HIPAA Compliance Checklist for 2025

Every day, enterprises collect and process massive amounts of personal and sensitive information. From healthcare records to financial data, if mishandled, can cause lasting harm.
Protecting this data is a regulatory and reputational necessity.
Real-world incidents highlight the risks. In 2023, MOVEit’s data breach exposed millions of records across governments and enterprises worldwide.
Events like this show how a single vulnerability can ripple across industries and damage trust instantly.
This article explains 10 essential data privacy frameworks every enterprise should know. You’ll learn what IT governance frameworks are, why they matter, and how aligning with them helps protect both customer data and brand reputation.
TL;DR
- Frameworks provide rules, policies, and practices to securely manage personal and sensitive data across its lifecycle.
- GDPR, CCPA, HIPAA, PCI DSS, ISO/IEC 27001, NIST, SOC 2, FedRAMP, GLBA, and COPPA set global and industry-specific privacy standards.
- They reduce breach risks, ensure regulatory compliance, build customer trust, and improve overall risk management.
- Enterprises face overlapping regulations, high costs, evolving threats, employee awareness gaps, and data mapping difficulties.
- Platforms like CloudEagle.ai centralize oversight, automate audits, enforce access controls, and continuously monitor compliance.
1. Data Privacy Frameworks: The Rulebook Your Legal Team Actually Follows
Data privacy frameworks define how organizations collect, process, store, and delete personal data responsibly.
They combine regulations, policies, and operational controls to ensure transparency, consent, accountability, and regional compliance.
When aligned with an information security framework, they reduce risk exposure and strengthen regulatory readiness across jurisdictions.
A. How Do Data Privacy Frameworks Actually Work?
A data privacy framework governs the full data lifecycle, from collection to secure disposal.
Enterprises first map where personal data lives, then apply encryption, access controls, monitoring, and audit processes to protect it.
Proper consent is always obtained before using personal data for any purpose. Regular audits and assessments of IT compliance frameworks help verify compliance and address SaaS security risks before they cause problems.
B. Why Data Privacy Frameworks Matter More Than Ever?
Data privacy frameworks are essential for protecting people's personal information from misuse or abuse. They help enterprises follow laws like GDPR compliance and avoid costly fines for non-compliance.
The data privacy compliance framework promotes trust by showing responsible data handling to consumers and partners. Here are some reasons why data privacy frameworks are important:
- Protect sensitive data from misuse and unauthorized access
- Align with regulations like GDPR, HIPAA, and CCPA
- Reduce exposure to costly fines and breach penalties
- Build customer trust through transparent data practices
- Strengthen risk management across global operations
2. Data Privacy vs Data Security and Data Governance vs Data Privacy: Who Owns What?
These three terms are frequently conflated, yet each carries a distinct scope, owner, and set of controls. Misaligning them is one of the fastest paths to compliance gaps and audit delays.
Within a privacy governance framework, privacy defines the what and why of data handling, while security delivers the how. Governance sets the operating rules that connect both to the broader data compliance frameworks across the enterprise.
3. How to choose the right data privacy frameworks for your organization?
The right data compliance frameworks depend on whether your primary concern is cost exposure, security risk, or IT workload.
- Jurisdictions: Identify every region where your data flows and confirm which regulations apply, such as GDPR compliance framework requirements for EU data or CCPA for California residents.
- Data classification: Map PII, PHI, and payment data first, since data governance vs data privacy obligations differ significantly by sensitivity level and data type.
- Third-party and vendor exposure: Count how many SaaS tools touch sensitive data, as each integration expands your compliance scope and vendor risk surface.
- Customer procurement requirements: Large enterprise buyers frequently require SOC 2 or ISO 27001 certifications before contract approval, making these data security standards non-negotiable for growth.
- Audit readiness: Prioritize frameworks with clearly defined control evidence requirements to cut access review cycles and avoid last-minute audit scrambles.
- Scalability: Select a privacy governance framework that expands alongside your SaaS ecosystem without demanding a full governance rebuild at every stage.
4. Top 10 Data Privacy Frameworks Every Enterprise Should Know
With dozens of regulations worldwide, knowing which privacy frameworks matter most can feel overwhelming. However, certain standards consistently shape how enterprises safeguard sensitive data and meet SaaS compliance obligations.
Here is the security framework list:
1. General Data Protection Regulation (GDPR)
The General Data Protection Regulation (GDPR), enforced in 2018, is the EU’s landmark privacy law. Unlike older data privacy frameworks, it applies extraterritorially, meaning any enterprise handling EU citizens’ data must comply, regardless of where the enterprise operates.
Why It Matters
GDPR changed the global conversation about privacy. It gave individuals more control over their data and pushed companies to adopt privacy-by-design practices.
For multinational enterprises, this information security framework sets a new benchmark that influences U.S. laws like CCPA and Brazil’s LGPD.
Core Components
- Lawful Processing: Enterprises must demonstrate a clear legal basis, such as consent or contractual necessity, before handling personal data.
- Expanded User Rights: Data subjects can access, rectify, port, or erase their data, forcing businesses to maintain transparent processes.
- Breach Notification: Enterprises must disclose common causes of data breaches within 72 hours, encouraging faster detection and stronger incident response.
- Privacy by Design: Enterprises are required to embed data protection into technology and processes from the ground up.
- Oversight and Accountability: Some Enterprises must appoint Data Protection Officers (DPOs) to oversee compliance efforts.
Consequences of Non-Compliance
Violations can lead to fines of up to €20 million or 4% of annual global turnover. In 2021, Amazon faced a €746 million fine under GDPR for inadequate consent practices.
As Margrethe Vestager, Executive Vice President of the European Commission, emphasized:
“Privacy is not a luxury, but a fundamental right.”
2. California Consumer Privacy Act (CCPA)
The California Consumer Privacy Act (CCPA), enacted in 2018, is one of the strongest data privacy frameworks in the United States. It grants California residents greater control over their personal information and imposes clear obligations on businesses.
Why It Matters
CCPA set the tone for privacy legislation across the U.S., influencing laws in other states. For enterprises, this data privacy compliance framework highlights the shift toward customer-centric privacy practices and creates operational models that may soon become nationwide standards.
Core Components
- Consumer Rights: Enterprises can know what data is collected, request deletion, and opt out of data sales.
- Business Obligations: Enterprises must disclose data practices, update privacy policies, and provide easy opt-out mechanisms.
- Coverage Thresholds: Applies to enterprises meeting criteria like $25 million in revenue or handling 50,000+ records.
- Non-Discrimination: Enterprises cannot penalize consumers for exercising their privacy rights.
- Transparency Requirements: Privacy notices must be clear, accessible, and updated regularly.
Consequences of Non-Compliance
Penalties include fines of up to $7,500 per intentional violation and $2,500 per unintentional violation. Beyond financial costs, non-compliance damages brand trust, especially in a state that leads U.S. privacy conversations, something which compliance risk management cannot rebuild.
3. Health Insurance Portability and Accountability Act (HIPAA)
The Health Insurance Portability and Accountability Act (HIPAA), enacted in 1996, is the primary U.S. law governing healthcare data privacy. This data privacy framework applies to healthcare providers, insurers, and their business associates handling protected health information (PHI).
Why It Matters
HIPAA ensures that sensitive health data remains confidential while still allowing necessary information sharing for patient care. Unlike other data privacy frameworks, it balances the need for security with the practical demands of healthcare operations.
Core Components
- Privacy Rule: Defines standards for safeguarding medical records and patient identifiers.
- Security Rule: Requires administrative, technical, and physical safeguards to protect electronic PHI.
- Breach Notification Rule: HIPAA compliance audit mandates timely disclosure to affected individuals and regulators after data breaches.
- Minimum Necessary Standard: Enterprises must limit data use and disclosure to what is essential.
- Business Associate Agreements: Contracts must ensure third parties follow HIPAA requirements.
Consequences of Non-Compliance
Penalties range from $100 to $50,000 per violation, capped at $1.5 million annually. Non-compliance may also result in legal action and permanent damage to patient trust. HIPAA Journal revealed that 725 data breaches took place in 2023.
4. Payment Card Industry Data Security Standard (PCI DSS)
PCI DSS is a global standard developed by major card brands to secure cardholder data. This data security framework applies to any enterprise that stores, processes, or transmits payment card information.
Why It Matters
With billions of transactions occurring daily, PCI DSS assessment is one of the most common data privacy frameworks that reduces the risk of card fraud and identity theft.
Core Components
- Secure Network: Firewalls and encryption to protect payment data.
- Access Control: Restricting cardholder data to authorized personnel.
- Monitoring and Testing: Regular system scans, penetration tests, and activity logging.
- Information Security Policy: Formalized policies to guide staff and vendors.
- Vulnerability Management: Ongoing updates and patch management to minimize risks.
Consequences of Non-Compliance
Organizations can face fines of $5,000 to $100,000 per month from payment brands.
5. ISO/IEC 27001 for Information Security
ISO/IEC 27001 is the global standard for information security, structured around establishing, implementing, and continually improving an Information Security Management System (ISMS). This is one of the most important data privacy frameworks enterprises should comply with.
Why It Matters
Achieving certification demonstrates to clients, partners, and regulators that your enterprise operates under rigorous access governance. It’s a foundation for trust building and supports international regulatory alignment.
Core Components
- Risk Assessment & Treatment: Continuously identify, evaluate, and mitigate risks to information assets.
- Comprehensive Controls: Implement 114 controls across security domains like access management, encryption, and incident response.
- Continuous Improvement Cycle: Plan–Do–Check–Act (PDCA) framework ensures ongoing policy, control, and performance enhancement.
- Leadership Commitment: Top management must endorse security strategies and allocate resources for effective ISMS operations.
Consequences of Non-Compliance
Beyond immediate breach costs, this incident led to remediation expenses, lost client contracts, and long-term erosion of trust. For example, despite having ISO 27001 in place, Capita suffered a major breach in 2025, after a ransomware attack exploited an unpatched Exchange server.
6. NIST Privacy Framework
The NIST Privacy Framework is a voluntary tool developed to help enterprises manage privacy risks through structured processes. Like other data privacy frameworks, this is also essential.
Why It Matters
It provides enterprises with a scalable model to identify, assess, and reduce SaaS security risks. This framework aligns with global regulations while offering flexibility for organizations across industries.
Core Components
- Identify-P: Understand data processing activities, systems, and potential privacy risks.
- Govern-P: Define organizational governance structures and responsibilities for privacy management.
- Control-P: Implement technical and procedural controls to manage personal data use.
- Communicate-P: Ensure transparency with stakeholders through policies, notices, and disclosures.
- Protect-P: Safeguard data with measures to minimize unauthorized use or exposure.
Consequences of Non-Compliance
Enterprises failing to use NIST’s model may face unchecked privacy risks, misaligned policies, and reduced regulatory readiness. This can erode customer confidence and increase exposure to enforcement actions.
7. SOC 2 Privacy Trust Principle
The SOC 2 Privacy Trust Principle is part of the SOC 2 framework. This data privacy compliance framework focuses on how enterprises handle personal data responsibly.
Why It Matters
It ensures that enterprises follow strict protocols for the collection, use, retention, and disposal of personal data. Customers and auditors of these data privacy frameworks often look to SOC 2 certification as a mark of trust and reliability.
Core Components
- Notice and Consent: Informing users about data use and obtaining their approval.
- Collection and Use: Limiting data gathering to relevant purposes and authorized needs.
- Retention and Disposal: Keeping data only as long as necessary and disposing of it securely.
- Access and Correction: Allowing individuals to review and correct their information.
- Security and Monitoring: Protecting personal data through safeguards and continuous monitoring.
As Satya Nadella, CEO of Microsoft, once said:
“Privacy is a human right. We have to treat it that way.”
Consequences of Non-Compliance
Ignoring the SOC 2 data security framework can lead to customer distrust, legal scrutiny, and significant business reputation damage.
8. Federal Risk and Authorization Management Program (FedRAMP)
FedRAMP is a U.S. government program that standardizes security assessments for cloud services used by federal agencies. This is one of the hardest data privacy frameworks to comply with in the first place.
Why It Matters
This data privacy compliance framework ensures that government data hosted in the cloud is protected with consistent, rigorous, and approved security controls.
Core Components
- Baseline Security Controls: Standardized requirements based on NIST guidelines.
- Assessment and Authorization: Independent audits for cloud providers seeking government use.
- Continuous Monitoring: Ongoing security checks to maintain authorization status.
- Documentation: Detailed security packages for transparency and trust.
Consequences of Non-Compliance
Failure to meet the FedRAMP information security framework blocks providers from serving federal agencies and risks contract loss.
9. Gramm-Leach-Bliley Act (GLBA)
GLBA, also known as the Financial Services Modernization Act, requires U.S. financial institutions to protect consumer data privacy.
Why It Matters
These IT compliance frameworks ensure banks, lenders, and insurance firms safeguard sensitive financial information and explain their data-sharing practices.
Core Components
- Privacy Rule: Requires institutions to disclose how customer data is collected and shared.
- Safeguards Rule: Mandates security measures to protect against unauthorized access or data breaches.
- Pretexting Provisions: Prevents fraudulent access to private financial records.
Consequences of Non-Compliance
Violations can lead to heavy fines, legal penalties, reputational harm, and customer trust erosion. In 2022, the FTC fined mortgage broker Mortgage Solutions for failing GLBA compliance after sensitive loan documents were exposed online.
10. Children’s Online Privacy Protection Act (COPPA)
COPPA, enacted in 1998, is a U.S. law designed to protect children under 13 online. It governs how businesses, websites, and apps handle personal information when kids use their services.
Why It Matters
With the rise of gaming apps, social media, and learning platforms, children’s data is more exposed than ever. COPPA ensures enterprises prioritize safety and transparency before collecting or processing that information.
Core Components
- Parental Consent: Websites and apps must obtain verifiable parental permission before gathering data from children.
- Privacy Notices: Businesses must display clear and accessible privacy policies detailing data practices for minors.
- Data Minimization: Companies are restricted from collecting unnecessary data, limiting use strictly to intended services.
- Advertising Restrictions: Behavioral ads targeting children under 13 are strictly regulated to prevent exploitation.
Consequences of Non-Compliance
Failing to follow COPPA can lead to hefty fines and legal scrutiny. For example, in 2019, Google and YouTube were fined $170 million by the FTC for illegally collecting children’s data without parental consent, highlighting the serious risks of ignoring compliance.
5. How CloudEagle.ai Can Secure Data and Compliance?
CloudEagle.ai is a SaaS procurement and management platform that helps organizations efficiently track, optimize, manage, and renew SaaS licenses.
With CloudEagle.ai, you can identify risks, enforce security policies, and generate audit-ready reports with ease. Here’s how the platform supports data privacy frameworks compliance.
Centralized Compliance Oversight
Non-compliance with data privacy frameworks often leads to expensive fines and legal issues, but CloudEagle.ai helps prevent this by maintaining continuous compliance. Real-time alerts highlight violations early, allowing you to act before penalties occur.
The platform centralizes compliance by monitoring user activity, tracking app access, and maintaining comprehensive records. This simplifies oversight, reduces complexity, and enhances operational efficiency.
With built-in coverage for information security compliance frameworks like SOC 2, ISO 27001, and GDPR compliance, CloudEagle.ai streamlines access control, monitoring, and auditing. This removes the need for multiple tools, making compliance simpler and more effective.
Data Encryption and Protection
CloudEagle.ai ensures that sensitive data is encrypted during transit and while stored, adhering to the rigorous standards of ISO 27001 and HIPAA. This SaaS security measure helps protect against unauthorized access and keeps your data secure at every stage.

Automated Compliance Reporting
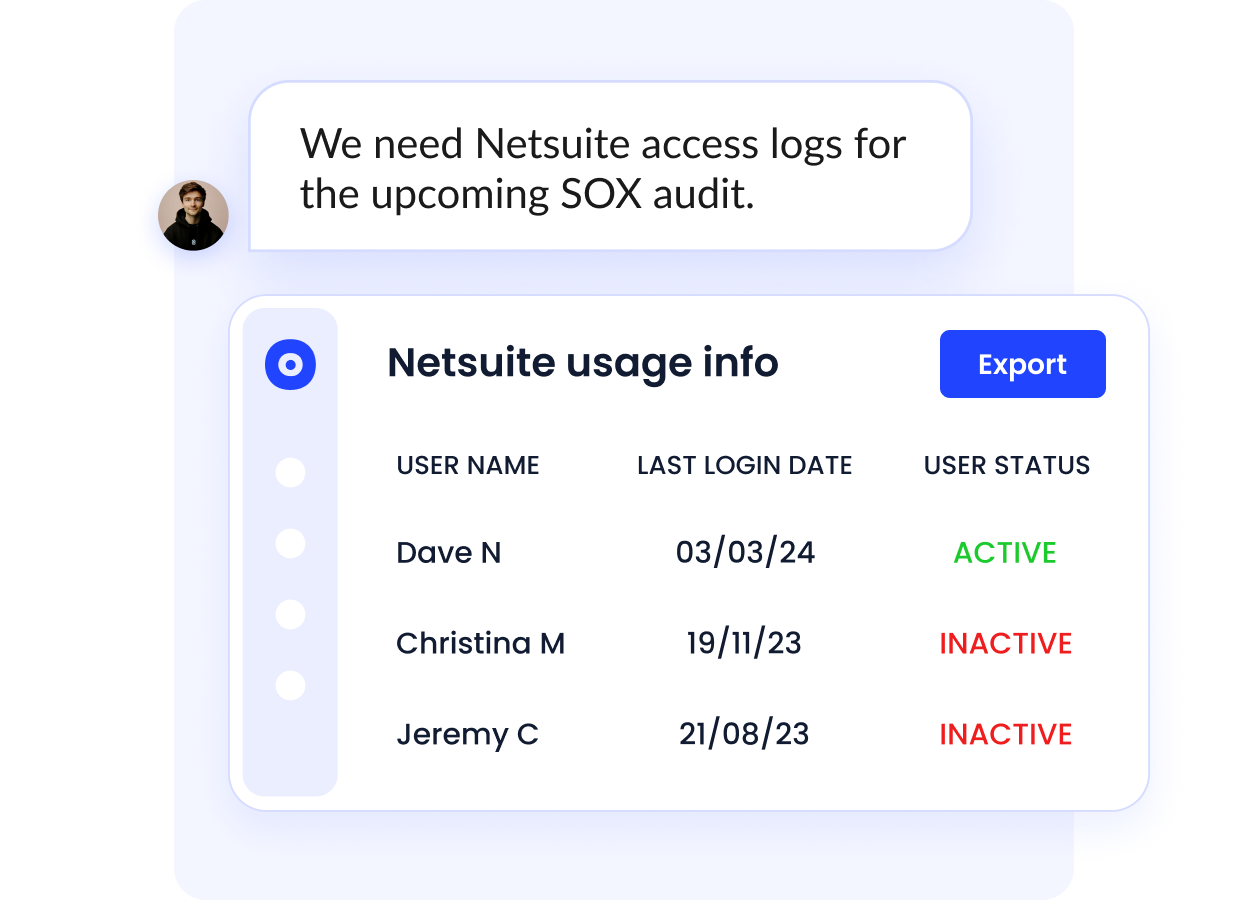
Manual compliance reporting in data privacy frameworks is resource-heavy, but CloudEagle.ai automates the process, ensuring audit-ready reports are always available. This saves time while minimizing manual work.
Its real-time audit logs deliver full visibility into access and usage, enabling swift detection and resolution of compliance concerns.
Continuous Monitoring and Risk Mitigation
CloudEagle.ai provides ongoing monitoring of identity and access management and data transactions to ensure controls stay effective. This helps organizations detect and fix security gaps before they escalate.
The platform also identifies compliance gaps early, providing actionable insights that strengthen security and reduce risks proactively.
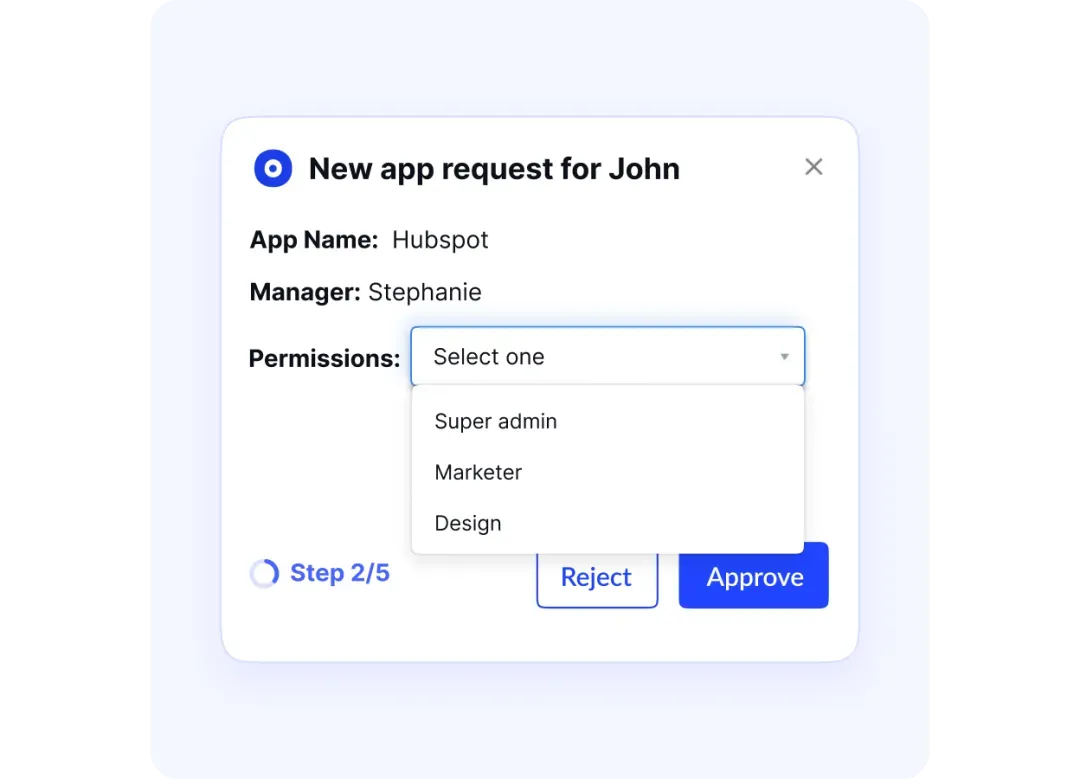
Automated Access Reviews
Regulations such as SOC 2 and ISO 27001 mandate periodic access reviews, which can be tedious without automation. CloudEagle.ai streamlines data privacy frameworks by continuously focusing on app access reviews, ensuring only authorized personnel can reach sensitive data.
By automating reviews, the platform cuts down manual work, reduces compliance risks, and ensures stronger regulatory alignment.
Detailed Audit Trails
Maintaining audit trails is essential for SOC 2 and ISO 27001 compliance. CloudEagle.ai captures all system activity, preserving data integrity and making audit evidence retrieval simple.
The platform also enforces security policies aligned with SOC 2, ISO 27001, and GDPR, while allowing customizations to meet unique compliance needs. This ensures ongoing adherence with evolving regulations.
6. Data Privacy Frameworks by Industry: Are You Using the Right One?
Matching the right framework to the right environment eliminates scope confusion before cross-functional teams lose time debating jurisdiction or data type.
- SaaS Vendors (PII): SOC 2 and ISO/IEC 27001 are the baseline data security standards enterprise buyers expect. GDPR compliance framework obligations also apply when serving EU customers or processing their personal data.
- Healthcare (PHI): HIPAA governs all protected health information across providers, insurers, and their business associates. ISO 27001 supplements it with broader organizational security controls.
- Finance (Financial PII): GLBA mandates consumer data safeguards for U.S. banks, lenders, and insurance firms. PCI DSS applies to any environment where payment card data is stored or processed.
- E-commerce (Payment and Children's Data): PCI DSS covers cardholder transaction data across retail and online platforms. COPPA becomes a mandatory data compliance framework for any service with users under 13.
- Public Sector (Government Data): FedRAMP authorization is required for cloud providers serving U.S. federal agencies. NIST provides the underlying privacy governance framework and control baseline that FedRAMP builds upon.
7. Key Components of a Data Privacy Governance Framework: What Are You Missing?
A robust privacy governance framework translates data compliance frameworks from policy documents into operational controls that teams can audit and enforce daily.
- Data Inventory and Mapping: Catalog every data asset, including where personal data lives, who accesses it, and how it flows across SaaS tools.
- Lawful Basis and Consent: Document the legal ground for each processing activity under your gdpr compliance framework before data collection begins.
- Retention and Deletion: Define schedules for how long data is kept and enforce automated deletion to reduce exposure.
- Data Protection Impact Assessments (DPIAs): Conduct risk assessments before launching new products or high-risk processing activities.
- Vendor and Third Party Risk: Evaluate supplier data security standards contractually and through ongoing monitoring, not just at onboarding.
- Access Controls: Enforce least privilege using feature-level usage signals rather than superficial login timestamps, so access decisions reflect actual need.
- Incident Response: Maintain a tested breach notification plan with defined escalation paths and regulatory timelines.
- Training and Awareness: Run role-specific training so employees understand their obligations under your privacy governance framework.
- Audit Evidence: Capture immutable logs and deprovisioning records that auditors can verify quickly.
- Metrics and KPIs: Track review cycle time, open access exceptions, and policy violations to demonstrate continuous improvement.
8. Data Privacy Compliance Framework Challenges Enterprises Face
Even well-designed data privacy frameworks are difficult to operationalize at scale. Changing regulations, expanding SaaS stacks, and evolving threats increase compliance pressure across teams.
- Regulatory Overlaps: Aligning GDPR, CCPA, HIPAA, and other data compliance frameworks across regions increases complexity and audit strain.
- High Implementation Costs: Tools, certifications, training, and audits require sustained investment and coordination.
- Evolving Threat Landscape: A static data security framework cannot address emerging vulnerabilities without continuous monitoring.
- Employee Awareness Gaps: Mismanaged access and inconsistent training often lead to preventable compliance failures.
- Data Mapping Complexity: Limited visibility into where sensitive data resides weakens documentation and audit readiness.
9. Best Data Privacy Management Software: What Should It Automate?
The best data privacy management software should not just “support compliance.” It should remove manual effort from your data privacy frameworks, enforce your gdpr compliance framework, and operationalize your privacy governance framework automatically.
- Automated Evidence Capture: The platform should log proof of every control action in real time, eliminating manual evidence collection before audits.
- Continuous Monitoring: Static snapshots miss drift between audits; look for tools that enforce data security standards around the clock across all connected SaaS apps.
- Slack-First Workflow Approvals: Access requests and policy exceptions should route directly to where users already work, cutting approval delays without additional portals.
- A privacy governance framework requires periodic reviews; software must complete them in days, not months, with deprovisioning proof attached automatically.
- Retention and Deletion Enforcement: Tools should trigger data deletion workflows based on defined schedules, not rely on manual reminders.
- Vendor Risk Tracking: Third-party exposure is a leading gap in data governance vs data privacy programs; automated vendor assessments keep obligations current.
- Immutable Audit Trails: Every access event must be timestamped and tamper-proof to satisfy GDPR compliance framework requirements and auditor expectations.
The best data privacy management software does not just help you document controls.
It helps you enforce them consistently, prove them instantly, and scale them without multiplying headcount.
10. What are security compliance frameworks?
- Laws vs. frameworks: Laws define obligations; data compliance frameworks specify the controls and documented procedures used to satisfy them in practice.
- Policies vs. frameworks: Internal policies express intent; frameworks produce independently verifiable evidence that auditors and third parties can assess.
- Third-party assurance: Standards such as SOC 2 and the GDPR compliance framework serve as trust signals in procurement, accelerating vendor approvals and reducing review scope.
- Ownership consolidation: Adopting a shared framework assigns clear control of ownership, eliminating fragmented accountability and compressing audit cycle time significantly.
Conclusion
Data privacy frameworks are the backbone of trust, compliance, and resilience in a digital-first world. By understanding their importance and addressing common challenges, enterprises can better protect sensitive data and maintain customer confidence.
To simplify compliance and strengthen your data security posture, consider exploring modern solutions tailored for enterprises.
CloudEagle.ai can help streamline compliance management and reduce risk across your SaaS ecosystem.
FAQs
1. What is the difference between GDPR and a privacy framework?
GDPR is a legal regulation focused on EU citizens’ data rights. Privacy frameworks provide structured guidance to implement security and compliance measures across organizations.
2. What is the difference between SCC and a data privacy framework?
Standard Contractual Clauses (SCC) are legal tools for transferring data internationally. Privacy frameworks are broader programs guiding overall data protection policies and practices.
3. What is an example of data compliance?
An example is a company following GDPR by obtaining user consent, securing personal data, and documenting access procedures.
4. What is the best data privacy certification?
ISO/IEC 27701 is widely recognized, providing guidance for implementing a privacy information management system aligned with GDPR and global regulations.
5. What are the three types of data security?
The three types are: physical security (protecting hardware), technical security (encryption, firewalls), and administrative security (policies, training, audits).

%201.svg)









.avif)




.avif)
.avif)




.png)





