HIPAA Compliance Checklist for 2025

In 2025, SaaS security stopped being a theoretical risk and became an operational crisis.
Enterprises weren’t breached because of zero-day exploits. They were breached because of excessive permissions, dormant accounts, shadow AI tools, and auto-renewed apps that no one was actively governing.
The surge in SaaS security incidents exposed a hard truth: most organizations had visibility, but not governance. For security leaders, the question is no longer "could we be breached?", it's "are we ready for what's coming next?"
This blog breaks down what drove SaaS data breaches in 2025, how AI security risks reshaped the threat landscape.
Did you know 67% of employees at Fortune 1000 companies use unapproved SaaS applications, putting your organization at serious compliance and security risk? Here's what that means for your security posture in 2026.
TL;DR
- SaaS security breaches surged in 2025 due to shadow IT sprawl, misconfigured access controls, overprivileged accounts, and supply chain vulnerabilities at SaaS vendors.
- AI supercharged attacker capabilities, from hyper-personalized phishing that bypassed traditional filters to automated vulnerability scanning that shortened exploit windows to minutes.
- AI-embedded SaaS tools created hidden data risks, and employees unknowingly fed sensitive data into AI-powered SaaS features, exposing it to third-party model providers without IT visibility.
- AI governance security is now non-negotiable; organizations without clear policies on AI-enabled SaaS usage are flying blind on one of the fastest-growing risk surfaces in their stack.
- Preparing for 2026 means going proactive, full SaaS discovery, least-privilege access enforcement, continuous posture management, and security-integrated procurement are the baseline, not the differentiator.
1. Why Did SaaS Security Breaches Spike in 2025?
The explosion in SaaS adoption created breaches not because organizations moved to the cloud, but because governance failed to scale with it.
By 2025, the average mid-sized enterprise will be running more than 500 SaaS applications. Many were procured outside formal IT approval processes, configured inconsistently, and monitored only periodically.
Without continuous visibility into who had access to what and why, organizations unknowingly created persistent attack paths through overprivileged accounts, dormant users, and unreviewed third-party integrations.
Several compounding factors drove the spike in SaaS security breaches:
- Employees adopted tools without IT knowledge, creating unmonitored entry points that attackers were quick to exploit. Research indicates 30 – 40% of enterprise SaaS apps are classified as shadow IT, tools that bypass security reviews, access controls, and compliance requirements entirely.
- Overprivileged accounts, dormant user licenses, and excessive OAuth permissions left massive gaps in SaaS security postures. Privilege creep, where users accumulate access they no longer need, became one of the most exploited attack surfaces of the year.
Overprivileged accounts don't fix themselves. See how one enterprise brought every privileged user access under centralized governance and closed the gaps attackers rely on most. Here's how exterprises fix it →
- SaaS vendors themselves became targets, with breaches at one vendor cascading into SaaS data breaches for dozens of their customers. Understanding the common causes of data breaches, from third-party vendor weaknesses to phishing.
- Phishing and credential stuffing campaigns became dramatically more effective, fueled by AI-generated lures that bypassed traditional detection. SSO security risks were particularly acute; a single compromised identity provider credential could unlock dozens of downstream SaaS applications simultaneously.
The common thread running through nearly every high-profile SaaS breach in 2025? Poor visibility. Organizations simply didn't know what applications their employees were using, who had access to what, or when something anomalous was happening, until it was too late.
Podcast Alert!
Want to hear how IT leaders are tackling this in real time? Tune into our podcast , "Optimizing Shadow IT Risks and Innovations in SaaS Management", and learn how top teams are getting ahead of Shadow IT before it spirals out of control.
Listen now→
2. How Did AI Change the SaaS Threat Landscape?
If 2024 put AI on the threat map, 2025 made it impossible to ignore. AI security risks stopped being hypothetical and started showing up in actual breach reports, post-mortems, and security advisories that IT teams were reading every week.
Here's how it played out across three distinct attack patterns:
AI-Powered Phishing Got Scarily Good
Attackers used large language models to write phishing emails that looked and sounded like they came from inside your organization matching tone, terminology, and even the writing style of specific colleagues.
The old tells? Gone. No grammar errors, no generic greetings, no obvious red flags.
Traditional email security tools weren't built for this. The result was a surge in SaaS credential compromise at organizations that hadn't kept their security awareness training current or hadn't enforced strong MFA across their SaaS stack.
The failure here wasn't a technical one. It was a governance one.
Automated Vulnerability Discovery
- AI-driven tools scanned entire SaaS environments in minutes, not hours
- Misconfigured APIs, weak OAuth grants, and exposed data stores were found before security teams even detected the probe
- Every unreviewed permission is now a potential breach vector
- Gartner estimates 75% of security failures by 2026 will stem from mismanaged identities, not infrastructure
Shadow AI Inside Your SaaS Stack
- Employees fed sensitive data into AI-powered CRMs, writing tools, and analytics platforms without knowing where it went
- AI features embedded in popular SaaS apps were ingesting confidential data and surfacing it to third-party model providers
- Most organizations only found out after the damage was done
- Discovering what shadow AI tools are running across your stack is now a foundational security requirement — not optional
3. What Role Does AI Governance Play in SaaS Security?
AI governance security emerged as a critical discipline in 2025, and for good reason.
As AI capabilities became embedded across the SaaS stack, organizations without clear policies for AI usage found themselves exposed in ways their existing security frameworks. Effective AI governance in a SaaS context goes far beyond writing a policy document. It means:
- Continuously discovering AI-enabled applications across your portfolio
- Understanding what data each tool accesses and processes
- Evaluating vendor AI practices as part of your SaaS procurement and compliance workflow
- Establishing guardrails that stop employees from inadvertently exposing sensitive data through AI features they may not fully understand
The challenge is compounded by how hidden AI inside SaaS actually is. Employees don't always know when they're using an AI feature; it might be a "smart compose" suggestion in a document tool.
Without dedicated tooling to surface these features, the hidden risks of poor SaaS compliance compound silently, across hundreds of applications, without anyone noticing.
Going deeper on compliance and risk? Watch our webinar, "Managing Risk and Compliance in Your SaaS Stack", to see how security teams are operationalizing these insights today. Watch now →
4. What Are the SaaS Security Best Practices IT Leaders Must Follow in 2026?
The lessons from 2025 are clear. Reactive, perimeter-focused security is no longer sufficient for the SaaS era. Here are the SaaS security best practices organizations must prioritize heading into 2026.
1. Achieve Full SaaS Visibility
You cannot secure what you cannot see. Comprehensive SaaS discovery, including shadow IT and AI-enabled applications, must become the foundation of your security posture.
The shadow IT assessment checklist is a practical starting point, but automated, continuous discovery is the long-term answer. CloudEagle.ai's automated SaaS discovery continuously inventories your entire application landscape, flagging new tools, unauthorized apps, and risky integrations in real time.
2. Enforce Least-Privilege Access Across Your SaaS Portfolio
Overprivileged accounts were a leading contributor to SaaS data breaches in 2025. Implementing least-privilege access policies and enforcing them consistently across your entire SaaS estate dramatically reduces your attack surface.
This means regular access reviews for SaaS, automated deprovisioning of dormant users, and tight controls on admin-level permissions. Stopping privilege creep before it accumulates is far cheaper than remediating a breach after the fact.
3. Build a SaaS Security Posture Management (SSPM) Program
SaaS security posture management tools continuously assess your SaaS configurations against security benchmarks, identifying drift, misconfigurations, and compliance gaps before attackers can exploit them. With AI security risks evolving rapidly, manual configuration audits simply aren't fast enough.
A practical SSPM checklist covers app-level security controls, over-privileged users, shadow IT exposure, and monitoring gaps, areas that account for over 45% of SOC 2 and ISO 27001 audit findings.
4. Integrate Security Into SaaS Procurement
One of the most effective SaaS security best practices is shifting security assessments earlier in the procurement cycle. Before a new SaaS tool is approved, evaluate it against your security and compliance requirements, including its AI capabilities, data retention policies, and subprocessor relationships.
CloudEagle.ai's vendor risk assessment capabilities help procurement and security teams work together to evaluate vendor security postures before contracts are signed.
5. Govern AI Usage Across Your SaaS Stack
Given the AI security risks that materialized in 2025, AI governance can no longer be an afterthought. Define clear policies for which AI-powered SaaS tools are approved, what data they can access, and how employees should use AI features in sanctioned applications.
Use shadow AI discovery solutions to surface tools operating outside IT visibility, and ensure your SaaS management platform provides enforcement, not just documentation, of your AI governance policies.
6. Prepare for Faster Incident Response
AI in cybersecurity is increasingly being used on the defensive side, too. Security teams are deploying AI-powered threat detection and response tools to match the speed of AI-assisted attacks.
Ensure your incident response playbooks account for SaaS-specific breach scenarios, including third-party vendor incidents, OAuth abuse, and AI data leakage events. SaaS management solutions that integrate with SSO and surface real-time anomalies are critical to shortening detection and response windows.
7. Apply a Zero Trust Framework Across Identity and Access
The Zero Trust security framework, never trust, always verify, is purpose-built for the SaaS era. Rather than assuming users inside the network perimeter are safe, Zero Trust requires continuous authentication based on identity, device posture, risk level, and location.
When combined with least-privilege access controls and strong Privileged Access Management (PAM), it becomes one of the most resilient defenses against credential-based SaaS attacks.
5. How Does CloudEagle.ai Help You Stay Ahead of SaaS Security Threats?
As SaaS stacks grow and AI tools spread across every team, the attack surface expands faster than IT and security teams can manage. CloudEagle.ai is an AI-powered SaaS Security, Management, and Identity Governance platform that gives enterprises a unified command center to discover, secure, govern, and optimize their entire SaaS and AI ecosystem.
With 500+ direct integrations and 30-minute onboarding, security teams gain immediate visibility and control, without disrupting existing tools or workflows.
Key risks CloudEagle helps enterprises address heading into 2026:
- Shadow SaaS and unauthorized AI tools operating outside IT oversight
- Over-provisioned access and orphaned identities are creating exploitable gaps
- Manual onboarding and offboarding leave security windows open
- Ungoverned AI adoption exposing sensitive data to unvetted platforms
Full Visibility Into Shadow SaaS and Unauthorized AI

Most breaches start where security teams have no visibility. Unauthorized apps, forgotten accounts, and unapproved AI tools are among the most common entry points.
CloudEagle discovers applications across browsers, firewalls, finance systems, SSO, and MDM tools simultaneously. This multi-source approach surfaces shadow SaaS and unauthorized AI that single-source discovery tools miss.
Least Privilege, Continuously Enforced
Over-provisioned access is one of the most exploited vulnerabilities in modern enterprises. Quarterly access reviews are too infrequent, too manual, and too prone to rubber-stamping to provide meaningful protection.
CloudEagle automates continuous access reviews across all SaaS applications, flagging:
- High-risk users and accounts with excessive privileges
- Orphaned identities and ex-employees with active access
- Standing privileged access without a business justification
Deprovisioning is automated, and evidence is attached automatically, eliminating manual documentation for audits. For Zero Trust alignment, CloudEagle also supports time-based and just-in-time access, granting access only when needed, for exactly as long as required.
Automated Onboarding and Offboarding With No Manual Gaps

Every minute of delay in offboarding is a security window. Manual processes across dozens of applications are slow, inconsistent, and difficult to audit.
CloudEagle detects employee exits through HRIS integration and automatically deprovisions access across all connected SaaS apps, including those not behind an IdP like Okta. Licenses are returned to the pool immediately. The full offboarding trail is documented automatically.
For onboarding, role-based automation ensures new employees receive the right access from day one, based on role and location, with no manual provisioning required from IT.
AI Governance Built for 2026
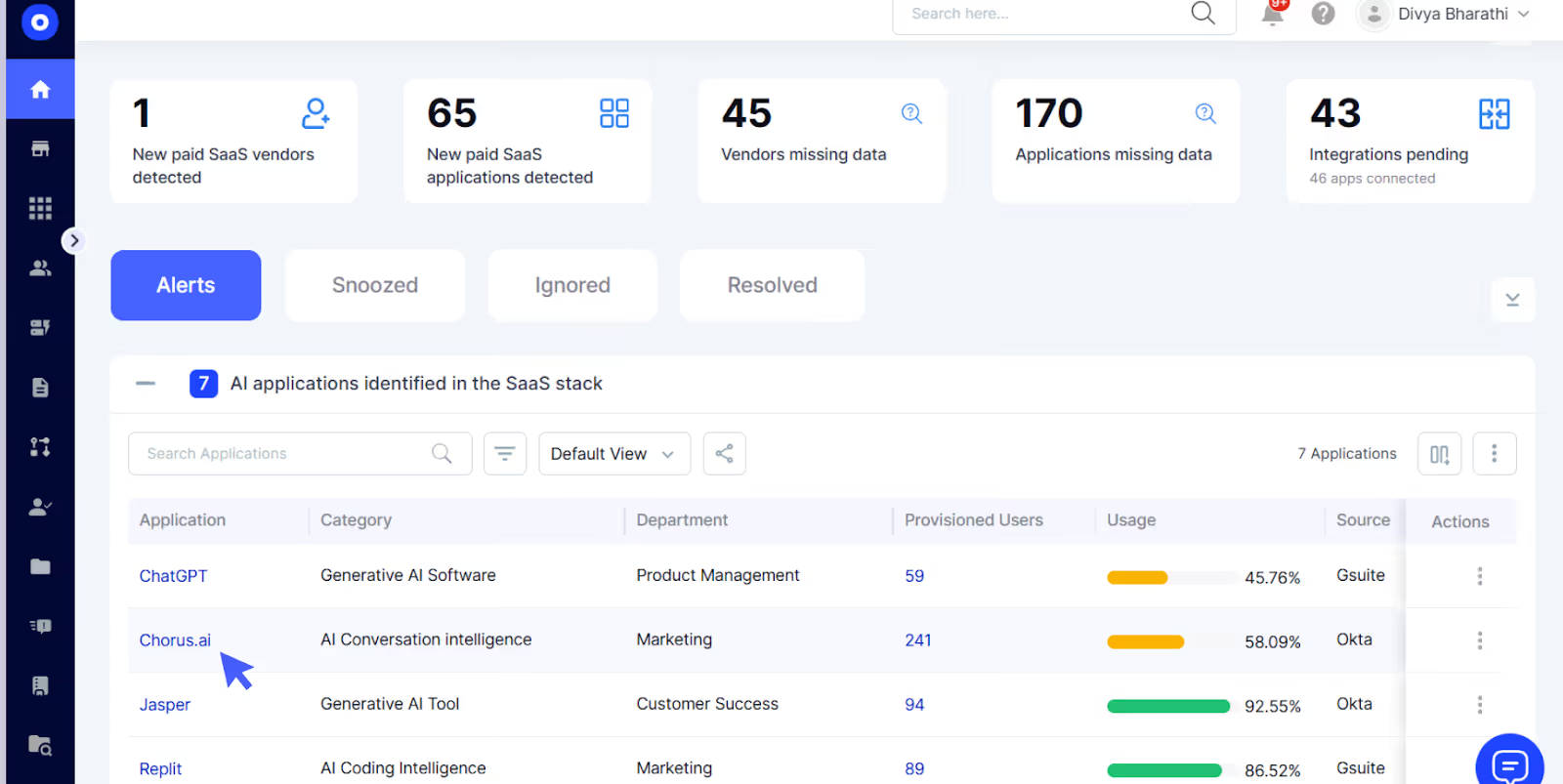
CloudEagle maintains a proprietary inventory of AI applications through its SaaSMap, correlating browser, Zscaler, and CrowdStrike data to give security teams a complete view of AI usage across the organization. From there, teams can:
- Enforce approval policies for AI tools
- Block access to unauthorized AI applications in real time
- Maintain audit-ready logs of AI tool usage across the organization
Why Security Teams Choose CloudEagle.ai
Organizations still relying on spreadsheets, manual reviews, and disconnected point tools are the most exposed heading into 2026. CloudEagle replaces that fragmented approach with continuous, automated SaaS and AI security governance across the full identity and application lifecycle.
- 500+ direct integrations across IT, HR, Finance, and Security systems
- 30-minute onboarding with immediate governance from day one
- Continuous lifecycle management replaces point-in-time audits
- No-code, Slack-enabled workflows requiring no engineering dependency
6. How CloudEagle.ai Helps You Stay Ahead of SaaS Security Threats
The SaaS security breaches of 2025 were a wake-up call. But a wake-up call only matters if you act on it.
The organizations that come out ahead in 2026 won't be the ones with the most security tools; they'll be the ones with the best visibility, governance, and execution. That means knowing every SaaS application in use, governing how AI features access your data, and closing access gaps before attackers find them.
That's exactly what CloudEagle.ai is built for. From automated SaaS discovery and AI governance to access controls and audit-ready reporting, CloudEagle.ai gives IT and security teams everything they need to stay ahead, not just catch up.
Book a Demo to see how CloudEagle.ai customers are already closing the gaps that defined 2025's biggest breaches.
Frequently Asked Questions
1. Why are SaaS security breaches increasing?
Breaches are rising due to rapid SaaS adoption, shadow IT growth, misconfigured access, and AI-powered attacks. Security controls haven’t kept pace with SaaS sprawl, leaving visibility gaps that attackers exploit.
2. How does AI increase SaaS security risks?
AI enables automated phishing, faster vulnerability discovery, and evasion tactics. AI features inside SaaS apps also create data exposure risks when employees input sensitive data without governance controls.
3. Why did SaaS security breaches spike in 2025?
The 2025 spike was driven by SaaS sprawl, weak access controls, AI-powered phishing, and vendor supply chain risks. Limited SaaS visibility meant many breaches went undetected longer.
4. How is AI changing the SaaS threat landscape?
AI helps attackers scale phishing and exploit weaknesses faster. Defensively, AI improves anomaly detection and response. Organizations must combine AI-driven defense with strong AI governance.
5. How can organizations prevent SaaS breaches in 2026?
Prevention requires full SaaS visibility, least-privilege access, continuous posture management, secure procurement, and AI governance. CloudEagle.ai centralizes visibility and access control.

%201.svg)









.avif)




.avif)
.avif)




.png)





