HIPAA Compliance Checklist for 2025

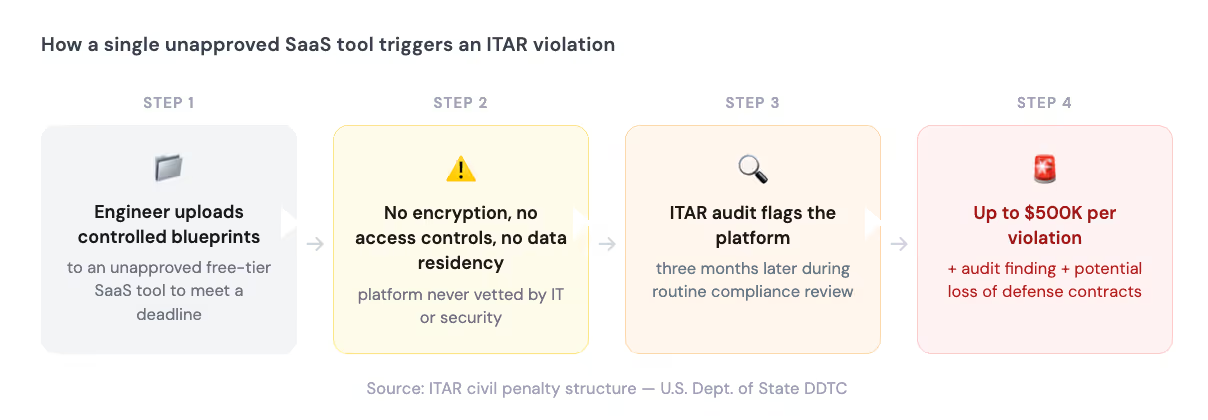
Your engineers are not trying to create a compliance incident. They're trying to ship.
So when the approved file-sharing tool is too slow to send blueprints to an external contractor, one of them finds something faster, uploads the files, and moves on. IT finds out three months later, during a routine audit.
The SaaS tool had no encryption, access controls, or data residency guarantees. Civil penalties up to $500,000 per violation. A compliance finding on record. Defense contracts are suddenly in question.
This is what ITAR violations look like in 2026. The threat is not from a sophisticated actor. It is a Tuesday afternoon workaround.
TL;DR
- ITAR restricts access to defense-related technical data, including software, documentation, and blueprints, to U.S. persons only
- Any SaaS tool that stores, transmits, or provides access to ITAR-controlled data must meet strict access, residency, and encryption requirements
- Shadow IT is the leading cause of accidental ITAR violations today: employees adopt unapproved tools faster than compliance teams can catch them
- "Is Microsoft ITAR compliant?" is the wrong question; the right question is whether your IT team has configured and governed it correctly
- CloudEagle.ai gives IT leaders full SaaS visibility, automated access reviews, and governance workflows to close ITAR compliance gaps across an entire app stack
1. ITAR and SaaS: Why This Is Now an IT Problem, Not Just a Legal One
ITAR, the International Traffic in Arms Regulations, is administered by the U.S. Department of State and controls the manufacture, sale, and distribution of defense and space-related articles listed on the United States Munitions List (USML).
Here is what most IT leaders miss: ITAR does not cover missiles and military hardware.
Technical data, meaning software, schematics, blueprints, and documentation used to develop or operate USML items, is fully controlled under ITAR. If it lives in a SaaS tool, it is still controlled. If a non-U.S. person can access it through that SaaS tool, that is a potential violation, and your organization is the one liable.
ITAR mandates that only U.S. persons, citizens, lawful permanent residents, or protected individuals can access this data.
Any exposure through an unvetted SaaS vendor or a misconfigured cloud environment qualifies. That makes ITAR compliance for SaaS a direct IT responsibility, not something to hand off to Legal and move on.
One more thing worth knowing: in September 2025, the DDTC issued targeted USML revisions, shifting some previously controlled items to the Commerce Department's Export Administration Regulations while tightening controls on advanced military platform components.
If your organization is defense-adjacent, your app classification assumptions may already be out of date.
2. Think ITAR Only Applies to Defense Primes? Read This
This is the assumption that gets mid-market IT leaders into trouble.
ITAR applies to any organization in the defense supply chain that handles USML-listed items or their technical data. That scope is broader than most teams realize:
The liability runs upstream, too. If your organization provides SaaS to a defense prime and that prime's controlled data sits in your environment, you are in scope. A non-U.S. person on your team with access to that data is a violation, regardless of whether they ever opened the file.
Ignorance of scope is not a defense that the DDTC accepts. In 2018, FLIR Systems paid $30 million in civil penalties after transferring USML data to dual-national employees. Their compliance program existed. The gap was in who could access what.
3. The Governance Gap ITAR Was Never Built to Close
ITAR was written for a world that no longer exists for most organizations: locked server rooms, classified networks, and physical perimeters that were actually perimeters.
Today, the average enterprise runs 275+ SaaS applications, and IT teams have direct visibility into fewer than 60% of them. The rest live across departmental credit cards, personal emails, and free-tier sign-ups that security never reviewed.
Every one of those apps is a potential ITAR exposure point the moment a controlled file touches it.
And that is the problem ITAR's original framework has no answer for.
As Nidhi Jain, CEO of CloudEagle.ai, puts it: "The SaaS sprawl problem is fundamentally an access governance problem. IT teams are not failing because they lack policies. They're failing because they lack visibility into what's actually running in their environment."
Shadow AI makes this harder still. Microsoft's 2024 Work Trend Index found that 78% of knowledge workers bring their own AI tools to work. Each one of those tools is a potential unauthorized recipient of ITAR-controlled technical data, and most ITAR compliance for SaaS programs has no detection layer for it at all.
4. The Five ITAR Controls IT Leaders Directly Own
ITAR compliance for SaaS is not purely a legal or export function. Five critical controls sit squarely with IT, and these are the ones that surface most often in audit findings.
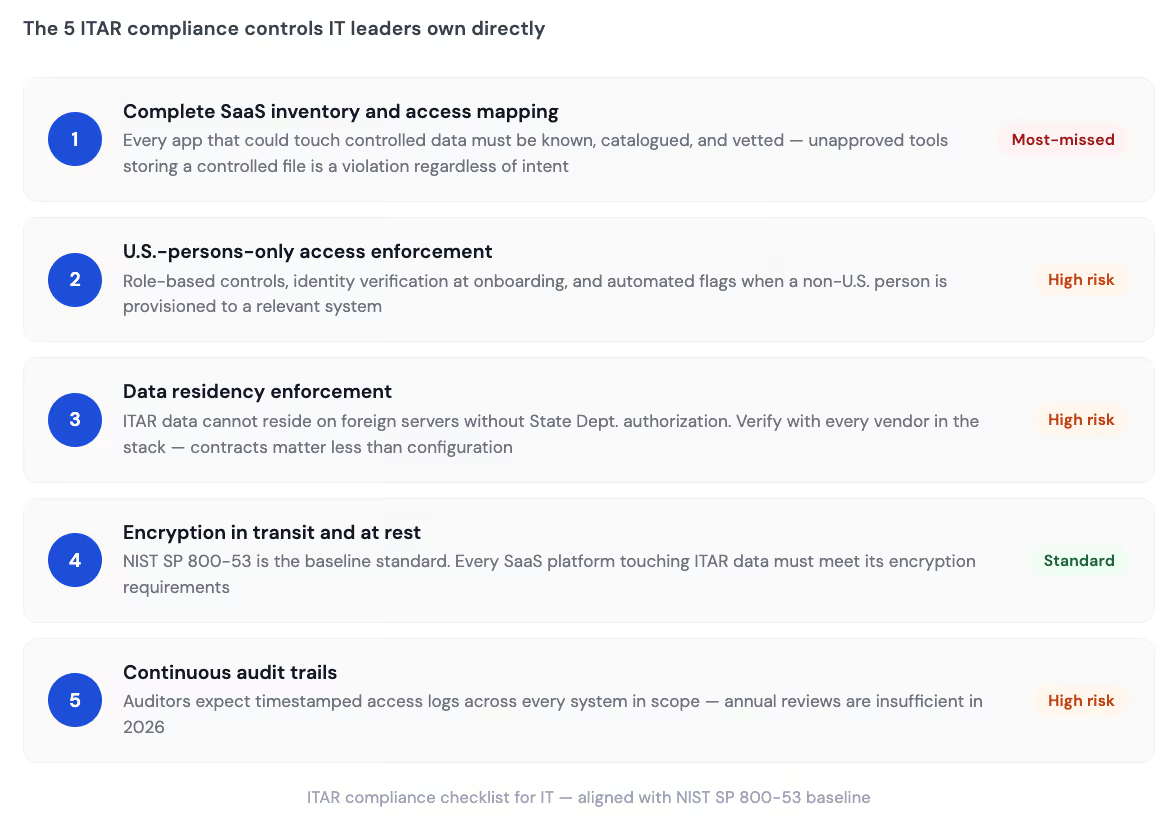
1. Complete SaaS inventory and access mapping
An unapproved SaaS tool storing a controlled file is a violation regardless of intent. This is the ITAR compliance checklist item most organizations fail, because they do not know what they do not know.
2. U.S. persons-only access enforcement
Access to ITAR-controlled data must be restricted to verified U.S. persons. This means role-based access controls, identity verification at onboarding, and automated flags when a non-U.S. person is provisioned to a relevant system. Privilege creep is not just a cost problem here. It is a federal compliance problem.
3. Data residency enforcement
ITAR-controlled data cannot reside on foreign servers without State Department authorization. Multi-tenant SaaS platforms frequently replicate data across regions for redundancy, often without surfacing it in any way visible to the customer. Vendor contracts matter less than actual configuration. Verify residency; do not assume it.
4. Encryption in transit and at rest
NIST SP 800-53 is the baseline standard for organizations handling ITAR-regulated materials. Every SaaS platform touching ITAR data must meet its encryption requirements. If a vendor cannot demonstrate alignment, it should not be in the stack.
5. Continuous audit trails
Auditors expect timestamped, continuous access logs across every system in scope, including SaaS platforms, not just on-premise environments. Annual reviews are not enough. By the time the next cycle runs, data may have already moved somewhere it should not have been.
5. "Is Microsoft ITAR Compliant?" You're Asking the Wrong Question
This is one of the most searched ITAR questions, and the framing is wrong.
Vendors are not ITAR compliant or non-compliant in isolation. Organizations are. A vendor gives you a technically capable platform. What your team does with it is your responsibility.
Microsoft offers Government Community Cloud High (GCC High), built for organizations handling ITAR-adjacent workloads. AWS GovCloud and Google Cloud operate comparable environments. These platforms provide the infrastructure layer: U.S. data residency, FedRAMP High authorization, and access controls at the vendor level.
That is the floor, not the finish line.
A defense contractor running Microsoft 365 GCC High, but allowing a non-U.S. contractor access to a SharePoint folder containing technical data has a violation instead of a compliance posture. The vendor's certification does not transfer to the organization's access governance decisions.
The right question is not "Is this tool ITAR compliant?" It is "has our IT team configured, governed, and continuously monitored this tool in a way that meets ITAR's access and residency requirements?"
Before your next SaaS vendor review, this is worth reading: How to Mitigate SaaS Compliance Risks breaks down where SaaS compliance programs actually fail, from shadow IT to data residency gaps, with practical steps to close them before an auditor does.
6. Shadow IT Is Your Biggest ITAR Exposure Point
The root cause of most accidental ITAR compliance for SaaS violations in cloud-first organizations comes down to the same thing: an employee used a tool IT did not know existed.
Over two-thirds of IT leaders said in 2023 they would rather allow a valued employee to choose their own tools than risk losing them. Reasonable. It becomes an ITAR liability the moment those tools store controlled technical data without encryption, access controls, or data residency guarantees.
The exposure is growing on two fronts:
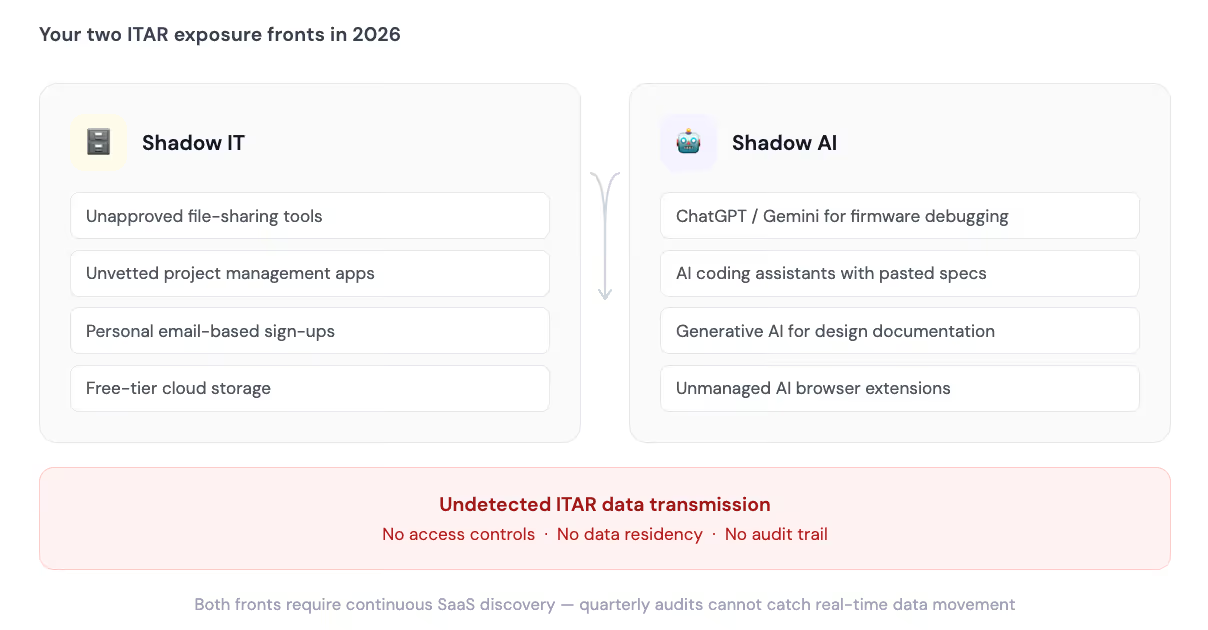
Traditional shadow IT: Employees signing up for file-sharing, collaboration, or project management tools using personal or corporate emails without IT review. These tools process and store whatever employees put in them, including ITAR-controlled blueprints, specs, and documentation.
Shadow AI: When an engineer pastes a firmware specification into ChatGPT to debug an issue, that data has been transmitted to an external system with no verified data residency and no U.S.-person access restriction. According to IBM's 2024 Cost of a Data Breach Report, the average cost of a data breach is now $4.88 million. In an ITAR context, that exposure comes with criminal penalties on top.
Quarterly SaaS audits cannot catch this. By the time the next review cycle runs, the data has already left the compliant environment.
If shadow AI is already on your radar: How to Manage Shadow AI and Shadow IT Using CloudEagle.ai covers how IT teams are building continuous detection programs that surface unapproved AI tools before they become compliance incidents.
7. How CloudEagle.ai Closes the ITAR Compliance Gap in Your SaaS Stack
Most ITAR compliance programs treat SaaS as a footnote. In 2026, it is the primary risk surface.
CloudEagle.ai is built to close the governance gap that ITAR frameworks were never designed to address: environments where SaaS sprawl is the default and shadow IT is the rule rather than the exception.
- SaaS Discovery: IT cannot govern what it cannot see. CloudEagle.ai surfaces every application in the environment, including shadow IT and shadow AI tools, using direct integrations, finance data, and SSO signals. Nothing slips through an ITAR audit because nothing is hidden from IT in the first place.

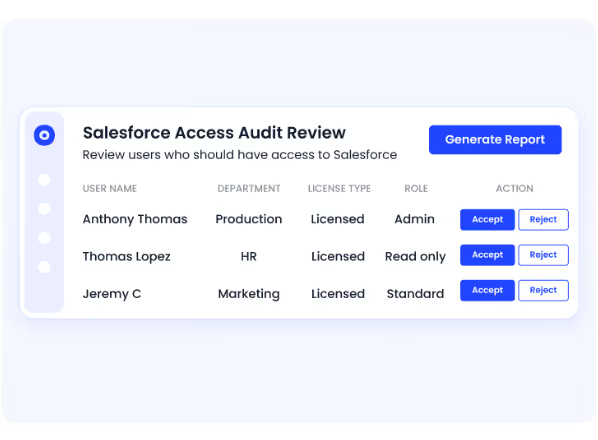
- User Access Reviews: Over-provisioned accounts and stale access grants are direct ITAR violation risks. CloudEagle.ai automates access reviews across the full SaaS portfolio, flagging accounts that should have been deprovisioned and identifying non-U.S. person access to sensitive systems. Lob completed access reviews 70% faster after deploying CloudEagle.ai.
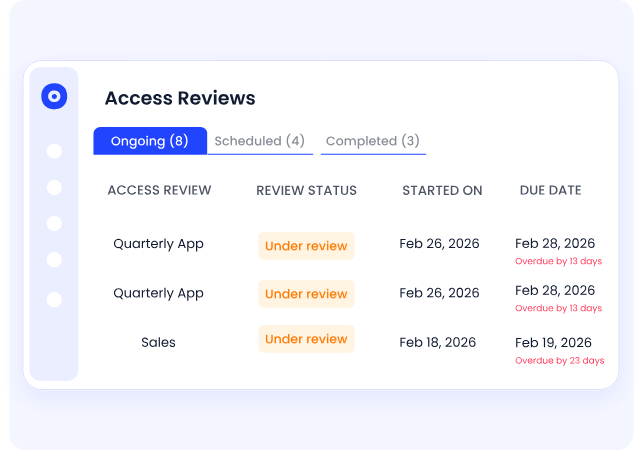
- Continuous Audit Trails: ITAR auditors expect documented evidence of who accessed what and when, across every system in scope. CloudEagle.ai generates continuous, timestamped logs without manual effort. Compliance evidence becomes a byproduct of normal operations, not an audit-season scramble.
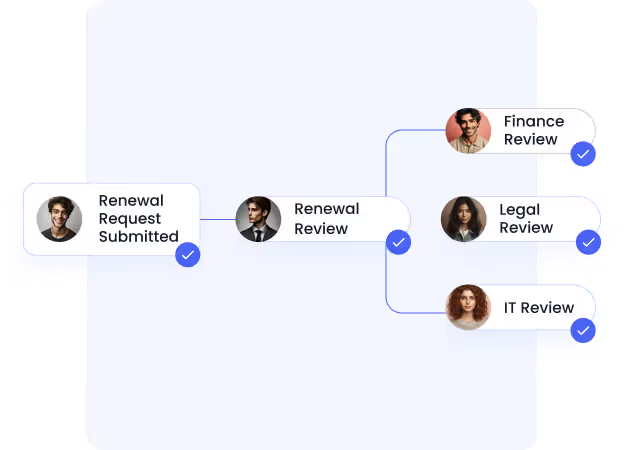
- SaaS Governance Workflows: Unapproved apps reach employees faster than manual approval queues can catch them. CloudEagle's tiered approval workflows enforce a vetted-tools-only environment, with rigorous security assessments for any application that could touch controlled data, before the first user is provisioned.
RingCentral saved $250K through consolidated access governance. The operational case for continuous SaaS governance is not theoretical.
The compliance gaps that surface during ITAR audits are almost never new risks. They are old risks that went undetected because the governance model was built for a pre-SaaS world. CloudEagle is built for the one you are operating in now.
8. FAQs
Does ITAR apply to software?
Yes. ITAR's definition of "technical data" explicitly includes software, source code, and documentation used to design, manufacture, or operate USML-listed defense articles. SaaS platforms hosting or providing access to this data fall within scope.
What are ITAR compliance requirements?
Core requirements include DDTC registration, U.S.-persons-only access controls, data residency enforcement, encryption per NIST SP 800-53, documented audit trails, and a written Export Compliance Program. IT is directly responsible for the access control and audit trail components across every system in scope.
Is Microsoft ITAR compliant?
Microsoft GCC High provides a platform-level environment designed for ITAR-adjacent workloads. Organizations are still responsible for how they configure access, govern users, and monitor activity on top of it. The vendor's certification does not make the organization ITAR-compliant by default.
What is SaaS compliance?
SaaS compliance is the practice of ensuring every cloud application in an organization's stack meets applicable regulatory, security, and access control requirements. For ITAR-regulated organizations, every SaaS tool that could touch controlled technical data must be vetted, configured, and continuously monitored.
9. The Compliance Gap Is Already Open
Every unapproved tool running in your environment with potential access to defense-related data is a live exposure right now.
The penalty structure, up to $500,000 per civil violation and $1 million per criminal violation, does not scale with company size. It does not adjust for intent.
The organizations that stay clean are not the ones with the most detailed compliance documentation. They are the ones with real-time visibility into every application, automated governance across every user, and workflows that intercept risk before an auditor finds it.
If your ITAR compliance for the SaaS program was built before SaaS became your primary operating environment, it needs to catch up.
See how IT teams use CloudEagle to close ITAR compliance gaps across a sprawling app stack. Book a demo.
.avif)
%201.svg)









.avif)




.avif)
.avif)




.png)





