HIPAA Compliance Checklist for 2025

Think about the last Oracle Fusion renewal your team processed.
Your CFO pings you on a Thursday afternoon:
"Are we actually using everything we're paying for?"
You open the license report. Seat counts, module assignments, and renewal date. Everything looks accounted for. You send it over.
She replies:
"This doesn't tell me who's actually using what."
She's right. Oracle Fusion sits at the center of finance, HR, and procurement. Access expands quietly as roles change, projects end, and contractors come and go. What started as structured provisioning turns into standing access that nobody revisits.
Meanwhile, finance teams start pulling Oracle data into AI tools for faster reporting.
Many of those tools were never formally vetted. The data leaves your governed environment. The cost accumulates in places nobody tracks.
By the time anyone asks the hard question at renewal, answering it requires piecing together four different systems owned by four different teams, and there still isn't enough time to do anything about it.
This article is about closing that gap: where Oracle Fusion spends leaks, why traditional tools miss it, and how CIOs are building the visibility to finally answer your CFO's question with data.
TL;DR
- Oracle Fusion overspend is almost never a pricing problem. It's a visibility problem.
- Over-provisioned roles, shadow AI tools pulling ERP data, and renewals based on static counts are where money quietly disappears.
- Traditional SAM tools track licenses but cannot correlate identity, usage behavior, or AI activity.
- CloudEagle.ai connects those signals into one view: real usage, identity lifecycle, AI app activity, and renewal intelligence.
- The CIOs winning this aren't cutting costs arbitrarily. They're governing access like it's a business asset.
The Real Oracle Fusion Problem Isn’t Cost; It’s Visibility
Here's how most Oracle Fusion environments get out of hand.
A project kicks off. Someone needs access to the Advanced Financial Controls module. IT grants it. Project ends. Access stays. Six months later, that person is in a different role, and nobody revisited the entitlement because nobody had a reason to.
That's one instance. Now multiply it by:
- Every reorg where roles changed, but access didn't
- Every contractor whose engagement ended but whose account stayed active
- Every "just in case we need this module" request that became permanent
- Every project-specific privilege that outlived the project
The result: an ERP environment where license counts tell a story that has nothing to do with what's actually happening.
A Ponemon Institute study found that 71% of employees have access to data they shouldn't see. In a role-based ERP system, every premium role assigned to a user who doesn't need it is a license delivering zero value. The license report confirms the role exists. It cannot tell you whether it's being exercised.
The AI layer makes it worse.
Finance teams have gotten good at extracting Oracle data: forecasts, procurement trends, payroll figures, and piping it into generative AI tools for faster analysis. Many of those tools were never formally approved. The data leaves your governed environment. Nobody connects the dots until an auditor does.
Three problems running simultaneously, all out of view:
- License waste from roles no one revisited
- Shadow AI spends no one approved
- Renewal decisions based on incomplete data
Where Oracle Fusion Spend Actually Leaks
It's never one big line item. It's four quiet ones, compounding every year.
1. Over-Provisioned Roles
The pattern is always the same:
- Senior employees get premium modules by default, scoping access precisely takes effort nobody has time for
- Contractors get provisioned at a full-time staff level, so onboarding doesn't slow down
- Project access becomes permanent because there's no trigger to revisit it
A user with an Oracle Fusion Enterprise license who logs in twice a quarter costs the same as a daily power user.
Without usage-level data mapped to roles, there's no way to tell one from the other.
2. Shadow AI Interacting With ERP Data
Your FP&A team started uploading quarterly close data into a ChatGPT-based tool six months ago. It generates variance commentary faster. Nobody asked IT or security. The tool isn't in your SaaS catalog.
It's now a regular part of the close process.
This is happening in finance teams across industries. The consequences are two separate budget problems that surface as one security problem:
- You're paying for a shadow SaaS tool that procurement doesn't know exists
- You're carrying compliance exposure nobody has formally assessed
3. Missed Renewal Leverage
Oracle sends a renewal proposal. You have 60 days. You pull the license report, confirm headcount looks approximately right, and sign.
No module usage audit or picture of which workloads are Oracle-dependent versus covered elsewhere.
Negotiations backed by behavioral usage data look very different from negotiations backed by seat counts. One side has leverage. The other is guessing.
4. Fragmented Reporting Across Teams
Each team owns one piece:
- Finance owns the invoice
- IT owns provisioning
- Security owns access alerts
- Procurement owns the contract timeline
The critical correlation of this role is unused AND this renewal is in 90 days never gets surfaced because no single system holds all four data points at once.
Why Spreadsheets and Siloed Tools Can't Solve This
Most organizations are managing Oracle Fusion the same way they were five years ago.
Renewals tracked in a shared spreadsheet. License counts are pulled manually from the admin console. Access reviews run as quarterly exports. Provisioning is handled through a combination of Okta, IT tickets, and someone's institutional knowledge of which modules each role needs.
Each of those things works in isolation. The problem is they don't talk to each other.
When a contractor's engagement ends:
- HR closes the record in Workday
- The Okta account gets suspended
- The Oracle module access stays active
- The license stays allocated
- Nobody connects all three because they live in different systems with different owners
That's not a process failure. That's a structural gap and no amount of spreadsheet discipline closes it.
What the current approach shows you:
- How many Oracle licenses you purchased this year
- What the renewal date is
- Who is assigned to which license type
- What you paid last cycle
What it cannot tell you:
- Whether assigned Oracle roles are being actively used
- Whether premium modules align with what people actually do
- Whether a contractor who left three months ago still has active entitlements
- Which AI tools are your finance team using to process Oracle data
- What comparable companies paid for the same configuration at renewal
The gap between those two lists is where Oracle Fusion spends accumulates. Spreadsheets capture what you decided. They have no mechanism to tell you whether that decision is still valid.
Closing this gap requires something the spreadsheet was never designed to do: correlate identity data, usage behavior, AI activity, and renewal timelines continuously and surface the gaps automatically, not when someone thinks to look.
How CloudEagle.ai Gives CIOs the Oracle Intelligence They're Missing
CloudEagle.ai is an AI-powered SaaS management, Identity governance, and SaaS security platform. A unified command center to discover, secure, govern, and optimize your entire SaaS and AI ecosystem without replacing your existing tools.
Before CloudEagle, here's what managing Oracle Fusion actually looked like:
Step 1: See Everything
Most organizations can tell you how much Oracle costs.
They cannot tell you what it's being used for.
CloudEagle aggregates data from 500+ integrations: IdP, HRIS, finance systems, browser data, firewalls, and MDM into one dashboard. Onboards in 30 minutes. Zero manual entry. AI extracts contract metadata automatically.
For Oracle specifically, every assigned role gets mapped against:
- Login frequency
- Module activity
- Feature access patterns
- Changes since last review
When a contract is up in 90 days, and module usage has dropped 40% over the prior quarter, that gets surfaced automatically. Nobody has to go looking.
Step 2: Find the Waste
IT teams know unused licenses exist. The practical problem is the process:
- Email 3,000 users across 300 apps
- Track who responded
- Manually deprovision stragglers
- Return the license to the pool
That's so cumbersome that it rarely happens. So the licenses sit.
CloudEagle's license harvesting engine automates the entire cycle. It identifies unused licenses, notifies inactive users, tracks responses, deprovisions non-responders, and returns licenses to the pool — automatically.

The key difference from other tools: harvesting decisions are based on feature usage, not just logins.
- A Zoom user who has never hosted a meeting doesn't need a paid host license
- A Salesforce user who only reads reports doesn't need an Enterprise seat
That granularity is what makes savings real and defensible at renewal.
App rationalization runs in parallel if three departments are running separate contract management tools; CloudEagle surfaces the overlap, shows which users duplicate across them, and quantifies the consolidation savings.
Step 3: Govern Identity Continuously
Access drift has no single moment of failure. It accumulates:
- A contractor keeps access for a month past the engagement end
- A promotion adds a new role, but nobody removes the old one
- A project ends, but module access stays active
Each event is minor. The aggregate is expensive.
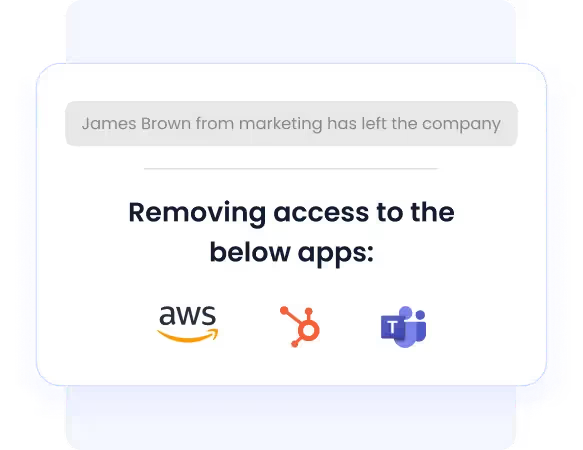
CloudEagle automates the full identity lifecycle against Oracle roles:
- New employee joins → Oracle module access provisioned automatically by role, department, location
- Employee moves teams → access adjusts in the same motion
- Contractor engagement ends → entitlements revoked, license returned to pool, no ticket required
Access reviews shift from quarterly campaigns to continuous monitoring. CloudEagle flags automatically:
- Ex-employees still holding access
- Elevated-privilege accounts inactive for 60-plus days
- Accounts present in Oracle but absent from HRIS
Time-based access lets IT grant Oracle module access for a fixed window: 30 days, 90 days, or project duration. Access expires automatically. No ongoing manual work required.
When the auditor asks for deprovisioning evidence, CloudEagle attaches it automatically. The evidence is captured in real time, not reconstructed from Slack threads the weekend before the audit.
Step 4: Stop Shadow AI Before It Starts
Shadow AI in Oracle environments gets discovered as a security problem. By the time finance finds a subscription charge for an unapproved AI tool, the data has been flowing through it for months.
CloudEagle maintains a proprietary inventory of SaaS and AI applications (SaaSMap™) correlated across browser plugin data, Zscaler, CrowdStrike, and IdP logs.
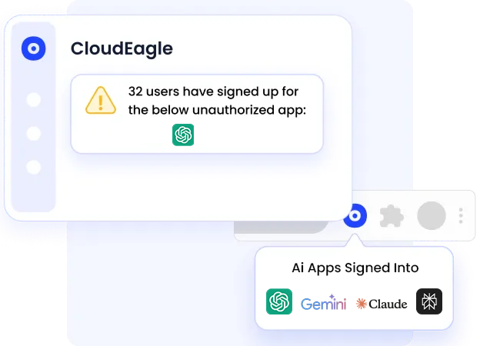
When a finance analyst uploads Oracle data into an unapproved AI tool: visible immediately. You don’t need a report anymore.
When a user tries to access an unapproved AI tool while an approved alternative exists, CloudEagle presents a real-time governance prompt, educates the user on policy, and redirects them to the sanctioned tool.
The intervention happens at adoption before the data flows, before the invoice arrives, before the audit finding gets written.
Step 5: Win Renewals Before Vendors Make Their Move
The typical Oracle renewal:
- Vendor sends proposal
- Procurement checks the seat count against last year
- Someone confirms the number feels approximately right
- Renewal gets signed usually within two weeks of the deadline
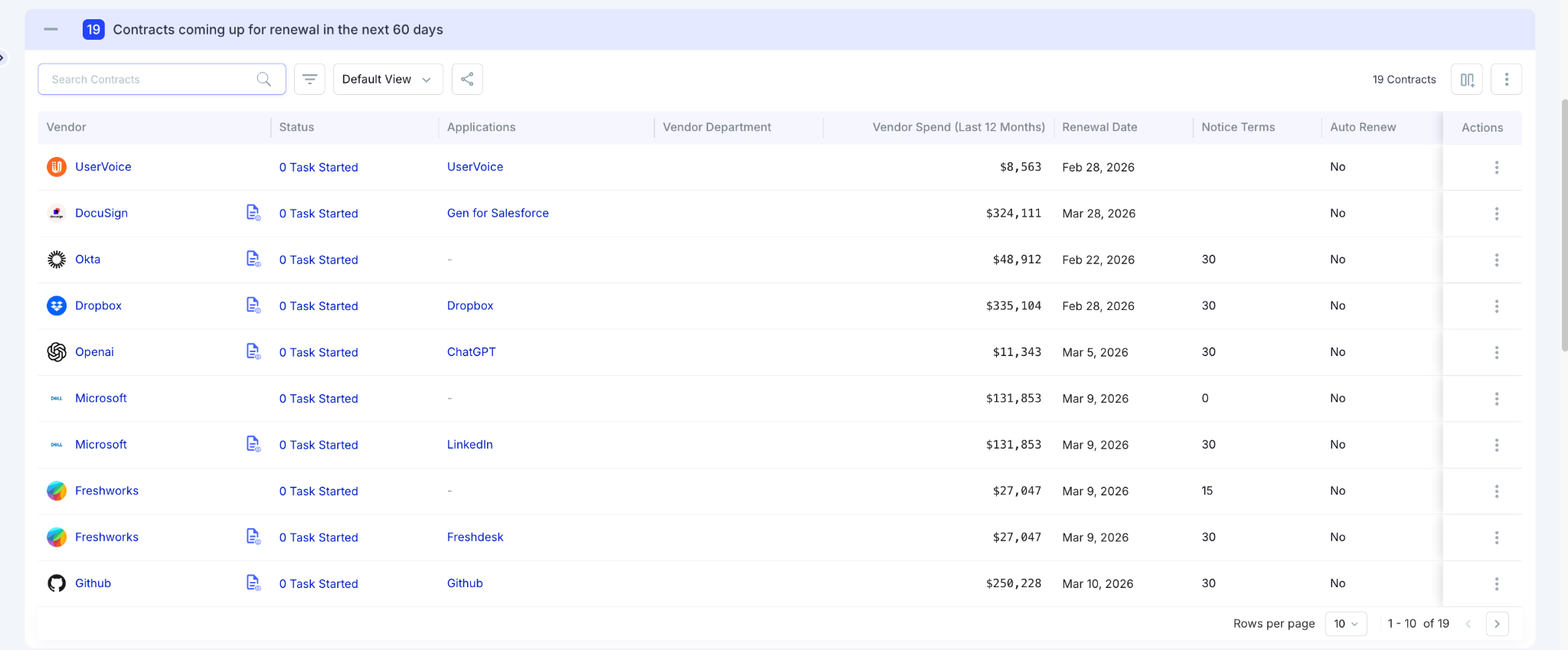
CloudEagle triggers automated renewal workflows 90 days before the contract date. The first message to your team includes:
- Current module usage data
- Price benchmarking against market rates
- Alternative vendor options
- AI-generated recommendation
Tasks are assigned with deadlines. Auto-escalated if stakeholders don't respond. Approvals happen in Slack, email, or Coupa, wherever your team already works.
The benchmarking database covers the mid and long tail of vendors: the renewals, where most enterprises overpay because nobody has market data. Your procurement team walks in knowing what comparable customers paid for equivalent configurations.
The Alignment Problem
One of the most predictable conversations in enterprise IT:
Finance: "Why is the Oracle bill going up?"
IT: "We provisioned based on what the business requested."
Security: "We flagged over-privileged access three months ago. Nobody actioned it."
Procurement: "The renewal was signed before we had time to review usage."
Nobody is wrong. Everyone is working from a partial picture.
When license usage data, identity assignments, AI activity, and renewal timelines sit in one system:
- IT can justify access decisions with behavioral evidence
- Finance can forecast from actual consumption trends
- Security can flag risk tied to specific Oracle roles
- Procurement can negotiate with a verified map of what's used and what isn't
CloudEagle integrates bi-directionally with existing ITSM, IdP, CLM, and security tools, the connective tissue their Oracle governance was missing.
What Happens When You Ignore Oracle Fusion Intelligence?
Oracle governance failures are quiet. The damage accumulates in four parallel tracks:
- Renewals auto-execute. Nobody had usage data in time to push back. Another year of unoptimized spend locked in.
- Access drift compounds. Roles accumulate faster than they get removed. The attack surface grows by default.
- Shadow AI spending goes undetected. Until a charge hits the expense report. By then, Oracle data had been flowing through an unapproved tool for months.
- Audit findings surface at the worst time. Contractor retained ERP access six months past their end date. No deprovisioning evidence. A finding gets written.
For a 5,000-employee firm running ~$30M across 250 SaaS vendors, 25% of spend wasted on unused or redundant tools (Gartner, 2023) is $7.5M sitting in access no one revisited, licenses no one right-sized, and renewals no one had time to negotiate.
The question for most CIOs isn't whether this is happening. It's whether they've decided to build a system to stop it.
The New CIO Mandate: Spend, AI, and Identity as One System
A decade ago: 10–15 vendors, 3-year licenses, centralized buying.
Today: 200-plus vendors, monthly licenses, 500-plus procurement touchpoints, and AI tools embedding into core business workflows before governance has caught up.
What used to be three separate problems has collapsed into one:
- Shadow AI tools accessing Oracle data → spend problem and security problem, same event
- Over-provisioned Oracle roles → license cost and access risk, same root cause
- Renewals without behavioral data → budget failure and governance failure, same conversation
The CIOs managing this well have stopped trying to govern each problem separately. Managing spend, AI governance, and identity from one evidence base is what makes Oracle Fusion optimization stick beyond a single renewal cycle.
Oracle Fusion Spend Reduction Is a Governance Strategy
The organizations that have meaningfully reduced Oracle Fusion spend showed up to renewals knowing exactly what they used, what they didn't, and why.
They had behavioral data. Oracle had a proposal. Those are different starting positions.
That posture comes from connecting things that typically operate in isolation: role assignments and usage data, identity lifecycle events and license consumption, AI tool activity and ERP data governance, renewal timelines and optimization reviews.
When spend intelligence and governance operate as one system, Oracle stops being a recurring budget surprise. That's the answer your CFO was actually asking for.
FAQs
What does "Oracle Cloud Spend Classification" actually mean in practice?
Breaking Oracle costs down beyond a single invoice line: by module, by department, by user role, by environment. When that connects to identity data and usage patterns, you can distinguish strategic investment from avoidable waste before renewal, not after.
What are the 4 C's of Oracle Fusion, and why do they matter for spend control?
Core Financials (GL, payables, receivables), Customer Experience (sales, service, marketing), Commerce and Supply Chain (procurement, inventory, operations), and Capital Management (HR, payroll, workforce). Access is role-based across all four. Improper provisioning in any one of them inflates license costs in ways standard reports won't surface.
How do organizations actually reduce Oracle license costs sustainably?
One-time audits produce temporary savings. What makes reduction stick: continuous access reviews grounded in behavioral data, time-bound permissions for project and contractor access, renewal planning from verified usage trends, and visibility into AI tools interacting with ERP data. Without those controls, access expands again and savings erode within a year.
How does CloudEagle.ai differ from SAM tools for Oracle environments?
A SAM tool tells you what you own. CloudEagle tells you what you're actually using, who has access they shouldn't, which AI tools are touching your Oracle data, and what to negotiate at renewal based on verified consumption. Most Oracle optimization failures happen because teams are working from an inventory view when they need an intelligence layer.
.avif)
%201.svg)









.avif)




.avif)
.avif)




.png)





