HIPAA Compliance Checklist for 2025

Most compliance programs are built to pass audits. Very few are built to stay ready for them.
The difference shows up in how a team behaves in the six weeks before an audit. If people are pulling evidence manually, chasing down access review logs, and scrambling to document controls that should have been monitored all year, the program is reactive. It works, until it does not.
The best practices for continuous compliance readiness are not complicated. Controls are monitored in real time. Evidence is collected automatically. Gaps surface before an auditor finds them. This guide breaks down the five practices that make that shift real.
TL;DR
- Reactive compliance programs built around annual audits leave security teams scrambling and controls unmonitored for months at a time
- Automated evidence collection cuts audit prep time by up to 80% and keeps your compliance posture current without manual effort
- Continuous control monitoring catches permission changes, configuration drift, and shadow AI adoption before an auditor does
- A unified control library lets you satisfy SOC 2, ISO 27001, HIPAA, and GDPR simultaneously, reducing compliance overhead by 40 to 60%
- CloudEagle.ai brings all five practices together in one platform, from automated evidence collection to real-time risk monitoring and identity governance
1. Why Continuous Compliance Readiness Matters More Than Passing Audits?
Passing an audit tells you where you stand on one specific day. It says nothing about what happens on day 366.
Regulators are aware of this gap and are moving accordingly. GDPR enforcement does not follow your audit calendar. SOC 2 customers ask for compliance evidence mid-contract, not just at renewal. The EU AI Act introduces ongoing obligations that cannot be satisfied with a once-a-year review.
56% of organizations cite lack of continuous monitoring as their top compliance gap, according to a 2024 Ponemon Institute study.
A solid compliance readiness strategy reduces that cost every week, not just in the weeks before an audit. Security teams that invest in continuous compliance readiness spend less time firefighting and more time on work that actually moves the business forward.
2. The Biggest Compliance Gaps Most Security Teams Overlook
Before getting into the best practices for continuous compliance readiness, it is worth being specific about where programs actually break down. These are not edge cases. They show up across industries and company sizes.
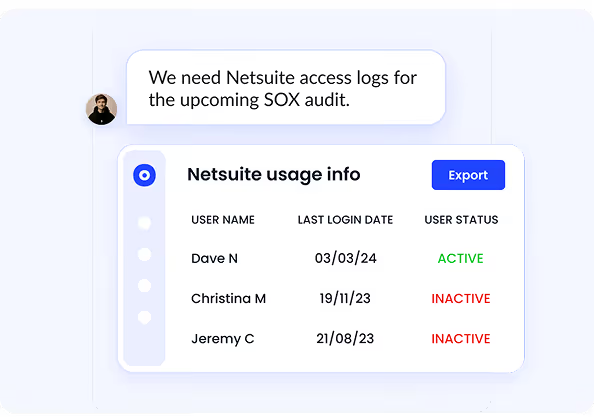
- Manual evidence collection: Teams spend weeks before each audit pulling access logs, HR records, and configuration screenshots by hand. It is slow, error-prone, and produces inconsistent results across audit cycles.
- Point-in-time control monitoring: A control passes in Q1. In Q3, a configuration change, a new SaaS tool gets onboarded, or an employee gets over-provisioned. Without continuous monitoring, that drift goes undetected until an auditor finds it.
- Shadow AI and unsanctioned apps outside compliance scope: Most compliance programs only cover IT-approved applications. But employees are adopting AI tools and SaaS products without IT sign-off, and those tools are processing company data outside any compliance boundary.
- Stale access permissions: When someone changes roles or leaves the company, their permissions often outlast their job. Over-privileged accounts are one of the most common compliance findings and one of the most avoidable.
- Compliance and risk run in parallel, not together: Compliance tells you whether a control is implemented. Risk tells you whether that control actually matters given your current threat exposure. When those two functions are not connected, you end up prioritizing the wrong things.
Worth a Read: How Enterprises Can Track Claude, Cursor and Gemini Spend in One Place
3. 5 Best Practices for Continuous Compliance Readiness
A. Best Practice 01: Automate Evidence Collection Across Your Security Stack
If your team is still pulling log exports, HR records, and access screenshots before every audit, that is the first problem to fix.
Manual evidence collection is slow, inconsistent, and scales badly. Automated collection through deep integrations across your HR systems, identity providers, cloud environments, and SaaS tools pulls evidence continuously and maps it to the right controls without anyone chasing it down.
- Evidence is pulled automatically from every connected system
- Controls are mapped and updated in real time, not before audits
- Audit reports are ready to export the moment an auditor asks
Teams typically cut audit prep time by up to 80%. For CloudEagle.ai customers, 500+ native integrations handle this automatically. Evidence is timestamped, organized by control, and always audit-ready.
B. Best Practice 02: Continuously Monitor Compliance Controls
Controls break quietly. A permission gets misconfigured. A new app slips through. An employee keeps access they should not have after a role change.
None of this shows up unless someone is actively watching. Continuous control monitoring catches these issues the moment they happen, not during the next audit cycle.
- Immediate alerts when access permissions change unexpectedly
- Automatic detection of application configuration drift
- Continuous discovery of new SaaS and AI tools adopted outside of IT approval
- Ongoing tracking of vendor security postures
The goal is simple: know about a control failure before your auditor does, with enough time to fix it automatically.
Security teams managing access reviews at scale know how quickly reviewer fatigue sets in. This quote from an ICEYE security leader captures what that looks like in practice.
"We lacked confidence in our access certifications. CloudEagle brought structure and accountability to user access reviews without reviewer fatigue." Michal Lipinski, Director of IT and Security, ICEYE
C. Best Practice 03: Centralize Compliance Monitoring and Reporting
Evidence in one system, controls in another, access reviews in a spreadsheet, vendor assessments in email. That is not a compliance program. That is disconnected work that someone stitches together before every audit.
Centralized compliance monitoring brings it all into one place.
- Every framework maps to a shared control library
- Evidence auto-links to the controls it satisfies
- Risk signals surface in one dashboard, not five tools
- Audit reports are generated on demand, not over two weeks
This is also what makes regulatory compliance optimization techniques work at scale. Organizations managing multiple frameworks this way report 40 to 60% lower compliance overhead compared to teams managing each framework separately.
Compliance monitoring is increasingly a C-suite conversation, not just an IT one. This webinar covers exactly what that shift looks like for enterprise security teams.
Watch the Webinar: 60% of SaaS and AI apps operate outside IT visibility. Kevin Lee covers what that means for your compliance posture.
Managing SaaS Risk and Compliance
D. Best Practice 04: Integrate Compliance Monitoring With Risk Management
Compliance tells you whether a control is implemented. Risk tells you whether that control actually matters given your current exposure. When the two do not share context, you end up prioritizing the wrong things.
Integrating compliance and risk management changes how decisions get made.
- Risk scores inform which compliance gaps to fix first
- Control failures automatically generate risk register entries
- Vendor risk assessments feed directly into compliance workflows
- Access risk data surfaces across both functions simultaneously
This is what turns a compliance program into genuine continuous audit readiness. Auditors are not just checking whether controls exist anymore. They want to see that risk context is actively shaping how those controls are maintained.
73% of security leaders say integrating compliance with risk management is a top priority for 2026, according to Gartner’s Annual CIO Survey.
Worth a Read: How CloudEagle.ai Simplifies App Access Review for Compliance Success
E. Best Practice 05: Apply a Regulatory Compliance Optimization Technique That Scales
Managing SOC 2, ISO 27001, HIPAA, GDPR, and the EU AI Act as five separate programs is how teams end up overwhelmed.
The overlaps between frameworks are significant. Build your program around a unified control library instead, and you satisfy multiple frameworks with the same work.
- Audit existing controls and map them to every framework in scope
- Identify overlapping requirements and consolidate where possible
- Use a platform that maintains cross-framework mapping as regulations evolve
- Document control intent alongside implementation, since auditors care about both
Teams that operate this way add new compliance frameworks in weeks rather than months, because the foundational work already exists.
4. How Continuous Compliance Readiness Reduces Audit Stress?
Audit stress is a symptom of a reactive program. Following the best practices for continuous compliance readiness turns audits into a documentation exercise rather than a crisis.
- In week one, the auditor gets access to a live compliance dashboard with evidence already collected, organized, and mapped to controls
- In week two, every control has a complete audit trail because monitoring has been continuous
- In week three, auditor questions are answered in hours because reports are exportable on demand
- Post-audit, remediation items feed back into the monitoring system, strengthening the program for the next cycle
- This is not luck; it happens when evidence collection is automated, controls are continuously monitored, and compliance visibility is centralized
Seeing this in real numbers helps. RingCentral needed full visibility into its SaaS stack and a way to stop managing licenses manually.
Case Study: RingCentral was losing time and money to manual license management with no clear picture of what was actually being used. CloudEagle.ai gave them full visibility and automated the process entirely.
👉 Read the full case study: CloudEagle.ai Saves RingCentral Time and Costs
5. How CloudEagle.ai Supports Continuous Compliance Readiness?
Each of the five best practices for continuous compliance readiness maps directly to a capability inside CloudEagle.ai.
Automated Evidence Collection
Automated evidence collection runs through 500+ native integrations that pull compliance data continuously from your HR systems, identity providers, SaaS tools, and cloud environments.
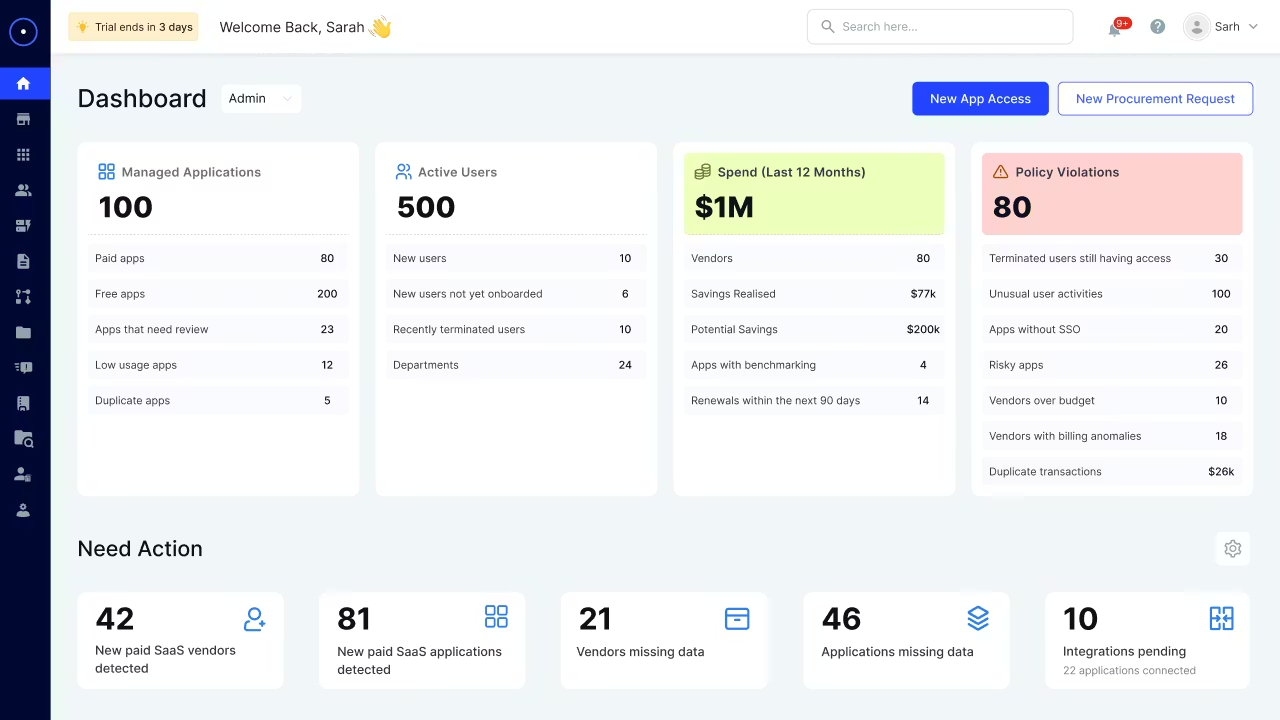
Evidence is timestamped, organized by control, and audit-ready without manual assembly.
Real-Time Control Monitoring
Real-time control monitoring is handled by EagleEye, CloudEagle's agentic AI engine.
It monitors your environment continuously, flags violations the moment they occur, and can trigger automated remediation workflows without waiting for human input.
Unified Compliance Dashboard
Unified compliance dashboard gives every team a single view across SOC 2, ISO 27001, HIPAA, GDPR, PCI-DSS, and the EU AI Act.
Controls are shared across frameworks. Evidence auto-links. Audit reports export on demand.
Shadow AI and Shadow IT Detection
Shadow AI and shadow IT detection close the visibility gap that most compliance programs ignore entirely.
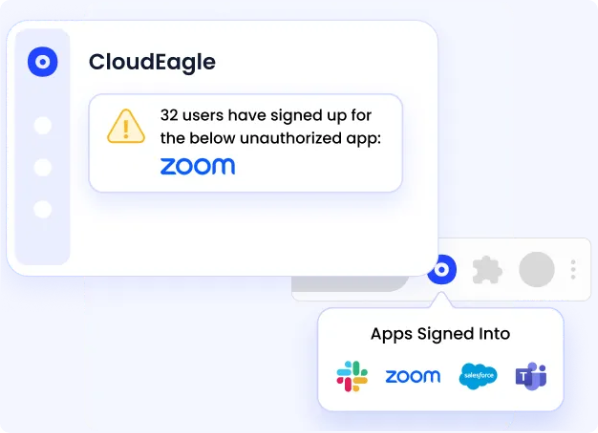
CloudEagle discovers every application in your environment, sanctioned or not, and assesses each one for risk and compliance exposure.
Identity Governance and Access Reviews
Identity governance and access reviews cover the full user lifecycle. Provisioning is automated. Deprovisioning is immediate.
Access review campaigns run on schedule, produce audit-ready certifications, and flag over-privileged accounts before they become findings.
Integrated Risk and Compliance View
Integrated risk and compliance view surfaces vendor risk scores, access risk data, and application security postures in the context of your compliance controls, so risk and compliance teams are working from the same picture.
If you want to see how these capabilities work together inside a live environment, the product walkthrough covers it without requiring a call.
Product Walkthrough: See exactly how CloudEagle.ai handles continuous compliance monitoring in practice, no demo call required.
👉 See the CloudEagle.ai Product Walkthrough
Conclusion
Implementing the best practices for continuous compliance readiness is not about buying a feature. It is about building a program where compliance runs in the background every single day.
Automate evidence collection so your team is not assembling it by hand. Monitor controls continuously so that drift gets caught before audits do. Centralize visibility so compliance is not fragmented across tools.
Connect compliance to risk so you are prioritizing what actually matters. Apply a cross-framework optimization approach so your program scales with your regulatory footprint rather than against it.
CloudEagle.ai brings all of this together in one platform. If your compliance program still feels reactive, book a demo and see what an always-on approach looks like for your specific environment.
Frequently Asked Questions
- What are the 4 pillars of ITGC?
The four pillars of ITGC are access controls, change management, IT operations, and data backup and recovery. - What is the meaning of continuous compliance?
Continuous compliance means monitoring controls and collecting evidence in real time so you are always audit-ready, not just prepared at audit time. - What does compliance readiness mean?
Compliance readiness means your controls, evidence, and documentation are complete, up to date, and ready for audit at any point in time. - What are the 3 C's of compliance?
The 3 C’s of compliance are compliance, consistency, and control. - What are the 5 steps of the ITGC process?
The ITGC process includes risk assessment, control design, control implementation, continuous monitoring, and audit/testing. - What is L1, L2, L3 SOC analyst?
L1 handles initial alert triage, L2 investigates and responds to incidents, and L3 performs advanced threat analysis and improves detection strategies.

%201.svg)









.avif)




.avif)
.avif)




.png)





