HIPAA Compliance Checklist for 2025

60% of SaaS and AI apps operate completely outside IT visibility, and that number is growing, says CloudEagle's 2025 IGA Report.
That is the reality most security and IT teams are working in. The SaaS environment moves fast, purchasing decisions are decentralized, and the compliance risk builds up quietly in the background. Unapproved tools grow.
This SaaS compliance checklist is built specifically for security and IT leaders who need continuous visibility, governance, and audit readiness across their SaaS stack.
This checklist is written to help you stay ahead of that. It walks through every layer of SaaS compliance in plain terms, with specific actions you can take at each stage.
Whether you are building your compliance program from scratch or tightening up an existing one, this is where to start.
TL;DR
- Shadow IT and unapproved AI tools are the number one source of SaaS compliance gaps in 2026.
- This SaaS compliance checklist highlights the core risks and controls security leaders must prioritize in 2026.
- Every SaaS tool you approve extends a degree of trust to that vendor and every third party they work with.
- GDPR, HIPAA, SOC 2, ISO 27001, and PCI DSS each have specific SaaS requirements, and most organizations are subject to more than one.
- Teams that rely only on periodic audits are always reacting. Automated, real-time visibility is what keeps you ahead.
1. SaaS Compliance Checklist for 2026: Step-by-Step Framework
Step 1: Discover and Inventory Every SaaS App in Use
You cannot protect what you do not know is there.
The average organization runs hundreds of active SaaS applications, and it never reviewed a large share of them.
Employees sign up for productivity tools, AI assistants, and file-sharing apps on their own, This is shadow IT. It is also where most SaaS compliance failures begin.
This is the foundation of any effective SaaS compliance checklist.
If you want to understand the full scope of what shadow IT looks like inside enterprise environments, this guide on how to manage shadow AI and shadow IT breaks it down in detail.
Step 2: Enforce Access Control and Identity Management
Employees accumulate more access than their role requires over time, especially when they change teams or take on new responsibilities. Former employees sometimes keep access for weeks after they leave because no one triggered the removal process.
Multiply this across hundreds of SaaS tools, and the exposure adds up fast.
The answer is not more manual access reviews.
For a closer look at how automated provisioning actually works in practice, see this breakdown of top automated provisioning tools.
Manual offboarding left ex-employees with active access across dozens of apps, a silent compliance risk. See how Rec Room closed those gaps with zero-touch offboarding and cut security risks overnight. Read the Case Study →
Step 3: Protect Data Across Every SaaS Application
Every SaaS tool your organization uses is handling data in some way, and you are responsible for how that data is protected, regardless of where it sits.
Regulations like GDPR, HIPAA, and SOC 2 place the data protection obligation on your organization, not your vendors.
Most organizations have strong controls in some tools and almost none in others. That inconsistency is precisely where audits fail, and breaches happen.
For a detailed look at what drove SaaS data breaches in 2025 and what changed in the threat landscape, this breakdown of AI and SaaS security breaches is worth reading before you finalize your data controls.
Step 4: Assess and Monitor Third-Party Vendor Risk
The moment you approve a SaaS tool, you are placing trust in that vendor and every company they work with behind the scenes.
If a vendor gets breached, loses a certification, or changes their data practices, the compliance impact lands on you. This is not a hypothetical.
Research shows that over 89 percent of third-party apps connected to Google Workspace can access sensitive data despite being flagged as medium or high risk.
Vendor assessments need to happen before a tool is approved, not as an afterthought after it is already in use. For a step-by-step framework on how to structure this process, see the vendor risk assessment checklist for secure vendor partnerships.
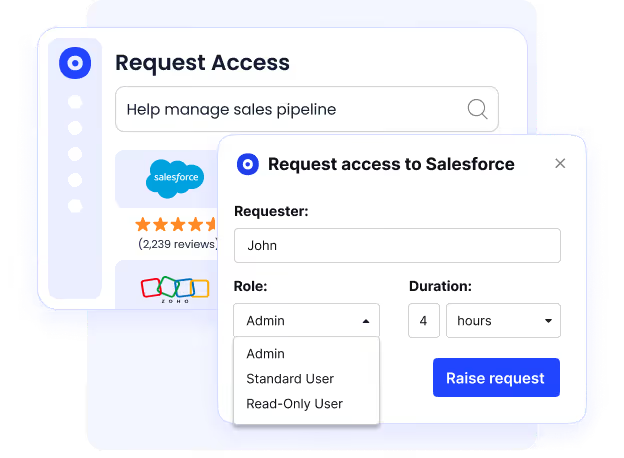
Step 5: Define Clear SaaS Usage Policies
A policy that nobody follows is not a policy. It is a document sitting in a folder.
Most organizations have an acceptable use policy in some form. Far fewer have made it easy enough for employees to actually follow.
When the process for requesting a new tool is confusing or slow, employees sign up on their own.
Clear policies, straightforward approval paths, and regular training are what bridge that gap.
Step 6: Map Your SaaS Stack to Compliance Frameworks
A strong SaaS compliance checklist must map your SaaS stack to the right compliance frameworks.The frameworks that apply to you depend on your industry, the data you work with, and where you operate.
For example, understanding ISO 27001 compliance steps for SaaS companies requires mapping access control, vendor management, and audit logging directly to Annex A controls, not treating ISO as a standalone checklist.
If your organization is subject to more than one framework simultaneously, which most are, this unified SOC 2, GDPR, and HIPAA SaaS compliance checklist shows how to map overlapping controls without running three separate programs.
Step 7: Set Up Continuous Monitoring and Alerts
A compliance review that runs twice a year will always be playing catch-up.
SaaS environments change constantly. Employees add new tools. Vendors revise their terms of service. Certifications expire. Access drifts.
Over-permissioned users, missed access reviews, growing compliance risk, Dezerv was fighting a losing battle with spreadsheets. See how they automated access reviews and got audit-ready in one cycle. Read the Case Study →
Step 8: Plan for Incidents and Offboarding
Even in a well-run environment, incidents happen. How your team responds in the first hours makes the difference between a manageable event and a regulatory investigation.
Offboarding is one of the most overlooked exposure points in SaaS compliance.
Research shows that 48 percent of former employees still have app access after termination when there is no automated system handling removal.
For a structured look at how to manage user access reviews across your SaaS stack and keep that number as close to zero as possible, this guide on user access review software covers the tooling and process in full.
2. How CloudEagle.ai Helps You Execute This Checklist
Knowing what strong SaaS compliance looks like is not the challenge. Executing your SaaS compliance checklist consistently across a fast-growing environment is. Executing it consistently across a fast-growing, AI-heavy, always-changing SaaS environment is.
Spreadsheets break. Quarterly reviews fall behind. Identity tools only cover apps behind SSO. Shadow IT and embedded AI features slip through the cracks.
Many teams evaluating the best security compliance tools for SaaS companies quickly realize that point solutions only address one layer of risk, identity, audit prep, or vendor monitoring, but rarely all three in one system.
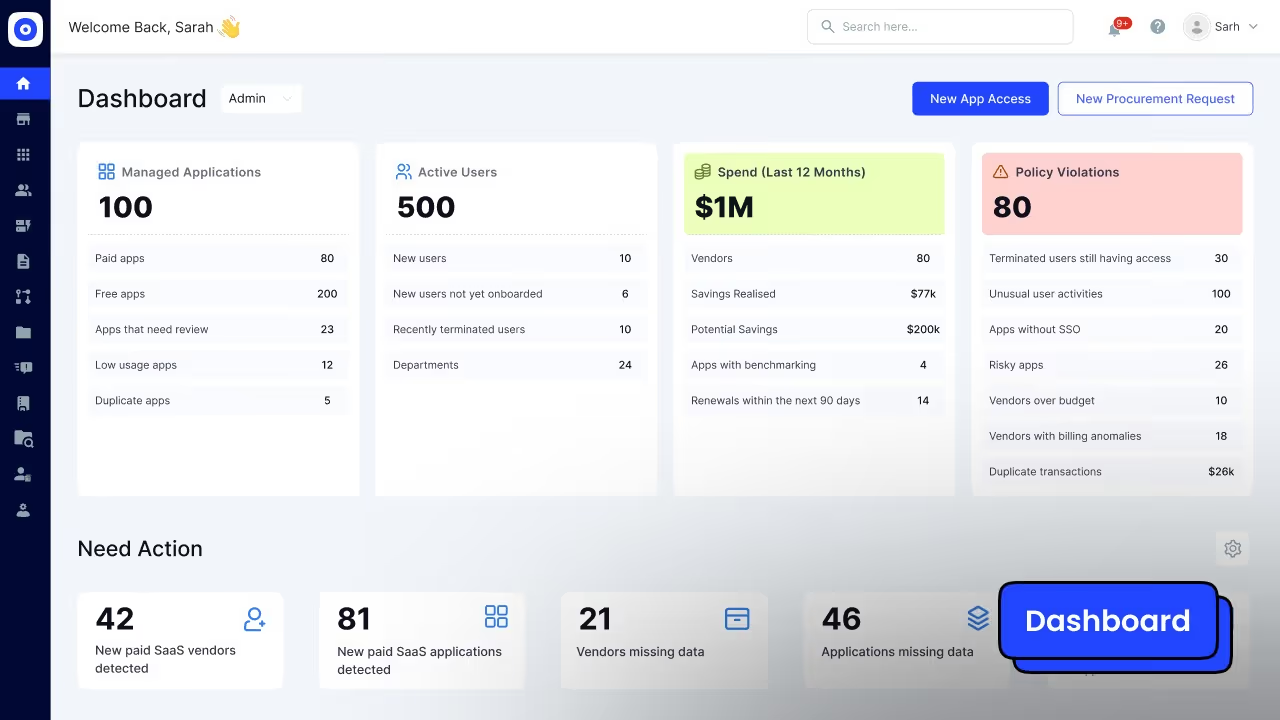
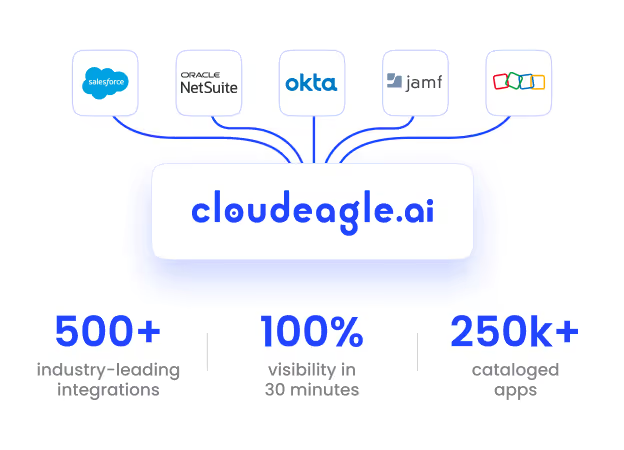
CloudEagle.ai is an AI-powered identity governance platform built to continuously discover, govern, optimize, and renew your entire SaaS ecosystem, not just the apps IT already knows about.
See how CloudEagle brings every layer of this checklist, discovery, access governance, vendor risk, and AI oversight into one automated platform. Watch the Product Walkthrough →
It is recognized in the 2025 Gartner Magic Quadrant for SaaS Management Platforms, and it centralizes SaaS visibility, access governance, AI risk detection, and cost optimization into one automated system.
Continuous Visibility Into Your Entire SaaS and AI Environment
Compliance starts with visibility, and most organizations do not have it.
CloudEagle uses 500+ integrations to automatically discover apps behind SSO, tools purchased on corporate or personal cards, free trials signed up with work emails, standalone AI tools like ChatGPT and Midjourney, and AI features embedded inside approved SaaS tools.
You can see a deeper breakdown of how this works in the guide on managing shadow AI and shadow IT with CloudEagle.
Zero-Touch Access Governance Without Manual Overhead
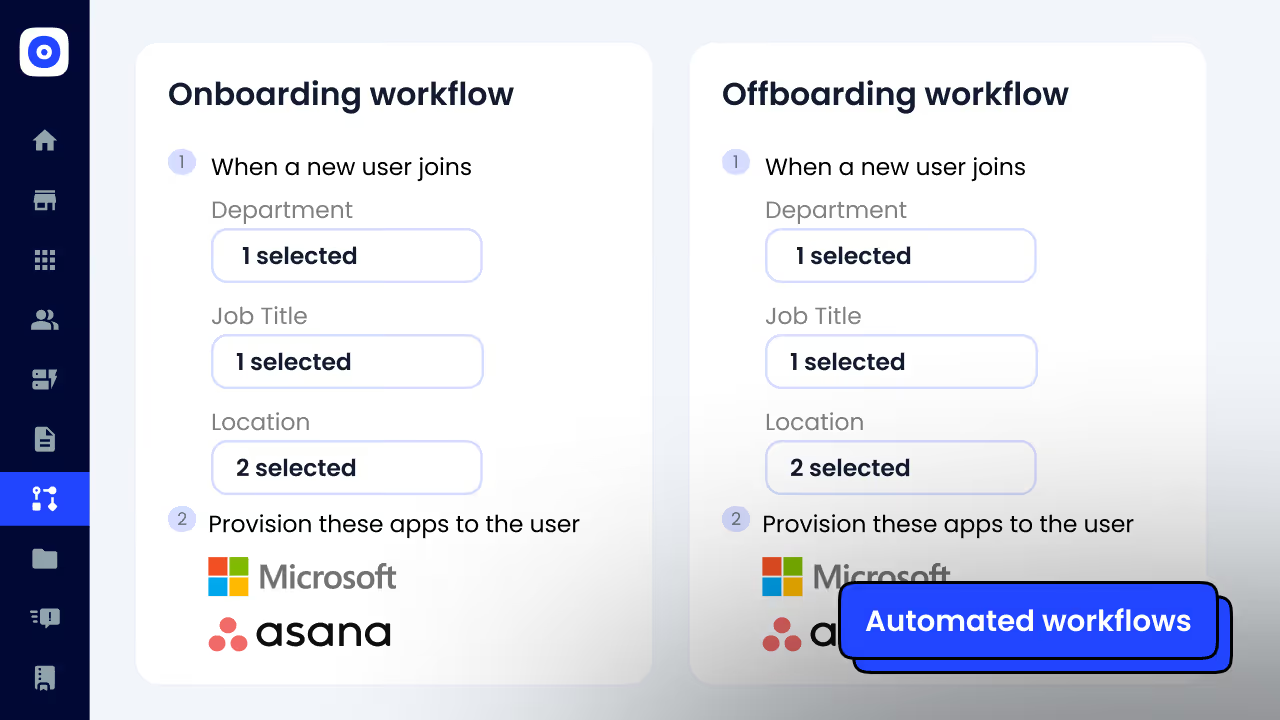
Manual onboarding, spreadsheet-based access reviews, and delayed offboarding are where compliance risk compounds.
This is why compliance automation tools for mid-market SaaS environments are gaining traction, growing companies need automation without the overhead of enterprise-grade complexity.
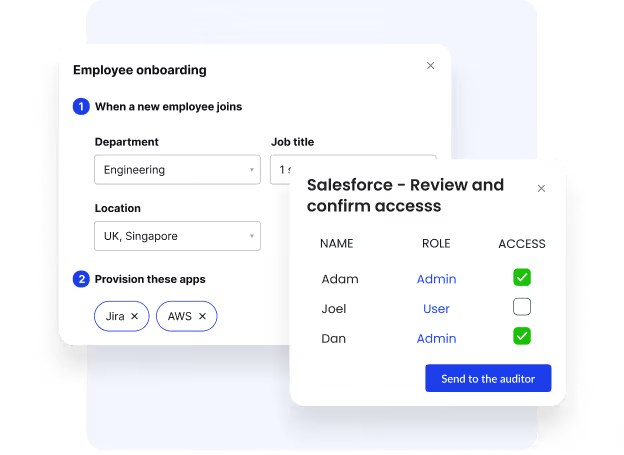
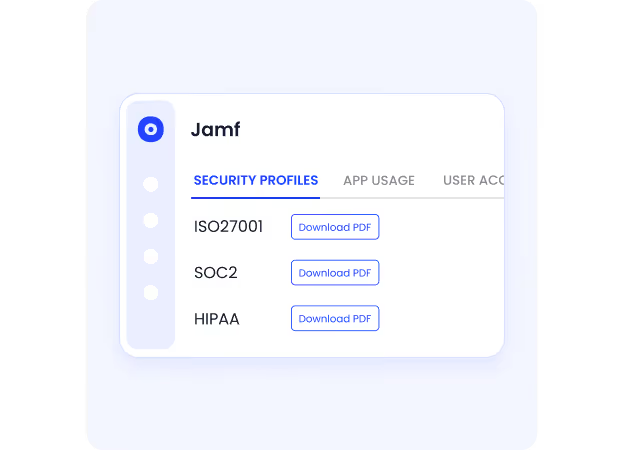
CloudEagle automates role-based provisioning, zero-touch onboarding and offboarding, time-bound access, continuous risk-based access reviews, and audit-ready logs for SOC 2, ISO 27001, HIPAA, and GDPR.
Unlike traditional identity tools that only govern apps behind Okta or SailPoint, CloudEagle extends governance across apps outside the identity provider, including shadow IT and AI tools.
The results: 80 percent reduction in access review effort, elimination of lingering access for former employees, faster audit readiness, and stronger least-privilege enforcement across the board.
For organizations managing SOC 2 specifically, this overview of common SOC 2 compliance challenges and how to solve them is worth reading alongside the access governance setup. Read more
Vendor Risk and Compliance Monitoring in One System
Compliance is not just about user access. It is also about vendor risk.
CloudEagle provides a centralized contract repository with AI metadata extraction, renewal tracking and opt-out date monitoring, vendor security posture evaluation, price benchmarking, and renewal workflows with stakeholder approvals.
Instead of scrambling before audits or renewals, teams operate from a proactive governance model. Compliance becomes operationalized, not event-driven.
You can see exactly how CloudEagle maps to SOC 2, ISO 27001, and HIPAA requirements in this guide on staying compliant across all three frameworks.
Governance Over Embedded AI, The Emerging Blind Spot
The next wave of SaaS compliance risk is not just standalone AI tools. It is AI embedded inside approved applications: AI assistants, auto-summarization features, AI-generated analytics, and smart compose features.
Most organizations do not know where AI is embedded or how it is being used.
As CloudEagle's 2025 IGA report highlights, 70 percent of CIOs consider unapproved AI a top security risk.
CloudEagle maps AI capabilities across your SaaS stack, flags risky usage, enables policy enforcement, and detects shadow AI activity.
For a full picture of what an AI compliance program looks like in practice, this AI compliance checklist covering SOC 2, GDPR, and the EU AI Act covers the governance layer that most organizations are still missing.
Compliance That Pays for Itself
Organizations using CloudEagle report 10 to 30 percent annual SaaS cost savings, 80 percent reduction in compliance prep time, faster onboarding and offboarding, fewer security gaps, and improved employee experience.
If your compliance gaps live in SaaS visibility, access governance, vendor risk, or AI oversight, CloudEagle.ai is built for exactly that.
3. Final Thoughts
This SaaS compliance checklist covers every layer of the problem. Work through it step by step, assign clear ownership for each area, and build toward a state where your SaaS environment is governed continuously rather than only when an audit is on the calendar.
The tools to do this well exist. The question is whether your current processes can keep pace with the rate at which your SaaS stack is growing.
Ready to get full visibility into your SaaS environment? See how CloudEagle.ai helps security and IT teams stay continuously compliant without the manual overhead.
Frequently Asked Questions
1. What is SaaS compliance?
It governs every cloud app your org uses, access, data, vendors, and audits. Not just approved tools. Every tool. Including the ones employees signed up for without telling IT
2. What is shadow IT, and why does it create compliance risk?
Shadow IT is any app that IT didn't approve. No security review. No audit trail. No controls. In 2026, shadow AI is the harder problem, employees feeding company data into AI tools that nobody's tracking.
3. Which compliance frameworks apply to SaaS environments?
GDPR, HIPAA, SOC 2, ISO 27001, PCI DSS, most orgs answer to more than one. Which applies depends on your industry, data type, and geography. Overlapping frameworks mean overlapping obligations.
4. How often should you conduct a SaaS compliance review?
Continuously. Formal reviews twice a year. Access reviews every 90 days. Real-time monitoring in between. Your SaaS stack changes daily; periodic audits alone will always leave you behind.
5. Do you need a Data Processing Agreement with every SaaS vendor?
Under GDPR, yes, it's legally required if a vendor touches personal data. Outside GDPR, it's still best practice. If they handle your data, you need it in writing. No exceptions.

%201.svg)









.avif)




.avif)
.avif)




.png)





