HIPAA Compliance Checklist for 2025

In May 2023, Ireland's data protection authority fined Meta $1.3 billion for GDPR violations. A few months later, Amazon was hit with $886 million for the same.
Neither company set out to break the rules. Both had compliance programs. What they didn't have was continuous visibility into whether those programs were actually working.
That's the gap compliance monitoring tools are built to close.
TL;DR
- Compliance monitoring tools give you a live, continuous view of your regulatory posture, replacing the guesswork between audits.
- SaaS sprawl, shadow AI, multi-framework obligations, and access drift are the compliance risks most organizations aren't tracking in real time.
- Annual audits aren't enough. Violations that happen between cycles stay hidden until a regulator finds them.
- Ownership is cross-functional, but without a centralized tool, it stays scattered.
- CloudEagle.ai covers the SaaS and AI compliance surface: shadow app discovery, license governance, access control, and audit-ready reporting.
1. What Compliance Monitoring Tools Actually Do?
Most organizations treat compliance like a project with a deadline. You prep, you audit, you pass, you move on.
The problem? Regulators don't wait for your audit schedule. Neither do attackers.
Compliance monitoring tools continuously track whether your systems, users, and processes meet regulatory requirements and internal policies in real time, around the clock. A traditional audit gives you a snapshot. These tools give you a live feed.
They detect violations automatically, generate tamper-proof audit trails, and alert the right teams before a compliance gap becomes an incident. For CISOs and CIOs managing complex IT environments, that shift from reactive to continuous is what separates a dashboard alert from a regulatory notice.
2. 5 Reasons Your Organization Needs Compliance Monitoring Tools
1. Your SaaS stack has blind spots manual reviews will never catch
The average enterprise runs hundreds of SaaS applications and a significant chunk of them are unsanctioned. Finance uses an unapproved invoicing tool. Marketing connects a third-party analytics platform. Someone in ops adds a project management app that wasn't reviewed by IT.
Every one of those apps is a potential compliance exposure. Manual processes have no way to see them, let alone enforce policy on them.
Compliance monitoring tools scan continuously, surface every application in use, and flag deviations before an auditor does.
2. Shadow AI is your fastest-growing compliance risk
Employees are adopting AI tools faster than most security teams can track. A personal ChatGPT account used for customer emails. An AI coding assistant that ingests proprietary code. An unapproved data analysis tool that processes PII.
Any of these can violate GDPR, HIPAA, or internal data policies in a single session without anyone in IT knowing it happened. According to Vanta's 2024 research, 65% of organizations say they have good visibility into AI tool usage, yet 51% believe internal AI use is increasing their overall security risk.
That gap between perceived and actual visibility is exactly where breaches and compliance failures originate.
3. Regulatory complexity has outpaced what humans can track
Modern enterprises don't answer to one regulation. GDPR, HIPAA, SOX, PCI-DSS, ISO 27001: these often apply simultaneously, each with its own controls, reporting timelines, and audit requirements.
62% of organizations must comply with multiple data privacy laws across local, national, and industry-specific levels. Tracking all of it manually creates gaps, especially as frameworks update mid-year. Compliance monitoring tools automate this coverage, mapping activity to the relevant frameworks and flagging deviations in real time.
4. Point-in-time audits leave months of exposure in between
A quarterly audit tells you where you stood on one specific day. What happened the other 89 days? You find out when a regulator asks.
The average cost of a data breach in 2024 was $4.88 million: a 10% increase over the year before, and the highest figure IBM has ever recorded. A significant portion of that cost comes directly from delayed detection. Continuous compliance monitoring closes the window between when a violation occurs and when someone acts on it.
5. Access sprawl and over-provisioned licenses are quiet audit liabilities
Permissions accumulate. Someone gets promoted, changes roles, or leaves and their old access doesn't get cleaned up. Over time, you end up with hundreds of users holding access they no longer need.
Excessive user permissions and over-provisioned SaaS licenses are among the most common compliance findings. Compliance monitoring tools track permissions in real time, enforce least-privilege policies automatically, and flag license over-provisioning before it shows up as an audit exception or a data exposure event.
3. What are the Types of Compliance Monitoring Tools?
Different tools cover different compliance surfaces. Here's how the category breaks down:
For organizations dealing with app sprawl and AI governance, SaaS compliance tools are the most relevant category and the most underinvested one.
4. Compliance Monitoring Examples Across Industries
Compliance obligations vary by industry, but no sector is exempt from continuous monitoring.
- Healthcare (HIPAA): Monitor patient record access, data storage practices, and encryption across all systems. Healthcare faces the highest average breach cost of any sector: $10.93 million per incident.
See real-life HIPAA violations that should have been caught earlier.
- Finance (SOX, PCI-DSS): Track financial reporting integrity, flag suspicious transactions, and ensure cardholder environments meet PCI-DSS controls. PCI non-compliance alone can result in fines of $5,000 to $100,000 per month.
- Any org handling EU data (GDPR): Monitor data collection, storage, and transfer continuously. EU supervisory authorities issued approximately €1.2 billion in GDPR fines in 2025 alone.
Start here: 10 steps to be GDPR-ready.
- Technology and SaaS companies: Track software license compliance, access provisioning, and shadow app usage to stay clean ahead of audits.
5. Key Features to Look for in Compliance Monitoring Tools
Compliance monitoring tools vary widely in depth and focus. When evaluating options, here's what actually matters:
Real-time alerting. Violations that sit in a queue compound. The right tool surfaces issues immediately so teams can act before exposure grows.
Policy enforcement. Flagging alone isn't enough. Strong tools enforce policies automatically: revoking access, blocking actions, or triggering approval workflows without waiting for human intervention.
Audit trail depth. Regulators want tamper-proof records with timestamps, user attribution, and full context. Shallow logs don't hold up under scrutiny.
Stack integration. A compliance tool disconnected from your SaaS stack, cloud environments, and identity providers creates more gaps than it closes. Native integrations are non-negotiable.
AI risk flagging. Rule-based monitoring misses novel threats. AI-driven tools detect behavioral anomalies that static rules weren't written to anticipate.
Regulator-ready reporting. Audit prep shouldn't consume weeks of manual data assembly. Look for tools that generate on-demand reports formatted for the frameworks you operate under.
See how leading platforms compare in this guide to continuous compliance monitoring tools.
6. Monitoring Compliance in the Workplace: Who Owns It?
Compliance monitoring is everyone's responsibility which is exactly why it often falls through the cracks.
Here's how ownership typically breaks down across functions:
When each function works from separate tools, risk falls between systems. A centralized compliance monitoring tool gives every stakeholder a shared view, closing the gaps that siloed approaches consistently miss.
For a deeper look at how the CISO fits into this picture, see what CISO responsibility looks like in an AI-first enterprise.
7. How CloudEagle.ai Helps with AI and SaaS Compliance Monitoring
SaaS and AI sprawl have created a compliance surface most traditional tools weren't designed to handle. CloudEagle.ai was.
CloudEagle gives IT, security, and finance teams complete visibility into every application in use across the organization: sanctioned or otherwise. That includes shadow SaaS and unauthorized AI tools employees adopt outside of IT's approval process, often without realizing the compliance exposure they're creating.
Shadow app and shadow AI discovery:
When AI tools spread informally across teams, compliance gaps follow. CloudEagle automatically surfaces every application in use including unauthorized AI tools accessing sensitive data, so your compliance posture reflects what's actually happening.

Iterative Health used this to surface 200+ ungoverned AI tools, achieve 100% auditable AI access, and cut approval time by 60%.
As their CTO Aditya Khosla put it:
"CloudEagle.ai helped us move from ad-hoc approvals to structured, defensible AI governance."
Read the full case study.
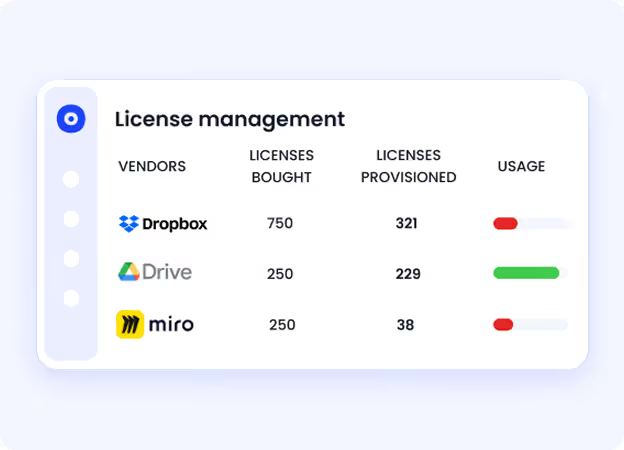
License compliance
Overprovisioned licenses create audit exposure and budget waste. CloudEagle tracks entitlements, actual usage, and contract terms across your entire SaaS portfolio, so you right-size before a renewal or an auditor asks.
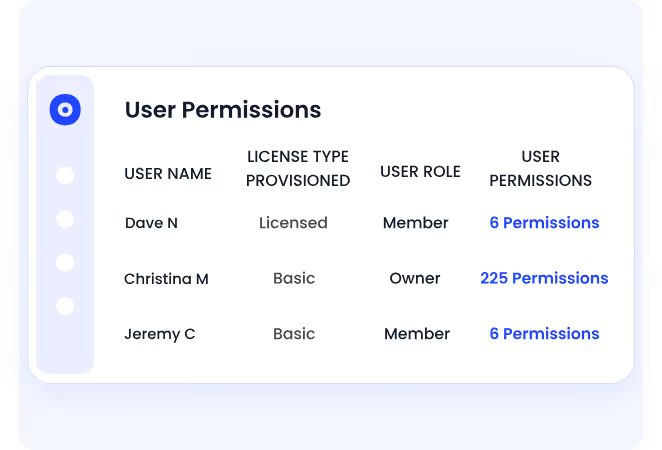
Access governance
Excessive permissions are one of the most common compliance findings. CloudEagle monitors access across applications, flags over-privileged accounts, and enforces least-privilege policies automatically without manual reviews.
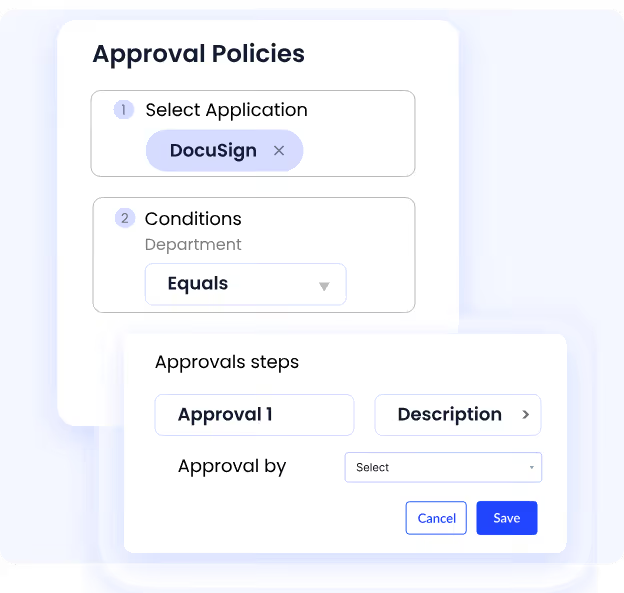
Policy enforcement
Compliance rules that live only in documents don't protect you. CloudEagle lets teams set policy-based controls that trigger automated actions: access revocations, approval workflows, real-time alerts, the moment a violation occurs.
Audit-ready reporting
Pulling audit evidence together manually takes weeks. CloudEagle generates on-demand reports across your SaaS and AI stack, formatted for internal audits, vendor reviews, or regulatory submissions.
For CISOs managing AI governance mandates and CIOs accountable for software compliance, CloudEagle turns a fragmented, manual process into a continuous, automated one. Book a demo to see it in action.
8. Compliance Gaps Don't Wait for Your Next Audit
The regulatory environment isn't getting simpler. More frameworks, more enforcement, more surface area to cover and less tolerance from regulators for "we didn't know."
The organizations getting this right aren't the ones with the biggest compliance teams. They're the ones that stopped treating compliance as a calendar event and started treating it as a continuous process.
Compliance monitoring tools are what make that shift operational. They give you the visibility, the automation, and the audit trail to stay ahead of violations instead of explaining them after the fact.
If your current approach relies on manual reviews and periodic audits, the question isn't whether you have gaps. It's how many, and how long they've been there.
9. FAQs
What is the purpose of compliance monitoring?
Compliance monitoring ensures an organization continuously adheres to regulatory requirements, internal policies, and industry standards. Its purpose is to detect violations in real time, reduce legal and financial risk, and maintain audit readiness rather than discovering gaps only during periodic reviews.
What is the purpose of monitoring tools?
Monitoring tools automate the tracking of system activity, user behavior, and policy adherence across an organization's technology environment. They replace manual oversight with continuous, scalable visibility, surfacing risks faster and with greater accuracy than human review alone.
What are the 5 C's of compliance?
The 5 C's of compliance are: Culture (organizational commitment to compliance), Controls (policies and mechanisms that enforce standards), Consistency (applying standards uniformly), Communication (keeping teams informed of obligations), and Continuous monitoring (ongoing oversight rather than point-in-time checks).
What are the 7 pillars of compliance?
The 7 pillars of compliance are: written policies and procedures, compliance leadership and oversight, training and education, effective communication, monitoring and auditing, enforcement and discipline, and response and prevention. Together, they form the foundation of a program built to withstand regulatory scrutiny.
.avif)
%201.svg)









.avif)




.avif)
.avif)




.png)





