identity Security with SaaS Cost Governance
Most identity security platforms focus only on access.
CloudEagle.ai connects governance with optimization by:
- Identifying duplicate applications
- Automating license harvesting
- Benchmarking spend
- Managing renewals
Enterprises typically reduce SaaS spend by 10 to 30 percent while strengthening identity security for enterprises.
In A Nutshell
Identity security is no longer just about authentication. It is about controlling access across humans, machines, SaaS apps, and AI tools in an environment that keeps expanding.
Enterprises are still getting identity security wrong because visibility is fragmented, access piles up over time, and traditional IAM tools were not built for SaaS-native, AI-driven environments.
CloudEagle.ai helps close identity security gaps by extending governance beyond SSO, automating access reviews, eliminating shadow IT blind spots, and connecting identity control with SaaS cost optimization.
Book a free demo with CloudEagle.ai and strengthen your identity security before small access gaps become major breaches.
Want to see how CloudEagle.ai actually works before booking a call? Take a self-guided walkthrough.
See It in Action: CloudEagle Product Walkthrough
Frequently Asked Questions
- What are the challenges in security?
Modern security challenges include identity compromise, phishing attacks, SaaS sprawl, shadow IT, excessive privileges, non-human identity growth, and limited visibility across cloud and AI environments.
- What are the 5 C’s in security?
The 5 C’s in security commonly refer to Change, Compliance, Cost, Continuity, and Complexity. These represent the operational pressures organizations must balance while maintaining strong security controls.
- What are some of the challenges related to identity management?
Key identity management challenges include privilege creep, orphaned accounts, fragmented SaaS access, manual access reviews, non-human identity sprawl, and difficulty detecting unauthorized AI or app usage.
- What are the 4 pillars of IAM?
The four pillars of IAM are authentication, authorization, user management (provisioning and deprovisioning), and auditing or governance.
- What are the 4 A’s of security?
The 4 A’s of security are Authentication (verifying identity), Authorization (granting access), Accounting (tracking activity), and Auditing (reviewing and validating access and behavior).

%201.svg)









.avif)




.avif)
.avif)




.png)





