HIPAA Compliance Checklist for 2025

If you’ve ever said, “We’re SOC 2 compliant,” and then immediately felt your eye twitch, this one’s for you.
Here’s the thing no one says out loud: compliance fatigue is real. According to a 2024 Drata report, over 60% of companies say preparing for audits consumes significant internal bandwidth, often pulling security teams away from actual security work.
So yes, you passed your SOC 2 audit.
Now you get to live inside it.
SOC 2 compliance challenges don’t usually come from misunderstanding the framework. They come from trying to keep everything aligned while the business keeps growing, hiring, buying tools, and moving fast.
Let’s talk about where it actually gets messy.
TL;DR
- SOC 2 compliance challenges usually stem from manual evidence collection, inconsistent access reviews, and SaaS sprawl.
- Passing a SOC 2 audit is easier than maintaining continuous compliance afterward.
- Shadow IT and third-party vendor risk are major blind spots for enterprises.
- SOC 2 compliance automation reduces audit prep time and improves year-round readiness.
- CloudEagle.ai helps centralize SaaS visibility, automate access reviews, and maintain audit-ready documentation.
1. What Is SOC 2 Compliance, and Why Do Enterprises Still Get It Wrong?
SOC 2 (System and Organization Controls 2) is a voluntary audit framework developed by the AICPA for service providers, especially SaaS and cloud companies.
It confirms that an organization has controls in place to protect customer data across security, availability, processing integrity, confidentiality, and privacy.
SOC 2 is built around five trust criteria:
- Security
- Availability
- Processing Integrity
- Confidentiality
- Privacy
That part isn’t complicated.
What makes SOC 2 compliance requirements painful at enterprise scale is this: the controls are simple, but the environment isn’t.
You don’t fail because you don’t have policies.
You struggle because:
- Access changes daily
- SaaS tools multiply quietly
- Vendors don’t all behave the same
- Evidence lives everywhere
2. The SOC 2 Compliance Challenges Most Enterprises Don’t See Coming
SOC 2 compliance challenges for enterprises usually arise from underestimating the operational and documentation shift required beyond basic IT security fixes.
Common hurdles include maintaining continuous compliance, managing third-party risk, and relying too heavily on manual, error-prone evidence collection.
Here’s what usually happens.
A. Evidence Collection That Eats Up Weeks Before Every Audit
You know the drill.
Auditors ask for:
- Access review records
- Offboarding documentation
- Vendor due diligence files
- Change management logs
And suddenly your team is screenshotting dashboards like it’s a full-time job.
According to Vanta’s 2024 State of Compliance report, companies spend an average of 100–150 hours preparing for a single SOC 2 audit cycle. That’s weeks of manual collection.
B. Passing the Audit Is Easy. Staying Compliant After Is Not
There’s a surge of discipline before an audit.
Policies are updated. Reviews are completed. Logs are checked.
Then the audit passes.
Three months later:
- A few access reviews slip
- A vendor hasn’t been reassessed
- A new SaaS tool enters the stack
SOC 2 compliance automation becomes critical here. Without continuous monitoring, compliance becomes seasonal.
And seasonal compliance doesn’t hold up well under surprise assessments.
C. Access Controls That Look Fine on Paper Until They’re Not
On paper, everything looks great.
You have:

- Role-based access
- Quarterly reviews
- Offboarding checklists
In practice?
People change roles. Contractors stick around. Admin privileges accumulate.
IBM’s 2023 Cost of a Data Breach report found that breaches caused by compromised credentials cost organizations an average of $4.45 million globally. Access governance isn’t theoretical.
D. The SaaS App Nobody Approved That Just Became Your Auditor’s Problem
Shadow IT is the quiet villain of SOC 2 compliance challenges.
Finance sees a charge.
IT may not.
Auditors ask for:
- Vendor security posture
- Data processing agreements
- Risk assessments
And now you’re scrambling to evaluate a tool that’s been in use for eight months.
SOC 2 challenges for enterprises increasingly intersect with SaaS discovery.
E. Running SOC 2 Alongside HIPAA, ISO 27001, and GDPR
You’re rarely managing just one framework.
SOC 2 overlaps with:
The problem isn’t overlap. It’s duplication.
Teams answer the same control question three different ways across three different documents.
Compliance work multiplies quietly.
F. Third-Party Vendors Who Don’t Share Your Standards
Your internal controls might be tight.
Your vendors? Mixed.
SOC 2 compliance requirements extend to vendor management. That means collecting SOC reports, questionnaires, and proof of security posture.
But vendors don’t operate on your audit timeline.
And you’re still responsible.
G. No Dashboard, No Visibility, No Idea Where You Stand
This is the quietest but most dangerous issue.
Policies exist.
Reviews happen.
But leadership cannot answer:
- Are we audit-ready today?
- Which access reviews are pending?
- Which vendors are overdue?
Without centralized visibility, SOC 2 compliance challenges remain invisible until audit time.
And audit time is not when you want surprises.
3. How Enterprises Are Actually Solving These SOC 2 Compliance Challenges?
Enterprises are shifting from manual, spreadsheet-driven SOC 2 audits to automated, continuous compliance platforms.
Tools like CloudEagle.ai, Vanta, and Sprinto help manage complex environments, cut manual evidence collection by up to 70–80%, and maintain audit readiness year-round.
Enterprises reducing SOC 2 challenges for enterprises are doing a few things differently:
- Automating evidence collection instead of gathering it manually
- Running continuous access reviews instead of quarterly scramble sessions
- Discovering SaaS apps before auditors do
- Centralizing vendor tracking
- Using SOC 2 compliance automation tools to maintain ongoing visibility
Manual coordination works with 50 employees.
It struggles at 500.
4. Where CloudEagle.ai Fits Into Your SOC 2 Compliance Strategy?
SOC 2 compliance challenges usually appear in access governance, documentation gaps, and SaaS sprawl. CloudEagle.ai addresses these areas by automating the operational pieces that often fail under scale.
A. Automated Access Reviews Across Your SaaS Stack
Access reviews are a core SOC 2 compliance requirement, but manual tracking creates inconsistency.
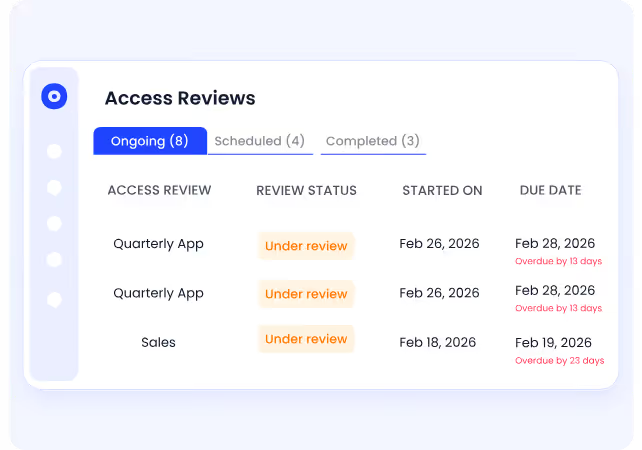
With CloudEagle.ai, you get:
- Centralized visibility into user access across all SaaS apps
- Automated review workflows sent directly to managers
- Flag for inactive, overprivileged, or high-risk users
- Audit-ready records of review completion
This ensures reviews are consistent, traceable, and completed on time.
B. Role-Based Onboarding and Instant Offboarding
Lingering access is one of the most common SOC 2 audit challenges.
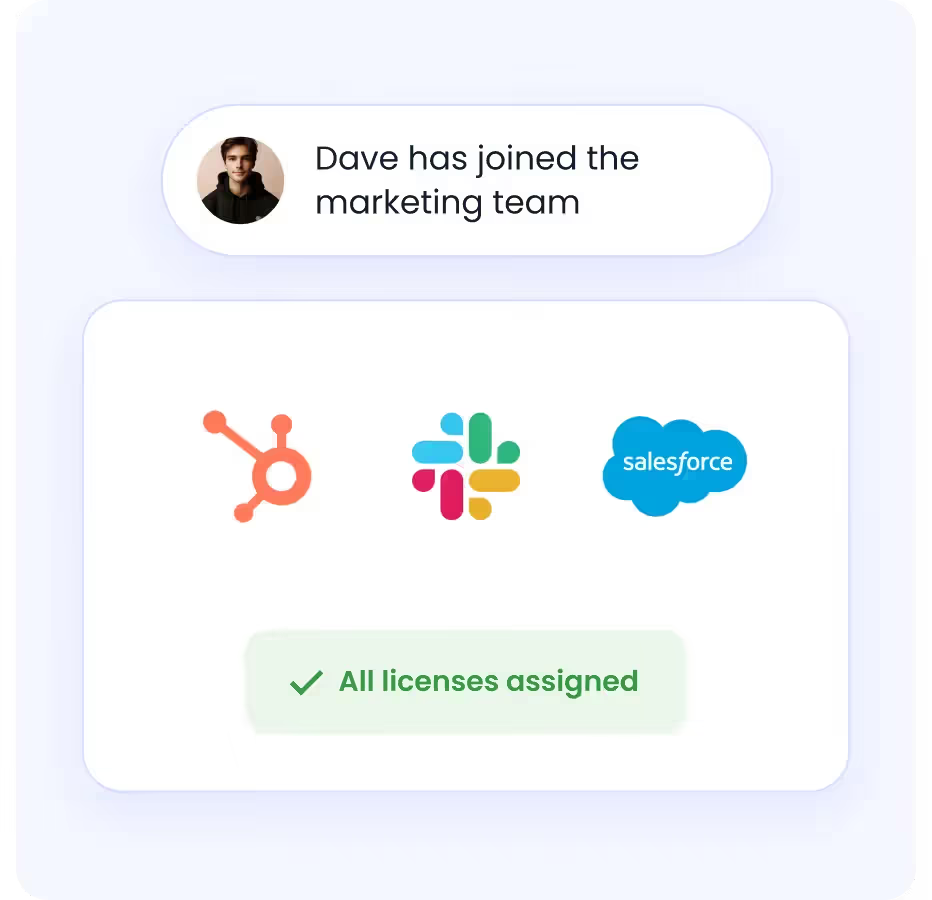
CloudEagle.ai supports:
- Automated role-based provisioning
- Immediate deprovisioning upon exit
- Access updates tied to role changes
- Elimination of manual checklist gaps
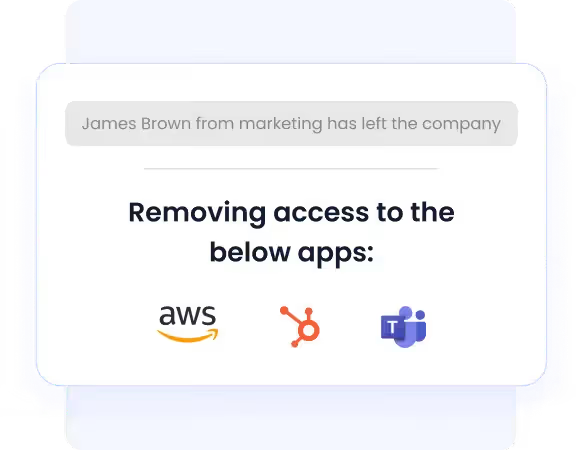
Access stays aligned with employment status and role.
C. SOC 2-Ready Audit Logs and Documentation
SOC 2 compliance requires proof of enforcement, not just written policy.
CloudEagle.ai provides:
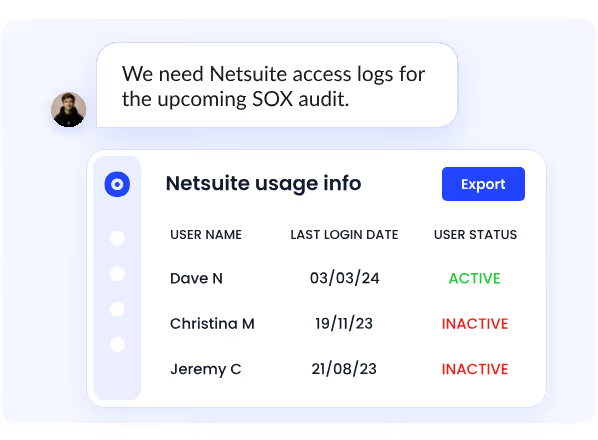
- Timestamped audit logs of access changes
- Documented approval workflows
- Provisioning and deprovisioning history
- Exportable reports for auditors
Evidence becomes structured instead of reactive.
D. SaaS Discovery and Shadow IT Visibility
Unapproved SaaS tools often create hidden compliance exposure.
CloudEagle.ai helps you:
- Discover all connected SaaS applications
- Identify unsanctioned tools
- Map user access across apps
- Extend compliance reviews to every system in use
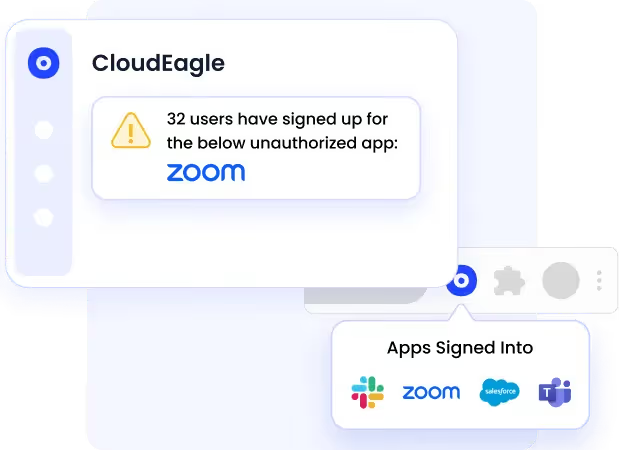
You can’t govern what you can’t see.
E. Centralized Compliance Visibility
SOC 2 compliance automation requires ongoing oversight.
CloudEagle.ai enables:
- A unified dashboard for access and vendor tracking
- Visibility into pending reviews
- Identification of compliance gaps
- Continuous readiness monitoring
Compliance shifts from audit-time activity to operational discipline.
Conclusion
SOC 2 compliance challenges rarely happen because teams don’t understand the rules. They happen because the business keeps changing while controls stay static. Growth, new tools, and shifting access quietly stretch compliance over time.
The audit itself isn’t the hardest part. Staying aligned between audits is. Without continuous visibility into access, vendors, and evidence, compliance turns into a periodic scramble instead of steady operations.
CloudEagle.ai helps enterprises bring structure back by centralizing SaaS discovery, automating access reviews, and aligning vendor oversight with real-time visibility.
Book a free demo and see where your SOC 2 posture stands today.
Frequently Asked Questions
- What are the 5 criteria for SOC 2?
The five SOC 2 Trust Services Criteria are Security, Availability, Processing Integrity, Confidentiality, and Privacy. Organizations are audited against one or more of these principles depending on their services.
- What are the challenges of compliance?
SOC 2 compliance challenges include manual evidence collection, inconsistent access reviews, third-party vendor risk, SaaS sprawl, and maintaining continuous compliance between audits.
- How hard is it to get SOC 2 compliance?
Getting SOC 2 compliance requires documented controls and structured processes. For enterprises, maintaining continuous compliance as systems and access change is often harder than the initial audits.
- What are SOC 2 compliance requirements?
SOC 2 compliance requirements include implementing and documenting controls related to security, access management, system monitoring, incident response, vendor oversight, and data protection.
- What are the 4 types of audits?
The four common audit types are financial audits, compliance audits, operational audits, and information systems audits. SOC 2 is classified as a compliance and IT audit.

%201.svg)









.avif)




.avif)
.avif)




.png)





