HIPAA Compliance Checklist for 2025

Cybersecurity has outgrown its silo. It’s no longer just an IT concern; it’s a business risk with real financial consequences. However, many CISOs still approach CFOs only when the budget season rolls around. That limits their impact.
The real challenge?
CISOs talk risk. CFOs talk numbers. And without common ground, both sides miss the bigger picture.
This article shows how to move past the budget ask – by aligning goals, speaking in business terms, and building a partnership that puts security at the center of strategy.
TL;DR
- CISOs can no longer operate in silos. Cybersecurity is a business risk with financial consequences, making CFO collaboration non-negotiable.
- Misalignment comes from language and priorities. CISOs focus on technical risk; CFOs care about financial impact.
- CISOs must align security with business goals, communicate in financial terms, and engage consistently throughout the year.
- Understanding finance cycles and using business cases helps CISOs secure funding and influence strategy.
- Tools like CloudEagle.ai support this shift by making security spending visible, measurable, and tied to outcomes CFOs care about.
1. Why CISO-CFO collaboration is more critical than ever
Cybersecurity has moved out of the server room and into the boardroom. It’s no longer just about patches and firewalls. It’s about revenue, reputation, and risk.
And boards are paying attention.
According to a Gartner survey, 84% of board members now see cybersecurity as a business risk, not a technical one.

That shift changes everything.
When security threats can trigger lawsuits, drop stock prices, or stall M&A deals, cybersecurity becomes a financial discussion, not just an IT concern.
And that means CISOs can’t operate in isolation anymore. They need to collaborate closely with the person who knows the business’s financial pulse best: the CFO.
But there's another force pushing this partnership forward: regulation.
Take the SEC Cybersecurity Disclosure Rules. They now require companies to report material cybersecurity incidents and outline risk management strategies. Compliance isn’t optional, and the financial implications of getting it wrong are steep. CFOs and CISOs can’t work in silos when the law expects them to coordinate.
The Real Cost of Misalignment: What the Numbers Say
The financial stakes of a weak CISO-CFO relationship are not theoretical. According to IBM's 2024 Cost of a Data Breach Report, the global average breach now costs $4.88 million: the highest figure ever recorded.
And FTI Consulting found that 66% of CFOs don't fully understand the CISO role and struggle to see tangible return on cyber investment.
That disconnect has a price tag.
Case in point: Target’s 2013 data breach
Hackers accessed payment data for over 40 million customers through a third-party HVAC vendor.
Months before the breach, Target’s security systems flagged suspicious activity; but the alerts weren’t prioritized or escalated effectively.
The result?
- $200M+ in breach-related costs
- Board and executive-level scrutiny
- Long-term brand damage
Analysts later pointed to poor communication between security and business leadership as a major reason the breach wasn’t contained sooner.
The takeaway: When CFOs and CISOs aren’t aligned, risk signals get lost; and companies pay the price.
2. Why CISOs and CFOs Still Don't Communicate Effectively (And How to Fix It)
If the need to collaborate is so clear, why is it still rare?
Let’s break down what’s getting in the way.
A. Siloed Mindset
CISOs often view CFOs as gatekeepers to the budget. CFOs see CISOs as cost centers.
Both roles tend to operate in silos, with little cross-functional overlap unless a crisis hits.
The result? They don’t fully understand each other’s priorities, which means opportunities for alignment get missed.
B. The Vocabulary Gap: How the Same Word Means Different Things
CISOs talk about zero-days, threat actors, and attack surfaces.
CFOs care about cash flow, liabilities, and market impact.
Both are speaking about risk – but in completely different languages.
And when risk isn’t communicated, it doesn’t get managed; it gets ignored.
Dipak Golencha, Global CFO of Palo Alto Networks, stressed this point at a CFO-CISO ADAPT Alliance event:
"Cybersecurity is an existential threat to every company. Gone are the days where CFOs could only be fired if they ran out of money, cooked the books, or had a major controls outage. Lack of adequate resourcing of cybersecurity is an emerging threat to their very existence." (via CSO Online, January 2025)
Here's exactly how that vocabulary gap plays out in practice:
C. Budget Approval Struggles
Cybersecurity costs can feel unpredictable. A quiet quarter might suddenly turn into an emergency funding request.
That unpredictability clashes with how CFOs work.
They like clean forecasts, predictable planning cycles, and measurable returns.
Without shared context, cybersecurity investments often get delayed, downsized, or denied.
D. Infrequent and Transactional Interactions
Too often, the only time CISOs engage CFOs is when money’s needed – or when something’s on fire.
This creates a transactional dynamic. It’s hard to build trust when the relationship only exists around funding requests or incident reports.
The real partnership needs regular check-ins, shared planning, and ongoing dialogue.
3. What CFOs Actually Want to Know About Cybersecurity
Most CISO-CFO collaboration guides are written entirely from the CISO's point of view. That's a mistake. Understanding what the CFO is actually asking – even when they're not saying it out loud – is the fastest way to close the communication gap.
The 4 Questions Every CFO Is Really Asking
1. "What is this going to cost me: this year and next year?"
CFOs think in planning cycles. Surprise budget requests are a red flag, not just an inconvenience. They want predictable, multi-year investment framing – not annual shock asks.
2. "What happens to us financially if we don't invest in this?"
CFOs quantify risk for a living. Show them the cost of not acting, expected breach costs, regulatory fines, insurance premium increases, operational downtime – and they have something to work with. Generic threat scenarios don't move the needle. Specific dollar figures do.
3. "How do I know this investment is working?"
ROI in cybersecurity is notoriously difficult to prove. But "we didn't get breached" is not a sufficient answer. CFOs want leading indicators – measurable KPIs that show the security posture is improving before something goes wrong.
4. "How does this connect to what we're trying to do as a business?"
Cybersecurity spending that isn't tied to a business objective looks like overhead. CFOs think in terms of growth, compliance, M&A readiness, and brand protection. Every security initiative needs to be mapped to at least one of those outcomes.
What Great CFOs Do Differently When It Comes to Cybersecurity
The best CFO-CISO relationships aren't one-sided.
Forward-thinking CFOs proactively learn cyber risk fundamentals, champion security investment with the board, join quarterly security reviews, and frame cybersecurity spend as enterprise risk management: the same way they'd treat insurance or legal exposure.
When the CFO takes shared ownership of cyber risk, the rest of the organization follows.
4. How CISOs Can Earn the CFO's Trust: 7 Proven Strategies
So we’ve covered why collaboration matters and what’s getting in the way. Now let’s get into the how.
Here are four practical ways CISOs can turn CFOs into strategic allies; not just budget approvers.
A. Align Cybersecurity with CFO Business Priorities
Start with what matters to them.
CFOs care about risk, yes, but through the lens of revenue, compliance, continuity, and cost efficiency. So if your security initiative doesn’t clearly connect to those outcomes, it’s going to fall flat.
Instead of leading with “we need a new XDR tool,” lead with this:
“This investment reduces the likelihood of downtime during peak sales periods by 60%, protecting an estimated $40M in revenue.”
That gets attention. That speaks their language.
Map every security project to a CFO priority:
- Preventing unexpected costs: data breach fines, ransomware payouts
- Ensuring compliance: SEC disclosures, SOX, GDPR
- Supporting growth: secure digital transformation, M&A readiness
- Preserving brand trust: risk to customer-facing systems or data
The more you can frame cybersecurity as business enablement, the easier it gets to win support.
B. How to Speak the CFO's Language: Translating Cyber Risk Into Financial Terms
You don’t need to become a finance expert, but you do need to stop speaking in acronyms.
Here’s what works better:
You get the idea.
When you reframe security risks as business risks with financial impact, CFOs can actually do something with that info. You’re not just alerting them – you’re helping them make better decisions.
C. Build Regular, Ongoing CISO-CFO Engagement
Waiting until budget time or breach time to talk? That’s too late. Make the CFO a partner in decision-making through consistent interaction:
- Monthly check-ins: 20 minutes is enough
- Shared cyber risk dashboard with financial impact estimates
- Pre-board prep sessions: align on the security narrative before it goes to directors
- Proactive context: explain high-profile breaches in the news before they ask
Real-world example:
At Turner Construction, the CFO and CISO meet twice a month to review risks, investment plans, and board readiness, proving regular alignment isn’t just possible, it’s effective.
This rhythm builds trust. And trust turns “no” into “let’s find a way.”
D. How to Get Cybersecurity Budget Approved: Understanding the CFO's Planning Cycle
One of the biggest friction points? Timing.
CISOs often drop funding requests mid-year when a new threat pops up. But CFOs run on structured cycles: Q4 forecasts, annual budget reviews, and forecast checkpoints. If your ask doesn’t match their rhythm, it’s dead on arrival.
Here’s how to fix that:
- Learn the finance team’s calendar: when do they plan, freeze, and review?
- Submit requests early, and tie them to financial goals or risk trade-offs
- Anticipate year-over-year trends: show progress, not just spend
- Back up your request with scenario analysis:
“If X risk happens, here’s the cost. Here’s what we save if we act now.”
Think less “ask for more,” and more “make the case.”
Since the most common reason CISOs lose budget battles is timing. Here's where to show up:
And if things change mid-cycle? Be transparent. Frame it as protecting an existing investment or avoiding a bigger loss. Lead with: "Here is the financial exposure we're carrying, here is what elevated it, and here is the cost of addressing it versus accepting it." Give the CFO a real choice.
A Gartner study found that 73% of CFOs now make strategic decisions with cross-functional input: which means the door is open. You just have to walk through it with context.
5. The 8 Cybersecurity Metrics CFOs Actually Care About
This is the most common gap in CISO-CFO communication: CISOs tell CFOs that security is improving. They rarely show CFOs how much it's improving in terms that the CFO can verify.
Here are the eight metrics that change that conversation:
Pro tip: Don't dump all eight metrics on a CFO in the first meeting. Start with Cost Avoidance and MTTD; they're the most intuitive bridge between security performance and financial impact.
6. The AI Risk Blind Spot: Why CFOs and CISOs Must Own It Together
Three-quarters of finance leaders believe AI introduces security and privacy risks that could threaten their organization's financial health.
At the same time, employees are adopting AI tools faster than either the CISO or CFO can track.
This creates shared exposure that neither role can manage alone.
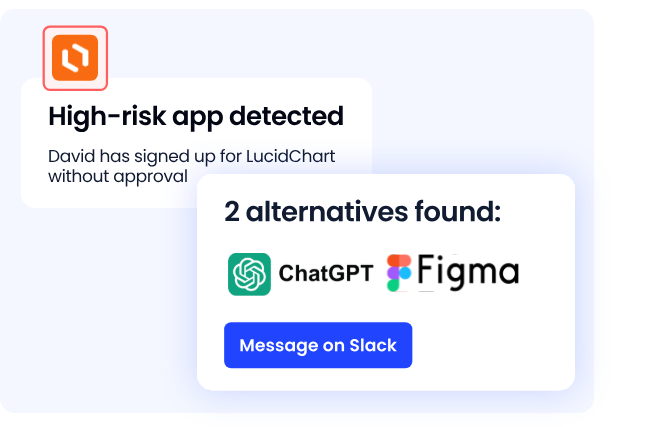
The core problem: Shadow AI. When employees use unsanctioned AI tools uploading customer data to public LLMs, using unapproved AI assistants for financial analysis the exposure is both a security risk and an uncontrolled cost.
That makes it a natural joint ownership problem.
How to govern it together:
- CISO governs what tools are approved and what data they can access
- CFO governs what gets budgeted, renewed, and cut
- Both teams maintain a centralized AI tool catalog, usage-based license reviews, and joint visibility into shadow AI spend
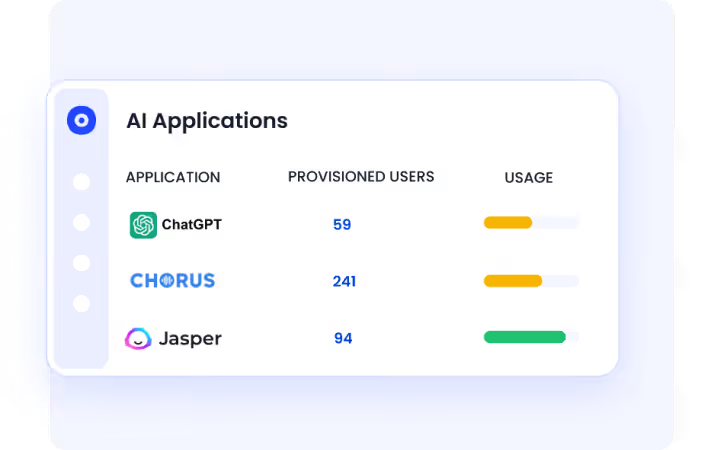
CloudEagle's AI detection capabilities give both teams exactly that shared view: which tools are in use, what they cost, and whether they have access they shouldn't.
The CFO-CISO AI governance conversation needs to happen now, before the first AI-related breach or compliance violation.
Also Read: AI and SaaS Security Breaches in 2025: How to Prepare for 2026
7. How CloudEagle.ai Bridges the CISO-CFO Gap
Most security tools give you visibility into threats. CloudEagle gives you visibility into spending, access, and risk: all in one place, in the language both the CISO and CFO speak.
Vendor Consolidation: The Shared Win
One of the most underutilized CISO-CFO collaboration opportunities is SaaS vendor consolidation. Here's why both sides win:
- CFOs win because consolidation reduces redundant spend. The average enterprise wastes 30% of its SaaS budget on underused or duplicate tools.
- CISOs win because fewer vendors mean a smaller attack surface. Every additional SaaS tool is a potential entry point for a breach or a shadow access risk.
CloudEagle surfaces both dimensions simultaneously: which tools are overspent, which licenses are underused, and which accounts have excessive or outdated permissions.
That single source of truth is what turns a CISO-CFO conversation from adversarial ("we need budget") to collaborative ("we found $400K in waste and here's how we're reinvesting it in stronger controls").
From Shadow IT to Shadow AI
Shadow AI is the new frontier. Employees are using AI tools that were never approved, reviewed for data security, or budgeted for. CloudEagle's AI detection gives CISOs and CFOs joint visibility into:
- Which AI tools are in use including ones never officially approved
- What data access those tools have and whether it crosses compliance lines
- What those tools are costing in direct spend, wasted licenses, and uncontrolled access risk
This closes the loop between the CISO's governance concern and the CFO's cost concern.
What CloudEagle Gives Both Teams
For the CISO:
- Full SaaS portfolio visibility, including shadow apps and unsanctioned AI tools
- Automated access reviews to identify and remove overprivileged accounts
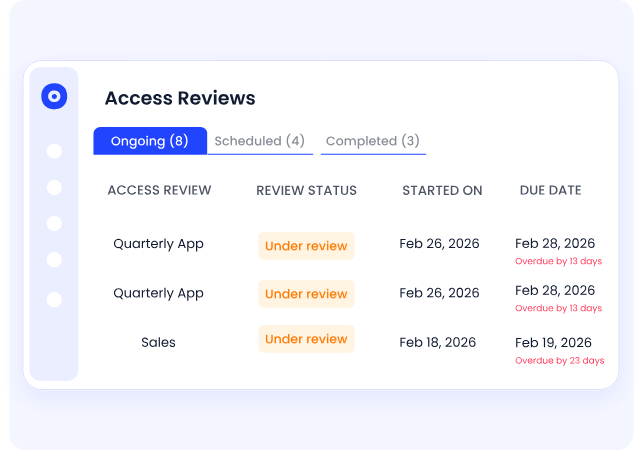
- Real-time risk flags when new tools or users are introduced outside governance
- License utilization data that ties directly to access hygiene
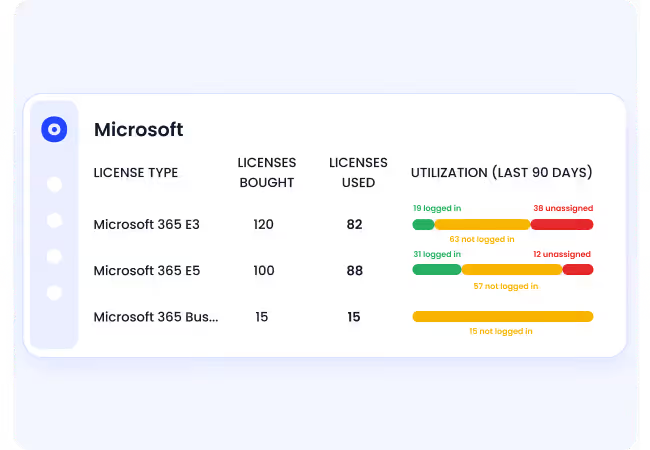
For the CFO:
- Real-time spend visibility across all SaaS vendors
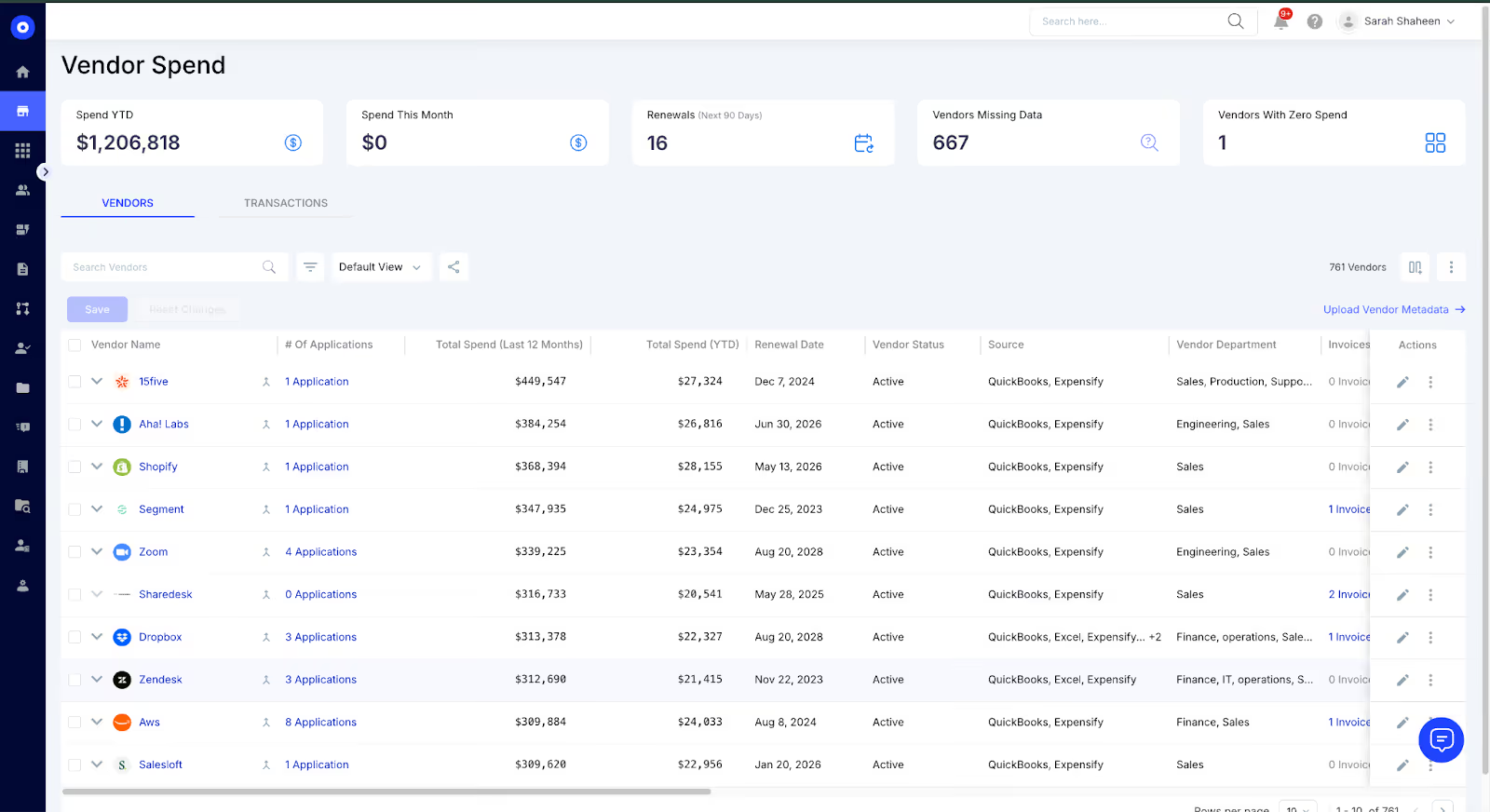
- License waste identification: see exactly where money is being spent on unused tools
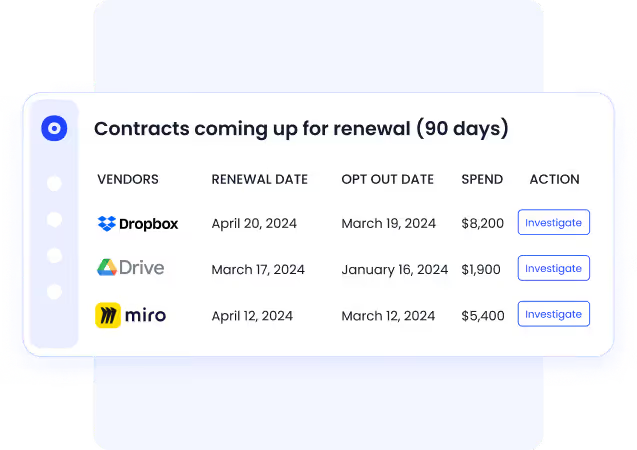
- Renewal calendar with advance notice, so nothing renews without CFO visibility
- Budget vs. actuals tracking for security and SaaS spend in one view
Together, these capabilities transform the CISO-CFO relationship from a quarterly budget fight into an ongoing, data-backed partnership.
8. How to Build a Cybersecurity Business Case Your CFO Will Actually Approve
The biggest moment of truth in the CISO-CFO relationship is the budget request. Most CISOs lead with the technical threat. The CFOs who say yes are responding to a different kind of pitch.
The 5-part framework:
1. Lead with the risk in dollars "A ransomware attack on our billing system = 4 days downtime = $2.3M revenue loss + $400K remediation." That's a number a CFO can work with. "Critical ransomware exposure" is not.
2. State the investment with a 3-year total CFOs make multi-year decisions. Single-year numbers feel incomplete. "We're requesting $180K/year for 3 years = $540K total investment."
3. Show the return with the math "This reduces our annual expected loss from $2.3M to under $400K, a 2.8:1 return." Don't claim ROI without showing the calculation.
4. State the cost of inaction "Without this, we accept $1.9M in unmitigated annual exposure and elevated insurance premiums." CFOs who say no often assume the status quo is acceptable. Make the cost explicit.
5. Anchor the timing to something real A regulatory deadline, a renewal window, a recent industry incident. Mid-cycle requests without urgency context almost always get deferred.
9. CISO-CFO Collaboration Checklist: 6 Actions That Build Lasting Trust
Use this before every budget meeting and as an ongoing operational rhythm.
Before the Budget Meeting
☑ Translated every major initiative into a financial risk/return statement
☑ Mapped top 3 security priorities to the CFO's stated business goals
☑ Built a 3-year investment roadmap
☑ Run a cost avoidance calculation to show ROI on last year's spend
☑ Identified SaaS license waste or over-provisioned access to return money on
☑ Pre-briefed the CFO so nothing is a surprise in the format meeting
Ongoing Rhythm
☑ Monthly 20-minute risk briefing with CFO
☑ Shared cyber risk dashboard with financial exposure estimates
☑ Quarterly SaaS and AI tool governance review with Procurement
☑ Pre-board prep session to align on security narrative
☑ Annual SOX/SEC/compliance review with CFO and Legal
☑ Post-incident debrief within 72 hours with financial impact assessment
Actionable Checklist: How to Strengthen CISO CFO Partnerships
If you’re serious about turning your CFO into a long-term ally, not just an approver, here’s what to focus on.
Keep this list close. Bookmark it. Print it. Whatever works.
A. Learn and Use Financial Terminology
Stop talking in acronyms. Start speaking in metrics that matter.
Words like ROI, P&L impact, cost avoidance, and forecast variance; they’ll go a lot further than “threat detection latency.”
B. Schedule Regular CFO Meetings
Don’t wait for a breach or budget season.
Book recurring 1:1s, even short ones. It signals that security is a shared responsibility, not a siloed one.
C. Create Cybersecurity Business Cases
Frame every investment like a business proposal.
What’s the risk if we do nothing? What’s the upside if we act? Add real numbers where possible.
Pro tip: Tie costs to potential savings, not just protection. CFOs are more likely to say yes to a pitch that prevents losses or protects revenue streams.
D. Align Security with CFO Priorities
Look at what your CFO is being measured on – cost control, regulatory reporting, resilience.
Now show how your initiatives support those goals. That’s the fastest way to get buy-in.
E. Educate the Finance Team
Most finance folks aren’t ignoring security; they just don’t know what to ask.
Offer training. Send plain-language updates. Share context when new risks pop up.
The more they know, the more they’ll care.
F. Build Relationships Beyond the CFO
Don’t just build a bridge to the CFO: loop in controllers, FP&A leads, and finance ops.
These are the people shaping the budget before it even hits the exec level.
Early support = fewer surprises.
10. CISOs as Business Leaders: The Shift That Changes Everything
The CISOs who build the strongest CFO relationships aren't the ones who learn to speak finance fluently. They're the ones who genuinely start thinking like business leaders.
That means:
- Owning business outcomes. The job is protecting the business's ability to operate, grow, and compete.
- Bringing solutions, not just problems. Every risk raised should come with a recommendation, a cost, and a trade-off analysis.
- Tracking metrics the board cares about. Mean time to detect, cost avoidance, license waste recovered.
- Building relationships before they're needed. The CFO should know your name before you show up in their calendar with a request.
As Brian Wenzel, CFO at Synchrony, put it:
"CFOs must think of cybersecurity as a business development arm versus a cost center."
That reframing is what the strongest CISO-CFO relationships are built on.
11. Should the CISO Report to the CFO?
There's no universal right answer. Here's the breakdown:
For reporting to the CFO:
- Risk management alignment is natural; both roles protect the business from financial exposure
- CFO's budget authority gives the CISO stronger organizational leverage
- SEC disclosure requirements already require close CFO-CISO coordination
Against reporting to the CFO:
- Creates perception that security is primarily a cost-control function
- Some CFOs lack the technical background to evaluate security decisions
- CISOs under CFOs often have less influence over operational technology
The trend: Most governance frameworks suggest the CISO should have direct access to both the CFO and CEO, with a dotted line to the board. The reporting structure matters less than the relationship quality. A CISO meeting monthly with their CFO and quarterly with the board will outperform one with a theoretically better org chart but no real communication.
12. CISOs as Business Leaders, Not Just Security Experts
The role has changed. Today’s CISOs aren’t just defending networks; they’re helping shape business decisions, protect revenue, and manage financial risk.
But that kind of influence doesn’t happen from the sidelines. It takes alignment, trust, and real partnership with the CFO.
When CISOs speak the language of business, understand planning cycles, and stay involved beyond the budget season, they earn a seat at the strategy table – not just a line item in someone else’s spreadsheet.
Security is the responsibility. Strategy is the opportunity.
And with platforms like CloudEagle, CISOs can back that strategy with clear data: on spend, renewals, and business impact that CFOs care about.
13. FAQs
1. Why do CFOs and CISOs need to collaborate?
Because cybersecurity is no longer just a technical issue; it’s a business risk with financial consequences. CFOs manage financial exposure. CISOs manage digital risk. When they work together, the business is stronger.
2. How can CISOs communicate cybersecurity risks in financial terms?
By focusing on business impact. Replace technical jargon with clear outcomes: cost avoidance, revenue protection, compliance risk, and operational uptime. Use real numbers, scenario planning, and tie every security initiative to a financial priority.
3. What metrics should a CISO present to the CFO?
Start with Cost Avoidance and MTTD. Then add MTTR, Cost Per Security Incident, SaaS License Utilization Rate, % of Overprivileged Accounts, Cyber Insurance Premium Trend, and Compliance Coverage Rate.
4. What does a CFO want to know about cybersecurity?
Four things: what it costs over multiple years, what happens financially without investment, how they'll measure ROI, and how it ties to business goals.
5. How can a CISO get executive buy-in for security budget?
Lead with financial exposure, show the investment to reduce it, calculate the ROI multiple, and state the cost of not acting. Present during Q3 strategic planning, not mid-cycle.
6. What is the role of CFO in cybersecurity?
Quantify cyber risk for the board, co-own regulatory compliance, evaluate cyber insurance, champion security investment internally, and govern AI and SaaS spending alongside the CISO.
7. How much should a company spend on cybersecurity?
Benchmarks suggest 10-15% of IT budget, but the real question is: what does your current risk exposure cost, and what investment brings it to an acceptable level?
Ready to give your CFO and CISO a shared view of your SaaS security posture and spending? Book a demo with CloudEagle to see how unified visibility changes both conversations.
Related reads:
→ Explore how CISOs can reduce internal risk by managing access at scale; and prove it to the CFO with real data.
→ Break down silos between security and finance by learning how CFOs approach cost-cutting; so you can align your next budget pitch with their priorities.
→ See how proactive security strategies and AI-driven insights can keep your team prepared, and your CFO looped in with measurable impacts
.avif)
%201.svg)









.avif)




.avif)
.avif)




.png)





