HIPAA Compliance Checklist for 2025

IT compliance regulations are not abstract governance ideas. They require specific actions, like reviewing user access every quarter, encrypting customer data at rest, and reporting breaches within defined timeframes.
For example, GDPR requires breach notification within 72 hours. CCPA gives consumers the right to request disclosure of what personal data you collect and delete it upon request.
These aren’t policy statements. They force enterprises to prove who has access to customer data, which SaaS apps store it, how it’s protected, and how quickly incidents are escalated
In this article, we break down how IT compliance regulations can move from obligation to competitive advantage when implemented correctly.
TL;DR
- IT compliance regulations require real operational proof, not just policies or documentation.
- Compliance feels like a cost center when processes are manual and reactive.
- Enterprises struggle most with audit evidence, access reviews, and fragmented data visibility.
- Regulations like GDPR, SOC 2, and ISO/IEC 27001 define modern security practices.
- Platforms like CloudEagle.ai turn compliance into continuous, automated advantage instead of audit stress.
1. Why Do IT Compliance Regulations Feel Like A Cost Center?
IT compliance regulations feel like a cost center because they require ongoing operational work. Teams spend time preparing audit evidence, reviewing access logs, documenting controls, and responding to questionnaires.
- Audit Preparation Effort: Security teams export user access review audit, compile vendor risk assessments, and document control changes before every audit cycle.
- Manual Access Reviews: Managers review spreadsheets of user permissions across tools like Google Workspace and Salesforce line by line.
- Incident Documentation And Reporting: Compliance teams document breach timelines to meet requirements like the 72-hour notification rule under GDPR.
The financial impact is measurable. According to Forta, the average cost of non-compliance with data protection regulations is around $14.82 million.
When compliance work is reactive and manual, it feels like overhead. But when IT compliance regulations are automated and continuously monitored, the same requirements become structured processes that reduce long-term risk and audit fatigue.
2. Where Do Most Enterprises Struggle With IT Compliance?
Most enterprises struggle with IT compliance when they have to prove control execution, not just policy existence. Writing a security policy is simple. Showing evidence that IT compliance regulations were followed consistently is where friction begins.
- Access Review Evidence Gaps: Managers are required to review user permissions quarterly, but approvals are tracked in emails or spreadsheets.
- Incomplete Audit Trails: Admin actions in tools like Salesforce or Google Workspace aren’t centrally logged or retained long enough.
- Vendor Risk Documentation Delays: Security questionnaires and SOC 2 reports from third-party vendors are collected late, often during active audits.
The struggle intensifies when frameworks demand proof. For example, FISMA requires documented security controls and continuous monitoring, not one-time certification.
Manual Control Testing
Teams pull screenshots and reports manually to demonstrate compliance.
No Single Source Of Truth
Evidence is scattered across HR systems, identity providers, and individual SaaS platforms.
SaaS Compliance doesn’t fail because enterprises lack intent. It fails because control evidence isn’t centralized, automated, or easily retrievable when auditors ask for it.
Also Read: Top 10 SOC 2 Type 2 Compliance Platforms
3. Which IT Compliance Regulations Shape Enterprise Security Today?
Enterprise security controls are no longer defined by internal policies alone. They are shaped by regulatory mandates that specify how data must be protected, logged, accessed, and reported.
Some IT compliance regulations require breach notification within strict deadlines. Others mandate documented access reviews, encryption standards, and continuous SaaS monitoring. The following IT compliance regulations most directly shape enterprise security architecture today.
A. GDPR
GDPR is one of the most popular IT compliance regulations which directly shapes how organizations collect, store, process, and report on personal data of EU residents.
It is not limited to European companies. Any business handling EU personal data must comply.
- 72-Hour Breach Notification Rule: Enterprises must report certain data breaches to regulators within 72 hours of becoming aware.
- Right To Access And Deletion: Individuals can request a copy of their personal data and demand its deletion.
- Data Processing Documentation: Companies must document where personal data is stored and how it is processed.
These requirements force operational changes. Security teams must track where customer data lives across SaaS tools like Salesforce or HubSpot and prove access is controlled.
- Fines For Non-Compliance: According to GDPR, the penalties of up to 4% of global annual revenue or €20 million, whichever is higher.
- Ongoing Supervisory Enforcement: Regulators actively investigate breach response timelines and data handling practices.
GDPR is not a documentation exercise. It requires real-time visibility into data locations, user access, and incident response execution across the enterprise.
B. SOC 2
A growing SaaS company is preparing to close an enterprise deal. The customer’s security team requests a recent SOC 2 Type II report before signing. This is another essential IT compliance regulation enterprises must know.
Sales Perspective:
The deal is ready to close, but without a valid SOC 2 report covering security, availability, and confidentiality controls, SaaS procurement pauses the contract.
Security Perspective:
Internal controls must prove that user access reviews are performed, admin actions are logged, and changes to production systems are monitored consistently over time.
SOC 2 is not a one-time certificate. SOC 2 Type 2 IT compliance regulations evaluate whether controls operated effectively over a defined observation period.
Enterprises that treat SOC 2 as an operational discipline move faster in enterprise sales. Those that treat it as an annual project often scramble when customers request proof.
C. ISO 27001
ISO/IEC 27001 requires enterprises to build and maintain a formal Information Security Management System (ISMS). It evaluates whether security controls are documented, reviewed, and continuously improved.
Risk Assessment Requirement
Enterprises must identify information security risks and document how they are treated.
Access Control Policies
User access must be granted, reviewed, and revoked through defined procedures.
Asset Inventory Maintenance
Companies must maintain an updated inventory of information assets, including SaaS systems.
ISO 27001 IT compliance regulation also requires evidence. Policies alone are insufficient unless supported by logs, review records, and documented corrective actions.
- Internal Audit Cycles: Organizations must perform periodic internal audits of their controls.
- Management Review Meetings: Leadership must review security performance and risk posture regularly.
- Continuous Improvement Mandate: Controls must evolve based on audit findings and risk changes.
As the International Organization for Standardization states,
“ISO 27001 requires organizations to systematically examine their information security risks, taking account of the threats, vulnerabilities, and impacts.”
ISO 27001 turns security from a technical function into a management system. It requires proof that security is structured, monitored, and improved over time.
C. HIPAA
HIPAA governs how protected health information (PHI) is stored, accessed, and transmitted in the United States. This IT compliance regulation applies to healthcare providers, insurers, and any business associate handling patient data.
- Access Controls For PHI: Systems must restrict access to patient records based on role and documented authorization.
- Audit Logging Requirements: Enterprises must record and retain logs showing who accessed or modified health data.
- Business Associate Agreements (BAAs): Vendors handling PHI must sign formal agreements defining security responsibilities.
HIPAA enforcement focuses on real operational controls. Healthcare companies must prove that access to electronic health records is monitored, encrypted where required, and reviewed regularly to prevent unauthorized disclosure.
Also Read: Real-Life HIPAA Violation Examples That Could Happen to You
D. PCI DSS
PCI DSS applies to any enterprise that stores, processes, or transmits cardholder data. This IT compliance regulation defines specific technical and operational controls around payment systems.
- Network Segmentation Requirements: Cardholder data environments must be isolated from general corporate networks.
- Encryption Of Payment Data: Stored card data must be encrypted, and transmission must use secure protocols.
- Access Restriction Controls: Only authorized personnel can access systems handling payment information.
PCI DSS failures are not minor oversights. Misconfigured payment pages, weak access controls, or unpatched systems can expose large volumes of card data quickly.
- Mandatory Logging And Monitoring: Enterprises must track access to payment systems and review logs regularly.
- Quarterly Vulnerability Scans: External scans are required to identify exploitable weaknesses.
The financial impact is significant. As per Upwind, the average cost of data breach in the retail sector is more than $3.48 million.
PCI DSS forces enterprises to treat payment environments as high-risk zones. It requires documented controls, regular testing, and strict access management to reduce exposure.
E. FISMA
FISMA IT compliance regulation requires U.S. federal agencies and their contractors to implement structured, continuous security controls. It is not limited to policy creation. It mandates measurable oversight of federal information systems.
- Continuous Monitoring Programs: Agencies must track security posture in real time, not just during annual reviews.
- Documented Security Controls: Controls must align with standards such as NIST SP 800-53.
- Authorization To Operate (ATO): Systems must receive formal approval before handling federal data.
FISMA compliance is operationally intensive. Organizations must demonstrate that controls are not only designed, but actively enforced and reassessed.
- Regular Control Assessments: Security controls are tested periodically for effectiveness.
- Incident Reporting Obligations: Federal incidents must be reported within defined government timelines.
- Ongoing Risk Management: Systems must be re-evaluated when architecture or threat landscapes change.
FISMA turns compliance into a lifecycle requirement. FISMA IT compliance regulation demands continuous visibility into system configurations, user access, and control performance across all federal-facing environments.
4. How Does CloudEagle.ai Help Enterprises Stay Compliant?
IT compliance is often treated as a checklist, something enterprises must complete to avoid penalties or pass audits. But in reality, compliance frameworks like SOC 2, ISO 27001, GDPR, and HIPAA hold more value.
CloudEagle.ai helps enterprises move beyond reactive compliance by turning AI governance into a continuous, automated system.
Instead of slowing teams down, compliance becomes a foundation for faster decision-making, stronger security, and better business outcomes.
A: Turning Identity Governance Into Operational Efficiency
CloudEagle.ai transforms access reviews and identity governance from manual overhead into a streamlined, automated process.
Current Process
Access reviews are conducted manually using spreadsheets, ticketing systems, and scattered logs across applications.
Pain Points
Reviews take months to complete. Managers approve access without full context, and compliance becomes a time-consuming exercise.
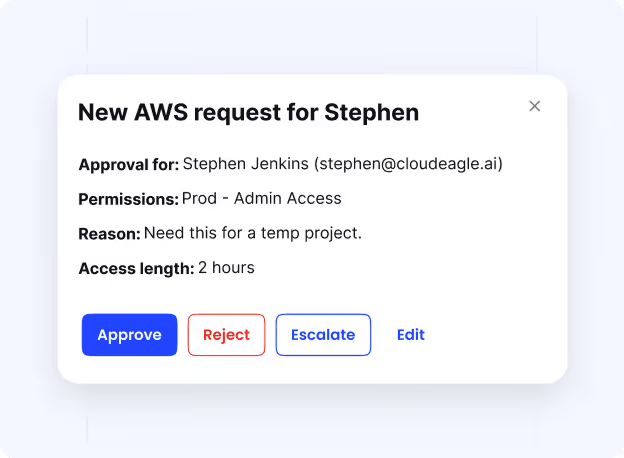
How We Do It
CloudEagle.ai automates access reviews, centralizes permissions, and continuously validates user access across SaaS apps.
Why We Are Better
Access governance becomes faster and more accurate, reducing operational burden while strengthening compliance.
B: Using Compliance Data to Drive Smarter Cost Decisions
CloudEagle.ai connects compliance data with usage and spend insights, enabling organizations to reduce waste while staying compliant.
Current Process
Compliance and cost management operate separately. Teams lack visibility into how access and usage impact SaaS spend.
Pain Points
Unused licenses, duplicate tools, and overprovisioned access increase costs without delivering value.
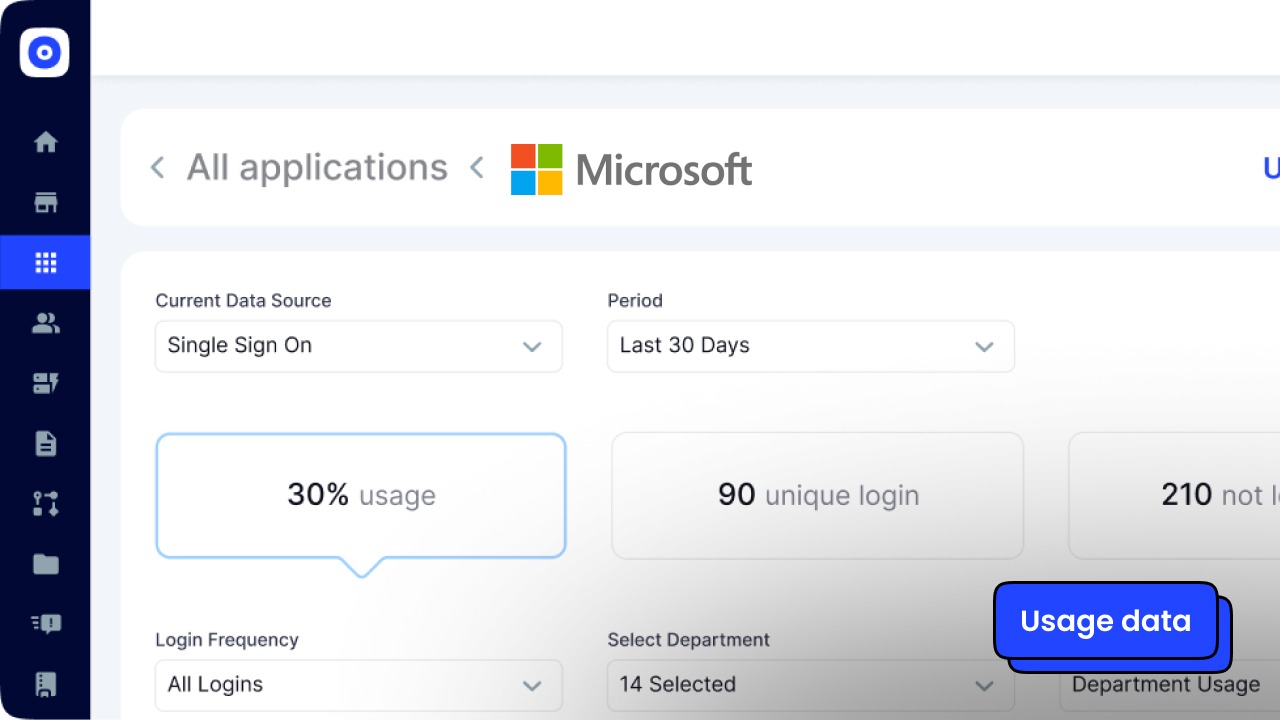
How We Do It
CloudEagle.ai correlates access, usage, and spend data to identify underutilized licenses and redundant applications.
Why We Are Better
Organizations reduce SaaS costs while maintaining compliance, turning governance into a financial advantage.
C: Building Continuous Audit Readiness Instead of Last-Minute Preparation
CloudEagle.ai ensures audit readiness is maintained at all times rather than rebuilt before each audit.
Current Process
Teams prepare for audits by gathering logs, approvals, and evidence manually across systems.
Pain Points
Audit preparation takes weeks. Missing documentation increases the risk of audit findings.
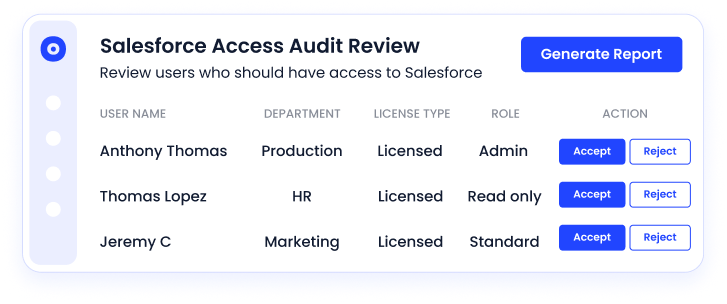
How We Do It
CloudEagle.ai automatically logs all access changes, approvals, and provisioning actions with audit-ready documentation.
Why We Are Better
Organizations maintain continuous audit readiness, reducing effort and improving compliance outcomes.
5. Conclusion
IT compliance regulations are no longer just obligations to satisfy auditors. They are a strategic lever that strengthens trust, reduces risk, and improves operational discipline.
Organizations that treat compliance as a continuous, integrated practice gain clearer visibility, faster audits, and stronger control over systems. Instead of slowing growth, compliance becomes a foundation for scaling securely and confidently.
6. FAQs
1. What is an example of IT compliance?
An example is meeting GDPR requirements by encrypting user data and controlling access. It also includes following HIPAA rules to protect patient information.
2. What is the meaning of IT compliance?
IT compliance means adhering to laws, regulations, and internal policies that govern how systems and data are managed. It ensures security, privacy, and proper usage of technology across the organization.
3. What are the 7 pillars of compliance?
The 7 pillars include standards, oversight, education, communication, monitoring, enforcement, and response. Together, they ensure compliance is structured, enforced, and continuously improved.
4. What are the IT compliance standards?
Common standards include ISO/IEC 27001, SOC 2, PCI DSS, and GDPR. Each focuses on security, privacy, or data protection.
5. What are the 5 C's of compliance?
The 5 C’s are commitment, compliance, communication, controls, and corrective action. They help organizations build a consistent and accountable compliance framework.

%201.svg)









.avif)




.avif)
.avif)




.png)





