HIPAA Compliance Checklist for 2025

Manual access reviews are slow, complicated, and prone to mistakes. IT teams spend hours checking spreadsheets, emails, and multiple SaaS apps just to verify user access. This scattered approach increases the risk of over-privileged accounts, compliance gaps, and security issues, which can affect an ITGC audit checklist evaluation.
According to CloudEagle.ai's IGA report, 95% of enterprises still conduct access reviews manually, highlighting a major efficiency and security challenge.
With the rapid growth of SaaS apps and constantly changing employee roles, quarterly or manual access reviews are no longer enough. Automated workflows, continuous monitoring, and AI-driven insights are a must to simplify ITGC audit checklist execution.
TL;DR
- CloudEagle.ai automatically schedules access reviews and sends reminders to reviewers and managers, eliminating manual follow-ups.
- The platform provides a centralized dashboard where all user access and permissions across applications can be viewed, making the ITGC audit checklist process faster and more accurate.
- AI-driven risk detection flags overprivileged, dormant, or inappropriate access, so IT teams focus on the riskiest accounts first.
- Access is intelligently mapped based on user roles, departments, or locations, ensuring permissions align with business responsibilities.
- All review actions are logged and documented automatically, providing audit-ready reports to simplify compliance and regulatory audits.
1. The ITGC Audit Checklist: 7 Steps to Get It Right
In today's digital world, ITGC audits help ensure systems are secure, compliant, and well-governed. Follow this ITGC audit checklist step by step to cover every critical control area.
Step 1: Define Scope and Regulatory Requirements
The first step in any ITGC audit checklist is defining its scope. Organizations need to identify which systems, applications, and departments will be included, and which regulatory frameworks apply, such as SOX, ISO 27001, GDPR, or HIPAA. If SOX is in scope, our breakdown of SOX 302 vs SOX 404 clarifies which section governs executive certification versus internal control assessment.
For example, a finance-focused audit may prioritize ERP systems like SAP or Oracle, while a data privacy audit may focus on cloud storage and HR systems containing personally identifiable information (PII).
Step 2: Identify Critical Systems and Applications
After defining the scope, organizations need to identify the systems and applications that are essential to operations, financial reporting, or regulatory compliance. Systems supporting core business functions or containing sensitive information should be prioritized.
For instance, payroll software, customer relationship management platforms, and cloud storage systems often represent high business impact. By categorizing systems based on risk and criticality, IT teams can allocate resources efficiently and ensure high-risk systems receive a thorough review.
Step 3: Assess User Access and Privilege Levels
User access reviews are a cornerstone of ITGC audits. IT teams must examine who has access to which systems, the type of permissions granted, and whether those permissions align with users' roles. Implementing least privilege principles ensures users only have access required for their job function.
SSO enforcement is the most reliable way to keep those permission boundaries intact at scale; see our comparison of the 8 best single sign-on tools to find the right fit for your stack.
Orphaned accounts or excessive permissions should be flagged and remediated immediately. For example, only finance managers should have approval rights for payments, while general staff should have read-only access. Failing to manage access can lead to internal threats, data misuse, or audit failures.
Know how Treasure Data Enhanced Access Management and Reporting with CloudEagle.ai.
Step 4: Review Change Management Procedures
Auditing change management ensures that all system modifications, such as software updates, configuration changes, or emergency fixes, are properly requested, tested, and approved. Documentation of emergency changes is equally important to prevent unauthorized modifications.
A typical best practice includes maintaining change logs with approvals and testing records. For instance, any upgrade to payroll software should include a change request, testing results, and manager approval before deployment.
Step 5: Evaluate Backup and Disaster Recovery Controls
Enterprises must verify that backup schedules, storage security, and disaster recovery procedures are robust. Regular testing of backup restoration is essential to ensure business continuity.
For example, daily backups of financial data with quarterly restoration drills help mitigate the risk of data loss due to system failures or cyberattacks. An effective backup strategy reduces downtime, limits operational impact, and provides evidence of control for auditors.
Step 6: Verify Incident Response Readiness
ITGC audits also focus on incident response preparedness. Teams must review incident response plans, alerting mechanisms, and escalation protocols to confirm readiness for data breaches or system failures. Employees should be trained to respond promptly to incidents.
For example, if unauthorized access occurs in payroll or HR systems, automatic alerts to IT and management can ensure immediate containment, reducing financial and reputational damage.
Step 7: Document Findings and Prepare Remediation Plans
The final step involves documenting all audit findings, highlighting gaps, and creating actionable remediation plans. Each issue should have a clear owner, timeline, and defined resolution steps.
Maintaining audit-ready documentation is crucial for demonstrating compliance to regulators and internal stakeholders. For instance, orphaned accounts identified during an audit should be deactivated within a defined period, with the actions logged and reported for future review.
2. ITGC Audit Checklist Template (Excel and PDF)
Most teams running their ITGC audit checklist manually rely on spreadsheets to track control areas, evidence collection, and remediation status. A structured template ensures nothing gets missed across the 7 steps above.
A solid ITGC audit checklist template should include:
- Control area (access, change management, backup, incident response, governance)
- Control owner and reviewer name
- Evidence collected (screenshots, logs, policy documents)
- Test result (pass, fail, exception noted)
- Remediation action and deadline
- Sign-off status
Having this in an Excel or PDF format also helps during external audits, as it provides a single source of truth that auditors can reference directly. CloudEagle.ai generates audit-ready reports automatically, so your ITGC audit checklist is always export-ready in the format required.
3. The 4 Control Areas Every ITGC Audit Must Cover
An ITGC audit evaluates an enterprise’s IT controls to ensure data integrity, security, and compliance. It helps identify gaps, prevent unauthorized access, and reduce operational risks.
Robbie Sinclair, Director of Corporate Security, Network Associates, Says:
“Security always feels excessive—until it’s too late.”
Thus, it becomes essential for enterprises to take proactive actions to ensure their IT controls are effective, consistently enforced, and aligned with regulatory requirements, reducing the risk of data breaches, compliance failures, and operational disruptions.
Here are the key areas enterprises must cover during an ITGC audit:
1. Access to Programs and Data
This area ensures that only authorized personnel can access applications, systems, and sensitive data. Auditors review user provisioning, role assignments, periodic access checks, and account deactivation processes.
For example, if a former employee can still approve invoices after leaving the company, it creates compliance and fraud risks. ITGC audits verify that access rights are updated immediately following role changes or departures.
Reports indicate that a significant portion of IT security incidents result from improper user access or excessive privileges. Properly managing access helps reduce fraud, prevent insider threats, and avoid regulatory penalties.
2. Program Development and Change Management
Auditors examine controls around software development and system changes. This includes approvals, testing, version control, and documentation to prevent unauthorized or erroneous changes.
When a company updates its payroll system, a change request must be formally approved, tested in a sandbox environment, and documented before deployment. Unauthorized changes could result in incorrect payments, audit failures, or system downtime.
3. Computer Operations and Backup Controls
This involves reviewing system monitoring, job scheduling, and backup processes. Auditors verify that critical systems run reliably, data is backed up consistently, and recovery procedures are tested regularly.
A manufacturing company relies on ERP systems for production scheduling. If backups are incomplete or restoration procedures fail, downtime can halt operations, leading to significant financial losses.
IDC estimates that unplanned downtime costs businesses $100,000 per hour on average. Effective backup and operational controls mitigate these costs and ensure business continuity.
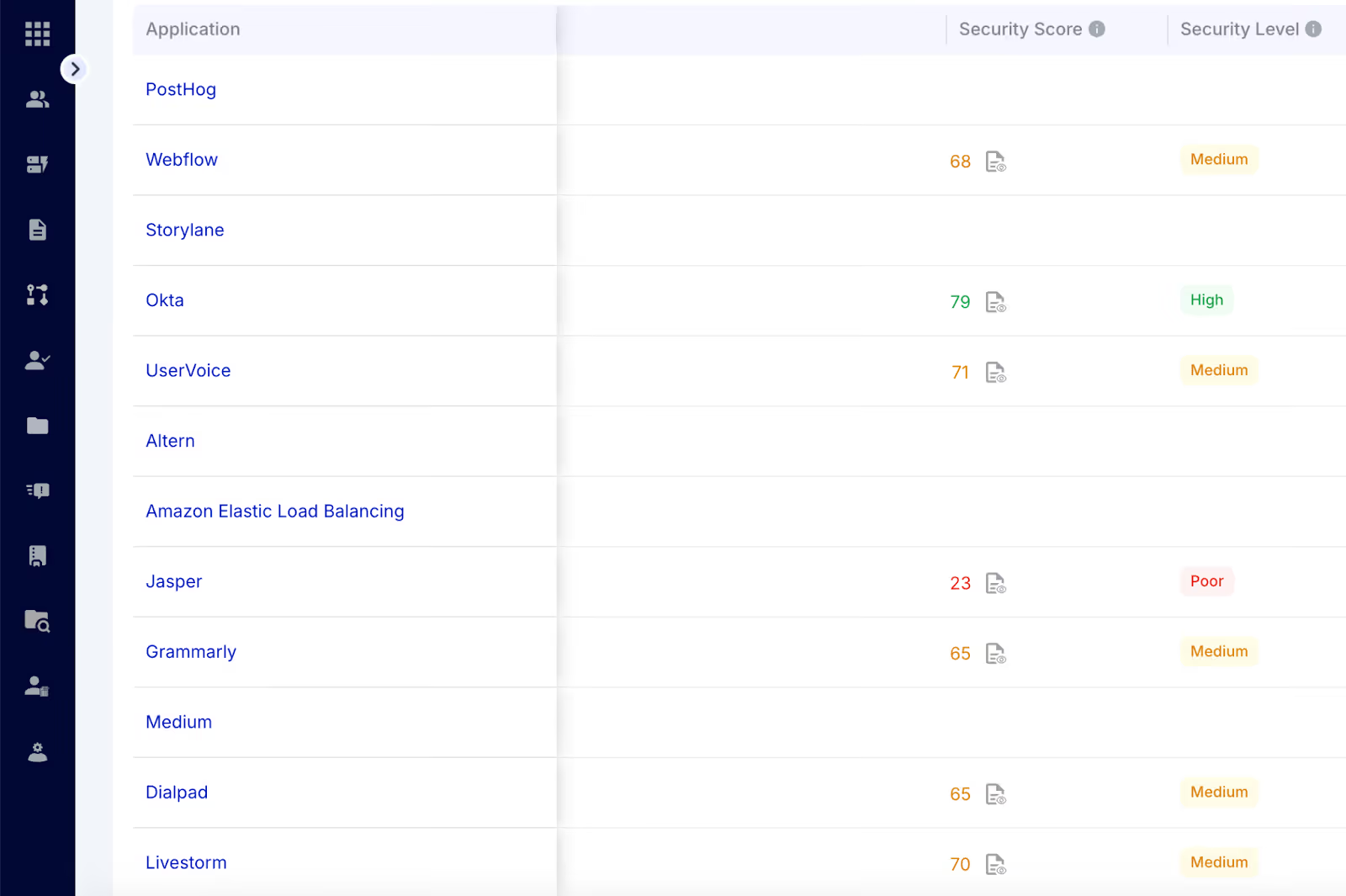
4. Logical and Physical Access Security
Auditors assess both digital and physical security measures. Logical controls include passwords, firewalls, multi-factor authentication, and access logs. Physical controls cover server rooms, data centers, and devices storing sensitive information.
If a server room lacks badge access or surveillance, unauthorized personnel could tamper with critical systems. Similarly, weak passwords or unmonitored administrative accounts increase cybersecurity risks.
A Ponemon Institute report indicates that 52% of data breaches are due to insider threats or compromised credentials. ITGC audits ensure layered security to protect assets.
5. IT Governance and Risk Management
This area evaluates overall IT oversight, policies, and risk management frameworks. Auditors review how the organization identifies, mitigates, and monitors IT risks, aligns IT strategy. For a deeper look at which frameworks apply to your organization, our guide to top 10 IT governance frameworks maps each one to the controls auditors expect.
A company may have documented IT policies but lacks an enforcement mechanism. ITGC audits ensure policies are implemented and monitored, from software approvals to disaster recovery planning.
Organizations with robust IT governance are 50% more likely to successfully pass IT audits and maintain regulatory compliance, according to ISACA research.
4. Why ITGC Audits Are Non-Negotiable in 2026?
5. Common ITGC Audit Challenges and Risks
Conducting ITGC audits can be complex, and organizations often face common challenges and risks that undermine effectiveness, create compliance gaps, and increase operational overhead.
1. Inconsistent Access Control Enforcement
When access policies are applied inconsistently across apps or departments, employees may end up with excessive privileges or access to sensitive data they do not need. Without a unified access control system, IT teams find it hard to keep user permissions accurate.
2. Manual Tracking of Changes and Approvals
Many enterprises still track system changes, user access, and approvals using spreadsheets, emails, or paper logs. This manual method takes a lot of time, often causes mistakes, and can result in missed changes or unauthorized actions.
3. Poor Backup Verification Processes
If backups are not regularly verified or tested, data loss during system failures or cyber incidents becomes a real threat. This increases recovery time and the potential impact of downtime, affecting business continuity.
4. Fragmented System Monitoring
Monitoring multiple IT systems independently can leave gaps in supervision. Security anomalies in one system may go unnoticed if monitoring is siloed, making it hard to detect risks early and respond proactively.
5. Inefficient Incident Response
A lack of clearly defined incident response procedures can delay detection and remediation of security events. Without standardized workflows, IT teams may struggle to respond quickly, increasing downtime and the chance of non-compliance.
6. Shadow IT and Unauthorized Applications
Applications used outside IT's purview (commonly referred to as Shadow IT) pose hidden risks. Unapproved software may introduce security vulnerabilities, create license compliance issues, or lead to data leakage. Finance teams are among the most frequent adopters of unauthorized tools; our roundup of AI tools for finance highlights which platforms include the governance controls that keep them audit-safe.
7. Limited Documentation and Audit Trails
Incomplete logs, missing approvals, or poorly organized system records make audits difficult and stressful. Demonstrating compliance with SOX, GDPR, or ISO standards becomes challenging, raising the risk of penalties and reputational damage.
Stéphane Nappo, Global CISO, Groupe SEB, Says:
“It takes 20 years to build a reputation and a few minutes of a cyber-incident to ruin it.”
6. How CloudEagle.ai Can Help Automate Access Reviews
CloudEagle.ai is a purpose-built SaaS governance platform that simplifies access reviews by automating the entire process. IT teams can quickly see who has access, spot risks, and remove unnecessary permissions; all from a single dashboard. This saves time, reduces errors, and keeps your organization secure and compliant.
Here’s how it automates access reviews:
1. Automated Review Scheduling and Notifications
Managing app access reviews manually is time-consuming and prone to missed deadlines. CloudEagle.ai eliminates this by automatically scheduling access reviews according to your organization’s cadence, whether monthly, quarterly, or continuous.
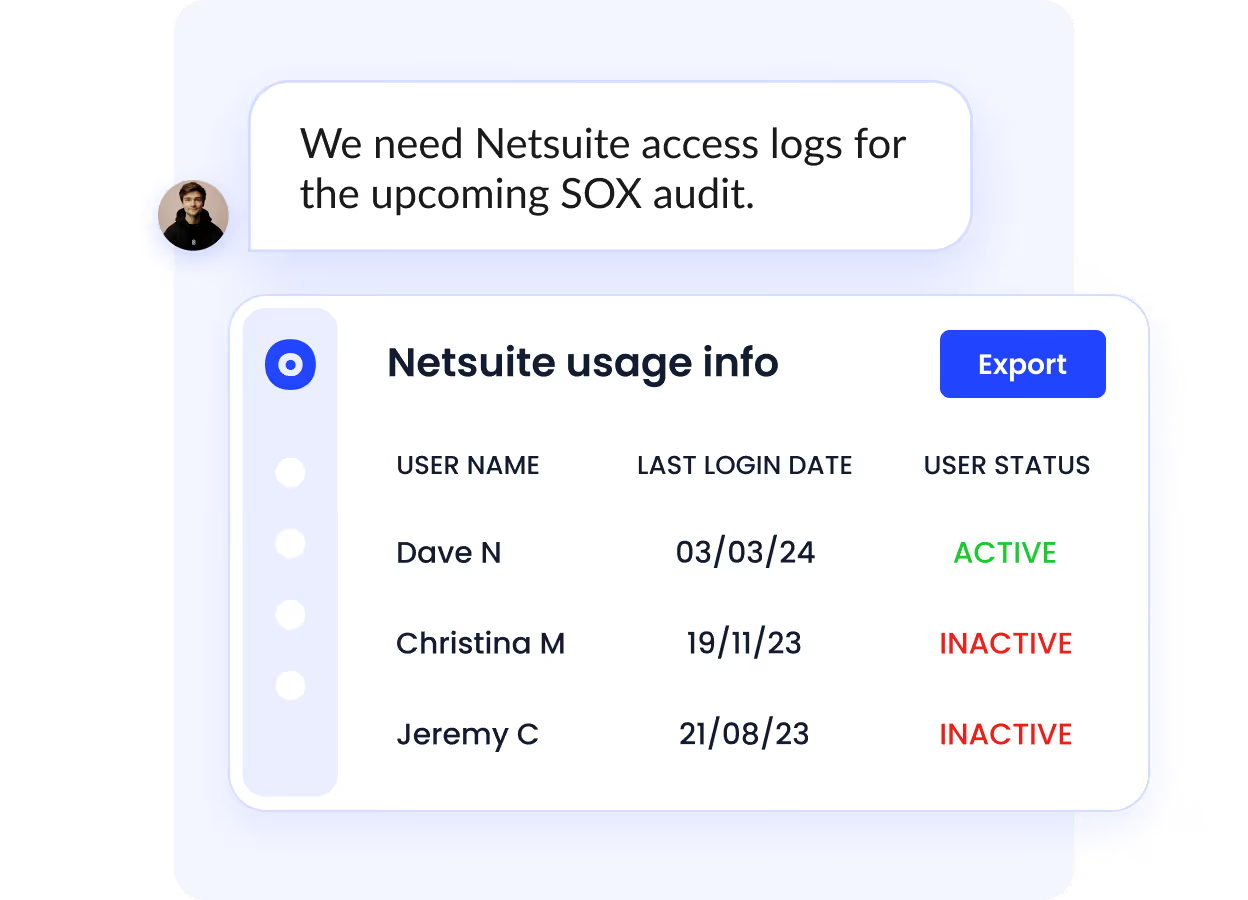
Reviewers and managers receive automated reminders and notifications, ensuring that every review is completed on time. IT teams no longer need to chase approvals or follow up across multiple systems, which saves time and reduces administrative overhead.
Know this inspiring success story of how Dezerv Automated Its App Access Review Process with CloudEagle.ai.
2. Centralized Access Review Dashboard
Instead of logging into dozens of SaaS apps or reconciling spreadsheets, CloudEagle.ai brings all user access data into a single, unified dashboard. IT and security teams can instantly view all permissions, roles, and access rights across every application.
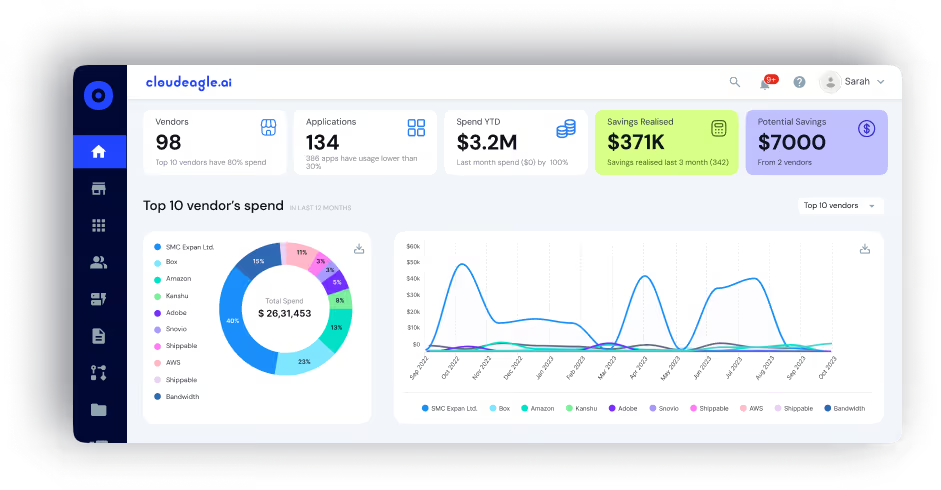
This centralization simplifies the review process, allowing administrators to quickly assess who has access to what, identify unnecessary permissions, and make informed decisions efficiently.
3. AI-Driven Risk Detection
CloudEagle.ai uses AI to identify unusual access patterns, overprivileged users, dormant accounts, or unauthorized permissions. By automatically flagging high-risk users, IT teams can focus on critical issues first, reducing the likelihood of human error and ensuring that risky access is addressed proactively.
4. Role-Based and Contextual Access Mapping
Access is intelligently mapped based on department, job role, or location. CloudEagle.ai ensures that each employee receives permissions aligned with their responsibilities, avoiding over-provisioning and unnecessary access.
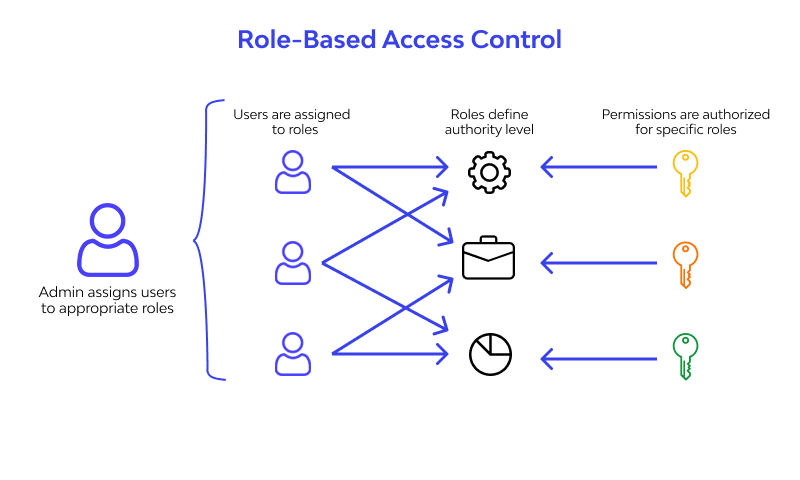
When roles or responsibilities change, access rules can be dynamically updated, ensuring continuous compliance and minimizing security gaps.
5. Automated Deprovisioning of Access
With CloudEagle.ai’s automated deprovisioning workflows, users can be removed from applications they no longer need. When excessive or inappropriate access is detected, the system automatically revokes permissions or routes them through simple approval workflows.
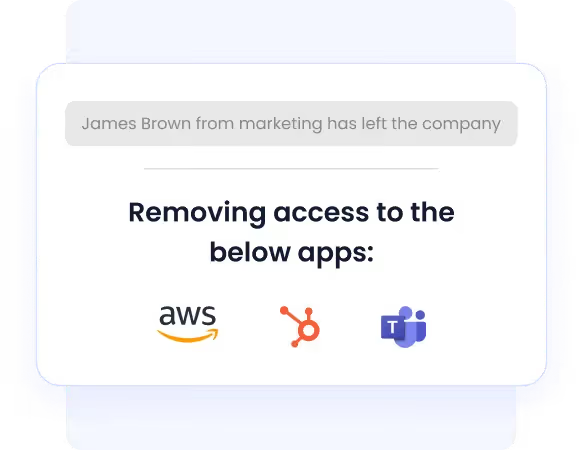
This reduces security risks, prevents human error, and ensures unnecessary access is removed promptly without adding extra work for IT teams.
Discover how RecRoom Automated Employee Offboarding and Saved $200K Annually with CloudEagle.ai.
7. Audit-Ready Reporting and Compliance
Every access review activity is automatically logged, producing detailed, audit-ready reports. Organizations can easily demonstrate compliance with standards like ISO 27001, SOC 2, GDPR, and others. CloudEagle.ai removes the need for hours of manual documentation, helping companies pass audits smoothly while maintaining transparency.
See how CloudEagle.ai made a difference: Alice Park from Remediant shares that the platform streamlined their app access management, saving 1,470 hours annually on onboarding and 1,690 hours on offboarding after implementation.
7. Conclusion
IT General Controls (ITGCs) are the foundation of a secure and compliant IT environment. Proper access management, reliable backups, and continuous monitoring help reduce operational risks, prevent security breaches, and keep organizations compliant.
Using a structured ITGC audit checklist lets companies identify gaps early, take corrective actions, and improve governance across all IT systems. Automation and consistent enforcement make audits faster, enhance decision-making, and lower overall organizational risk.
For enterprises aiming to simplify ITGC management, enhance compliance, and gain real-time visibility, a centralized platform like CloudEagle.ai can automate access reviews, streamline audits, and provide actionable insights, all from a single solution.
Ready to automate access reviews and simplify ITGC management?
Schedule a demo with CloudEagle.ai to see how easy it can be.
8. FAQs
1. How does CloudEagle.ai handle access reviews for applications that are not connected to a corporate identity provider?
CloudEagle.ai uses browser-level signals, expense data, and direct API integrations to discover and review access in apps that sit outside SSO, ensuring no SaaS tool escapes the audit scope.
2. Can CloudEagle.ai scope an ITGC access review campaign to a specific business unit or risk tier instead of running it org-wide?
CloudEagle.ai lets administrators define review campaigns by department, application category, or risk classification, so high-risk systems can be reviewed on a tighter cadence without triggering unnecessary reviews across low-risk tools.
3. How does CloudEagle.ai produce evidence that satisfies an external auditor's sampling requirements for access controls?
Every review action, approval, and revocation is timestamped and stored automatically, giving auditors a complete, exportable record that matches the population they sample without requiring manual reconstruction.
4. What happens in CloudEagle.ai when a reviewer fails to complete an access review before the deadline?
CloudEagle.ai escalates overdue reviews automatically to the reviewer's manager and logs the escalation, ensuring no review window closes without a documented disposition.
5. Does CloudEagle.ai track access changes triggered by role changes mid-period, not just at scheduled review time?
CloudEagle.ai monitors role and department changes in real time through its HR system integrations, triggering an access re-evaluation immediately when a user's job function shifts rather than waiting for the next scheduled review cycle.

%201.svg)









.avif)




.avif)
.avif)




.png)





