HIPAA Compliance Checklist for 2025

SOC 2 compliance is not failing because controls are missing. It is failing because those controls are not operating continuously.
60% of SaaS and AI apps operate outside IT visibility. 95% of organizations still run manual access reviews. 48% of ex-employees retain system access after offboarding. These are not edge cases. They are the norm, and traditional SOC 2 approaches were never built to handle them.
This is exactly why CloudEagle.ai stands out as the best AI for continuous SOC 2 compliance. In this blog, we break down what makes it different, what it actually does inside your environment, and why security teams running always-on compliance programs trust it over every alternative.
The best AI for continuous SOC 2 compliance does not just automate evidence collection. It closes visibility gaps, enforces access governance in real time, and keeps your audit trail current without anyone manually assembling it.
TL;DR
1. Why Traditional SOC 2 Compliance Approaches No Longer Work?
Traditional SOC 2 assumes you know every system in scope, can enforce access centrally, and can validate controls on a schedule. None of those assumptions holds anymore.
From CloudEagle's 2025 IGA report, the numbers are clear:
- 60% of SaaS and AI applications operate outside IT visibility
- 95% of organizations still rely on manual, non-AI access reviews
- 48% of ex-employees retain system access post-termination
- 1 in 2 employees carry excessive privileges
Each of these creates a direct SOC 2 failure point. An incomplete scope means controls cannot cover what you cannot see. Quarterly reviews mean privilege creep accumulates for months before anyone catches it.
Persistent access after offboarding violates logical access control requirements outright. The problem is structural. Periodic controls cannot keep pace with environments that change daily.
"Traditional IGA tools were never designed for the unmanaged employee-brought AI and SaaS environments we operate in today." — CloudEagle 2025 IGA Report
Worth a Read: CloudEagle.ai Launches EagleEye — Autonomous SaaS and AI Governance
2. How AI Is Transforming Continuous SOC 2 Compliance?
AI for continuous SOC 2 compliance is not about doing the same things faster. It changes the model entirely.
SaaS environments are growing at 19 to 20% annually. Manual review cycles were built for a different era. Automated SOC 2 compliance AI closes the gap between how fast your environment changes and how fast your controls respond.
The shift is from periodic enforcement to continuous enforcement. From reactive discovery to real-time detection. From manual evidence to system-generated proof that exists whether or not an audit is coming.
SOC 2 is fundamentally an access governance problem. This episode breaks down exactly how enterprises are rethinking SaaS governance to stay ahead of it.
Podcast: Optimizing Shadow IT Risks and Innovations in SaaS Management — an 11-minute listen on how shadow app sprawl creates real governance and compliance exposure. 👉 Listen now
3. What Makes CloudEagle.ai the Best AI for Continuous SOC 2 Compliance?
A. Full SaaS and AI Visibility
SOC 2 controls are only valid if you know every system in scope. CloudEagle closes that gap before anything else.
- Discovers every SaaS and AI app in use, sanctioned or not
- Correlates data from 500+ integrations, identity providers, and finance systems
- Rec Room gained complete visibility into unmanaged apps across teams
- Heath Ceramics achieved 100% SaaS visibility across IT and finance
B. Continuous Access Lifecycle Enforcement
Access that outlasts its purpose is one of the most common SOC 2 failure points. CloudEagle enforces the full lifecycle automatically.
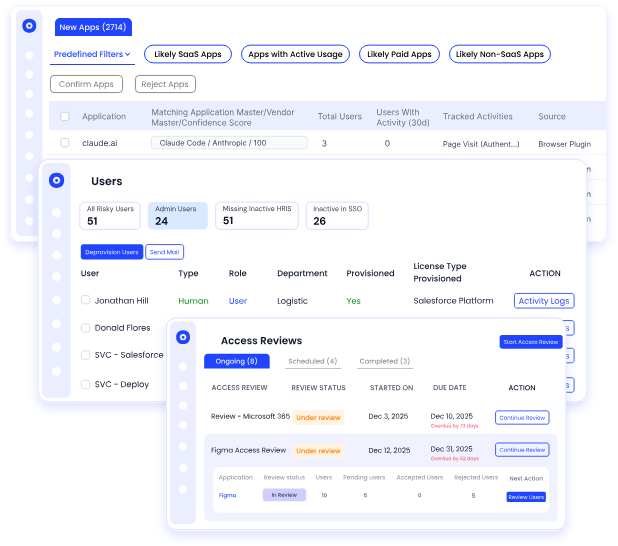
- Provisions access based on role at onboarding
- Revokes access immediately at offboarding
- Rec Room eliminated $200K in unused license exposure annually
- A mid-market SaaS company detected and removed 7 unsanctioned AI tools within a week
C. Dramatically Reduced Audit Effort
Audit readiness should not depend on a two-week sprint before the audit begins.
- Centralized evidence eliminates manual log stitching
- Access review history is always current, not compiled under a deadline
- Shiji completed a full SOC 2 access review preparation in 72 hours
D. Financial and Governance Impact in One View
Most compliance tools have no financial context. Most cost tools have no governance context. CloudEagle connects both.
- RingCentral saved $250K by consolidating duplicate apps
- ICEYE saved $300K in 120 days
- Lob reduced SaaS spend by 20% from day one
- Unused licenses are treated as open access risk, not just wasted spend
The proof points above are not isolated wins. Here is what one enterprise team achieved end-to-end.
Case Study: RingCentral needed full SaaS visibility and a way to stop managing licenses manually. CloudEagle gave them both, saving $250K through consolidated access governance. 👉 Read the full case study
4. Core Capabilities of CloudEagle's AI for Continuous SOC 2 Compliance
A. Continuous Access Reviews
Replaces scheduled quarterly campaigns with always-on access validation.
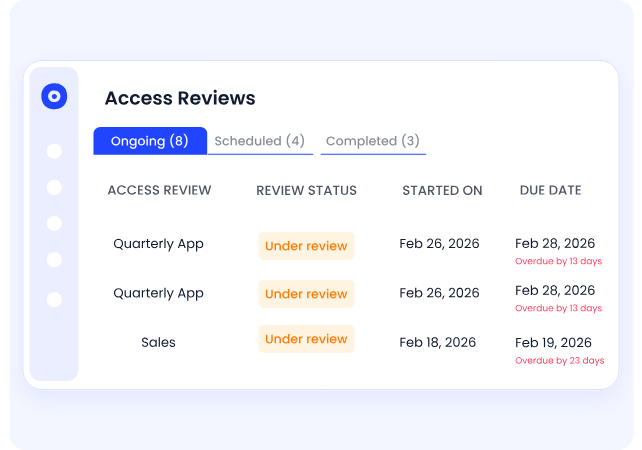
- Flags overprivileged accounts dynamically as conditions change
- Removes the lag between access changes and control enforcement
- Sends automated alerts when permissions deviate from policy
B. Automated Provisioning and Deprovisioning
Access is granted and revoked in real time across every app, managed or not.
- Role-based provisioning triggers at onboarding automatically
- Deprovisioning executes immediately when someone leaves or changes roles
- Directly addresses the 48% access retention issue post-offboarding
C. Shadow IT and AI Discovery
Keeps your SOC 2 scope accurate in environments where employees adopt tools freely.
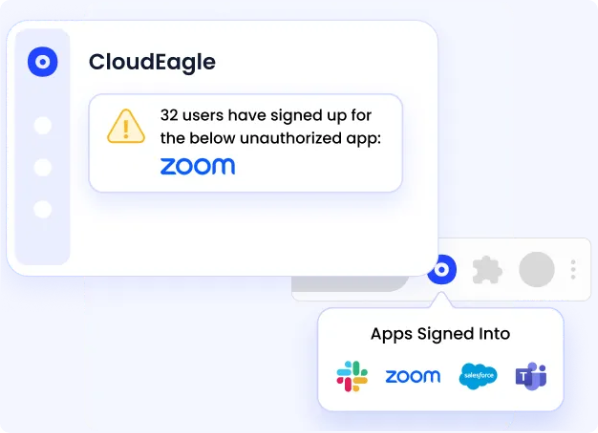
- Correlates login activity, spend signals, and identity provider data
- Surfaces unsanctioned SaaS and AI tools outside IT approval workflows
- Every newly discovered app is assessed for risk and added to the compliance scope
Worth a Read: How Enterprises Can Track Claude, Cursor, and Gemini Spend in One Place
D. Workflow-Native Audit Logs
Evidence is generated automatically as part of normal operations, not assembled before audits.
- Every access request, approval, and deprovisioning event is logged instantly
- No post-processing or cross-tool reconciliation required
- Audit trail is always current and exportable on demand
E. License and Access Intelligence
Links financial data with access governance for a view that neither IAM tools nor compliance platforms provide.
- Identifies unused but active access across your entire app portfolio
- Ties cost optimization directly to access risk reduction
- Supports both compliance decisions and SaaS spend management in one workflow
5. How Security Teams Stay Audit-Ready With CloudEagle.ai?
Most security teams spend weeks before an audit pulling data from IAM systems, HRIS platforms, finance tools, and SaaS applications. Evidence gets reconciled manually. Reviews are completed under deadline pressure.
With continuous SOC 2 monitoring through CloudEagle, audit readiness becomes a byproduct of normal operations:
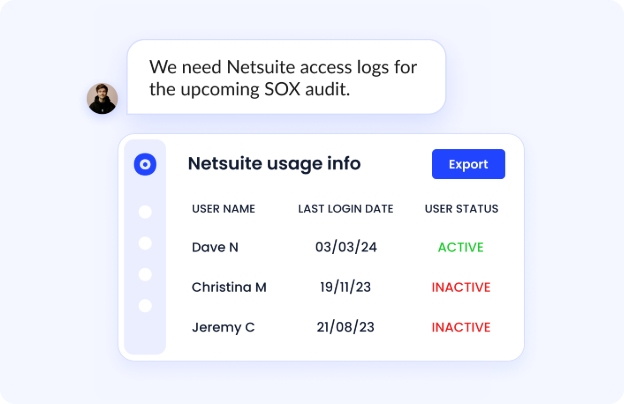
- Access changes are logged the moment they happen
- Reviews are continuously updated rather than run once a quarter
- Evidence is centralized and exportable on demand
- The scope is always current because shadow app discovery runs continuously
The outcome across CloudEagle customers speaks for itself:
- Up to 80% reduction in compliance effort
- Audit preparation reduced from weeks to days
- Lob completed access reviews 70% faster
"Stop relying on quarterly spreadsheet reviews. Use AI-powered tools that monitor access continuously and alert on risks in real time." — CloudEagle IGA Report
Reading about it only goes so far. If you want to see how CloudEagle handles SOC 2 monitoring inside a real environment, the product walkthrough shows you without requiring a call.
Product Walkthrough: See exactly how CloudEagle.ai handles continuous SOC 2 monitoring in a live environment, no demo call required. 👉 See the CloudEagle.ai Product Walkthrough
Conclusion
Continuous SOC 2 compliance comes down to three things: complete visibility across all applications, continuous enforcement of access controls, and automated evidence generation. Most tools address one or two of these. CloudEagle.ai integrates all three.
The results are not theoretical. Lob completed access reviews 70% faster. Rec Room eliminated $200K in access and cost leakage. RingCentral saved $250K through consolidated access governance.
These outcomes come from treating AI for continuous SOC 2 compliance as an operational system, not an audit-season tool.
If your SOC 2 program still depends on manual reviews and pre-audit scrambles, it is worth seeing what always-on compliance looks like in practice.
Frequently Asked Questions
- What is the best AI for continuous SOC 2 compliance?
CloudEagle.ai is purpose-built for continuous SOC 2 compliance, combining full SaaS visibility, automated access governance, shadow AI detection, and always-on audit logging in one platform.
- How does automated SOC 2 compliance AI reduce audit prep time?
By generating audit logs automatically as workflows execute, eliminating manual evidence collection. CloudEagle customers like Shiji have reduced full access review preparation to 72 hours.
- Why do traditional SOC 2 approaches fail in modern SaaS environments?
Because 60% of apps operate outside IT visibility, and 95% of organizations still use manual access reviews. Controls built for periodic validation cannot keep pace with environments that change daily.
- What is continuous SOC 2 monitoring?
It means your access controls, evidence collection, and compliance scope are being maintained in real time rather than checked on a quarterly or annual schedule. Every change is logged, flagged, and remediated automatically.
- How does CloudEagle.ai handle shadow AI in the SOC 2 scope?
CloudEagle continuously discovers unsanctioned SaaS and AI tools by correlating login activity, spend data, and identity signals. Every newly discovered app is assessed for risk and added to your compliance scope automatically.
- What makes CloudEagle.ai different from standalone IAM tools?
IAM tools govern access within SSO-covered apps. CloudEagle extends governance beyond SSO, integrates financial and usage context, and connects compliance with cost optimization in a single operational system.

%201.svg)









.avif)




.avif)
.avif)




.png)





