HIPAA Compliance Checklist for 2025

Every access decision your organization makes, whether assigning a role in Microsoft Teams, managing permissions in Salesforce, or syncing accounts across cloud apps, either strengthens or weakens your security posture.
The surge in SaaS tools, remote workforces, and cloud infrastructure has compelled organizations to reassess their approach to managing access and protecting data.
As cyberattacks become increasingly sophisticated and internal governance becomes more complex, the choice between centralized and decentralized access management can significantly impact compliance, scalability, and control.
This guide breaks down both models side by side across multiple dimensions and helps you identify the right fit for your organization.
TL;DR
1. What Is Centralized Access Management?
Centralized access management is a security model that manages user identities and permissions from a single, unified system. It simplifies administration, improves visibility, and strengthens security, especially for organizations managing a large number of digital tools and resources.
This model provides consistent rules and controls across your ecosystem, making it easier to enforce compliance and reduce risks from over-provisioned or outdated access.
Key characteristics of centralized access management:
- Single point of control over all access decisions and permissions
- Easier enforcement of company-wide policies and compliance standards
- Simplified onboarding and offboarding processes tied to a central system
- Enhanced visibility into user activities, access logs, and anomalies
- Best suited for large enterprises or regulated industries like finance and healthcare
In the context of centralized vs decentralized access management, centralized systems offer better visibility and audit readiness, making them the preferred choice for organizations with strict compliance obligations.
2. What Is Decentralized Access Management?
Decentralized access management is a security model where access decisions are handled independently by various teams or systems without a central authority. This distributed approach increases flexibility, enhances resilience, and reduces the risks tied to a single point of failure.
Decentralized identity and access management aligns with modern DevOps and product-led cultures where speed and autonomy matter. Teams can quickly grant or revoke access based on operational needs without waiting for central IT approval.
However, it also increases the complexity of governance. Without a central view, it becomes harder to detect anomalies, enforce consistent policies, or prove compliance during audits.
Key characteristics of decentralized access management:
- Teams and departments manage access independently based on local needs
- Increases speed and flexibility in access provisioning across the organization
- Encourages autonomy but can lead to inconsistent policy enforcement
- Limited centralized visibility increases security and compliance risk
- Ideal for fast-moving startups or distributed engineering teams
3. Why the Centralized vs Decentralized Access Management Debate Is Getting More Complex?
The debate around centralized vs decentralized access management used to be straightforward. Large enterprises centralized. Startups decentralized. That boundary no longer holds.
Three forces are making this decision significantly harder in 2026:
- SaaS sprawl has fragmented access across dozens of systems: The average enterprise now runs 130+ SaaS applications. Each one has its own permission model, admin console, and access lifecycle. Centralized oversight that does not extend to all of these tools creates blind spots as large as the gaps it is trying to close.
- Remote and hybrid work has dissolved the traditional perimeter: Access decisions that used to happen inside a corporate network now happen across home connections, personal devices, and unmanaged cloud apps. Neither purely centralized nor purely decentralized models were designed for this environment.
- Regulatory pressure is increasing on both fronts: GDPR, HIPAA, SOC 2, DORA, and the EU AI Act all require continuous evidence of access governance. Centralized models make this easier to demonstrate. But they also create bottlenecks that push teams toward workarounds, which is exactly the shadow IT and access sprawl problem that auditors flag.
4. Centralized vs Decentralized Access Management: Key Differences
Centralized access management uses one central system to control access to all resources. Decentralized access management spreads control across multiple systems or teams. The core difference is where authority resides and how user credentials are managed and enforced.
Control and Oversight
Centralized systems give IT full visibility and control over user access, reducing blind spots and unauthorized permissions. Decentralized access management distributes control across teams, which can empower productivity but also leads to outdated or excessive permissions accumulating over time.
Policy Enforcement and Consistency
Centralized access management enforces uniform security policies like MFA or password updates across all systems simultaneously. Decentralized setups often result in inconsistent enforcement, with some teams applying stricter standards than others, creating potential security loopholes that compound during audits.
Scalability and Flexibility
Decentralized systems offer better flexibility and scale easily as teams adopt their own tools and processes. However, without centralized oversight, data governance becomes complex, prompting many organizations to adopt hybrid approaches that balance both.
Security Posture and Risks
Centralized access control provides a stronger defense through centralized logging, audits, and better anomaly detection. Decentralized identity and access management can increase the attack surface due to scattered access points, stale credentials, and limited visibility across the environment.
Compliance and Audit Readiness
Centralized systems simplify compliance by unifying logs and roles, making audits like SOC 2 or HIPAA significantly easier. Decentralized environments demand more manual effort to prove compliance and track access across fragmented systems.
5. How to Choose Between Centralized and Decentralized Access Management?
The right model should align with your organization's size, complexity, compliance requirements, and internal capabilities. There is no universal answer in the centralized vs decentralized access management debate, but there are clear signals that point toward the right direction.
When centralized access management works best:
- Large financial institutions needing strict access governance across Salesforce, AWS, and internal CRMs
- Healthcare networks managing patient data across multiple hospitals and third-party systems for HIPAA compliance
- Enterprises with global operations where centralized oversight ensures compliance with local and international regulations
- Government agencies require uniform identity verification with reduced insider threat exposure
When decentralized identity and access management works best:
- Startups using tools like GitHub, Slack, and Notion, where product teams manage access independently to iterate faster
- Engineering-driven companies where developers need autonomy to provision cloud resources or test environments
- Companies with distributed teams across time zones, allowing local leads to manage access based on immediate operational needs
- Innovation labs within enterprises that need a flexible, experimentation-friendly access environment
The hybrid approach: best of both worlds
Many organizations find themselves between two extremes, wanting the control of centralization with the flexibility of decentralization. Hybrid IAM models allow central IT to define policies while giving teams local autonomy for day-to-day access management.
Benefits of hybrid models:
- Central policy engines with decentralized execution points
- Centralized visibility with team-level provisioning autonomy
- Ideal for companies scaling rapidly, entering new regions, or managing both cloud-native and legacy systems
- Preferred approach for M&A scenarios where multiple access environments need unified governance
6. How CloudEagle.ai Supports Modern Access Management?
CloudEagle.ai is your strategic partner in streamlining identity and access management through automation, visibility, and control. Whether you are running centralized access management or exploring hybrid strategies, CloudEagle.ai helps you manage access consistently, securely, and efficiently.
Centralized Control With a Unified Dashboard
CloudEagle provides a centralized dashboard where IT admins can manage all users, roles, and permissions across applications, track who has access to what and why, and streamline provisioning and deprovisioning workflows at scale.
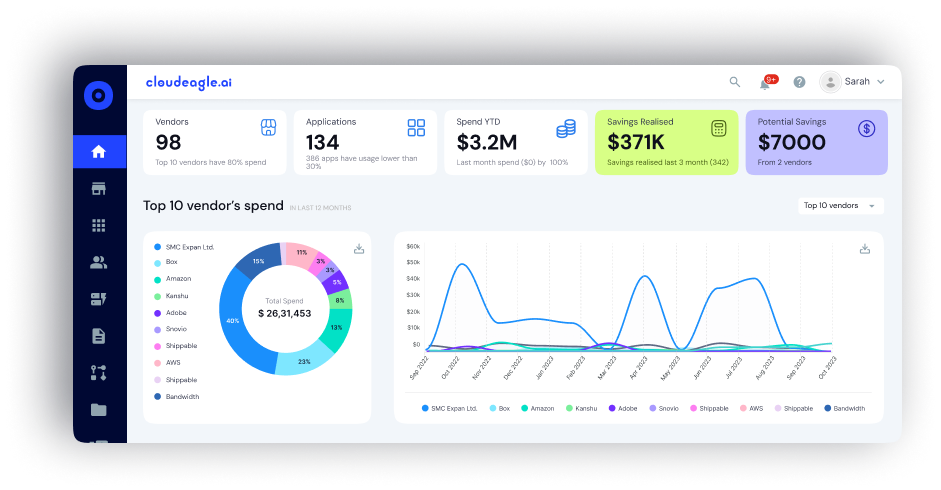
How it helps:
- Gives complete visibility across your entire SaaS environment in one place
- Supports organizations debating centralized vs decentralized access management by providing tighter oversight without slowing operations
- Connects with over 500 integrations across HRIS, SSO, and financial systems for end-to-end control
Self-Service App Catalog
CloudEagle strikes a balance between control and autonomy with its self-service app catalog, addressing the core tension in centralized vs decentralized access management.
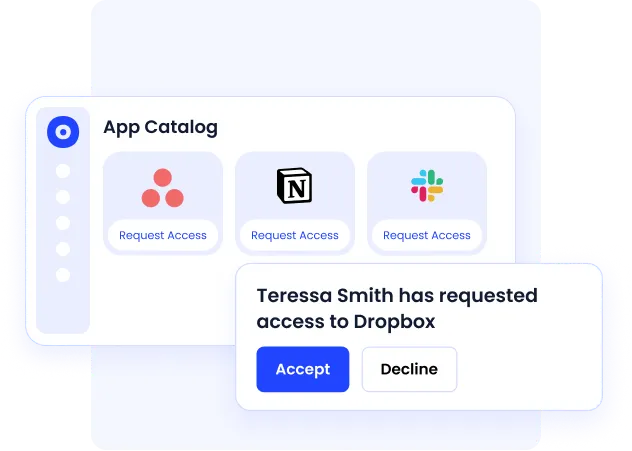
How it helps:
- Employees request access to apps directly through Slack without IT bottlenecks
- Admins receive real-time notifications via Slack or email for timely approvals
- The platform flags duplicate app requests and suggests available alternatives automatically
- Reduces procurement redundancy while keeping IT in the loop on every request
Automated App Access Reviews
How it helps:
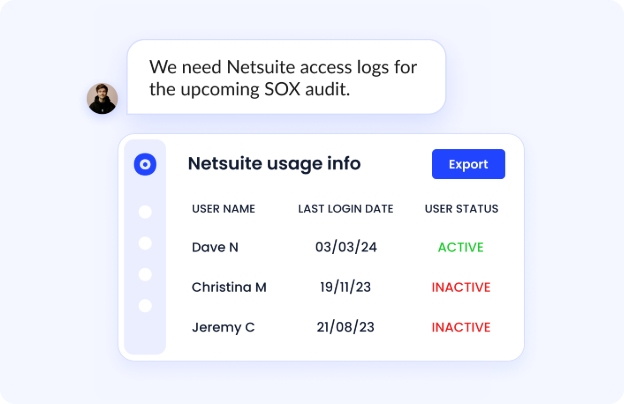
- Automates SOC 2 and ISO 27001 access audits without manual evidence collection
- Centralizes all access review tools in one dashboard for compliance teams
- Provides instant deprovisioning logs when needed for forensic or audit purposes
- Ensures every access decision is verifiable, trackable, and compliant
Just-in-Time Access Management
How it helps:
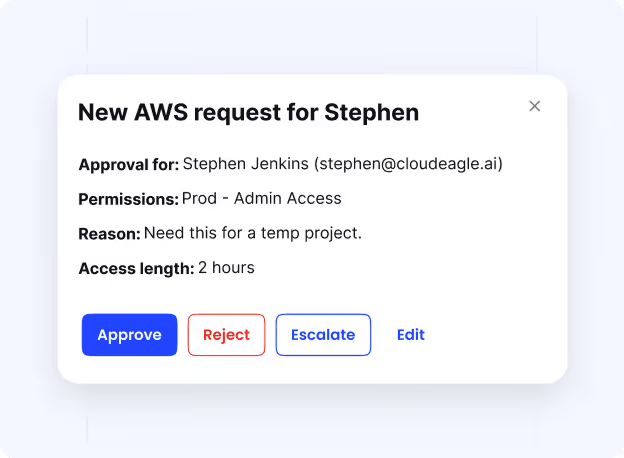
- Grants access to contractors, freelancers, or internal users for a fixed duration
- Automatically revokes access after task completion without manual intervention
- Customizes access by user type and department for granular control
- Reduces the risk of standing access that accumulates over time
Seamless Onboarding and Offboarding
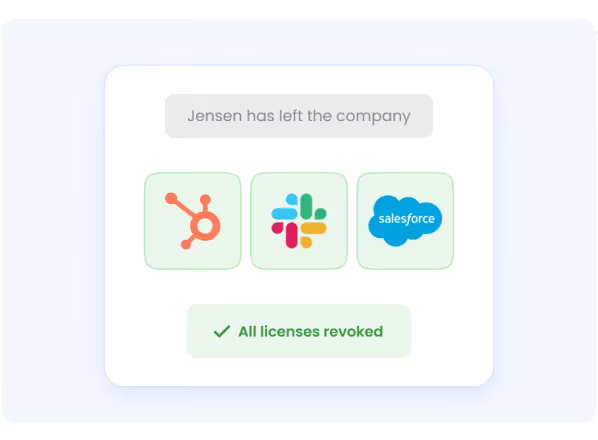
Manual onboarding and offboarding often lead to delays or security gaps. CloudEagle automates this with zero-touch onboarding via SCIM and non-SCIM, just-in-time access for role-based permissions, and automated triggers to instantly revoke access when employees leave.
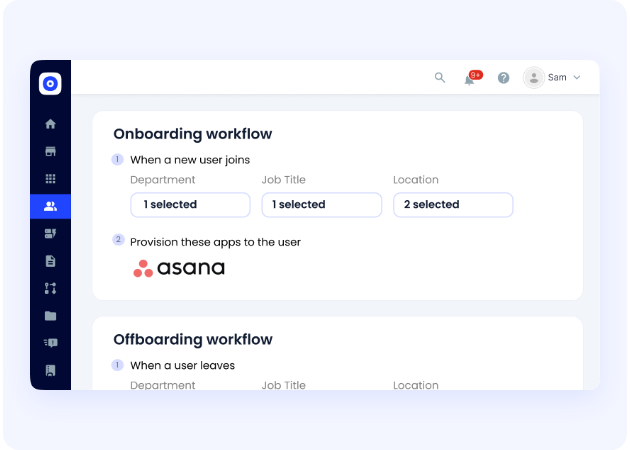
How it helps:
- Eliminates lingering permissions from former employees or role-changed staff
- Speeds up access management while strengthening identity and access security
- Reduces manual workload for IT teams managing large user populations
Privileged Access Management
How it helps:
- Automates the assignment of privileged roles across systems like AWS and NetSuite
- Continuously monitors high-risk accounts for unusual activity or privilege escalation
- Reduces unauthorized usage and human error in sensitive system access
- Supports a centralized privileged access approach while retaining flexibility for role-specific needs
7. Is Your Current Access Management Model Creating Hidden Risk?
Most organizations believe their access management is under control. The reality is that the gap between what IT governs and what employees actually access grows wider every quarter.
If your team cannot confidently answer these questions, your current model, whether centralized or decentralized, is creating risk you cannot yet see:
- Do you know exactly which employees have access to sensitive systems right now?
- Are any former employees or contractors still holding active permissions?
- Can you generate a complete access audit trail for SOC 2 or HIPAA without manual effort?
- Are different departments buying and managing SaaS tools with access controls that IT has never reviewed?
- Does your access model extend to every SaaS application in your stack, including the ones IT did not approve?
The answer to these questions determines whether your centralized vs decentralized access management strategy is working in practice, not just in theory.
CloudEagle.ai gives you the visibility and automation to close these gaps regardless of which model you operate. It surfaces access anomalies, automates lifecycle workflows, and generates compliance evidence across every app in your environment.
Conclusion
The centralized vs decentralized access management debate is not about choosing a winner. It is about aligning your strategy with your business structure, risks, and compliance needs.
Centralized access management offers control, consistency, and audit readiness. Decentralized access management enables speed and team autonomy. Most enterprises end up adopting a hybrid approach that combines centralized visibility with decentralized execution.
Decentralized identity and access management works well for agile organizations but demands robust internal controls to prevent access sprawl and privilege creep. As regulatory pressure increases and SaaS environments grow more complex, the organizations that get this right will be the ones that treat access governance as a strategic function, not an IT afterthought.
CloudEagle.ai simplifies access management with centralized visibility, automated workflows, and seamless app integrations across 500+ applications. It empowers you to balance security and agility while reducing manual effort across the entire user lifecycle.
Ready to modernize your access management strategy? Book a free demo with CloudEagle.ai today.
Frequently Asked Questions
- What are the 4 types of access control?
The four main types are: Discretionary Access Control (DAC), Mandatory Access Control (MAC), Role-Based Access Control (RBAC), and Attribute-Based Access Control (ABAC). - What is decentralized key control?
Decentralized key control distributes cryptographic key management across multiple systems or users, reducing single points of failure and improving resilience and privacy. - What is decentralized control?
Decentralized control refers to distributing decision-making authority across departments or teams, enabling local autonomy while reducing dependency on a central authority. - What is centralized access control?
Centralized access control is a system that manages user permissions from a single platform, ensuring consistent, secure access to apps and data across an organization. - What is meant by access management?
Access management refers to the process of controlling who can access specific systems, applications, or data, ensuring the right users have the right access at the right time.

%201.svg)









.avif)




.avif)
.avif)




.png)





