HIPAA Compliance Checklist for 2025

In a board meeting, a director asks a simple question: “How many former employees still have access to our SaaS tools today?” The CISO knows access reviews happen quarterly, but can’t answer with a number.
Another director follows up: “How many admins do we have across Salesforce, Google Workspace, and GitHub?” Again, no immediate answer.
This is where SaaS KPIs break down at the board level. Leaders don’t want to hear that controls exist. They want to know how many risky permissions are active right now and how long access removal takes.
In this article, we’ll break down the SaaS compliance KPIs that actually matter to the board. You’ll know why they reflect real risk and how they turn compliance from a checkbox into executive-level visibility.
TL;DR
- SaaS compliance metrics fail when they track activities instead of measurable risk exposure.
- Boards care about real indicators like access removal time and number of privileged users.
- Key KPIs include MFA coverage, shadow IT detection rate, and monitored vs unmonitored apps.
- Enterprises struggle due to fragmented data across identity systems, SaaS apps, and manual reports.
- CloudEagle.ai centralizes data and turns compliance KPIs into real-time, board-level visibility.
1. Why Do Most SaaS Compliance Metrics Fail To Resonate With The Board?
Most SaaS compliance metrics fail at the board level because they describe activities instead of measurable risk. Boards don’t ask how many policies exist. They ask how many users still have access they shouldn’t.
- Shadow IT Exposure Instead Of App Counts: Reports list approved apps but don’t quantify undiscovered shadow IT. According to CISCO, 80% of end users use software without IT approval.
- Audit Tasks Without Business Impact: Metrics track completed access reviews but don’t reveal how long it takes to remove access.
- Compliance Language Instead Of Operational Data: Dashboards mention “control effectiveness” but don’t show how many SaaS apps store customer data.
Boards respond to numbers tied to exposure. Metrics like number of privileged accounts and number of SaaS apps storing sensitive data translate compliance into operational risk.
2. Which SaaS Compliance KPIs Should Be Reported To The Board?
Boards don’t need long lists of compliance controls. For example, directors often ask questions like: How quickly is SaaS access removed after employees leave? How many SaaS applications store customer or financial data?
These are SaaS compliance KPIs. They translate daily security operations into measurable indicators of risk and identity governance. The following SaaS KPIs are the ones boards can quickly understand.
A. Percentage Of SaaS Apps Covered By Compliance Monitoring
This B2B SaaS KPI shows how many SaaS applications in the company are actively monitored for security and IT compliance controls. Boards want to know whether oversight covers all critical tools or only a small portion of them.
- Known Apps Under Monitoring: Core systems like Salesforce, Google Workspace, and Slack may have logging, access reviews, and security policies in place.
- Unmonitored Apps Handling Business Data: Smaller tools used by teams might store customer lists, internal documents, or financial reports without compliance oversight.
- Shadow SaaS Applications: Departments sometimes adopt tools independently, meaning they operate outside centralized monitoring.
Joshua Peskay, a 3CPO (CIO, CISO, and CPO) at RoundTable Technology, stated:
“80% of the time people are just ignorant about the tools that they have in the company. So they just use another tool because they didn't know.”
The gap between monitored and unmonitored apps is where compliance risk grows. If monitoring only covers a portion of the SaaS stack, security teams cannot verify where sensitive data is stored.
- Some apps may not have logging, access reviews, or vendor risk assessments.
- Sensitive information may exist in tools outside compliance monitoring.
This SaaS compliance KPI answers a simple board-level question: Of all the SaaS apps used in the company, how many are actually under compliance risk management?
B. Time To Revoke SaaS Access After Employee Offboarding
This SaaS compliance KPI measures how long it takes to remove a departing employee’s access from SaaS systems after HR records the exit. Boards care about this because delayed revocation leaves real accounts active in production tools.
Active Accounts After Departure
A former employee may still log into Google Workspace, view conversations in Slack, or export records from Salesforce if access isn’t revoked immediately.
Manual Deprovisioning Delays
If each application requires separate removal steps, access may remain active for hours or days.
Disconnected HR And Identity Systems
When HR systems are not linked to identity providers, employee offboarding updates do not automatically trigger account removal.
As Bruce Schneier once said,
“Security is a process, not a product.”
When offboarding relies on manual updates, that process slows down. Measuring the time it takes to revoke SaaS access shows whether identity controls keep pace with employee changes.
C. Number Of Privileged Users Across Critical SaaS Systems
This SaaS compliance KPI tracks how many users have privileged access across core SaaS applications. Boards care about this because privileged accounts can change configurations, export sensitive data, or grant access to other users.
- Admins In Financial Systems: Administrators in NetSuite or QuickBooks can modify financial records and reporting structures.
- Workspace Owners In Knowledge Platforms: Owners in Notion or Confluence can change workspace permissions and access sensitive documentation.
- Support Platform Super Admins: Privileged users in Zendesk or Intercom can view customer conversations and export support data.
Privileged access is necessary for operations, but the number of such accounts should stay tightly controlled. As per GMInsights, the privileged access management market size will grow at a CAGR of 23.3% between 2025 and 2034.
D. Percentage Of Users With Multi-Factor Authentication Enabled
This SaaS KPI measures how many SaaS users must verify their identity using a second factor. Boards track this because single-password access remains one of the most common entry points for attackers.
- Identity Provider MFA Coverage: Users logging in through Okta or Microsoft Entra ID must confirm their identity with a mobile authenticator or hardware key.
- Application-Level MFA Enforcement: Systems like Zendesk or HubSpot can require MFA even if SSO policies fail.
- Privileged Account Protection: Admin accounts often require stronger authentication methods such as hardware security keys.
MFA coverage becomes meaningful when measured across all users and applications. According to Microsoft Lean, almost 99% of breached accounts don’t have MFA.
- Users Without MFA Enabled: Some legacy accounts may still authenticate with only a password.
- Service Accounts Excluded From Policies: Automated integrations sometimes bypass MFA enforcement.
- Inconsistent Enforcement Across Apps: MFA may be required for identity systems but optional within individual SaaS tools.
Tracking this SaaS business KPI shows whether advanced authentication methods are consistently applied across the enterprise’s SaaS environment.
E. Shadow IT Discovery And Remediation Rate
This SaaS compliance KPI measures how quickly new, unapproved SaaS applications are discovered under security oversight. Boards care about this because unknown tools often store company data before security teams even know they exist.
- New Apps Detected Through Identity Logs: Security teams identify previously unknown tools when users authenticate through Okta.
- Apps Found In Finance Or Expense Data: Subscriptions to platforms such as Airtable or Miro appear in corporate card transactions before IT approval.
- Tools Storing Business Data Without Review: Employees upload project files or internal documentation into new SaaS tools without security assessment.
Monitoring how quickly these tools are discovered and reviewed helps boards understand whether SaaS usage is expanding faster than governance controls can keep up.
3. Where Do Enterprises Struggle When Tracking SaaS Compliance KPIs?
Enterprises struggle to track SaaS compliance KPIs when the data needed to calculate them lives across multiple systems. Access records, SaaS inventories, and user roles are often stored in separate tools.
- User permissions exist in identity platforms like Okta, while application roles are managed inside SaaS tools.
- Security teams may not have a complete list of apps storing company data.
- Teams export logs, permissions, and app lists from multiple systems to build KPI dashboards.
This fragmentation creates operational friction. Even when organizations know which metrics matter, collecting reliable data becomes time-consuming.
- Some systems provide real-time logs while others require manual exports.
- Numbers appear in dashboards without showing which users or apps are driving the risk.
Tracking SaaS compliance KPIs requires connecting identity systems, SaaS applications, and monitoring tools into a single view. Without that integration, reporting becomes slow and incomplete.
4. How Does CloudEagle.ai Help Enterprises Measure SaaS Compliance KPIs?
SaaS compliance is no longer just about passing an annual audit. Enterprises must continuously demonstrate that access is controlled and risky applications are monitored.
Yet most teams still track SaaS compliance KPIs through scattered logs, spreadsheets, and manual reviews that make real metrics difficult to produce.
CloudEagle.ai brings compliance data together into a single system. Security and IT leaders can track measurable indicators across access governance, application usage, and policy enforcement.
A: Access Review Completion Rate
CloudEagle.ai helps enterprises track how consistently teams review and certify user access across applications.
Current Process
Access reviews are conducted manually using spreadsheets and ticketing systems. Managers often receive fragmented information about permissions.
Pain Points
Review cycles stretch across months. Managers may approve access without proper verification, weakening compliance controls.
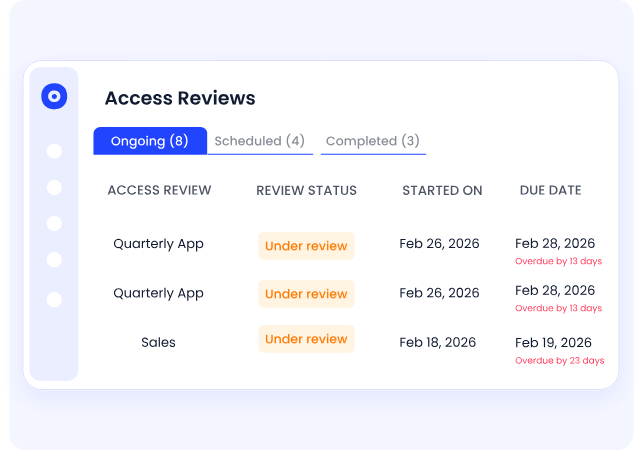
How We Do It
CloudEagle.ai automates user access review workflows and centralizes permissions across applications in one dashboard.
Why We Are Better
Security teams can monitor review completion in real time and identify which departments or reviewers have outstanding certifications.
B: Shadow IT and Unauthorized Application Rate
CloudEagle.ai helps enterprises measure how frequently employees adopt unapproved applications across the SaaS environment.
Current Process
Organizations rely on expense reports or ad hoc audits to identify shadow applications.
Pain Points
Security teams lack visibility into unsanctioned tools, making it difficult to measure compliance gaps.
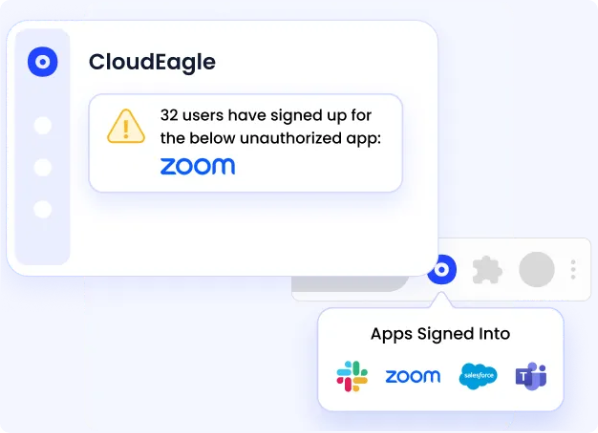
How We Do It
CloudEagle.ai detects shadow IT applications using SSO activity, financial transactions, and browser-level signals.
Why We Are Better
Teams gain a continuously updated inventory of SaaS applications, allowing them to quantify and reduce shadow IT risk.
C: Privileged Access Exposure
CloudEagle.ai allows organizations to track how many users hold privileged permissions across critical SaaS systems.
Current Process
Security teams must manually review admin roles within each application to identify privileged users.
Pain Points
Excessive privileges remain unnoticed between review cycles, increasing both breach and compliance risk.
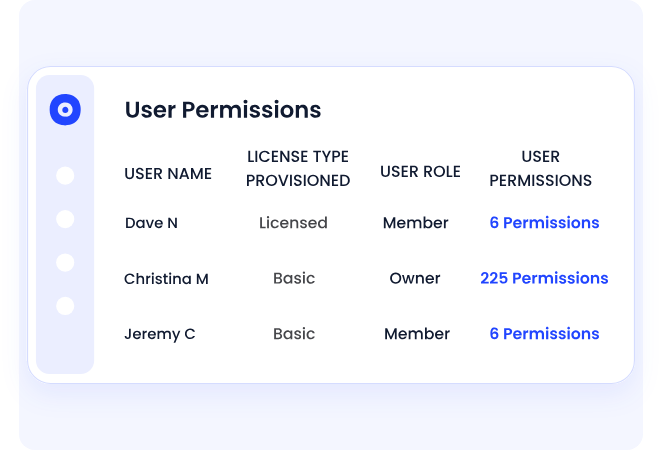
How We Do It
CloudEagle.ai centralizes role and permission data across applications and highlights elevated or over-privileged accounts.
Why We Are Better
Security teams gain continuous visibility into privileged access and can measure how privilege exposure changes over time.
D: Identity Lifecycle Compliance
CloudEagle.ai helps enterprises measure how effectively onboarding and offboarding processes maintain correct access levels.
Current Process
IT manually provisions and deprovisions users across applications when employees join, change roles, or leave.
Pain Points
Access removal may be delayed or incomplete, leaving ex-employees with active accounts.
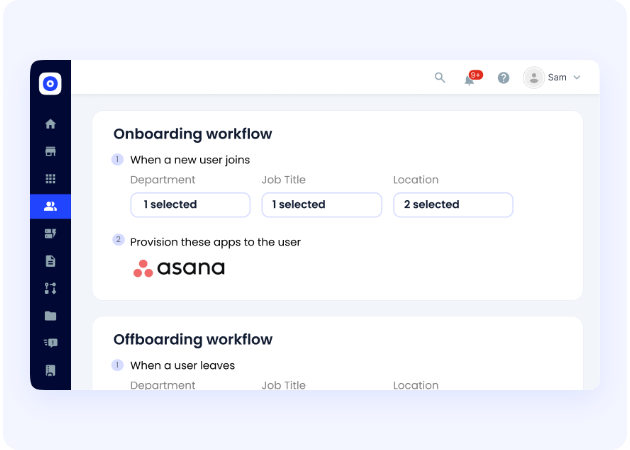
How We Do It
CloudEagle.ai automates onboarding and offboarding workflows using role-based access rules.
Why We Are Better
Security teams can measure how quickly access is provisioned or revoked and ensure identity lifecycle compliance.
5. Conclusion
SaaS compliance KPIs only matter to the board when they translate directly into operational risk. Directors are not looking for lists of controls or audit activities. They want clear answers to their questions.
This is where CloudEagle.ai becomes critical. It helps organizations with SaaS monitoring, monitor user permissions, and surface compliance KPIs from a single platform.
When compliance metrics are grounded in real operational data, they stop being audit artifacts. They become strategic indicators that help leadership understand and manage SaaS risk.
6. FAQs
1. What are good KPIs for a SaaS company?
Good SaaS KPIs measure growth, revenue, and operational health. Common examples include Monthly Recurring Revenue (MRR), customer churn rate, customer acquisition cost (CAC), and customer lifetime value (LTV). For governance, companies also track security metrics like number of privileged users and time to revoke access in SaaS systems.
2. What are KPI metrics for compliance?
Compliance KPIs measure whether security and regulatory controls are actually functioning. Examples include time to revoke user access after offboarding, percentage of users with MFA enabled, number of SaaS apps under compliance monitoring, and rate of shadow IT discovery and remediation.
3. What are the 5 C's of compliance?
The 5 C’s of compliance typically refer to key governance principles: Commitment, Compliance culture, Communication, Controls, and Continuous monitoring. These elements help organizations ensure policies are implemented and maintained over time.
4. What are the 5 pillar SaaS metrics framework?
The five-pillar SaaS metrics framework focuses on growth and retention. It includes acquisition, activation, retention, revenue, and referral. These metrics help companies measure how customers adopt, use, and expand within SaaS products.
5. What are the key metrics of SaaS?
Key SaaS metrics include Monthly Recurring Revenue (MRR), Annual Recurring Revenue (ARR), churn rate, customer acquisition cost (CAC), customer lifetime value (LTV), and average revenue per user (ARPU). These metrics help leadership track financial performance and customer growth.

%201.svg)









.avif)




.avif)
.avif)




.png)





