HIPAA Compliance Checklist for 2025

Most IT leaders discover access issues in an acquired company on Day 1 of integration. By then, it is already their problem.
According to IBM’s 2024 Cost of a Data Breach Report, the average cost of a data breach reached $4.88 million, with identity-related access gaps remaining one of the most common causes of post-acquisition security exposure.
Overprivileged accounts, orphaned identities, undisclosed SaaS apps, and lingering OAuth connections from past vendors.
This blog covers what IT leaders must do before closing to get access governance during M&A right and avoid post-deal risk.
TL;DR
- 60% of organizations only discover cybersecurity issues at acquisition targets after the deal has already closed
- Access governance during M&A creates three distinct risk windows: pre-close, Day 1, and post-merge, each with different failure modes
- Disabling the target's identity provider does not close SaaS app access. OAuth tokens, shadow SaaS, and personal accounts survive any IdP migration
- The Day 1 access governance playbook has six steps and needs to run before systems are integrated, not after
- CloudEagle.ai gives IT leaders a complete cross-stack access picture before Day 1, including every app that lives outside SSO
1. Access Governance During M&A Starts With One Question: Who Has Access to What
Before you integrate a single system, you need a clear answer to that question. Not from the data room, but from real signals like SSO logs, browser activity, expense data, and OAuth connections across the target environment.
This is where M&A access governance begins.
The 60% Problem: Issues Found Only After Close
Nearly 60% of organizations uncover cybersecurity gaps only after a deal closes. During integration, IT teams often discover overprivileged accounts, undisclosed SaaS tools, or inactive users with active access.
By then, the liability has already transferred. What should have been part of access governance for mergers and acquisitions becomes a post-close cleanup.
Why Access Governance Is the First Line of Defense
Access governance during M&A is the foundation for every integration decision.
You cannot enforce least privilege or align identity systems without knowing who has access to what. Teams that prioritize access governance for mergers and acquisitions before close move faster and avoid rework.
Those who delay it spend months fixing issues that early visibility would have surfaced.
📖 Worth a Read: Access creep during role changes is one of the most common governance gaps in any environment. The same patterns show up during M&A, often at larger scale. 👉 How CloudEagle.ai Streamlines App Access Review for Compliance Success
2. The Access Governance Risks That Emerge at Every Stage of M&A
Access governance for mergers and acquisitions operates across three distinct phases, each with different risks.
Pre-Close: Overprivileged Accounts and Ungoverned SaaS
Before the deal closes, you see what the target shares. Not what their employees have quietly accumulated over years of normal business.
In a typical target environment:
- Shadow AI tools like ChatGPT, Claude, and Microsoft Copilot are being adopted by departments without IT review
- AI agents, service accounts, and non-human identities (NHIs) are retaining privileged access without clear ownership
- Shared API tokens and OAuth permissions connected to AI tools are creating unmanaged access paths
- Browser-based AI tools using personal accounts that sit completely outside traditional IAM visibility
None of this appears in a standard data room disclosure.
Day 1: Privilege Sprawl When Two Identity Systems Coexist
The moment a deal closes, two identity environments need to coexist, and privilege sprawl begins.
Access gets expanded to keep operations running, with the intent to fix it later. That rarely happens. Temporary access becomes permanent, and role-based controls are bypassed.
- Broad access granted for speed, not control
- Temporary permissions become permanent
- Duplicate admin roles and overlapping access models
- OAuth connections continue without clear ownership
This is where access governance during M&A starts to break.
Post-Merge: Orphaned Accounts and Unmanaged Access
A few months after close, the visible cleanup is done. What remains are the gaps.
Orphaned accounts, duplicate identities, and service accounts continue running without review. These are not obvious issues, but they persist quietly.
- Orphaned accounts from employees who left during integration
- Duplicate identities with inconsistent access levels
- Service accounts and automations left unchecked
- Access that was never right-sized post-integration
This is where audit findings typically originate, not from major failures, but from small access decisions made during mergers and acquisitions that were never revisited.
3. Pre-Close Access Governance for M&A: What IT Must Audit
Build a Complete Access Inventory
Pull from every source available during diligence, not just what the target's IT team provides:
- Identity provider logs for the past 90 days
- Expense reports and corporate card data for SaaS charges
- OAuth grants connected to core systems
- Browser activity or endpoint logs were available
Identify Every Admin Account, Shared Credential, and Privileged Role
For every system in the target's environment, identify:
- Who holds admin or elevated privileges
- When those privileges were last reviewed
- Whether the account belongs to a current employee, contractor, or service account
- Whether admin access was granted for a purpose that no longer exists
Review SaaS App Access and OAuth Integrations That Bypass IAM
Not all access is controlled by the identity provider. This is where access governance for mergers and acquisitions breaks most often.
- Identify all OAuth grants across critical systems
- Flag connections tied to former employees
- Review integrations accessing sensitive or regulated data
- Detect API keys embedded in scripts or internal tools
If it is not in your IdP, it will not show up in a standard review.
Map Regulatory Requirements to the Combined Entity’s Access Model
Access governance for mergers and acquisitions is directly tied to compliance.
- Map frameworks like GDPR, HIPAA, and SOC 2
- Identify systems handling regulated data
- Align access controls with compliance requirements
- Prioritize high-risk gaps before Day 1
This ensures access governance during M&A is not just about security, but also audit readiness.
Review Shadow AI and AI Tool Access Before Close
- Identify ChatGPT Enterprise, Microsoft Copilot, Claude, and browser-based AI tools already in use
- Review OAuth permissions connected to AI tools across critical systems
- Detect API tokens tied to AI workflows and automation
- Flag AI agents and service accounts with privileged access
- Identify AI tools accessing sensitive or regulated company data
4. The Day 1 Access Governance Playbook for M&A IT Leaders
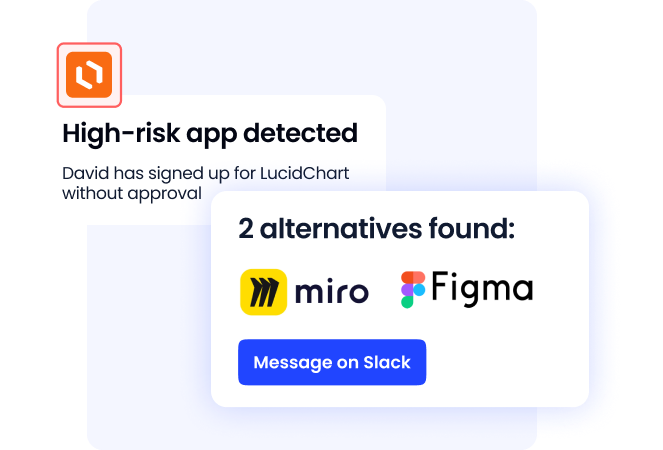
5. Access Governance During M&A: Why SaaS Access Slips Through
- Disabling the IdP does not close all access:
In access governance during M&A, SSO only covers connected apps. Everything outside it remains active - Shadow SaaS and personal accounts stay live:
Apps created with personal emails or team purchases sit outside access governance for mergers and acquisitions - AI tool OAuth tokens remain active even after the target’s IdP is disabled:
AI tool integrations continue working even after SSO is removed, creating hidden access paths outside standard governance. - Shadow AI and personal AI accounts survive any IdP migration:
Employees using personal accounts or department-purchased AI tools sit outside formal access governance. - AI agents and external AI integrations extend access risk:
AI agents, service accounts, and workflow automations often retain privileged access without ownership review.
6. How CloudEagle.ai Gives You Full Access Visibility Before Day 1
M&A moves fast, but access governance usually doesn’t. By the time IT begins auditing systems and onboarding users, employees from the acquired company may already have access to critical apps.
CloudEagle.ai is an AI-powered SaaS Management, Security, and Identity Governance platform that gives enterprises a unified command center to discover, secure, govern, and optimize both human and non-human identities across their entire SaaS and AI ecosystem.
It helps IT teams move from reactive access cleanup to Day-1 access control across both organizations.
A. Unified App Discovery Across Both Entities
Challenge
Traditional identity tools only cover apps behind SSO, while up to 60% of SaaS apps operate outside IT visibility. This makes it difficult to identify shadow IT, duplicate tools, and hidden access risks before integration begins.
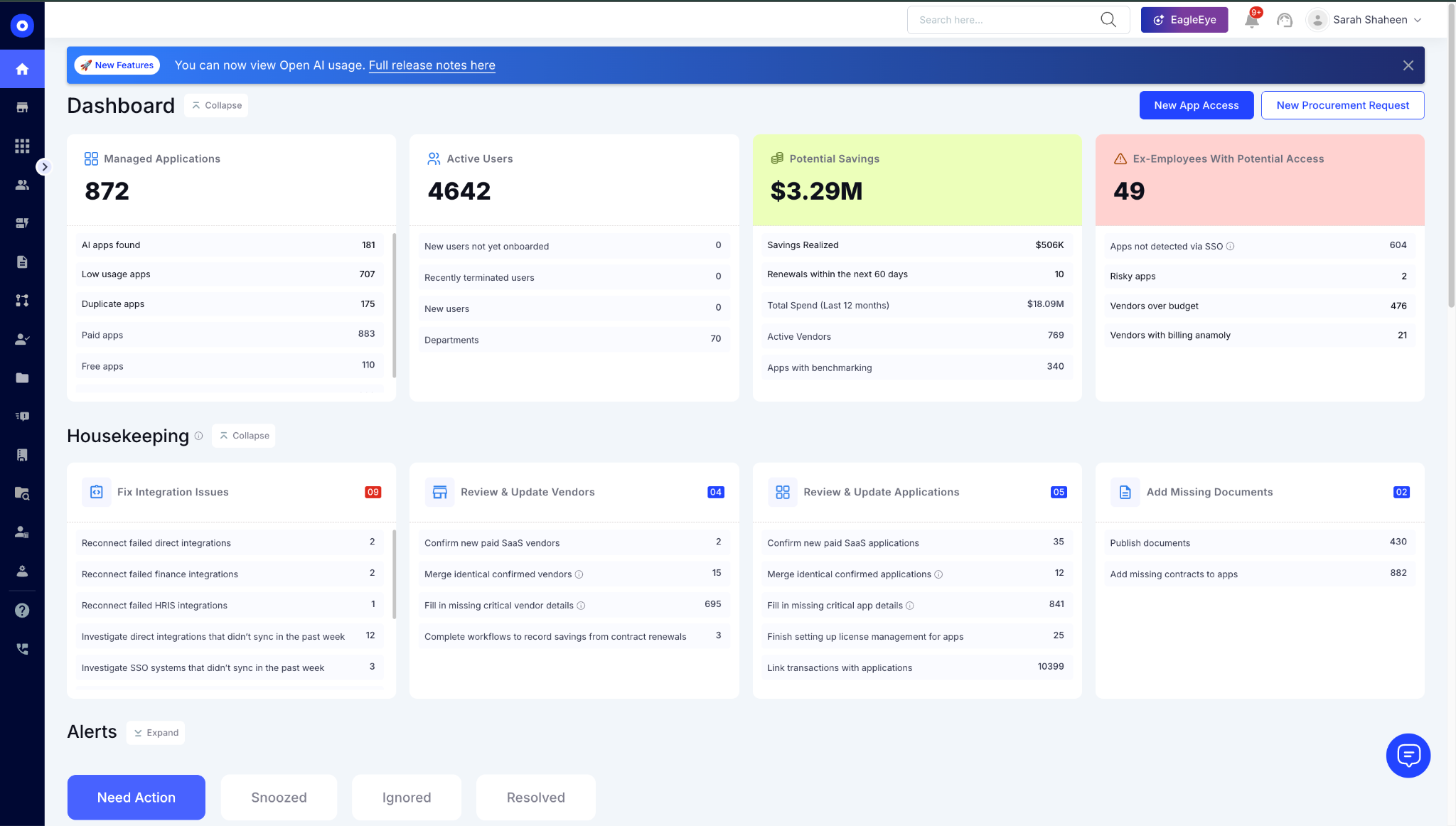
CE Solution
- Discovers apps through SSO, browser activity, and finance data
- Identifies shadow IT, unsanctioned SaaS, and browser-based AI tools
- Maps users, licenses, and spend across both organizations
- Detects duplicate tools and redundant spend early
Outcome
IT gets a complete view of all applications and access before Day 1, not after risk has already entered the environment.
B. Pre-Day-1 Access Risk Identification
Challenge
Without visibility, excessive privileges, orphaned accounts, contractors, and ex-employees retaining access become major Day-1 security risks.
CE Solution
- Identifies admin access and excessive permissions across apps
- Flags orphaned accounts and lingering contractor access
- Detects ex-employees still retaining system access
- Surfaces risky apps with security and compliance exposure
Outcome
Security teams can proactively remediate access risks before they become Day-1 liabilities.
C. Automated Onboarding, Offboarding, and Just-in-Time Access
Challenge
Manual provisioning and deprovisioning slow onboarding, create privilege creep, and leave access behind after employees leave. Temporary access often becomes permanent exposure.
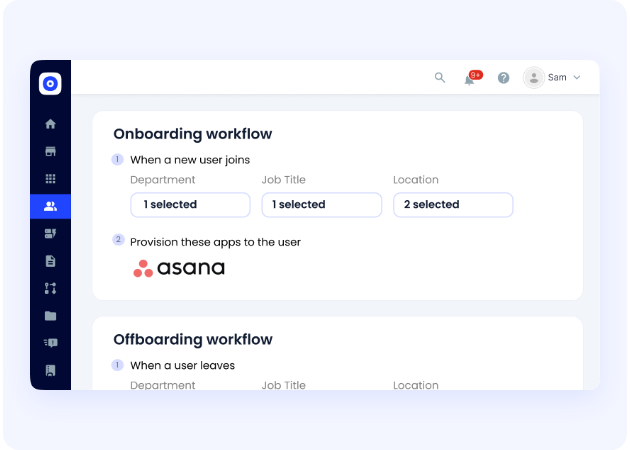
CE Solution
- Role-based auto-provisioning and deprovisioning across SSO and non-SSO apps
- Just-in-Time access for contractors and temporary users
- Centralized employee app catalog for controlled access requests
- Audit-ready access reviews and approval logs
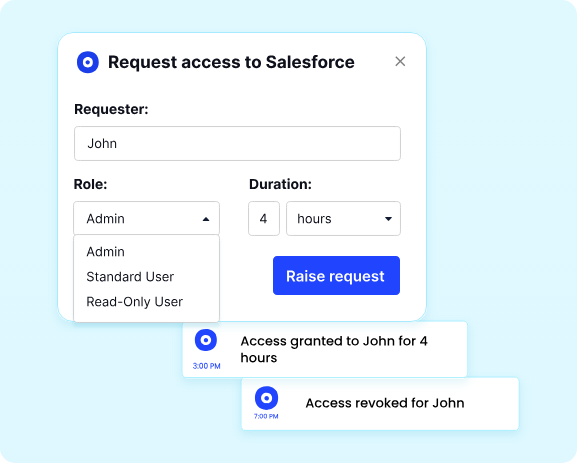
Outcome
Acquired employees get secure Day-1 access, unnecessary access is removed immediately, and compliance stays continuous from Day 1.
With 500+ direct integrations, $2B+ in savings delivered, and access governance across hundreds of SaaS and AI applications, CloudEagle helps IT teams move from reactive access cleanup to Day-1 access control across both organizations.
Conclusion
Access governance during M&A does not have to be the thing that causes post-close surprises. But it usually is, because it gets treated as an integration task rather than a pre-close requirement.
The IT leaders who handle cybersecurity for mergers and acquisitions well start earlier, look beyond the IdP, and treat Day 1 as a hard deadline rather than a starting point. They build a documented baseline that the combined entity's compliance program can actually stand on.
CloudEagle.ai gives IT leaders that visibility before the deal closes, across the full access surface, including everything that lives outside SSO.
Book a demo and see what access governance during your next deal looks like before Day 1.
Frequently Asked Questions
1. What is access governance during M&A?
Access governance for mergers and acquisitions is the process of auditing, controlling, and continuously managing who has access to what systems across both organizations throughout the deal lifecycle. It covers pre-close auditing, Day 1 revocations, and post-integration lifecycle management for the combined entity.
2. Why do cybersecurity issues in M&A usually surface after close?
Most access audits rely on what the target's IT team knows to disclose. Shadow SaaS, personal accounts, and OAuth connections are often invisible to the target's IT team as well. Without independent discovery across SSO, browser, financial, and endpoint data sources, these gaps do not surface until integration begins.
3. Does disabling the target's IdP close all access?
No. SSO controls authentication for apps connected to it. Apps that authenticate directly, through personal accounts, through shared credentials, or through OAuth without SSO remain entirely unaffected by an IdP disable.
4. What should IT leaders do in the week before close?
Freeze privileged access changes in both environments. Establish which IdP governs the combined entity. Revoke access for employees not continuing with the combined entity. Stand up access monitoring before systems are integrated. Document every access decision made during the transition.
5. How does access governance connect to compliance during M&A?
GDPR, HIPAA, and SOC 2 all require documented evidence of access controls and timely revocation. When two organizations merge, their compliance obligations merge too. Access governance gaps at the target become compliance gaps at the combined entity, and they are significantly easier to close before the deal than after the first audit.

%201.svg)









.avif)




.avif)
.avif)




.png)





